U.S. Pat. No. 8,972,476
EVIDENCE-BASED VIRTUAL WORLD VISUALIZATION
AssigneeMicrosoft Technology Licensing LLC
Issue DateJune 23, 2009
Illustrative Figure
Abstract
When evidence is received, a determination is made as to whether the evidence is sufficient to determine whether to block transmission of virtual world data to a client device. If it is determined that the evidence is sufficient, then another determination is made as to whether to block transmission of virtual world data to the client device based on the evidence. If it is determined to block transmission of virtual world data to the client, a data protection and abstraction module is transformed to a first state that blocks transmission of the virtual world data to the client device.
Description
DETAILED DESCRIPTION The following detailed description is directed to technologies for providing evidence-based virtual world visualization. Through the utilization of the technologies and concepts presented herein, a variety of evidence is collected through an evidence collection module and provided to a data protection and abstraction module. The data protection and abstraction module may permit or block the transmission of virtual world data to a client device based on the collected evidence. Depending on the virtual world data that is permitted or blocked by the data protection and abstraction module, the client device may render a different view of the virtual world. While the subject matter described herein is presented in the general context of program modules that execute in conjunction with the execution of an operating system and application programs on a computer system, those skilled in the art will recognize that other implementations may be performed in combination with other types of program modules. Generally, program modules include routines, programs, components, data structures, and other types of structures that perform particular tasks or implement particular abstract data types. Moreover, those skilled in the art will appreciate that the subject matter described herein may be practiced with other computer system configurations, including hand-held devices, multiprocessor systems, microprocessor-based or programmable consumer electronics, minicomputers, mainframe computers, and the like. As used herein, the term virtual world refers to a computer-implemented environment, which may include simulated, lifelike environments as well as fanciful, non-existing environments. Examples of virtual worlds may include any massively multiplayer online (“MMO”) computer application including, but not limited to, massively multiplayer online role-playing games (“MMORPGs”), virtual social communities, and virtual reality computer applications. In one embodiment, the MMO computer application simulates a real world environment. For example, the virtual world may be defined by a number of rules, such as ...
DETAILED DESCRIPTION
The following detailed description is directed to technologies for providing evidence-based virtual world visualization. Through the utilization of the technologies and concepts presented herein, a variety of evidence is collected through an evidence collection module and provided to a data protection and abstraction module. The data protection and abstraction module may permit or block the transmission of virtual world data to a client device based on the collected evidence. Depending on the virtual world data that is permitted or blocked by the data protection and abstraction module, the client device may render a different view of the virtual world.
While the subject matter described herein is presented in the general context of program modules that execute in conjunction with the execution of an operating system and application programs on a computer system, those skilled in the art will recognize that other implementations may be performed in combination with other types of program modules. Generally, program modules include routines, programs, components, data structures, and other types of structures that perform particular tasks or implement particular abstract data types. Moreover, those skilled in the art will appreciate that the subject matter described herein may be practiced with other computer system configurations, including hand-held devices, multiprocessor systems, microprocessor-based or programmable consumer electronics, minicomputers, mainframe computers, and the like.
As used herein, the term virtual world refers to a computer-implemented environment, which may include simulated, lifelike environments as well as fanciful, non-existing environments. Examples of virtual worlds may include any massively multiplayer online (“MMO”) computer application including, but not limited to, massively multiplayer online role-playing games (“MMORPGs”), virtual social communities, and virtual reality computer applications. In one embodiment, the MMO computer application simulates a real world environment. For example, the virtual world may be defined by a number of rules, such as the presence of gravity or the lack thereof. In other embodiments, the MMO computer application includes a fanciful environment that does not simulate a real world environment.
The virtual world may be inhabited by avatars, which are virtual or symbolic representations of real world participants (hereinafter referred to as participants). As such, each avatar is typically associated with and controlled by a particular participant. Avatars may include two-dimensional and/or three-dimensional images. Through the virtual world, the avatars may interact with other avatars, as well as with virtual objects. Virtual objects may include virtual representations of real world objects, such as houses, cars, billboards, clothes, packages, and soda cans, as well as fanciful creations, such as a teleportation machine or a flying car. The avatars and the virtual objects utilized in the virtual world may or may not be animated images.
In the following detailed description, references are made to the accompanying drawings that form a part hereof, and which are shown by way of illustration specific embodiments or examples. Referring now to the drawings, in which like numerals represent like elements through the several figures, aspects of a computing system and methodology for implementing a virtual world will be described. In particular,FIG. 1illustrates a simplified network architecture100for implementing a virtual world. The network architecture100shown inFIG. 1includes a server computer102and a client device104, each of which is operatively coupled via a network108. The network108may be any suitable network, such as a local area network (“LAN”) or the Internet. Although only one client device104is illustrated inFIG. 1, the network architecture100may include multiple client devices and multiple computing devices in any suitable network configuration.
The client device104may be any suitable processor-based device, such as a computer, a mobile device, or a gaming device. Exemplary gaming devices include the XBOX and the XBOX 360 from MICROSOFT CORPORATION, the WII from NINTENDO COMPANY, LIMITED, and the PLAYSTATION 3 and the PSP from SONY CORPORATION. Although not so illustrated inFIG. 1, the client device104may be coupled to any suitable peripheral devices to enable the participant to experience and interact with the virtual world. Example peripheral devices may include an input device, such as a keyboard, a mouse, a microphone, and a game controller, and an output device, such as a display and speakers. Some peripheral devices may even provide both input and output functionality. For example, a game controller may provide vibration feedback.
As shown inFIG. 1, the client device104includes a virtual world client module120, which interacts with a virtual world server module110executing on the server computer102. In particular, the virtual world client module120may receive and process data from the virtual world server module110and output the data to output devices coupled to the client device104. Further, the virtual world client module120may receive data from input devices coupled to the client device104and transmit the data to the virtual world server module110.
The virtual world client module120may include any suitable component for accessing the virtual world server module110. In one example, the virtual world client module120may be a computer application configured to locally provide at least a portion of the virtual world for the client device104. In this way, the amount of data retrieved from the server computer102by the client device104to generate the virtual world may be reduced. In another example, the virtual world client module120may be a web browser configured to retrieve the virtual world from the virtual world server module110. Since many public computers, such as those found in Internet cafes, commonly have a web browser installed and prohibit the installation of new computer applications, providing participants a way to access the virtual world via the web browser may provide greater accessibility and convenience.
As shown inFIG. 1, the server computer102includes an evidence collection module122and a data protection and abstraction module126. The virtual world server module110generally administers the virtual world and serves as a conduit between multiple client devices, including the client device104. The evidence collection module122generally collects evidence124regarding participants, the virtual world, and/or computing resources providing the virtual world. As described in greater detail below, the evidence collection module112may collect the evidence124via a push-based process and/or a query-based process. The data protection and abstraction module126generally permits or restricts the transmission of virtual world data132from the virtual world server module110to the virtual world client module120based on the collected evidence124.
When a participant desires to access the virtual world, the participant may initiate the virtual world client module120to establish a session with the virtual world server module110via the network108. During the session, the virtual world server module110may transmit virtual world data132(e.g., environment layouts, avatar movements of other participants, virtual objects) associated with the virtual world to the virtual world client module120. Similarly, the virtual world client module120may transmit data from associated input devices to the virtual world server module110.
According to embodiments, the evidence collection module122is operative to collect the evidence124. The evidence124may include, but is not limited to, information about the participants, information about the virtual world, and information about computing devices operating the virtual world. Information about the participants may be provided by or retrieved from a database (not shown inFIG. 1) storing personal information about the participant. Information about the virtual world may be provided by or retrieved from virtual world server module110and/or the virtual world client module120. Information about computing devices operating the virtual world may be provided by or retrieved from the computing devices, such as the server computer102and the client device104. It should be appreciated that the evidence124is not limited to evidence provided by the participants and the computing devices. For example, the evidence124may also include other information such as time of day, network traffic, network usage, and the like. As used herein, the term “evidence provider” refers to a computing device, module, database, or the like that is capable of providing the evidence124to evidence collection module122.
The evidence collection module122may obtain the evidence124through a push-based process and/or a query-based process. In the push-based process, the information is provided directly to the evidence collection module122in an automated process without input from the evidence collection module122. In the query-based process, the evidence collection module122transmits a query and retrieves the information in response to the query. In some embodiments, the push-based process is utilized to obtain general evidence that is applicable for the majority of applications, while the query-based process is utilized to obtain more specific or customized evidence that is not obtained by the push-based process.
The push-based process and the query-based process may be defined by a protocol128or a program130. The protocol128and the program130may define the operations the virtual world server module110and the evidence collection module122with respect to the push-based process and the query-based process. In one example, the protocol128and the program130may define the type of data that is pushed to the evidence collection module122through the push-based process. In another example, the protocol128and the program130may define the type of data that is queried by the evidence collection module122. The protocol128and the program130may also define the type of connection between modules, the method of communication between the modules, and the like.
The protocol128is generally a pre-defined and standardized collection of rules. In contrast, the program130is generally created based on a suitable programming language that enables a user to dynamically define the operations of the evidence providers. The programming language may be a domain-specific language, a conventional programming language, or a XML-based language or configuration. In further embodiments, a workflow-based rule set such as those found in WINDOWS WORKFLOW FOUNDATION or MICROSOFT BIZTALK SERVER both from MICROSOFT CORPORATION may also be similarly utilized.
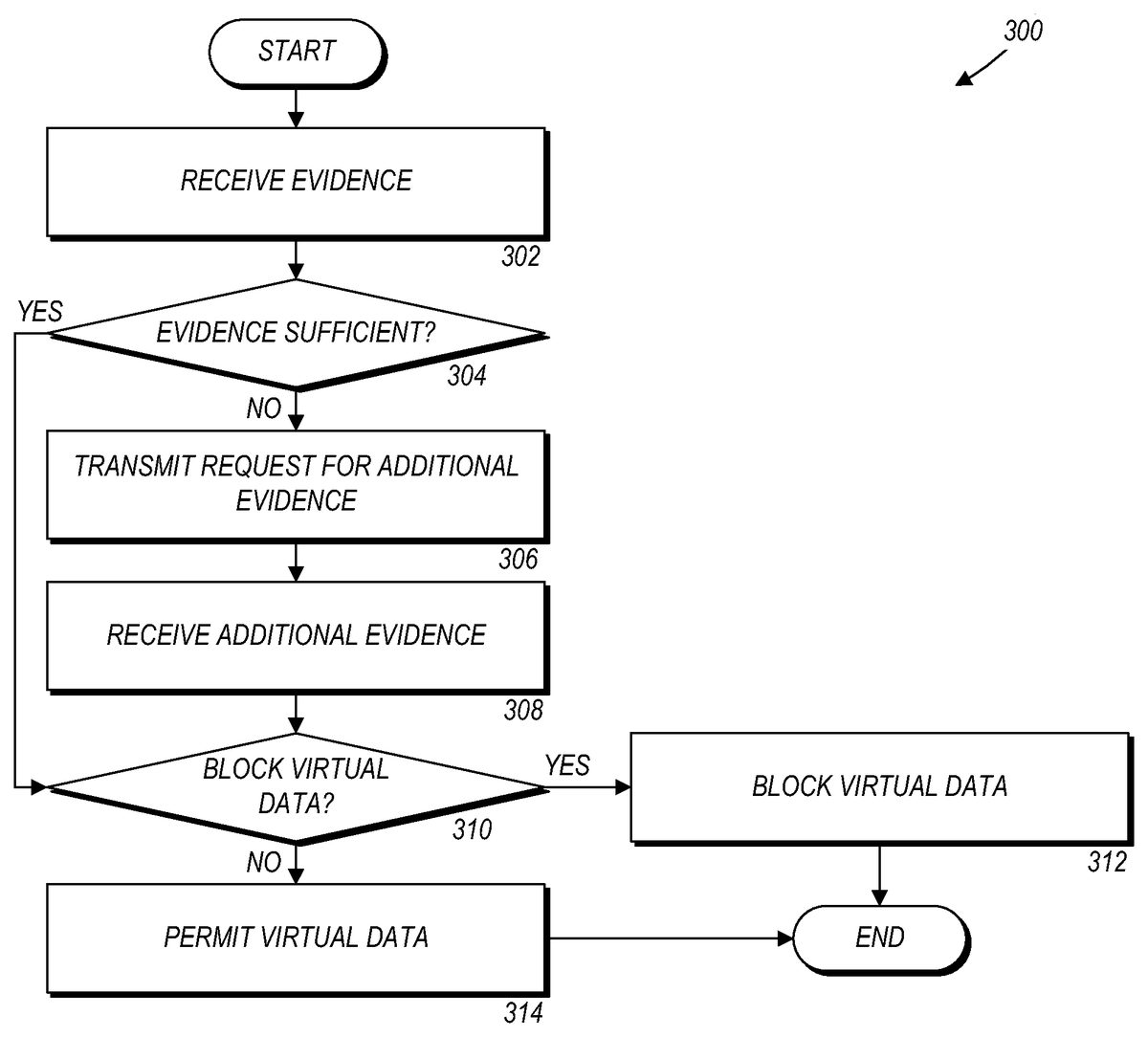
Referring now toFIGS. 2A-2Band3, additional details will be provided regarding the embodiments presented herein for providing evidence-based virtual world visualization. In particular,FIGS. 2A-2Bare flow diagrams illustrating methods for providing evidence, such as the evidence124, to the evidence collection module122in accordance with a push-based process (FIG. 2A) or a query-based process (FIG. 2B). According to embodiments, the methods illustrated inFIGS. 2A-2Bmay be implemented on various components (referred to herein as “evidence providers”) capable of providing the evidence124to the evidence collection module122. Examples of such components may include the virtual world server module110, the virtual world client module120, the server computer102, the client device104, and the like.FIG. 3is a flow diagram illustrating a method for permitting or restricting the transmission of virtual world data, such as a virtual world object (hereinafter referred to as a “virtual object”), to the client device104based on the evidence124collected by the evidence collection module122. According to embodiments, the method illustrated inFIG. 3may be implemented on the data protection and abstraction module126.
It should be appreciated that the logical operations described herein are implemented (1) as a sequence of computer implemented acts or program modules running on a computing system and/or (2) as interconnected machine logic circuits or circuit modules within the computing system. The implementation is a matter of choice dependent on the performance and other requirements of the computing system. Accordingly, the logical operations described herein are referred to variously as states operations, structural devices, acts, or modules. These operations, structural devices, acts, and modules may be implemented in software, in firmware, in special purpose digital logic, and any combination thereof. It should be appreciated that more or fewer operations may be performed than shown in the figures and described herein. These operations may also be performed in a different order than those described herein.
InFIG. 2A, a routine200A begins at operation202, where the evidence provider receives a computer protocol, such the protocol128, or a computer program, such as the program130. The evidence provider may be the virtual world server module110, the virtual world client module120, the server computer102, the client device104, or any other component capable of pushing evidence, such as the evidence124, to the evidence collection module122, in accordance with the protocol128or the program130.
The protocol128and the program130may define the operations of each component with respect to the push-based process and the query-based process. In one embodiment, the protocol128or the program130may be distributed as part of the component. For example, the protocol128or the program130may be part of the virtual world server module110or the virtual world client module120. In other embodiments, the protocol128or the program130may be distributed as they are developed and/or updated. Once the evidence provider receives the protocol128or the program130, the routine200A proceeds to operation204.
At operation204, the evidence provider identifies the evidence124in accordance with the protocol128or the program130. The protocol128or the program130may specify a condition or occurrence that triggers the identification of evidence. The protocol128or the program130may further specify the type of information that is identified as evidence. The evidence124may include any data point in the virtual world or the real world that can be utilized as criteria for determining whether to permit or block the transmission of the virtual world data132to the client device104.
In one example, the protocol128or the program130may specify that when an avatar enters a virtual location, evidence collected may include the relationship status between the participant controlling the avatar and the participant who owns the virtual room. In this example, the virtual world server module110or the virtual world client module120may push the relationship status to the evidence collection module122. The relationship status may later be utilized by the data protection and abstraction module126, as described in greater detail below, to permit or restrict the display virtual world data, such as the virtual world data132, at the client device104. For example, certain virtual world data may only be displayed to “friends” of the participant who owns the virtual world.
In another example, the protocol128or the program130may specify that when an avatar requests certain information, evidence may be collected regarding the security level of the computer or the network108. The security level may include information about secure connections, secure protocols, encryption, installed patches, version information, and the like. In this example, the server computer102or the client device104may push the security level to the evidence collection module122. The security level may later be utilized by the data protection and abstraction module126, as described in greater detail below, to determine whether to permit or restrict the transmission of the virtual world data132to the client device104. For example, confidential or sensitive virtual world data may only be transmitted to the client device104if the client device104communicates to the virtual world server module110over a secure and encrypted connection.
According to embodiments, the protocol128or the program130may also specify the type of connection (e.g., wired, wireless, secure, unsecure, etc.) made between the evidence provider and the evidence collection module122and the communications protocol (e.g., Transmission Control Protocol/Internet Protocol (“TCP/IP”), User Datagram Protocol (“UDP”), etc.) utilized by the evidence provider to transmit the evidence124to the evidence collection module122. Once the evidence provider identifies the evidence124according to the protocol128or the program130, the routine200A proceeds to operation206.
At operation206, the evidence provider transmits the identified evidence124to the evidence collection module122. In the example illustrated inFIG. 2A, the evidence provider transmits the evidence124to the evidence collection module122through a push-based process. That is, the evidence provider transmits the evidence124to the evidence collection module122without a query from the evidence collection module122. The push-based process illustrated inFIG. 2Acan be contrasted from the query-based process illustrated inFIG. 2B.
InFIG. 2B, a routine200B begins at operation212, where the evidence provider receives the protocol128or the program130. The routine200B then proceeds to operation214, where the evidence provider receives a query for the evidence124from the evidence collection module122. In the push-based process described above with respect toFIG. 2A, the protocol128or the program130specified the type of information that is collected as evidence. In the query-based process illustrated inFIG. 2B, the query may specify the type of information that is collected as evidence. Once the evidence provider receives the query for evidence from the evidence collection module122, the routine200B proceeds to operation216.
At operation216, the evidence provider determines whether the evidence124requested by the query is available. If the evidence provider determines that the evidence124requested by the query is available, then the routine200B proceeds to operation218. At operation218, the evidence provider identifies the evidence124, if the evidence was not previously identified, and transmits the evidence124to the evidence collection module122according to the protocol128or the program130. If the evidence provider determines that the evidence124requested by the query is unavailable, then the routine200B proceeds to operation220. At operation220, the evidence provider transmits an indication that the evidence124is unavailable to the evidence collection module122. For example, the requested evidence124may be unavailable if the evidence provider cannot obtain or disclose the evidence124.
It should be appreciated that the push-based process illustrated inFIG. 2Aand the query-based process illustrated inFIG. 2Bmay be separate processes or combined into a single process. For example, the push-based process may be utilized to obtain generic information, while the query-based process may be utilized to obtain custom information. In this example, the protocol128or the program130may identify information that is collected as generic evidence in each execution of the protocol128or the program130. In this way, the evidence provider may efficiently push this generic evidence to the evidence collection module122without input from the evidence collection module122. If the evidence collection module122later requires additional evidence that is not included in the generic evidence, the evidence collection module122may then transmit a query for the additional evidence to the appropriate evidence provider.
InFIG. 3, a routine300begins at operation302, where the data protection and abstraction module126receives the evidence124from the evidence collection module122. The evidence collection module122may provide the evidence124to the data protection and abstraction module126at predefined times or intervals. In the alternative, the data protection and abstraction module126may request the evidence124from the evidence collection module122as necessary. In the example illustrated inFIG. 3, the evidence124received in operation302is generic evidence that the evidence collection module122received during the push-based process. Once the data protection and abstraction module126receives the generic evidence, the routine300proceeds to operation304.
At operation304, the data protection and abstraction module126determines whether the generic evidence is sufficient to determine whether to permit or block the transmission of the virtual world data132. If the data protection and abstraction module126determines that the generic evidence is sufficient to determine whether to permit or block the transmission of the virtual world data132, then the routine300proceeds to operation310.
If the data protection and abstraction module126determines that the generic evidence is not sufficient to determine whether to permit or block the virtual world data132, the routine300proceeds to operation306. At operation306, the data protection and abstraction module126transmits a request for additional evidence to the evidence collection module122. The evidence collection module122may then transmit a query for the additional evidence to the appropriate evidence providers, as previously described. The routine300then proceeds to operation308, where the data protection and abstraction module126receives the additional evidence. Once the data protection and abstraction module126receives the additional evidence, the routine300proceeds to operation310.
At operation310, the data protection and abstraction module126determines, based on the collected evidence (e.g., generic evidence, additional evidence, etc.)124, whether to permit or block the transmission of the virtual world data132. The data protection and abstraction module126may utilize any suitable criteria and thresholds regarding the collected evidence in order to determine whether to permit or block the transmission of virtual world data132.
If the data protection and abstraction module126determines, based on the collected evidence124, to block the virtual world data132, then the routine300proceeds to operation312, where the data protection and abstraction module126blocks the virtual world data132from being transmitted to the virtual world client module120for display through the client device104. For example, if the virtual world data132includes an image of a political poster in a virtual room, then the data protection and abstraction module126may block the image of the political poster from being transmitted to the virtual world client module120. However, the data protection and abstraction module126does not affect transmission of the virtual world data regarding the remainder of the virtual room. In this way, the client device104still displays virtual room. The participant operating the client device104may or may not have any knowledge that the image of the political poster is missing.
If the data protection and abstraction module126determines, based on the collected evidence124, to permit the transmission of the virtual world data132, then the routine300proceeds to operation314, where the data protection and abstraction module126permits the transmission of the virtual world data132from the virtual world server module110to the virtual world client module120. In particular, the data protection and abstraction module126may determine whether the evidence124satisfies a condition for blocking transmission of the virtual world data132or for permitting transmission of the virtual world data132. For example, if the virtual world data comprises an image of a political poster in a virtual room, then the data protection and abstraction module126does not block the virtual world server module110from transmitting the image of the political poster to the virtual world client module120. Thus, the client device104may display the virtual room including the image of the political poster.
According to embodiments, the data protection and abstraction module126may operate in one of two states. In one state, the data protection and abstraction module126permits the transmission of the virtual world data132to the virtual world client module120. In the other state, the data protection and abstraction module126blocks the transmission of the virtual world data132to the virtual world client module120. The method described above with reference toFIG. 3may be utilized to determine the state to which the data protection and abstraction module126is transformed based on the evidence124.
Referring now toFIG. 4, an exemplary computer architecture diagram showing aspects of a computer400is illustrated. Examples of the computer400may include the server computer102and the client device104. The computer400includes a processing unit402(“CPU”), a system memory404, and a system bus406that couples the memory404to the CPU402. The computer400further includes a mass storage device412for storing one or more program modules414and one or more databases416. Examples of the program modules414include the evidence collection module122and the data protection and abstraction module126. The mass storage device412is connected to the CPU402through a mass storage controller (not shown) connected to the bus406. The mass storage device412and its associated computer-storage media provide non-volatile storage for the computer400. Although the description of computer-storage media contained herein refers to a mass storage device, such as a hard disk or CD-ROM drive, it should be appreciated by those skilled in the art that computer-storage media can be any available computer storage media that can be accessed by the computer400.
By way of example, and not limitation, computer-storage media may include volatile and non-volatile, removable and non-removable media implemented in any method or technology for storage of information such as computer-storage instructions, data structures, program modules, or other data. For example, computer-storage media includes, but is not limited to, RAM, ROM, EPROM, EEPROM, flash memory or other solid state memory technology, CD-ROM, digital versatile disks (“DVD”), HD-DVD, BLU-RAY, or other optical storage, magnetic cassettes, magnetic tape, magnetic disk storage or other magnetic storage devices, or any other medium which can be used to store the desired information and which can be accessed by the computer400.
According to various embodiments, the computer400may operate in a networked environment using logical connections to remote computers through a network such as the network108. The computer400may connect to the network108through a network interface unit410connected to the bus406. It should be appreciated that the network interface unit410may also be utilized to connect to other types of networks and remote computer systems. The computer400may also include an input/output controller408for receiving and processing input from a number of input devices (not shown), including a keyboard, a mouse, a microphone, and a game controller. Similarly, the input/output controller408may provide output to a display or other type of output device (not shown).
The bus406may enable the processing unit402to read code and/or data to/from the mass storage device412or other computer-storage media. The computer-storage media may represent apparatus in the form of storage elements that are implemented using any suitable technology, including but not limited to semiconductors, magnetic materials, optics, or the like. The computer-storage media may represent memory components, whether characterized as RAM, ROM, flash, or other types of technology. The computer-storage media may also represent secondary storage, whether implemented as hard drives or otherwise. Hard drive implementations may be characterized as solid state, or may include rotating media storing magnetically-encoded information.
The program modules414may include software instructions that, when loaded into the processing unit402and executed, cause the computer400to facilitate non-linguistic interaction with users via surface stimulation. The program modules414may also provide various tools or techniques by which the computer400may participate within the overall systems or operating environments using the components, flows, and data structures discussed throughout this description. For example, the program modules414may implement interfaces that facilitate non-linguistic interaction between the computer400and any number of users.
In general, the program modules414may, when loaded into the processors106and executed, transform the processing unit402and the overall computer400from a general-purpose computing system into a special-purpose computing system customized to facilitate non-linguistic interaction with computer systems via surface stimulation. The processing unit402may be constructed from any number of transistors or other discrete circuit elements, which may individually or collectively assume any number of states. More specifically, the processing unit402may operate as a finite-state machine, in response to executable instructions contained within the program modules414. These computer-executable instructions may transform the processing unit402by specifying how the processing unit402transitions between states, thereby transforming the transistors or other discrete hardware elements constituting the processing unit402.
Encoding the program modules414may also transform the physical structure of the computer-storage media. The specific transformation of physical structure may depend on various factors, in different implementations of this description. Examples of such factors may include, but are not limited to: the technology used to implement the computer-storage media, whether the computer-storage media are characterized as primary or secondary storage, and the like. For example, if the computer-storage media are implemented as semiconductor-based memory, the program modules414may transform the physical state of the semiconductor memory, when the software is encoded therein. For example, the program modules414may transform the state of transistors, capacitors, or other discrete circuit elements constituting the semiconductor memory.
As another example, the computer-storage media may be implemented using magnetic or optical technology. In such implementations, the program modules414may transform the physical state of magnetic or optical media, when the software is encoded therein. These transformations may include altering the magnetic characteristics of particular locations within given magnetic media. These transformations may also include altering the physical features or characteristics of particular locations within given optical media, to change the optical characteristics of those locations. Other transformations of physical media are possible without departing from the scope of the present description, with the foregoing examples provided only to facilitate this discussion.
Based on the foregoing, it should be appreciated that technologies for providing evidence-based virtual world visualization are presented herein. Although the subject matter presented herein has been described in language specific to computer structural features, methodological acts, and computer readable media, it is to be understood that the invention defined in the appended claims is not necessarily limited to the specific features, acts, or media described herein. Rather, the specific features, acts and mediums are disclosed as example forms of implementing the claims.
The subject matter described above is provided by way of illustration only and should not be construed as limiting. Various modifications and changes may be made to the subject matter described herein without following the example embodiments and applications illustrated and described, and without departing from the true spirit and scope of the present invention, which is set forth in the following claims.
Claims
- A computer-implemented method for providing evidence-based virtual world visualization, the computer-implemented method comprising computer-implemented operations for: receiving evidence;determining whether the evidence is sufficient to determine whether to block transmission of virtual world data regarding a virtual object to a client device, the virtual object being in a virtual location;in response to determining that the evidence is sufficient to determine whether to block transmission of the virtual world data to the client device, determining whether to block transmission of the virtual world data to the client device based on the evidence;in response to determining to block transmission of the virtual world data to the client device based on the evidence, transforming a data protection and abstraction module to a first state that blocks the transmission of the virtual world data to the client device;and wherein the first state blocks transmission of the virtual world data regarding the virtual object in the virtual location to the client device while permitting transmission of virtual world data regarding the virtual object in the virtual location to another client device and permitting transmission of virtual world data regarding another virtual object in the virtual location to the client device.
- The computer-implemented method of claim 1 , further comprising computer-implemented operations for: in response to determining to permit transmission of virtual world data to the client device based on the evidence, transforming the data protection and abstraction module to a second state that permits transmission of the virtual world data to the client device.
- The computer-implemented method of claim 1 , further comprising computer-implemented operations for: in response to determining that the evidence is not sufficient to determine whether to block transmission of the virtual world data to the client device, transmitting a request for additional evidence, and upon transmitting the request for additional evidence, receiving the additional evidence.
- The computer-implemented method of claim 3 , wherein determining whether to block transmission of the virtual world data to the client device based on the evidence comprises determining whether to block transmission of the virtual world data to the client device based on the evidence and the additional evidence.
- The computer-implemented method of claim 1 , wherein receiving evidence comprises receiving the evidence from an evidence collection module through a push-based process.
- The computer-implemented method of claim 1 , wherein receiving evidence comprises receiving the evidence from an evidence collection module through a query-based process.
- The computer-implemented method of claim 1 , wherein the evidence comprises information regarding a virtual world, and wherein the determination whether to block transmission of the virtual world data is based at least in part on attributes comprising a picture or message associated with the virtual object in the virtual world.
- The computer-implemented method of claim 1 , wherein determining whether to block transmission of the virtual world data to the client device based on the evidence comprises determining whether the evidence satisfies a condition for blocking transmission of the virtual world data to the client device or for permitting transmission of the virtual world data to the client device.
- The computer-implemented method of claim 1 , wherein the virtual object is in a virtual room in a virtual world, and wherein the determination whether to block transmission of the virtual world data is based at least in part on attributes of the virtual object.
- A computer system, comprising: a processor;a memory operatively coupled to the processor;an evidence collection module which executes in the processor from the memory and which, when executed by the processor, causes the computer system to obtain evidence by collecting evidence through a push-based process, providing the evidence to a server module, receiving a request for additional evidence from the server module, in response to receiving the request to collect additional evidence, collecting the additional evidence through a query-based process, and upon collecting the additional evidence, providing the additional evidence to the server module;and the server module which executes in the processor from the memory and which, when executed by the processor, causes the computer system to provide evidence-based virtual world visualization by receiving the evidence from the evidence collection module, determining whether the evidence is sufficient to determine whether to block transmission of virtual world data regarding a virtual object to a client device over a network, in response to determining that the evidence is not sufficient to determine whether to block transmission of the virtual world data to the client device, requesting additional evidence from the evidence collection module;in response to determining that the evidence including any additional evidence is sufficient to determine whether to block transmission of the virtual world data to the client device, determining whether to block transmission of the virtual world data to the client device over the network based on the evidence and any additional evidence, in response to determining to block transmission of the virtual world data to the client device based on the evidence and any additional evidence, transforming a data protection and abstraction module to a first state that blocks transmission of the virtual world data to the client device over the network, and in response to determining not to block transmission of virtual world data to the client device based on the evidence and any additional evidence, transforming the data protection and abstraction module to a second state that permits transmission of the virtual world data to the client device over the network.
- The computer system of claim 10 , wherein the server module, when executed by the processor, further causes the computer system to provide evidence-based virtual world visualization by in response to determining that the evidence is not sufficient to determine whether to block transmission of the virtual world data to the client device, transmitting the request for additional evidence to the evidence collection module, and upon transmitting the request for additional evidence to the evidence collection module, receiving the additional evidence from the evidence collection module.
- The computer system of claim 10 , wherein collecting evidence through the push-based process comprises receiving, from an evidence provider, the evidence through an automated process specified by a computer protocol executed by the evidence provider.
- The computer system of claim 10 , wherein collecting additional evidence through a query-based process comprises: transmitting a query for the additional evidence to an evidence provider;and upon transmitting the query for the additional evidence to the evidence provider, receiving the additional evidence from the evidence provider.
- A computer-storage medium comprising an optical disk, a magnetic storage device, or a solid state storage device, the computer-storage medium having computer-executable instructions stored thereon which, when executed by a computer, cause the computer to: receive evidence from an evidence collection module, the evidence comprising information regarding a virtual world and information regarding a real world;determine whether the evidence is sufficient to determine whether to block transmission of a virtual object to a client computer over a network, the client computer operative to render the virtual object for display;in response to determining that the evidence is not sufficient to determine whether to block transmission of the virtual object to the client computer, transmit a request to the evidence collection module for additional evidence, and upon transmitting the request to the evidence collection module for the additional evidence, receive the additional evidence from the evidence collection module;in response to determining that the evidence is sufficient to determine whether to block transmission of the virtual object to the client computer, determine whether to block transmission of the virtual object to the client computer over the network based on the received evidence;and in response to determining to block transmission of the virtual object to the client computer based on the received evidence, transform a data protection and abstraction module to a first state that blocks transmission of the virtual object to the client computer over the network;and in response to determining to permit transmission of the virtual object to the client computer based on the evidence, transform the data protection and abstraction module to a second state that permits transmission of the virtual object to the client computer over the network.
- The computer-storage medium of claim 14 , wherein the evidence collection module collects the evidence through a push-based process and collects the additional evidence through a query-based process.
- The computer-storage medium of claim 14 , wherein the evidence is specified by a computer protocol or a computer program, and wherein the additional evidence is specified by a query.
- The computer system of claim 10 , wherein the virtual object is in a virtual location and wherein the server module, in response to determining to block transmission of the virtual world data to the client device based on the evidence, blocks transmission of the virtual world data regarding the virtual object in the virtual location to the client device while permitting transmission of virtual world data regarding the virtual object in the virtual location to another client device and permitting transmission of virtual world data regarding another virtual object in the virtual location to the client device.
- The computer-storage medium of claim 14 , wherein the virtual object is in a virtual location and wherein the first state blocks transmission of the virtual world data regarding the virtual object in the virtual location to the client device while permitting transmission virtual world data regarding the virtual object in the virtual location to another client device and permitting transmission of virtual world data regarding another virtual object in the virtual location to the client device.
Disclaimer: Data collected from the USPTO and may be malformed, incomplete, and/or otherwise inaccurate.