U.S. Pat. No. 8,990,230
INCORPORATING SOCIAL-NETWORK INFORMATION IN ONLINE GAMES
AssigneeFacebook, Inc.
Issue DateDecember 30, 2010
Illustrative Figure
Abstract
Particular embodiments receive an indication from a first user that the first user desires to play a game; retrieve, from a social-networking system, one or more second users who are connected to the first user within a threshold degree of separation within the social-networking system; and invite each second user to play the game with the first user.
Description
DETAILED DESCRIPTION A social network is generally defined by the relationships among groups of individuals, and may include relationships ranging from casual acquaintances to close familial bonds. A social network may be represented using a graph structure. Each node of the graph corresponds to a member of the social network. Edges connecting two nodes represent a relationship between two individuals. In addition, the degree of separation between any two nodes is defined as the minimum number of hops required to traverse the graph from one node to the other. A degree of separation between two members is a measure of relatedness between the two members. FIG. 1illustrates a graph representation of a social network centered on a given individual (ME). Other members of this social network include A-U whose position, relative to ME's, is referred to by the degree of separation between ME and each other member. Friends of ME, which includes A, B, and C, are separated from ME by one degree of separation (1 d/s). A friend of a friend of ME is separated from ME by 2 d/s. As shown, D, E, F and G are each separated from ME by 2 d/s. A friend of a friend of a friend of ME is separated from ME by 3 d/s.FIG. 1depicts all nodes separated from ME by more than 3 degrees of separation as belonging to the category All. Degrees of separation in a social network are defined relative to an individual. For example, in ME's social network, H and ME are separated by 2 d/s, whereas in G's social network, H and G are separated by only 1 d/s. Accordingly, each individual will have their own set of first, second and third degree relationships. As those skilled in the art understand, an individual's social network may ...
DETAILED DESCRIPTION
A social network is generally defined by the relationships among groups of individuals, and may include relationships ranging from casual acquaintances to close familial bonds. A social network may be represented using a graph structure. Each node of the graph corresponds to a member of the social network. Edges connecting two nodes represent a relationship between two individuals. In addition, the degree of separation between any two nodes is defined as the minimum number of hops required to traverse the graph from one node to the other. A degree of separation between two members is a measure of relatedness between the two members.
FIG. 1illustrates a graph representation of a social network centered on a given individual (ME). Other members of this social network include A-U whose position, relative to ME's, is referred to by the degree of separation between ME and each other member. Friends of ME, which includes A, B, and C, are separated from ME by one degree of separation (1 d/s). A friend of a friend of ME is separated from ME by 2 d/s. As shown, D, E, F and G are each separated from ME by 2 d/s. A friend of a friend of a friend of ME is separated from ME by 3 d/s.FIG. 1depicts all nodes separated from ME by more than 3 degrees of separation as belonging to the category All.
Degrees of separation in a social network are defined relative to an individual. For example, in ME's social network, H and ME are separated by 2 d/s, whereas in G's social network, H and G are separated by only 1 d/s. Accordingly, each individual will have their own set of first, second and third degree relationships.
As those skilled in the art understand, an individual's social network may be extended to include nodes to an Nth degree of separation. As the number of degrees increases beyond three, however, the number of nodes typically grows at an explosive rate and quickly begins to mirror the ALL set.
FIG. 2is a block diagram illustrating a system for creating and managing an online social network. As shown,FIG. 2illustrates a system100, including an application server200and graph servers300. The computers of system100are connected by a network400, e.g., the Internet, and accessible by over the network by a plurality of computers, collectively designated as500. The application server200manages a member database210, a relationship database220, and a search database230.
The member database210contains profile information for each of the members in the online social network managed by the system100. The profile information may include, among other things: a unique member identifier, name, age, gender, location, hometown, references to image files, listing of interests, attributes, and the like. The profile information also includes VISIBILITY and CONTACTABILITY settings, the uses of which are described in a commonly owned, co-pending application, “System and Method for Managing Information Flow Between Members of an Online Social Network,” U.S. patent application Ser. No. 10/854,057, filed May 26, 2004, the contents of which are hereby incorporated by reference. The relationship database220stores information defining to the first degree relationships between members. The relationship database220stores information relating to the first degree relationships between members. In addition, the contents of the member database210are indexed and optimized for search, and stored in the search database230. The member database210, the relationship database220, and the search database230are updated to reflect inputs of new member information and edits of existing member information that are made through the computers500.
The application server200also manages the information exchange requests that it receives from the remote computers500. The graph servers300receive a query from the application server200, process the query and return the query results to the application server200. The graph servers300manage a representation of the social network for all the members in the member database. The graph servers300have a dedicated memory device310, such as a random access memory (RAM), in which an adjacency list that indicates all first degree relationships in the social network is stored.
A sample adjacency list that reflects the social network map ofFIG. 1is shown inFIG. 3. A list item is generated for each member and contains a member identifier for that member and member identifier(s) corresponding to friend(s) of that member. As an alternative to the adjacency list, an adjacency matrix or any other graph data structure may be used. The graph servers300and related components are described in detail in a commonly owned, co-pending application, “System and Method for Managing an Online Social Network,” U.S. patent application Ser. No. 10/854,054, filed May 26, 2004, the contents of which are hereby incorporated by reference.
The graph servers300respond to requests from application server200to identify relationships and the degree of separation between members of the online social network. The application server200is further configured to process requests from a third party application610to provide social network information (e.g., the relationships between individuals) for user records maintained in a third party database620. The third-party application610makes the requests to the application server200through an application programming interface (API)600.
The API600provides application developers with a set of methods, method signatures, data structures, and the like that expose an interface used by the third party application610to communicate with the application server200. Application developers use the methods defined by the API600to construct applications that can communicate with the application server200. There are many programmatic and syntactical choices to define the API methods that will effectively encapsulate the data and operations that are used in the invention. Thus, specific API methods, routines and data structures described below are illustrative in nature and are neither limiting nor definitive of the API600.
FIG. 4illustrates an example of a subset of a social network graph350maintained by the graph servers300along with a subset of database records360maintained in the third party database620. As depicted, the subset350includes members A, B, C, D, E and F, and the subset360include records for A′, B′, E′, F′, G and H. A and A′ represent the same individual but are labeled differently to signify that a database record for this person exists in both the member database210and the third party database620. The same is true for: B and B′, E and E′, and F and F′. By contrast, database records for individuals C, D exist in the member database210, but not in the third party database620, and database records for individuals G, H exist in the third party database620, but not in the member database210.
The relationships between individuals A, B, C, D, E and F are maintained in the relationship database220and the graph servers300. The flow diagram shown inFIG. 5is used to find out the relationships between individuals A′, B′, E′, F′, G and H, namely to obtain the social network information used to construct the edges (shown as dashed lines inFIG. 4) between (A′, B′), (E′, F′) and (A′, F′).
FIG. 5is a flow diagram that illustrates a method for processing a request for social network information by the third party application610in the system ofFIG. 2. In Step410, the application server200receives a request from the third party application610to identify social network relationships (i.e., the edges between nodes) among users who are represented by a set of ID tokens405. For example, API600may provide a method to make such a request according to the following:
relationship_pairs[ ]find_Connections(ID_Tokens[ ], credential_Type, hash_Type).
The find_Connections method accepts an array of ID Tokens, an indication of the type of shared credentials used (credential_Type), and an indication of the type of hash algorithms used (hash_Type). In response, the find_Connections method returns an array of relationship pairs comprising two ID tokens and an indication of the relationship between the members represented by the two ID tokens.
The shared credential types include an e-mail address (credential_Type=1), first and last name (credential_Type=2), telephone number (credential_Type=3), and any other types or a combination of two or more types that might be used to identify an individual. Of the three types specifically identified here, the e-mail address type is preferred, because in most instances an e-mail address is associated with a single individual.
The hash algorithm types include none (hash_Type=0), MD5 one-way hash algorithm (hash_Type=1), and SHA-1 one-way hash algorithm (hash_Type=2). When hash_Type=1 or 2, the corresponding one-way hash algorithm is used to create a hash value from the identifying information associated with the credential type selected (e.g., e-mail, first and last name, telephone number, etc.), and the hash value is used as a shared credential. When hash_Type=0, a hash algorithm is not used and the shared credential comprises the identifying information associated with the credential type selected (e.g., e-mail, first and last name, telephone number, etc.).
In Step420, after receiving the set of the ID tokens405from the third party application610, the application server200compares the value of each ID token from the set against ID tokens corresponding to the members of the online social network. The ID tokens corresponding to the members of the online social network are generated using the shared credential type and the hash algorithm type specified in the variables credential_Type and hash_Type. A match from this comparison indicates that there is a record for that individual in both the third party database620and in the member database210.
For some embodiments, the application server200may improve its processing efficiency by generating the ID tokens for its members ahead of time and having them stored for use in the comparison of Step420. For example, the application server200may maintain an index of unique member identifiers, each associated with the corresponding member's e-mail address (credential_Type=1, hash_Type=0), a hash value generated from the corresponding member's e-mail address using the MD5 hash algorithm (credential_Type=1, hash_Type=1), and a hash value generated from the corresponding member's e-mail address using the SHA-1 hash algorithm (credential_Type=1, hash_Type=2).
At this point, the application server200has identified which ID Tokens have a member profile in the online social network. In Step430, the application server200queries the graph servers300to obtain the specific relationship information for the identified members. For example, referring toFIG. 4, for each member pair: (A, B), (A, E), (A, F), (B, E), (B, F), and (E, F), the application server200issues a query to the graph servers300to obtain the degree of separation between the member pair.
Then, in Step440, the application server200returns an array455, which includes the ID tokens corresponding to each member pair and the degree of separation obtained for each member pair, e.g., (A, B, 1), (A, E, 4), (A, F, 3), (B, E, 5), (B, F, 4), and (E, F, 1). Optionally, other attributes, e.g., demographic information, may be returned. Using the ID tokens that are returned, the third party application610identifies the corresponding members in the third party database620, and records the degrees of separation between the member pairs.
Note, in the above example, the application server200returns a pair indicating a third degree relationship between A and F, but does not include the connecting members, C and D. Unless the set of ID tokens405includes a token for each member with a record in the online social network, the information returned by the application server200may be incomplete in some respects. In other words, when the relationship graph is reconstructed from the information returned by the application server200, A and F will be connected to two dummy nodes.
In another embodiment of the invention, the third party application610may use a method from API600that requires the passing of a single ID token (e.g., corresponding to member M1), a shared credential type, a hash algorithm type, and a d/s setting N, in its request to the application server200. In response, the application server200returns an indication of M1's social network up to N degrees of separation. The method signature is as follows:
network get_Network(ID_Token, credential_Type, hash_Type, N).
The d/s setting N is optional. If it is omitted, a default value, e.g., 3, is used. If it is specified, the application server200returns an indication of M1's social network up to the specified degree of separation.
After receiving the request according to the get_Network method, the application server200identifies the member corresponding to the ID token (e.g., M1) provided by the third party application610. If the ID token does not correspond to any member, the application server returns an indication of this to the third party application610. Otherwise, the application server200queries the graph servers300to identify the members of the online social network that are related to M1within N degrees of separation (or a number specified in the get_Network method). For each member identified, the application server200creates an ID token in accordance with the shared credential type and the hash algorithm type specified in the request. The application server200returns all ID tokens so created along with an indication for each ID token the degree of separation from M1. The third party application610then uses the returned set of ID tokens to determine whether the third party database620contains records corresponding to the members in M1's social network, and if there are, it stores the degree of separation information for each such record.
As an example, the third party application610may be an online gaming site and the third party database620may be the database of registered users maintained by the online gaming site. The process described above would be used by the online gaming site, as illustrated inFIG. 11, to obtain social network information for its registered users from the computer system ofFIG. 2,1102so that each time a registered user logs in to play1101, the online gaming site can invite (by e-mail or IM, for example) one or more additional registered users in his or her network to log on and play as well1103.
The present invention may also be used to clarify ambiguities in certain requests for information. For example, if a user queried an online telephone directory for the number of “John Smith,” many results may be returned. The online telephone directory could use the get_Network API method to query the application server200to identify a John Smith present in the requestor's social network, likely eliminating all but one “John Smith” from consideration.
FIG. 6illustrates the above process in further detail. In Step510, the ID token of the user requesting the number of “John Smith” (e.g., M1) is transmitted by the third party application610to the application server200along with the get_Network request which also specifies the shared credential type used, the hash algorithm type used, and the d/s setting N. The application server200then compares the ID token of the requesting user with the ID tokens of its members. If a match is found, the application server200queries the graph server300for all members related to the member corresponding to the matching ID token within N degrees of separation. The ID tokens of all such members are then transmitted to the third party application610. The third party application610receives these ID tokens (Step520) and compares them against the ID token of a “John Smith” candidate (Step530). If there's a match, it is confirmed that the “John Smith” candidate is the “John Smith” that M1is looking for (Step540). If there is not a match, the “John Smith” candidate is not confirmed as the “John Smith” that M1is looking for (Step550), and the third party application610compares the received ID tokens against the ID token of another “John Smith” candidate. This process is repeated until a match is found or all “John Smith” candidates have been exhausted.
The application server200may be configured to provide the degree of separation between two individuals. A method signature from the API600call for this could be the following:
get_Degrees(ID_Token1, ID_Token2, credential_Type, hash_Type).
The application server200processes this call in a manner similar to the above calls. First, the application server200resolves which members in the member database210correspond to IDToken1 and ID_Token2. If the application server200is unable to resolve one or both an error is returned. Otherwise, the application server200queries the graph servers300to determine the degree of separation between the members corresponding to ID_Token1 and IDToken2. Once determined, the application server200returns a number as the degree of separation between the two members. Using the degree of separation between the two individuals, the third party application610may manage transaction processing based on the relationship (or lack thereof) between the two members.
The third party application610may use this information to control the visibility of information in the third party database620. For example, the third party application610might store telephone numbers, or other personal information related to a user M1in the third party database620, and an access preference from M1that specifies how closely related to M1a user has to be (expressed in terms of degrees of separation) in order to view M1's phone number. Using the relationship information obtained from the online social network as described above, the third party application610may limit access to M1's information stored in the third party database620to only those users who are within N degrees of separation, where N is the degree of separation specified by M1in the access preference.
In the above examples, as an alternative to the MD5 and SHA-1, Message Authentication Code (MAC) may be used as the hash algorithm. MAC is also a one-way hash algorithm but uses a secret key that the party maintaining social network information and the party requesting social network information through the API600would agree to in advance. The use of the key provides extra security.
FIG. 2depicts the third party database620to be external to the computer system100of the online social network. In alternative embodiments of the invention, the operator of the online social network may act as an application service provider (ASP) that maintains the third party database620, on behalf of the third party, within the computer system100. In such a case, the online social network periodically maps the social network information maintained by its graph servers300onto the third party database620, so that the social network information will be made available for use without the information flow that is illustrated inFIGS. 5 and 6.
FIG. 7is a flow diagram illustrating the steps carried out by a search engine that uses social network information to tailor search results delivered to its users in response to a search query. A sample search query810and search results820, which includes sponsored links (online ads)830and web search results840, that are generated in response to the sample search query810is illustrated inFIG. 8.
The sponsored links830represent hyperlinks to web pages of advertisers who have agreed to pay the search engine operator for listing their hyperlinks on the search results page of users who submit search queries using certain keywords. In a typical arrangement, the advertisers bid on keywords such that higher bids result in higher placement on the search results page. The bids represent the amount the advertisers are willing to pay per click on their online ads. The web search results840represent what is commonly known in the art as algorithmic search results.
In this example, the third party application610is a search engine operator that manages a search results database, and the third party database620represents a plurality of databases including: (i) a user database that keeps track of all search queries specified by each user and, for each such search query, a record of all hyperlinks that the user clicked on when search results responsive to the search query were served to the user; (ii) a database containing information on advertisers, keywords that the advertisers bid on, and the sponsored links corresponding to the keywords; and (iii) a database of web pages that are used to generate the algorithmic search results.
In Step710, the third party application610receives a search query from a registered user. In Step720, the third party application610retrieves the search results (both sponsored links and algorithmic search results) responsive to the search query from its search results database. The retrieved sponsored links are ranked in accordance with the bids submitted by their advertisers, and the retrieved algorithmic search results are ranked based on their relevance as determined by the search engine. In Step730, the third party application610searches the third party database620for search queries that match the one received from the user in Step710. If there are no matches, the search results retrieved in Step720are served to the user (Steps740and750).
If there are one or more matches, the algorithmic search results are re-ordered based on the frequency of “relevant” clicks on the hyperlinks associated with the search results and then served to the user. Frequency of clicks is equal to the number of prior clicks on a hyperlink divided by the number of times that hyperlink was displayed, and hyperlinks with higher frequencies are ranked higher than hyperlinks with lower frequencies. Relevant clicks are those clicks made by users who are within a specified degree of separation from the user who requested the search. The degree of separation information (i.e., social network or relationship information) may be maintained by the third party application610or obtained from an online social network in the manner described above in connection withFIG. 5. The specified degree of separation may be any number or set as ALL, in which case all clicks become relevant, and it may be set by the operator of the search engine, or it may be set by a user in his or her profile. For example, if the user sets the specified degree of separation as 1, only clicks made by those who are friends of the user become relevant clicks.
In addition, visual tags may be displayed on the search results page next to those search results (both sponsored links and algorithmic search results) for which relevant clicks have been recorded.FIG. 9shows a sample search query910and search results920, which includes sponsored links930and web search results940, that are generated in response to the sample search query910. Visual tags are displayed next to those search results for which relevant clicks have been recorded. Visual tags may be an image951or a text string952. When the visual tag is an image, the source for the web page that displays the search results920specifies a pointer to a file that contains that image. When the visual tag is a text string, the source for the web page that displays the search results920includes the text string.
The computer system100of the online social network may also deliver Internet search results to members of the online social network and to Internet users who are not members of the online social network. In this example, the computer system100is provided with an Internet search results database and an Internet search query database that keeps track of all Internet search queries specified by each member of the online social network and, for each such search query, a record of all hyperlinks that the member clicked on when search results responsive to the search query were served to the member.
When the computer system100receives an Internet search query from one of its members, it retrieves the search results responsive to the search query from the Internet search results database, and searches the Internet search query database for search queries that match the one received from the member. If there are no matches, the search results retrieved from the Internet search results database are served to the member. If there is one or more matches, the search results retrieved from the Internet search results database are ranked based on the frequency of “relevant” clicks on the hyperlinks associated with the search results and then served to the member. Relevant clicks are those clicks made by members who are within a specified degree of separation from the member who requested the search. The specified degree of separation may be any number or set as ALL, in which case all clicks become relevant, and it may be set by the operator of the online social network, or it may be set by a member in his or her profile. For example, if the member sets the specified degree of separation as 1, only clicks made by those who are friends of the members become relevant clicks.
When the computer system100receives an Internet search query from an Internet user who is not a member of the online social network, it retrieves the search results responsive to the search query from the Internet search results database, and searches the Internet search query database for search queries that match the one received from the user. If there are no matches, the search results retrieved from the Internet search results database are served to the user. If there is one or more matches, the search results retrieved from the Internet search results database are ranked based on the frequency of clicks on the hyperlinks associated with the search results and then served to the user.
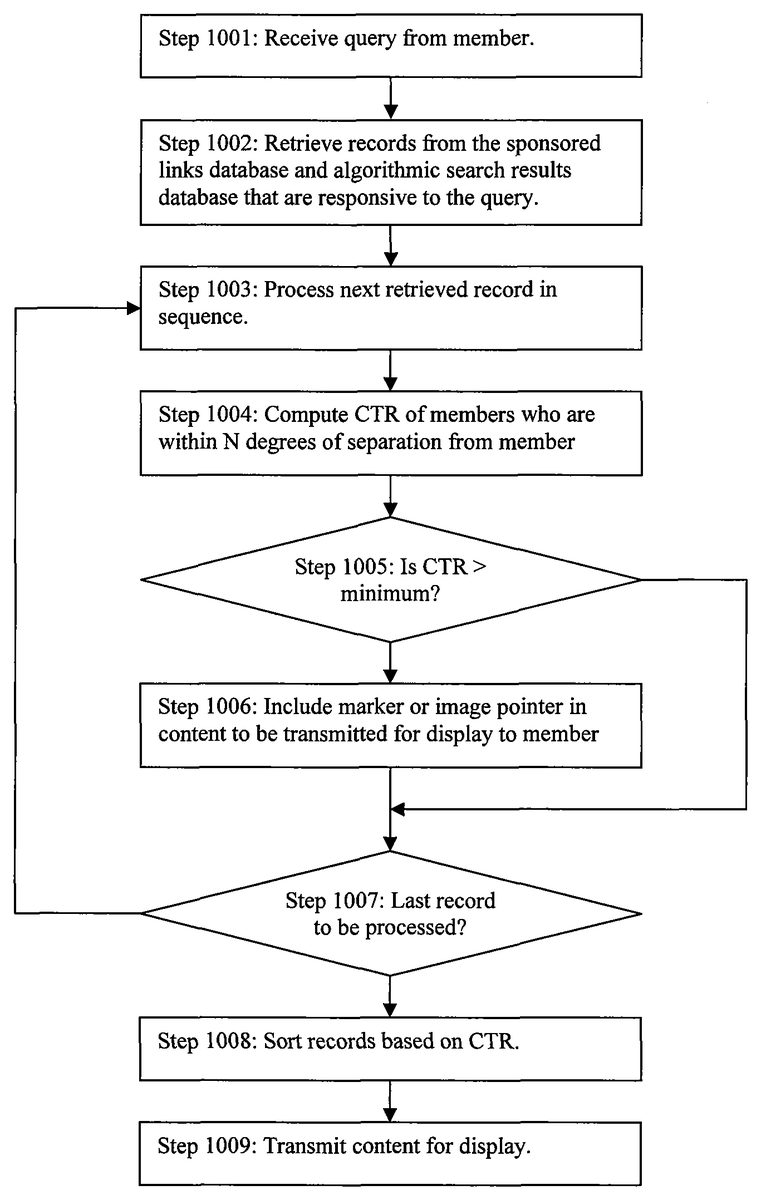
In a slightly different embodiment, the computer system100of the online social network delivers both sponsored links and algorithmic search results to members of the online social network. This process is illustrated inFIG. 10. In this example, the computer system100is provided with a search query database that keeps track of all Internet search queries specified by each member of the online social network and, for each such search query, a record of all hyperlinks that the member clicked on when search results responsive to the search query were served to the member. It also includes or is connected to: (i) a database containing information on advertisers, keywords that the advertisers bid on, and the sponsored links corresponding to the keywords; and (ii) a database of web pages that are used to generate the algorithmic search results.
In Step1001, the computer system100receives an Internet search query from a member. In Step1002, it retrieves records that are responsive to the search query from the sponsored links database and the algorithmic search results database, and searches the Internet search query database for search queries that match the one received from the member.
In Steps1003-1007, it processes each of the retrieved records in sequence (Step1003). In Step1004, it computes the click-through rate (CTR) on that record by members of the social network who are within a specified degree of separation from the member, and in Step1005, checks to see if the computed CTR is greater than a minimum value. The specified degree of separation may be any number or set as ALL, and it may be set by the operator of the search engine, or it may be set by a user in his or her profile. The minimum value may be zero or a small value (e.g., 0.01). If the computed CTR is greater than the minimum value, the computer system100determines the record to be “relevant” and specifies a marker to be displayed next to this record in the search results (Step1006). Flow then proceeds to Step1007where it continues processing of the remaining records. If the computed CTR is less than or equal to the minimum value, flow proceeds to Step1007where it continues processing of the remaining records. After the last record has been processed, the records are sorted based on their computed CTR (Step1008) and the content is transmitted for display.
While particular embodiments according to the invention have been illustrated and described above, those skilled in the art understand that the invention can take a variety of forms and embodiments within the scope of the appended claims.
Claims
- A method comprising: receiving, at one or more computing devices, an indication from a first user of a social-networking system that the first user desires to play an online game of a third-party online gaming site, the social-networking system comprising a graph that comprises a plurality of nodes and edges connecting the nodes, each edge between two nodes representing a relationship between them and establishing a single degree of separation between them, wherein the first user corresponds to a first node of the graph;identifying, by the one or more computing devices, one or more second users of the social-networking system that are connected to the first user within the social-networking system by a degree of separation less than or equal to a threshold degree of separation, the one or more second users corresponding to one or more second nodes of the graph, respectively, wherein, the threshold degree of separation being configurable;and inviting, by the one or more computing devices, each of one or more of the second users each corresponding to a second node having a degree of separation from the first node less than or equal to the configured threshold degree of separation to play the online game of the third-party gaming site with the first user by sending a message to each of the second users.
- The method of claim 1 , wherein the threshold degree of separation is specified by the first user.
- The method of claim 1 , further comprising: receiving, at the one or more computing devices, an indication from a second user that the second user desires to play the online game with the first user;and enabling, by the one or more computing devices, the first user and the second user to play the online game together at an online gaming system.
- The method of claim 1 , wherein the indication comprises a username and a password of the first user that enable the first user to log on to an online gaming system where the first user plays the online game.
- The method of claim 1 , wherein inviting a second user comprises sending an e-mail to the second user inviting the second user to play the online game with the first user.
- The method of claim 1 , wherein inviting a second user comprises sending an instant message to the second user inviting the second user to play the online game with the first user.
- The method of claim 1 , wherein identifying the one or more second users comprises: sending, to the social-networking system, a first identifier corresponding to the first user;and receiving, from the social-networking system, one or more second identifiers corresponding to the one or more second users.
- The method of claim 7 , further comprising computing the first identifier by applying a hash algorithm to a credential associated with the first user.
- The method of claim 1 , wherein the threshold degree of separation is one, two, three, or all.
- A system comprising: a memory comprising instructions executable by one or more processors;and the one or more processors coupled to the memory and operable to execute the instructions, the one or more processors being operable when executing the instructions to: receive an indication from a first user of a social-networking system that the first user desires to play an online game of a third-party online gaming site, the social-networking system comprising a graph that comprises a plurality of nodes and edges connecting the nodes, each edge between two nodes representing a relationship between them and establishing a single degree of separation between them, wherein the first user corresponds to a first node of the graph;identify one or more second users of the social-networking system that are connected to the first user within the social-networking system by a degree of separation less than or equal to a threshold degree of separation, the one or more second users corresponding to one or more second nodes of the graph, respectively, wherein, the threshold degree of separation being configurable;and invite each of one or more of the second users each corresponding to a second node having a degree of separation from the first node less than or equal to the configured threshold degree of separation to play the online game of the third-party gaming site with the first user by sending a message to each of the second users.
- The system of claim 10 , wherein the threshold degree of separation is specified by the first use.
- The system of claim 10 , wherein the one or more processors are further operable when executing the instructions to: receive an indication from a second user that the second user desires to play the online game with the first user;and enable the first user and the second user to play the online game together at an online gaming system.
- The system of claim 10 , wherein the indication comprises a username and a password of the first user that enable the first user to log on to an online gaming system where the first user plays the online game.
- The system of claim 10 , wherein inviting a second user comprises sending an e-mail to the second user inviting the second user to play the online game with the first user.
- The system of claim 10 , wherein inviting a second user comprises sending an instant message to the second user inviting the second user to play the online game with the first user.
- The system of claim 10 , wherein identifying the one or more second users comprises: sending, to the social-networking system, a first identifier corresponding to the first user;and receiving, from the social-networking system, one or more second identifiers corresponding to the one or more second users.
- The system of claim 16 , wherein the one or more processors are further operable when executing the instructions to compute the first identifier by applying a hash algorithm to a credential associated with the first user.
- The system of claim 10 , wherein the threshold degree of separation is one, two, three, or all.
- The method of claim 1 , wherein the threshold degree of separation is specified by a system operator.
- The method of claim 1 , wherein the threshold degree of separation is specified by a third party application.
- The method of claim 1 , wherein the threshold degree of separation is variable.
- The method of claim 1 , wherein the threshold degree of separation is one.
- The method of claim 1 , wherein inviting a second user comprises displaying to the second user a hyperlink for the online game.
- The method of claim 1 , wherein inviting a second user comprises displaying a hyperlink for the online game, the displayed hyperlink being based on an algorithmic search.
- The method of claim 1 , wherein inviting a second user comprises displaying a hyperlink for the online game, the displayed hyperlink being a sponsored link.
- The method of claim 1 , wherein inviting a second user comprises displaying a visual tag next to a hyperlink for the online game, the visual tag comprising an image or text string-indicating that one or more other second users have clicked on the hyperlink for the online game.
- The system of claim 10 , wherein the threshold degree of separation is specified by a system operator.
- The system of claim 10 , wherein the threshold degree of separation is specified by a third party application.
- The system of claim 10 , wherein the threshold degree of separation is variable.
- The system of claim 10 , wherein the threshold degree of separation is one.
- The system of claim 10 , wherein inviting a second user comprises displaying to the second user a hyperlink for the online game.
- The system of claim 10 , wherein inviting a second user comprises displaying a hyperlink for the online game, the displayed hyperlink being based on an algorithmic search.
- The system of claim 10 , wherein inviting a second user comprises displaying a hyperlink for the online game, the displayed hyperlink being a sponsored link.
- The system of claim 10 , wherein inviting a second user comprises displaying a visual tag next to a hyperlink for the online game, the visual tag comprising an image or text string indicating that one or more other second users have clicked on the hyperlink for the online game.
- The method of claim 1 , further comprising: determining, by the one or more computing devices, for each of the second users, the degree of separation between the first node corresponding to the first user and the second node corresponding to the second user.
Disclaimer: Data collected from the USPTO and may be malformed, incomplete, and/or otherwise inaccurate.