U.S. Pat. No. 8,308,569
REWARD FOR RESURRECTING TEAMMATE IN A MULTIPLAYER GAME
AssigneeMicrosoft Technology Licensing LLC
Issue DateMay 12, 2008
Illustrative Figure
Abstract
Teamwork in a multiplayer video game is encouraged by rewarding game characters who resurrect killed teammates with spendable cash that may be used to purchase additional capabilities or tools to enhance the players' ability to progress through the game. Resurrected teammates are tied to the game character who performed the resurrections by splitting their future earnings accumulated during gameplay with that game character. If a resurrected game character goes on to resurrect other teammates then he will be entitled to a portion of the future earnings of those other resurrected teammates. But the resurrected teammate will also give a portion of those earnings to the original game character who resurrected him in the first place. A resurrection chain is thus created in which game characters can be resurrected and go on to resurrect other teammates while sharing earnings with other game characters that are above them in the chain using a pyramid payment system.
Description
Like reference numerals indicate like elements in the drawings. Elements are not drawn to scale unless otherwise indicated. DETAILED DESCRIPTION FIG. 1illustrates an example of a gaming system100on which computer games, video games, and/or other electronic games (collectively referred to herein as video games) may be played. The gaming system100is only one example of a suitable gaming system and is not intended to suggest any limitation as to the scope of use or functionality of the features described herein. Neither should the gaming system100be interpreted as having any dependency or requirement relating to any one or combination of components illustrated in the illustrative operating gaming system100. Aspects described herein are operational with numerous other general purpose or special purpose computing system environments or configurations. Examples of well-known computing systems, environments, and/or configurations that may be suitable for use include, but are not limited to, PCs, server computers, portable and hand-held devices such as personal digital assistants (“PDAs”), mobile phones, smart phones, handheld game devices, tablet PCs or laptop PCs, media centers, multiprocessor systems, microprocessor-based systems, set-top boxes, programmable consumer electronics, network PCs, minicomputers, mainframe computers, electronic game consoles, distributed computing environments that include any of the above systems or devices, and the like. Aspects herein may be described in the general context of computer-executable instructions, such as program modules, being executed by a computer. Generally, program modules include routines, programs, objects, components, data structures, etc., that perform particular tasks or implement particular abstract data types. The features described herein may also be practiced in distributed computing environments where tasks are performed by remote processing devices that are linked through a communications network. In a distributed computing environment, program modules may be located in both local and remote computer storage media including memory storage devices. The gaming system100may include a game ...
Like reference numerals indicate like elements in the drawings. Elements are not drawn to scale unless otherwise indicated.
DETAILED DESCRIPTION
FIG. 1illustrates an example of a gaming system100on which computer games, video games, and/or other electronic games (collectively referred to herein as video games) may be played. The gaming system100is only one example of a suitable gaming system and is not intended to suggest any limitation as to the scope of use or functionality of the features described herein. Neither should the gaming system100be interpreted as having any dependency or requirement relating to any one or combination of components illustrated in the illustrative operating gaming system100.
Aspects described herein are operational with numerous other general purpose or special purpose computing system environments or configurations. Examples of well-known computing systems, environments, and/or configurations that may be suitable for use include, but are not limited to, PCs, server computers, portable and hand-held devices such as personal digital assistants (“PDAs”), mobile phones, smart phones, handheld game devices, tablet PCs or laptop PCs, media centers, multiprocessor systems, microprocessor-based systems, set-top boxes, programmable consumer electronics, network PCs, minicomputers, mainframe computers, electronic game consoles, distributed computing environments that include any of the above systems or devices, and the like.
Aspects herein may be described in the general context of computer-executable instructions, such as program modules, being executed by a computer. Generally, program modules include routines, programs, objects, components, data structures, etc., that perform particular tasks or implement particular abstract data types. The features described herein may also be practiced in distributed computing environments where tasks are performed by remote processing devices that are linked through a communications network. In a distributed computing environment, program modules may be located in both local and remote computer storage media including memory storage devices.
The gaming system100may include a game console102and multiple controllers, as represented by controllers1041and1042. The game console102is equipped with a removably attachable hard disk drive105and a portable media drive106that supports various forms of portable storage media as represented by optical storage disc108. Examples of suitable portable storage media include DVD (digital versatile disc), CD-ROM (compact disc—read only memory), game discs, and so forth.
Game console102has slots110on its front face to support up to two controllers, although the number and arrangement of slots may be modified. A power button112and an eject button114are also positioned on the front face of the game console102. The power button112switches power to the game console and the eject button114alternately opens and closes a tray of the portable media drive106to allow insertion and extraction of the storage disc108.
Game console102may connect to a television118or other display via A/V interfacing cables120. A power cable122provides power to the game console. Game console102may further be configured with broadband network capabilities, as represented by the cable or modem connector124to facilitate access to a network, such as the Internet.
Each controller104may be coupled to the game console102via a wired or wireless interface. In the illustrated implementation, the controllers are USB (Universal Serial Bus) compatible and are connected to the console102via respective USB cables1301and1302. The controllers104may be equipped with any of a wide variety of user interaction mechanisms. In this example, each controller104is equipped with two thumbsticks1321and1322, a D-pad (directional pad)134, buttons136(e.g., ‘A’, ‘B’, ‘X’, ‘Y’), and two triggers138(although only one trigger is shown in the drawing). These mechanisms are merely representative, and other known gaming mechanisms may be substituted for or added to those shown inFIG. 1.
A memory unit140may be inserted into a memory unit reader141in the game console102to provide additional and portable storage. In this example, up to two memory units may be supported by the game console102. Portable memory units enable users to store game parameters and user accounts, and port them for play on other consoles. A headset142may be connected to the controller104or game console102to provide audio communication capabilities. Headset142may include a microphone for audio input and one or more speakers for audio output.
Gaming system100is capable of playing, for example, games, music, and videos. With the different storage offerings, titles can be played from the hard disk drive or the portable media108in drive106, from an online source, or from a memory unit140. For security, in some embodiments executable code can only be run from the portable media108. A sample of what gaming system100is capable of playing includes game titles played from CD and DVD discs, from the hard disk drive, or from an online source, digital music played from a CD in the portable media drive106, from a file on the hard disk drive (e.g., Windows Media Audio (“WMA”) format), or from online streaming sources, and digital audio/video played from a DVD disc in the portable media drive106, from a file on the hard disk drive (e.g., Active Streaming Format), or from online streaming sources.
FIG. 2shows functional components of the gaming system100in more detail. The game console102has a central processing unit (“CPU”)200and a memory controller202that facilitates processor access to various types of memory, including a flash ROM (Read Only Memory)204, a RAM (Random Access Memory)206, the hard disk drive105, the memory unit reader141, and the portable media drive106. The CPU200is equipped with a level 1 cache210and a level 2 cache212to temporarily store data and hence reduce the number of memory access cycles, thereby improving processing speed and throughput.
The CPU200, memory controller202, and various memory devices are interconnected via one or more buses, including serial and parallel buses, a memory bus, a peripheral bus, and a processor or local bus using any of a variety of bus architectures. By way of example, such architectures can include an Industry Standard Architecture (“ISA”) bus, a Micro Channel Architecture (“MCA”) bus, an Enhanced ISA (“EISA”) bus, a Video Electronics Standards Association (“VESA”) local bus, and a Peripheral Component Interconnects (“PCI”) bus also known as a Mezzanine bus.
As one suitable implementation, the CPU200, memory controller202, ROM204, and RAM206are integrated onto a common module214. In this implementation, ROM204is configured as a flash ROM that is connected to the memory controller202and a ROM bus (not shown). RAM206is configured as multiple DDR SDRAM (Double Data Rate Synchronous Dynamic RAM) that is independently controlled by the memory controller202via separate buses (not shown). The hard disk drive105and portable media drive106are connected to the memory controller via the PCI bus and an ATA (Advanced Technology Attachment) bus216.
A 3D graphics processing unit220and a video encoder222form a video processing pipeline for high speed and high resolution graphics processing. Data is carried from the graphics processing unit220to the video encoder222via a digital video bus (not shown). An audio processing unit224and an audio codec (coder/decoder)226form a corresponding audio processing pipeline with high fidelity and stereo processing. Audio data is carried between the audio processing unit224and the audio codec226via a communication link (not shown). The video and audio processing pipelines output data to an A/V (audio/video) port228for transmission to the television or other display. In the illustrated implementation, the video and audio processing components220-228are mounted on the module214.
Also implemented on the module214are a USB host controller230and a network interface232. The USB host controller230is coupled to the CPU200and the memory controller202via a bus (e.g., PCI bus) and serves as host for the peripheral controllers1041and1042. The network interface232provides access to a network (e.g., Internet, home network, etc.) and may be any of a wide variety of various wired or wireless interface components including an Ethernet card, a modem, a Bluetooth module, a cable modem, and the like.
The game console102has a dual controller port subassembly240which supports the game controllers1041and1042. A front panel I/O subassembly242supports the functionality of the power button112and the eject button114, as well as any LEDs (light emitting diodes) or other indicators exposed on the outer surface of the game console. The subassemblies240and242are coupled to the module214via one or more cable assemblies244.
A system power supply module250provides power to the components of the gaming system100. A fan252cools the circuitry within the game console102.
The game console102implements a uniform media portal model that provides a consistent user interface and navigation hierarchy to move users through various entertainment areas. The portal model offers a convenient way to access content from multiple different media types—game data, audio data, and video data—regardless of the media type inserted into the portable media drive106.
To implement the uniform media portal model, a console user interface (“UI”) application260is stored on the hard disk drive105. When the game console is powered on, various portions of the console application260are loaded into RAM206and/or caches210and212and executed on the CPU200. The console application260presents a graphical user interface that provides a consistent user experience when navigating to different media types available on the game console.
The gaming system100may be operated as a standalone system by simply connecting the system to a television or other display. In this standalone mode, the gaming system100allows one or more players to play games, watch movies, or listen to music. However, with the integration of broadband connectivity made available through the network interface232, the gaming system100may further be operated as a participant in a larger network gaming community. This network gaming environment is described next.
FIG. 3shows an exemplary network gaming environment300that interconnects multiple gaming systems1001 . . . Nvia a network302. The network302represents any of a wide variety of data communications networks. It may include public portions (e.g., the Internet) as well as private portions (e.g., a residential Local Area Network (“LAN”)), as well as combinations of public and private portions. Network302may be implemented using any one or more of a wide variety of conventional communications media including both wired and wireless media. Any of a wide variety of communications protocols can be used to communicate data via network302, including both public and proprietary protocols. Examples of such protocols include TCP/IP (Transport Control Protocol/Internet Protocol), IPX/SPX (Internetwork Packet Exchange/Sequenced Packet Exchange), NetBEUI (NetBIOS Extended User Interface where BIOS stands for Basic Input/Output System), etc.
In addition to gaming systems100, one or more online services3041 . . . Nmay be accessible via the network302to provide various services for the participants, such as hosting online games, serving downloadable music or video files, hosting gaming competitions, serving streaming audio/video files, and the like. The network gaming environment300may further involve a key distribution center306that plays a role in authenticating individual players and/or gaming systems100to one another as well as online services304. The distribution center306distributes keys and service tickets to valid participants that may then be used to form games amongst multiple players or to purchase services from the online services304.
The network gaming environment300introduces another memory source available to individual gaming systems100, namely online storage. In addition to the portable media108, the hard disk drive105, and the memory unit(s)140, the gaming systems100can also access data files available at remote storage locations via the network302, as exemplified by remote storage308at online service304N.
FIG. 4is a block diagram of another illustrative online gaming environment400, e.g. XBOX® LIVE by Microsoft Corporation. Multiple game consoles4021, 2 . . . Nare coupled to a security gateway404via a network406. Each game console402can be configured in a similar manner as game console102ofFIG. 1orFIG. 2, for example. Network406represents any one or more of a variety of conventional data communications networks. Network406will typically include packet switched networks, but may also include circuit switched networks. Network406can include wired and/or wireless portions. In one exemplary implementation, network406includes the Internet and may optionally include one or more local area networks and/or wide area networks (“WANs”). At least a part of network406is a public network, which refers to a network that is publicly-accessible.
In some situations, network406includes a LAN (e.g., a home network), with a routing device situated between game console402and security gateway404. This routing device may perform network address translation (“NAT”), allowing the multiple devices on the LAN to share the same IP address on the Internet, and to operate as a firewall to protect the device(s) on the LAN from access by malicious or mischievous users via the Internet.
Security gateway404operates as a gateway between public network406and a private network408. Private network408can be any of a wide variety of conventional networks, such as a local area network. Private network408, as well as other devices discussed in more detail below, is within a data center410that operates as a secure zone. Data center410is made up of trusted devices that communicate using trusted communications. Thus, encryption and authentication within secure zone410is not necessary. The private nature of network408refers to the restricted accessibility of network408such that access to network408is limited to only certain individuals (e.g., restricted by the owner or operator of data center410).
Security gateway404is a cluster of one or more security gateway computing devices. These security gateway computing devices collectively implement security gateway404. Security gateway404may optionally include one or more conventional load balancing devices that operate to direct requests to be handled by the security gateway computing devices to appropriate ones of those computing devices. This directing or load balancing is performed in a manner that attempts to balance the load on the various security gateway computing devices approximately equally (or alternatively in accordance with some other criteria).
Also within data center410are: one or more monitoring servers412, one or more presence and notification front doors414, one or more presence servers416, one or more notification servers418, and a profile store428(collectively implementing a presence and notification service or system430), one or more match front doors420and one or more match servers422(collectively implementing a match service), and one or more statistics front doors424and one or more statistics servers426(collectively implementing a statistics service). The servers416,418,422, and426provide services to game consoles402, and thus can be referred to as service devices. Other service devices may also be included in addition to, and/or in place of, one or more of the servers416,418,422, and426. Additionally, although only one data center is shown inFIG. 4, alternatively, multiple data centers may exist with which game consoles402can communicate. These data centers may operate independently, or alternatively may operate collectively (e.g., to make one large data center available to the game consoles102and402).
Game consoles402are situated remotely from data center410, and may access data center410via network406. A game console402desiring to communicate with one or more devices in the data center logs in to the data center and establishes a secure communication channel between the game console402and security gateway404. Game console402and security gateway404encrypt and authenticate data packets being passed back and forth, thereby allowing the data packets to be securely transmitted between them without being understood by any other device that may capture or copy the data packets without breaking the encryption. Each data packet communicated from game console402to security gateway404, or from security gateway404to game console402, can have data embedded therein. This embedded data is referred to as the content or data content of the packet. Additional information may also be inherently included in the packet based on the packet type (e.g., a heartbeat packet).
The secure communication channel between a game console402and security gateway404is based on a security ticket. Game console402authenticates itself and the current user(s) of console402to a key distribution center450and obtains, from key distribution center450, a security ticket. Game console402then uses this security ticket to establish the secure communication channel with security gateway404. In establishing the secure communication channel with security gateway404, the game console402and security gateway404authenticate themselves to one another and establish a session security key that is known only to that particular game console402and the security gateway404. This session security key is used to encrypt data transferred between the game console402and the security gateway404, so no other devices (including other game consoles402) can read the data. The session security key is also used to authenticate a data packet as being from the security gateway404or game console402that the data packet alleges to be from. Thus, using such session security keys, secure communication channels can be established between the security gateway404and the various game consoles402.
Once the secure communication channel is established between a game console402and the security gateway404, encrypted data packets can be securely transmitted between the two. When the game console402desires to send data to a particular service device in data center410, the game console402encrypts the data and sends it to security gateway404requesting that it be forwarded to the particular service device(s) targeted by the data packet. Security gateway404receives the data packet and, after authenticating and decrypting the data packet, encapsulates the data content of the packet into another message to be sent to the appropriate service via private network408. Security gateway404determines the appropriate service for the message based on the requested service(s) targeted by the data packet.
Similarly, when a service device in data center410desires to communicate data to a game console402, the data center sends a message to security gateway404, via private network408, including the data content to be sent to the game console402as well as an indication of the particular game console402to which the data content is to be sent. Security gateway404embeds the data content into a data packet, and then encrypts the data packet so it can only be decrypted by the particular game console402and also authenticates the data packet as being from the security gateway404.
Although discussed herein as primarily communicating encrypted data packets between security gateway404and a game console402, alternatively some data packets may be partially encrypted (some portions of the data packets are encrypted while other portions are not encrypted). Which portions of the data packets are encrypted and which are not can vary based on the desires of the designers of data center410and/or game consoles402. For example, the designers may choose to allow voice data to be communicated among consoles402so that users of the consoles402can talk to one another—the designers may further choose to allow the voice data to be unencrypted while any other data in the packets is encrypted. Additionally, in another alternative, some data packets may have no portions that are encrypted (that is, the entire data packet is unencrypted). It is also noted that, even if a data packet is unencrypted or only partially encrypted, all of the data packet can still be authenticated.
Each security gateway device in security gateway404is responsible for the secure communication channel with typically one or more game consoles402, and thus each security gateway device can be viewed as being responsible for managing or handling one or more game consoles. The various security gateway devices may be in communication with each other and communicate messages to one another. For example, a security gateway device that needs to send a data packet to a game console that it is not responsible for managing may send a message to all the other security gateway devices with the data to be sent to that game console. This message is received by the security gateway device that is responsible for managing that game console and sends the appropriate data to that game console. Alternatively, the security gateway devices may be aware of which game consoles are being handled by which security gateway devices—this awareness may be explicit, such as each security gateway device maintaining a table of game consoles handled by the other security gateway devices, or alternatively, implicit, such as determining which security gateway device is responsible for a particular game console based on an identifier of the game console.
Monitoring server(s)412operate to inform devices in data center410of an unavailable game console402or an unavailable security gateway device of security gateway404. Game consoles402can become unavailable for a variety of different reasons, such as a hardware or software failure, the console being powered-down without logging out of data center410, the network connection cable to console402being disconnected from console402, other network problems (e.g., the LAN that the console402is on malfunctioning), etc. Similarly, a security gateway device of security gateway404can become unavailable for a variety of different reasons, such as hardware or software failure, the device being powered-down, the network connection cable to the device being disconnected from the device, other network problems, etc.
Each of the security gateway devices in security gateway404is monitored by one or more monitoring servers412, which detect when one of the security gateway devices becomes unavailable. In the event a security gateway device becomes unavailable, monitoring server412sends a message to each of the other devices in data center410(servers, front doors, etc.) that the security gateway device is no longer available. Each of the other devices can operate based on this information as it sees fit (e.g., it may assume that particular game consoles being managed by the security gateway device are no longer in communication with data center410and perform various clean-up operations accordingly). Alternatively, only certain devices may receive such a message from the monitoring server412(e.g., only those devices that are concerned with whether security gateway devices are available).
Security gateway404monitors the individual game consoles402and detects when one of the game consoles402becomes unavailable. When security gateway404detects that a game console is no longer available, security gateway404sends a message to monitoring server412identifying the unavailable game console. In response, monitoring server412sends a message to each of the other devices in data center410(or alternatively only selected devices) that the game console is no longer available. Each of the other devices can then operate based on this information as it sees fit.
Presence server(s)416holds and processes data concerning the status or presence of a given user logged in to data center410for online gaming. Notification server(s)418maintains multiple notification queues of outgoing messages destined for a player logged in to data center410. Presence and notification front door414is one or more server devices that operate as an intermediary between security gateway404and servers416and418. One or more load balancing devices (not shown) may be included in presence and notification front door414to balance the load among the multiple server devices operating as front door414.
Security gateway404communicates messages for servers416and418to the front door414, and the front door414identifies to which particular presence server416or particular notification server418the message is to be communicated. By using front door414, the actual implementation of servers416and418, such as which servers are responsible for managing data regarding which users, is abstracted from security gateway404. Security gateway404can simply forward messages that target the presence and notification service to presence and notification front door414and rely on front door414to route the messages to the appropriate one of server(s)416and server(s)418.
Match server(s)422holds and processes data concerning the matching of online players to one another. An online user is able to advertise a game available for play along with various characteristics of the game (e.g., the location where a football game will be played, whether a game is to be played during the day or at night, the user's skill level, etc.). These various characteristics can then be used as a basis to match up different online users to play games together. Match front door420includes one or more server devices (and optionally a load balancing device(s)) and operates to abstract match server(s)422from security gateway404in a manner analogous to front door414abstracting server(s)416and server(s)418.
Statistics server(s)426holds and processes data concerning various statistics for online games. The specific statistics used can vary based on the game designer's desires (e.g., the top ten scores or times, a world ranking for all online players of the game, a list of users who have found the most items or spent the most time playing, etc.). Statistics front door424includes one or more server devices (and optionally a load balancing device(s)) and operates to abstract statistics server(s)426from security gateway404in a manner analogous to front door414abstracting server(s)416and server(s)418.
Thus, it can be seen that security gateway404operates to shield devices in the secure zone of data center410from the untrusted public network406. Communications within the secure zone of data center410need not be encrypted, as all devices within data center410are trusted. However, any information to be communicated from a device within data center410to a game console402passes through security gateway cluster404, where it is encrypted in such a manner that it can be decrypted by only the game console402targeted by the information.
One or more features described herein may be embodied in computer-executable instructions (i.e., software) stored in RAM206, non-volatile memory108,105,308, or any other resident memory on game console102. Generally, software modules include routines, programs, objects, components, data structures, etc. that perform particular tasks or implement particular abstract data types when executed by a processor in a computer or other device. The computer executable instructions may be stored on a computer readable medium such as one or more hard disks105, portable storage media108(e.g., CD-ROM, DVD, disk, etc.), solid state memory, RAM206, etc. As will be appreciated by one of skill in the art, the functionality of the software modules may be combined or distributed as desired in various embodiments. In addition, the functionality may be embodied in whole or in part in firmware or hardware equivalents such as application specific integrated circuits (“ASIC”), field programmable gate arrays (“FPGA”), and the like.
Turning now toFIG. 5, shown is an illustrative set of game characters500split between “Team A”505and “Team B”511that may take part, for example, in an illustrative multiplayer video game such as an RPG or FPS game, or a game that uses a combination of both game genres. In this example, the teams505and511each include eight game characters that are controllable by respective human video game players. In alternative implementations, some of the characters on a team may be computer-controlled (i.e., non-game characters). It is also noted that the use of eight game characters on a team is merely illustrative and that other numbers of teammates may be used depending on the requirements of a specific implementation.
The game characters500on the teams505and511are typically user-definable in some ways. For example, there may be different class types of characters with distinct strengths and weaknesses from which players may choose to control. Some types of characters may be better able to use technology aids (like “wired reflexes” which makes the game character a lot faster and, if armed with a sword for example, able to deflect incoming bullets), while others are particularly adept at handling conventional weapons like guns, knives, and swords. As described below in the text accompanyingFIGS. 8 and 9, magical abilities are also supported in the multiplayer video game including the ability to resurrect teammates who are killed during the course of gameplay.
Players will typically make character selections, form teams, and decide which type of game to play (e.g., capture the flag; attrition, where one team tries to kill all the players on the other team; etc.) in a game lobby606as shown inFIG. 6. Once these initial selections are made, the gameplay itself will typically take place on one of several available maps6101, 2 . . . Nwhich are entered from the game lobby606. Typically the maps will differ in size and topology (as represented by the differently sized circles inFIG. 6) to thus present varied environments or “worlds” in which to play the video game.
In this example, as shown inFIG. 7, each match between the teams505and511is divided into rounds7011, 2 . . . N. Rounds can be any length of time, but in this example they are typically around four to five minutes. A game character's performance in each round earns that player money that can be spent on performance aids, or donated to other teammates. Generally, the more enemy kills, etc., that a game character makes during a round, the more spendable cash can be earned. In addition, as described below, cash can be generated for a game character by resurrecting dead teammates and then taking a portion of their earnings during the round.
At the beginning of each round7011, 2 . . . Nis a respective purchasing opportunity7151, 2 . . . Nthat is given to each of the game characters500on the teams505and511. At the beginning of the first round7011, the game characters500start with some set level of spendable cash. This set level may vary, in some cases, according to the character type chosen for example, or according to some other criteria. Thus, some of character types which may be stronger or endowed with other abilities may be given less spendable cash at the outset of the match compared with other characters. This ability to select the particular attributes or balance of strengths/weaknesses applied to a given character is often considered an enjoyable part of the gameplay.
At the beginning of a match between the teams505and511a particular game character might only be able to afford to purchase a few aids. However, as the rounds701progress and a game character earns more cash through performance, a host of magical abilities, technology, and weapons can often be accumulated. In addition, purchased items may be set in some scenarios so that they remain with a game character throughout a match, even if the game character is killed in a given round (i.e., the purchased items are still available to the game character when starting at the next round).
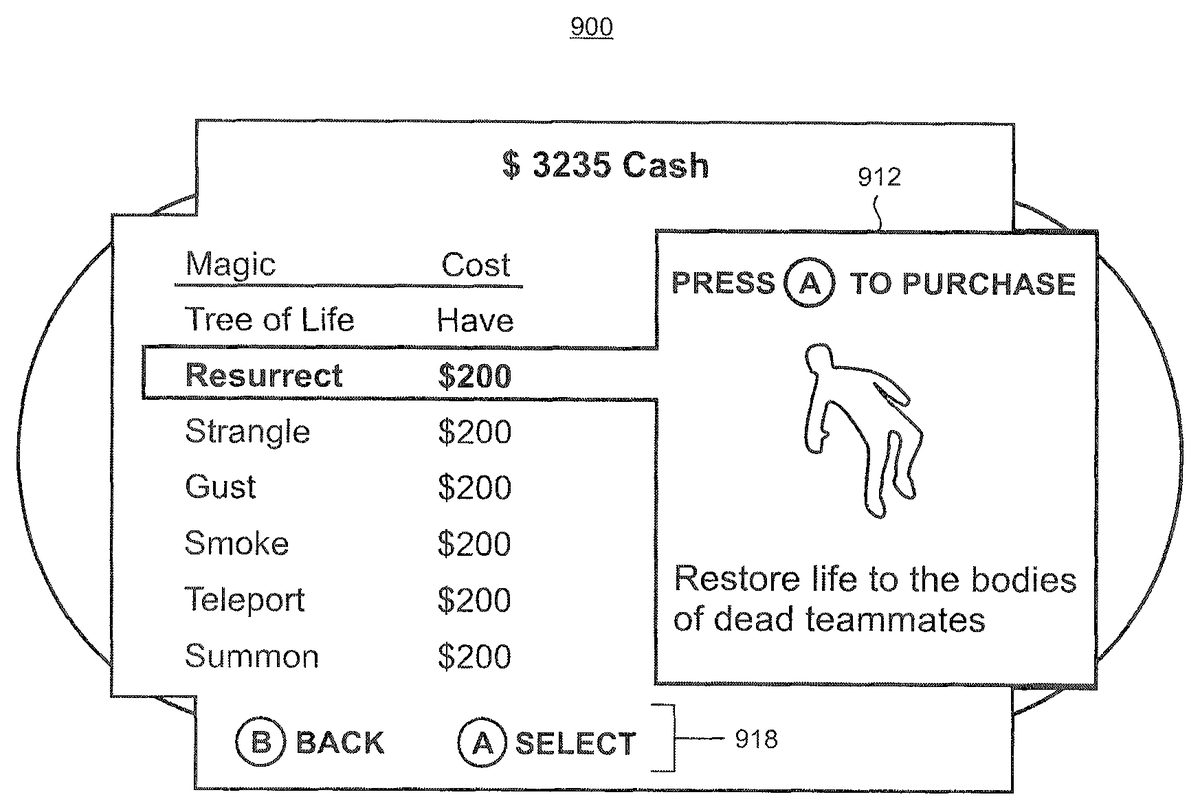
During a purchase opportunity715at a beginning of a round701, a game character is presented with a graphical user interface that is displayed by the game console102on the television118which shows a player's available spendable cash and a number of categories of items from which purchases may be made. An illustrative menu800provided by a user interface is shown in the screenshot inFIG. 8. As indicated by reference numeral810, one of the game characters500(named here “Player1”) has $3235 in cash that may be spent on items in categories of weapons, magic, technology, and team, as respectively indicated by reference numerals815,820,825, and830. The weapons category815comprises weapons such as guns and swords, and the like. The technology category825comprises a variety of devices such as devices that enable a user to see through walls, laser sights, and gliders. It is emphasized that these purchasable items are intended to be illustrative and that the particular items utilized in a given implementation can vary as may be required to meet specific needs.
The magic category820, when selected from the menu800, opens a menu900as shown in the screenshot inFIG. 9from which various types of magical abilities (i.e., “spells”) may be purchased by a game character prior to the start of each round. The menu900here lists a number of illustrative magical abilities including “Resurrect” which, when highlighted by the player as shown, provides a window912that provides a brief description of the magical ability (i.e., “restore life to the bodies of dead teammates”). Window912also includes purchasing instructions which the player can follow to effectuate the purchase of the Resurrect magical ability. In this example, the player can press the “A” button136on the controller104to make the purchase, or press the “B” button to go back to the previous menu800as collectively indicated by reference numeral918.
Once a game character has purchased the magical ability to resurrect dead teammates, the ability may be used in one or more of the rounds701during gameplay. In particular, the ability to resurrect dead teammates may be used to create “chains” of resurrected teammates, as shown inFIG. 10. In this example, a game character5001has previously purchased the Resurrect magical ability. Coming across a dead teammate5002wearing a black hat (1), the game character5001casts the Resurrect magical spell to resurrect game character5002and bring him back to life (2). Game character5001is deemed the master game character and game character5002the slave.
The resurrected game character5002engages in gameplay and then comes across a teammate5003wearing black shoes (3). Game character5002casts the Resurrect magic spell to bring game character5003back to life (4). In some cases, the game character5002needs to have previously purchased the Resurrect magical ability during a purchasing opportunity715to have his own independent ability to resurrect dead teammates. Alternatively, the game character5002may inherit the ability from the master game character5001and would not need to have the independent ability.
After resurrecting game character5003, the game character5002becomes the master for game character5003who becomes the slave. However, while a master for game character5003, the game character5002remains the slave to game character5001.
The previously resurrected game character5002continues to engage in gameplay and then comes across another dead teammate5004who is wearing a black belt (5). Game character5002casts another Resurrect magic spell to bring game character5004back to life (6). As above, after resurrecting game character5004, the game character5002becomes the master for game character5004while remaining the slave to game character5001.
In this example, the master-slave relationship is arranged to provide incentives for players to work cooperatively as teammates because when a master game character is killed, the slave to that master will also die. In some cases, the death of the slave will be immediate upon the death of the master. Alternatively, the slave game character can die more slowly (e.g., “bleed out”) over time while losing fighting prowess and ability. In that case, the slave game character will eventually die unless resurrected again by a teammate. Thus, for example, if the master game character5002is later killed during gameplay in the current round, then both slaves to that master (i.e., game characters5003and5004) will also die or bleed out over time unless resurrected again. If the master game character5001is killed, then all the slave came characters5002,5003, and5004will also die or eventually bleed out and die unless resurrected again. Having a game character's fate tied to a master game character will tend to make players be protective of their masters in their chain of resurrection as it is in their own interests to do so.
Financial incentives are provided to game characters to cooperate with their teammates. This is implemented through use of a pyramid payment system (i.e., a pyramid “scheme”) by which master game characters receive a split of the earnings of all their slave game characters in a resurrection chain. An illustrative resurrection chain1100is shown in block diagram form inFIG. 11which corresponds to the example resurrection chain scenario shown inFIG. 10. A game character in a tier of the resurrection chain1100is a master to a game character slave below it according to the dependency arrows shown. Accordingly, game character5001is the master of game character5002. Game character5002is the master of both game character5003and game character5004.
Although not demonstrated in the scenario shown inFIG. 10, it is possible for the resurrection chain1100to include all eight game characters on a team (e.g., team505or511) as shown by the dashed rectangles and dependency arrows. For example as shown inFIG. 11, game characters5005and5006could be resurrected by game character5003and become slaves to that master game character. And, game characters5007and5008could be slaves to the master game character5004. However, it is emphasized that the configuration of the resurrection chain1100could take any of a variety of different shapes with different dependencies in accordance with a given set of actions performed by the game characters during gameplay. For example, it is possible that the resurrection chain1100could be very flat with just a couple of tiers where one master game character resurrects many of his teammates. The resurrection chain1100might be tall and narrow where there are as many tiers as teammates. Or, there could be virtually any configuration that falls in between these two examples.
FIG. 12shows an illustrative distribution of earnings using a pyramid payment system for a resurrection chain1200that corresponds to the illustrative scenario shown inFIG. 10. In this example, it is assumed that game character5003earns $100 for an action that is performed during a round. As game character5003is a slave to his master game character5002, the $100 in earnings is split between the two game characters. A 50-50 split is used here which means that game character5003keeps $50 of the $100 in earnings and gives $50 to his master game character5002as a reward for the earlier resurrection. It is noted that money that is held by a game character inFIG. 12is shown in parentheses while money that moves to and from game characters is underlined. It is further noted that the 50-50 split is illustrative and other splits may also be used if desired.
As game character5002is also himself a slave to game character5001, under the pyramid payment system, the $50 reward received from game character5003is again split 50-50. The game character5002keeps $25 and the master game character5001receives $25 as a reward for resurrecting the game character5002.
Game character5001will continue to receive payments in the form of a split of the earnings for all the actions of all the slave game characters below him in the chain until the current round ends. Accordingly, it is possible to accumulate money that can be spent at the beginning of the next round merely by resurrecting fallen teammates. In addition, by virtue of being positioned at the top of the resurrection chain1200, when game character5001takes actions during the gameplay, the money earned for those actions is not split with any others as game character5001is not beholden to any other game characters.
Although the subject matter has been described in language specific to structural features and/or methodological acts, it is to be understood that the subject matter defined in the appended claims is not necessarily limited to the specific features or acts described above. Rather, the specific features and acts described above are disclosed as example forms of implementing the claims.
Claims
- A system for implementing a resurrection chain in a multiplayer game environment, comprising: a game console having a capability for executing programming to implement multiplayer gameplay;a data store accessible by the game console over a network, the data store comprising a plurality of profiles associated with unique game characters, the profiles tracking information associated with the resurrection chain which is configured for identifying master game characters and slave game characters;memory in communication with the game console bearing computer-readable instructions, said computer-readable instructions enabling game characters to resurrect dead teammates to implement the resurrection chain, a game character performing a resurrection being a master game character and a resurrected teammate being a slave game character, the resurrection chain arranging master game characters and slave game characters in hierarchical tiers so that a particular game character is simultaneously a master to a first game character and a slave to a second game character;and memory in communication with the game console bearing computer-readable instructions, said computer-readable instructions splitting earnings of the slave game characters with the master game characters.
- The system of claim 1 in which the network comprises at least one of public network infrastructure, a portion of which include the Internet, or private network infrastructure.
- The system of claim 1 in which the programming comprises a video game.
- The system of claim 1 further comprising memory in communication with the game console bearing computer-readable instructions capable of disabling resurrection for dead teammates whose bodies have been cleared from the gameplay.
- The system of claim 4 in which the bodies are cleared through actions of game characters on an opposing team.
- The system of claim 1 further comprising memory in communication with the game console bearing computer-readable instructions capable of tying the master game character to the slave game character so that death of the master game character during gameplay results in death of the slave game character.
- The system of claim 1 in which the death of the slave character occurs over a time interval during which capabilities of the slave character diminish.
- A computer-readable medium containing instructions which, when executed by one or more processors disposed in an electronic device, perform a method for operating a video game including game characters controlled by players, the method comprising the steps of: providing a facility for the game characters to be organized into teams;establishing a resurrection chain among the game characters on a team, the resurrection chain reflecting acts of resurrection performed by game characters to restore life to game characters killed during gameplay, the resurrection chain arranging master game characters and slave game characters in hierarchical tiers so that a particular game character is simultaneously a master to a first game character and a slave to a second game character;and sharing earnings of game characters according to their tier position on the resurrection chain, the earnings being obtained during gameplay as compensation for actions performed in the video game.
- The computer-readable medium of claim 8 in which the method includes a further step of terminating life of a resurrected game character when a game character performing an act of resurrection is killed during gameplay.
- The computer-readable medium of claim 8 in which the method includes a further step of providing purchase opportunities in which earnings may be utilized to purchase aids for game characters to progress through the video game.
- The computer-readable medium of claim 8 in which the facility comprises a game lobby.
- The computer-readable medium of claim 11 in which the game lobby is accessible over an Internet connection.
- The computer-readable medium of claim 8 in which the resurrection chain includes master game characters and slave game characters, a game character performing the resurrection being a master game character and a resurrected game character being a slave game character.
- The computer-readable medium of claim 8 in which the sharing comprises splitting using a pyramid payment system.
- A method for rewarding teamwork in a multiplayer video game, the method comprising the steps of: controlling gameplay in the video game so that game characters may earn money for actions performed, the money being spendable to purchase aids to assist the game characters to progress through the gameplay;providing game characters with an ability to resurrect teammates who are killed during gameplay to bring the teammates back to life, the resurrecting establishing a resurrection chain arranging master game characters and slave game characters in hierarchical tiers so that a particular game character is simultaneously a master to a first game character and a slave to a second game character;and implementing a pyramid payment system for splitting earnings of the resurrected teammates with the game characters who resurrected the resurrected teammates.
- The method of claim 15 including a further step of providing a user interface to facilitate the purchase of the aids.
- The method of claim 15 in which the aids comprise one of technology, magic, or weapons.
- The method of claim 15 in which the gameplay is conducted in rounds and the aids may be purchased prior to the start of each round.
- The method of claim 15 in which the splitting is performed on a 50-50 basis.
- The method of claim 15 in which the ability to resurrect teammates is a purchased aid.
Disclaimer: Data collected from the USPTO and may be malformed, incomplete, and/or otherwise inaccurate.