U.S. Pat. No. 7,654,903
ONLINE GAMING CHEATING PREVENTION SYSTEM AND METHOD
AssigneeCHARTOLEAUX KG LIMITED LIABILITY COMPANY
Issue DateDecember 21, 2006
U.S. Patent No. 7,654,903: Online gaming cheating prevention system and method
Summary:
The ‘903 patent describes a system which observes players playing online for any signs of cheating. For anyone who has played Halo online and been a victim of the “laggers,” this invention couldn’t come soon enough. While the players play their game, their data is sent to a separate server which analyzes the data for any signs of cheating. All of the servers which run the game are linked together and share information—this helps prevent cheaters from jumping from server-to-server and never getting caught. Whenever a player is caught cheating on a certain server, the player will be banned from that server. While he can still play on the other servers, he will never be allowed back on the server he has been banned from; this effectively prevents him from continuous cheating without being punished.
Abstract:
Technology is provided for preventing cheating during online gaming, including a first online gaming server computer system configured to gather information regarding cheaters detected during online gaming; a second online gaming server computer system configured to receive the information; and a central database configured for aggregating the received information regarding cheaters detected during online gaming gathered by the first online gaming server computer system along with information stored on the central database regarding cheaters detected during online gaming gathered from a plurality of online gaming server computer systems. The aggregated information from the central database regarding cheaters detected is made available to the second online gaming server computer system, and cheaters identified in the aggregated information are prevented from online gaming on the second online gaming server computer system based on the aggregated information from the central database.
Illustrative Claim:
1. A system for preventing cheating during online gaming, the system comprising: a first online gaming server computer system configured to gather information regarding cheaters detected during online gaming; a second online gaming server computer system configured to receive the information regarding cheaters detected during online gaming gathered by the first online gaming server computer system; and a central database configured to aggregate the received information regarding cheaters detected during online gaming gathered by the first online gaming server computer system along with information stored on the central database regarding cheaters detected during online gaming gathered from a plurality of online gaming server computer systems, wherein the aggregated information from the central database regarding cheaters detected during online gaming is made available to the second online gaming server computer system, whereby cheaters identified in the aggregated information from the central database are prevented from online gaming on the second online gaming server computer system based on the aggregated information from the central database.
Illustrative Figure
Abstract
Technology is provided for preventing cheating during online gaming, including a first online gaming server computer system configured to gather information regarding cheaters detected during online gaming; a second online gaming server computer system configured to receive the information; and a central database configured for aggregating the received information regarding cheaters detected during online gaming gathered by the first online gaming server computer system along with information stored on the central database regarding cheaters detected during online gaming gathered from a plurality of online gaming server computer systems. The aggregated information from the central database regarding cheaters detected is made available to the second online gaming server computer system, and cheaters identified in the aggregated information are prevented from online gaming on the second online gaming server computer system based on the aggregated information from the central database.
Description
DETAILED DESCRIPTION OF THE PREFERRED EMBODIMENTS An online gaming cheater prevention system and method are described. In the following description, for purposes of explanation, numerous specific details are set forth in order to provide a thorough understanding of the present invention. It is apparent to one skilled in the art, however, that the present invention may be practiced without these specific details or with an equivalent arrangement. In some instances, well-known structures and devices are shown in block diagram form in order to avoid unnecessarily obscuring the present invention. Referring now to the drawings, wherein like reference numerals designate identical or corresponding parts throughout the several views, and more particularly toFIG. 1thereof, there is illustrated an online gaming cheater prevention system100, according to an embodiment of the present invention. InFIG. 1, generally, the cheater prevention system100provides for centralization and sharing of a master file117of identified online gaming cheaters. The system100includes, for example, a cheating prevention Server Module, including one or more master servers101and master databases107, and a cheater prevention server program or software111. The system100further includes, for example, a cheating prevention Client Module, including one or more individual game servers103, a cheater prevention client program or software113, and a cheat detection program115. The master server101communicates with the master database107for storing information about identified cheating players, for example, including Internet Protocol (IP) addresses of the cheating players, in-game names or handles of the cheating players, unique online gaming identifications (IDs, e.g., WonIDs used in several popular online games, etc.) of the cheating players, etc. The cheater prevention server program111running on the master server101handles the connection with the cheater prevention client programs113running on the game servers103and interacts with the master database107. The cheater prevention client program113and the cheat detection or anti-cheat program115reside on the individual game servers103. The master database107receives instructions (e.g., ...
DETAILED DESCRIPTION OF THE PREFERRED EMBODIMENTS
An online gaming cheater prevention system and method are described. In the following description, for purposes of explanation, numerous specific details are set forth in order to provide a thorough understanding of the present invention. It is apparent to one skilled in the art, however, that the present invention may be practiced without these specific details or with an equivalent arrangement. In some instances, well-known structures and devices are shown in block diagram form in order to avoid unnecessarily obscuring the present invention.
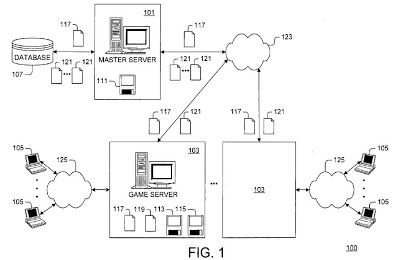
Referring now to the drawings, wherein like reference numerals designate identical or corresponding parts throughout the several views, and more particularly toFIG. 1thereof, there is illustrated an online gaming cheater prevention system100, according to an embodiment of the present invention.
InFIG. 1, generally, the cheater prevention system100provides for centralization and sharing of a master file117of identified online gaming cheaters. The system100includes, for example, a cheating prevention Server Module, including one or more master servers101and master databases107, and a cheater prevention server program or software111. The system100further includes, for example, a cheating prevention Client Module, including one or more individual game servers103, a cheater prevention client program or software113, and a cheat detection program115.
The master server101communicates with the master database107for storing information about identified cheating players, for example, including Internet Protocol (IP) addresses of the cheating players, in-game names or handles of the cheating players, unique online gaming identifications (IDs, e.g., WonIDs used in several popular online games, etc.) of the cheating players, etc. The cheater prevention server program111running on the master server101handles the connection with the cheater prevention client programs113running on the game servers103and interacts with the master database107. The cheater prevention client program113and the cheat detection or anti-cheat program115reside on the individual game servers103.
The master database107receives instructions (e.g., database update instructions, database query instructions, etc.) from the cheater prevention server program111. The master database107also receives, via the cheater prevention server program111, new cheater entries or information121extracted by the cheater prevention client programs113from cheater log files119of cheaters detected on and/or banned from the game servers103. Accordingly, the master server101communicates with the master database107and the cheater prevention server program111. The game servers103provide online game connectivity for one or more online gaming clients105.
The software portion of the cheater prevention Client Module resides on the game servers103and includes the cheat detection and/or logging program115(e.g., HLGuard, CSGaurd, etc.) and the cheater prevention client program or software113. The cheater prevention client program113provides connectivity between the cheater prevention client program113of the Client Module and the cheater prevention server program111of the Server Module.
Accordingly, the devices and subsystems of the cheater prevention system100ofFIG. 1can include, for example, any suitable servers, workstations, personal computers (PCs), laptop computers, PDAs, Internet appliances, set top boxes, modems, handheld devices, telephones, cellular telephones, wireless devices, other devices, etc., capable of performing the processes of the embodiments of the present invention. The devices and subsystems can communicate with each other using any suitable protocol and can be implemented using the computer system500ofFIG. 5, for example. One or more interface mechanisms can be used in the system100including, for example, Internet access, telecommunications in any form (e.g., voice, modem, etc.), wireless communications media, etc.
Accordingly, communications network123connecting the master sever101with the game servers103and communications network125connection the game servers103with the online gaming clients105can include, for example, wireless communications networks, cellular communications networks, G3 communications networks, Public Switched Telephone Networks (PSTNs), Packet Data Networks (PDNs), the Internet, intranets, etc. In addition, the communications networks123and125can be the same or different networks, as will be appreciated by those skilled in the relevant art(s).
It is to be understood that the system100ofFIG. 1is for exemplary purposes, as many variations of the specific hardware used to implement the embodiments of the present invention are possible, as will be appreciated by those skilled in the relevant art(s). For example, the functionality of the devices and the subsystems of the system100can be implemented via one or more programmed computer systems or devices.
To implement such variations as well as other variations, a single computer system (e.g., the computer system500ofFIG. 5) can be programmed to perform the special purpose functions of one or more of the devices and subsystems of the system100. On the other hand, two or more programmed computer systems or devices can be substituted for any one of the devices and subsystems of the system100. Accordingly, principles and advantages of distributed processing, such as redundancy, replication, etc., also can be implemented, as desired, to increase the robustness and performance of the system100, for example.
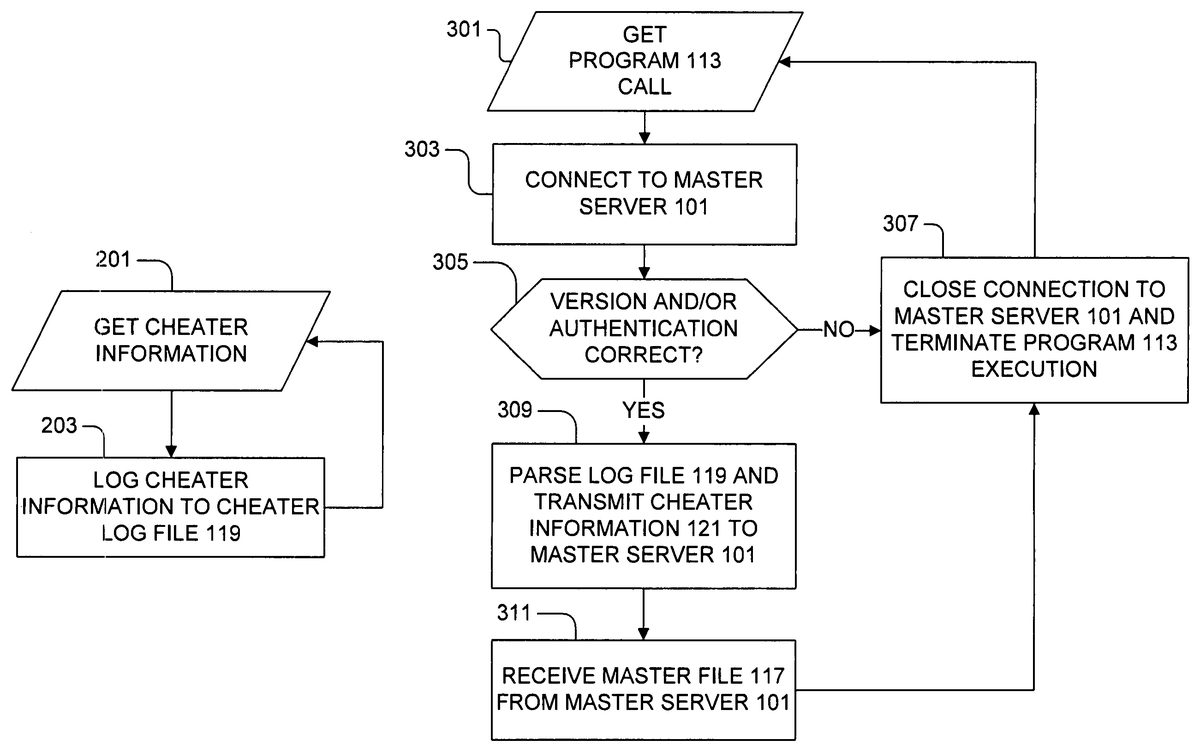
FIG. 2is a flowchart depicting processes performed by an exemplary cheater detection program115running on the game servers103ofFIG. 1. As the online game clients or players105connect to the game server103, the cheat detection/logging program115scans for the clients105using known or suspected cheats. Upon detection of a cheating client or player105, the relevant information about the cheater is logged to the cheater log file119by the cheat detection/logging software115. Accordingly, inFIG. 2, at step201, the cheater detection/logging program115gets detected cheater information and logs the cheater information to the log file119, at step203. Execution then returns to step201, completing the cheater information logging processing.
FIG. 3is a flowchart depicting processes performed by an exemplary cheater prevention client program113running on the game servers103ofFIG. 1. Generally, the cheater log file119is read and parsed by the cheater prevention client program113. Then, when the cheater prevention client program113is appropriately commanded or called, the cheater prevention client program113attempts to connect to the master server101to transmit the cheater information121.
Accordingly, inFIG. 3, at step301, the cheater prevention client program113is called and then connects to the master server101, at step303. Once a stable connection is established between the master server101and the game server103, at step305, the cheater prevention client program113waits for the cheater prevention server program111to perform an authentication process. The authentication process can be performed, for example, by the cheater prevention server program111comparing the IP address associated with the game server103running the cheater prevention client program113with a list of authorized game servers103and/or by checking a security password. This feature, however, is optional and no authentication can be performed, if desired.
If the authentication fails, the connection is closed, at step307. Otherwise, upon positive authentication or upon disabling of the authentication feature, the cheater prevention client program113waits for the cheater prevention server program111to verify software versions to ensure compatibility, at step305. If the version comparison fails, the connection can be terminated, at step307.
Otherwise, at step309, the cheater prevention client program113reads and parses the cheater log file119generated by the anti-cheat software115and transmits the cheater information121extracted from the log file119to the master server101. Then, at step311, the master server101then appends and stores the new cheater entries from the cheater information121into the master file117on the master database107. The cheater prevention client program113then receives the master file117of the cheaters identified by the various game servers103from the master server101.
The cheater prevention client program113, at step311, also stores the cheater information from the master file117into one or more files that can be read by online gaming software running on the game server103. Advantageously, the cheating players listed in the master file117are automatically banned by the online gaming software on the game server103. Then, at step307, the cheater prevention client program113closes the connection with the master server101and terminates execution, and returns to step301to wait for the next program call, completing the cheater prevention client process.
FIG. 4is a flowchart depicting processes performed by an exemplary cheater prevention server program111running on the master server101. As noted above, the Server Module includes, for example, the master database107, including the master list117of cheaters, and the cheater prevention server program or software111. Accordingly, inFIG. 4, at step401, the cheater prevention server program111listens for or gets connection requests from the cheater prevention client programs113running on the game servers103.
When a connection is requested and after a connection is established, at step403, the cheater prevention server program111optionally performs the previously described authentication process, followed by the previously described version checking process, at step405, and closes the connection, at step407, if necessary. Otherwise, at step409, the cheater prevention server program111receives the cheater information121, parsed from the log file119by the cheater prevention client program113, from the cheater prevention client program113. Then, at step411, the cheater prevention server program111transmits the updated master file117to the cheater prevention client program113. The connection is then closed, at step407, and control returns to step401for further cheater information121processing, completing the cheater prevention server process.
An exemplary implementation of the present invention will now be described. The cheater prevention program (e.g., written in Perl, C++, etc.), including the Server and Client modules, allows the online game (e.g., Half-Life, Counter-strike, etc.) servers103to transmit the cheater information121regarding cheaters during online games to the master database107and automatically receive master files117of cheaters (e.g., banned cheaters) from participating game servers103from the master database107. The cheater prevention client program113automatically parses the anti-cheat program115(e.g., CSGuard, HLGuard, etc.) log files119of detected online game cheaters that are in a standard log format and transmits the cheater information121to the master server101, where the data is stored in the master file117on the master database107by the server module. Game server plugins115(e.g., CSGuard, HLGuard, etc.) perform the cheater detection on the individual game servers103.
The cheater prevention program113can be implemented, for example, as a standalone executable program. The cheater prevention client program113can work in conjunction with an automatic execution scheduling program (e.g., Cron, etc.) for scheduled execution operation. The client program113runs on an Operating System (OS) capable of running a dedicated game server103, such as a Half-Life Dedicated Server (HLDS), etc., and remote system access can be employed. In a preferred embodiment, the client program113is not configured as a server module or a plugin (e.g., an adminmod plugin, etc.) so that the client program113is not run via file transfer protocol (FTP), etc. However, the client program113can be configured as a server module or a plugin (e.g., an adminmod plugin, etc.) so that the client program113can run via FTP, etc., as will be appreciated by those skilled in the relevant art(s)
As noted above, the cheater prevention client program113works on systems that support online games (e.g., Half-Life with any of the various configurations, etc.). In the Windows environment, the master file117and the cheater log file119(e.g., a *.cfg file, etc.) paths employ forward slashes (“/”) rather than the standard Windows backslash (“\”). Accordingly, the path “c:\Windows\Desktop” would be written as “c:/Windows/Desktop.”
Although an infinite number of possible log formats can be employed, the cheater prevention client program113employs a standard log format. Accordingly, an end user of the online game server103can add a line to the configuration file of the anti-cheat detection program115(e.g., CSGuard, HLGuard, etc.) to appropriately format output for the cheater prevention client program113. For example, the standard log format can be given by:mm/dd/yyyy:cheatername:wonid:ip:cheattype
where mm/dd/yyyy is a timestamp in month, day, and year format, cheatername is an online handle or name used by a detected cheater, wonid is an online gaming identification (e.g., a WON identification) of the detected cheater, ip is an Internet Protocol (IP) address of the online gaming client105of the detected cheater, and cheattype is the type of online game cheat detected.
The data that is relevant to cheater prevention program113, for example, is included in a single string separated by colons. Advantageously, this simple yet effective format all but eliminates the chance for errors in parsing and conserves memory space and bandwidth. For most anti-cheat detection programs115, one line can be added to the configuration file. For example, in the case of the HLGuard anti-cheat detection program115, the following line is added to the configuration file (e.g., csgconfig.cfg):csg_action “b:found” “csg_writefile cstrike/cheaterlist.txt; csg_write \‘%d:%n:%w:%i:%y\’”
where cheaterlist.txt is the cheater log file119that the detected cheater information is stored in, %d:%n:%w:%i:%y is the standard format described above, and the remaining terms are commands specific to the HLGuard anti-cheat detection program115.
In the above example, the added command line is written as one line (e.g., not including any hard returns). In a similar manner, other types of anti-cheat detection programs115can be configured to support the Standard format. If the game server103is rented from a hosting company (e.g., Martnet, TheNetGamer, etc.), the hosting company can technically support the cheater prevention program113by providing any necessary system and program access and permit use of the program113.
In a preferred embodiment, only cheaters who are actually banned from a game server103are added to the master file117. Otherwise, minor offenders and questionable cheaters (e.g., cheaters detected by methods that are potentially faulty, such as aimbot detection, etc.) can get added to the master file117, leading to undesirable results.
The cheater prevention client program113can be installed by storing the executable program file scripts on the game server103where the anti-cheat program115cheater log files119are stored. This usually entails some sort of shell access to the game server103. As noted above, the configuration file (e.g., csgconfig.cfg) for the anti-cheat program115can be modified to support the Standard log format. In addition, in the case of the cheater prevention client program113being implemented via a Perl script, Perl script support can be installed on the game server103.
Accordingly, the above process includes extracting executable and other program files (e.g., filename.tar.gz) to a directory where the client program113is to reside. For example, this creates an installation instruction file (e.g., Readme.txt), an executable file, (e.g., client.pl) and a configuration file (e.g., config.cfg) for the cheater prevention client program113.
Advantageously, variables in the cheater prevention client program113configuration file can be edited for user customization. For example, the configuration file can include the following variables:allowupload=1;allowdownload=1;
where these variables control what action the client program113performs when the client program113connects to the master server101. For example, the allowupload variable determines whether or not the client program113is to parse the cheater log file119and upload the cheater information121to the master server101. The allowdownload variable determines whether or not the client program113is to download the latest version of the master file117from the master server101. In both cases, for example, a setting of “1” enables the specified function.
The configuration file also can include the following variable:port=0;
where this variable control which port on the game server103is used by the client program113. For example, users behind a firewall can specify a port for the client program113to use via the port variable. If the port variable is set to zero, a random port can be employed.
The configuration file also can include the following variables:bannedfilepath=/path/to/csbl_banned.cfg;cheaterlistpath=/path/to/cheaterlist.txt;
where these variables control which files the client program113uses for its operations. For example, the bannedfilepath variable is the full path to the file that the client program113writes to when it downloads a new master file117(e.g., csbl_banned.cfg) from the master server101. By default, this file is given a different name than the cheater log file119(e.g., banned.cfg), so that it will not overwrite the original cheater log file119of the anti-cheat detection program115. If another name is used, exec yourbannedfilename.cfg can be added to the config.cfg file of the game server103. The csbl_banned.cfg file gets overwritten every time a new master file117is downloaded from the master server101. The cheaterlistpath variable is the full path to the file cheaterlist.txt that contains the anti-cheat detection program115output cheater log file119in the Standard log format.
The configuration file also can include the following variable:verbose=0;
where this variable controls verbose logging. When turned on by being set to a value of 1, details of data transfers are logged for debugging purposes.
The configuration file also can include the following variable:password=nopass;
where this variable controls the client program113authentication on the master server101. When turned off by being set to a value of nopass, no authentication is performed by the master server101. Otherwise, the password variable can be set with a valid security password used by the master server101for authentication purposes. In this way, the client program113hosts with invalid security passwords will not be allowed to connect to the master server101.
The configuration file also can include the following variable:max_filesize=1500;
where this variable is employed for game servers103having an excessive number of banned player entries (e.g., banid) in a single *.cfg file, which can cause lag, slow game map changes and even crash the game server103. In one embodiment, the client program113automatically distributes the cheater entries to several different files. In this case, these files take the format of the csbl_banned.cfg file name followed by a number (e.g., csbl_banned1.cfg). The csbl_banned.cfg file executes each of such files in sequence. Accordingly, adding exec csbl_banned.cfg to the game server103server.cfg file is sufficient. The max_filesize variable controls the maximum number of cheater entries that can be placed in each of such files. Advantageously, if the game server103is experiencing lag or crash problems, the value assigned to this variable can be adjusted, as necessary.
As noted above, the configuration file (e.g., csgconfig.cfg for CSGuard, etc.) for the anti-cheat detection program115can be edited to create detected cheater log files119in the Standard format. Otherwise, the parser in the client program113may not work with other formats, including any default anti-cheat program115formats. However, the client program113can be configured to support formats used by the anti-cheat program115, as will be appreciated by those skilled in the relevant art(s).
In addition, since the client program113downloads the latest master file117to a specified file, a single line can be added to the configuration file (e.g., server.cfg, autoexec.cfg, etc.) of the game server103. For example, if the master file117is called csbl_banned.cfg (e.g., the default name), the following line can be added:exec csbl_banned.cfg
Otherwise, if the master file117is called something other than csbl_banned.cfg, the corresponding filename can be substituted for csbl_banned.cfg.
As noted above, for scheduled execution, a program (e.g., Cron) can be used to schedule the client program113(e.g., client.pl) to run automatically. For example, a Cron job to run the client program113can be scheduled. Although it does not really matter how often the client program113is run, running the client program113once daily is adequate for most game servers103. Advantageously, such a schedule will ensure that the master file117is updated daily and that new cheaters are logged every time the client program113runs.
For example, for scheduling the running of the client program113once daily, a crontab of the Cron program can be given by:# Run client program once daily@daily /path/to/client-os
where the real path to the client program113executable is used in place of path, and the actual name and version for the client program113is used in place of client.
Otherwise, manual operation or other programs can be employed to schedule the execution of the client program113. However, the client program113can be modified to perform automatically scheduled execution, as will be appreciated by those skilled in the relevant art(s).
Accordingly, the above and other features of the present invention include, for example, enabling or disabling of client program113authentication at the master server101; optimized network communications; automatic generation of multiple sequential csbl_banned.cfg files to address potential game server lag and efficient program operation; printing of various client program113output to console, as an indication that the client program113is working properly; providing routines for terminating a connection to the master server101to reduce hangs; including a SO_KEEPALIVE variable so dead clients113get pushed out of the connection queue faster; providing a verbose logging configuration option; providing an executable for other systems (e.g., libc5 Linux systems, etc.); logging and printing of an error if a new version of the client program113exists; database queries that do no take place during the client/server interaction to speed program operation; user selection of a port for use by the client program113; and use of a timeout value for the client program113, so connections to the master server101do not hang.
The system100can store information relating to various processes described herein. This information can be stored in one or more memories, such as a hard disk, optical disk, magneto-optical disk, RAM, etc., of the devices of system100One or more databases of the devices and subsystems of the system100ofFIG. 1can store the information used to implement the embodiments of the present invention. The databases can be organized using data structures (e.g., records, tables, arrays, fields, graphs, trees, and/or lists) included in one or more memories, such as the memories listed above or any of the storage devices listed below in the discussion ofFIG. 5, for example.
The previously described processes can include appropriate data structures for storing data collected and/or generated by the processes of the system100ofFIG. 1in one or more databases thereof. Such data structures accordingly can include fields for storing such collected and/or generated data. In a database management system, data can be stored in one or more data containers, each container including records, and the data within each record can be organized into one or more fields. In relational database systems, the data containers can be referred to as tables, the records can be referred to as rows, and the fields can be referred to as columns. In object-oriented databases, the data containers can be referred to as object classes, the records can be referred to as objects, and the fields can be referred to as attributes. Other database architectures can be employed and use other terminology. Systems that implement the embodiments of the present invention are not limited to any particular type of data container or database architecture.
All or a portion of the system100(e.g., as described with respect toFIGS. 1-4) can be conveniently implemented using one or more conventional general purpose computer systems, microprocessors, digital signal processors, micro-controllers, etc., programmed according to the teachings of the embodiments of the present invention (e.g., using the computer system ofFIG. 5), as will be appreciated by those skilled in the computer and software art(s). Appropriate software can be readily prepared by programmers of ordinary skill based on the teachings of the present disclosure, as will be appreciated by those skilled in the software art. Further, the system100can be implemented on the World Wide Web (e.g., using the computer system ofFIG. 5). In addition, the system100(e.g., as described with respect toFIGS. 1-4) can be implemented by the preparation of application-specific integrated circuits or by interconnecting an appropriate network of conventional component circuits, as will be appreciated by those skilled in the electrical art(s).
FIG. 5illustrates a computer system500upon which the embodiments of the present invention (e.g., the devices and subsystems of the system100ofFIG. 1) can be implemented. The embodiments of the present invention can be implemented on a single such computer system, or a collection of multiple such computer systems. The computer system500can include a bus501or other communication mechanism for communicating information, and a processor503coupled to the bus501for processing the information. The computer system500also can include a main memory505, such as a random access memory (RAM), other dynamic storage device (e.g., dynamic RAM (DRAM), static RAM (SRAM), synchronous DRAM (SDRAM)), etc., coupled to the bus501for storing information and instructions to be executed by the processor503.
In addition, the main memory505also can be used for storing temporary variables or other intermediate information during the execution of instructions by the processor503. The computer system500further can include a ROM507or other static storage device (e.g., programmable ROM (PROM), erasable PROM (EPROM), electrically erasable PROM (EEPROM), etc.) coupled to the bus501for storing static information and instructions.
The computer system500also can include a disk controller509coupled to the bus501to control one or more storage devices for storing information and instructions, such as a magnetic hard disk511, and a removable media drive513(e.g., floppy disk drive, read-only compact disc drive, read/write compact disc drive, compact disc jukebox, tape drive, and removable magneto-optical drive). The storage devices can be added to the computer system500using an appropriate device interface (e.g., small computer system interface (SCSI), integrated device electronics (IDE), enhanced-IDE (E-IDE), direct memory access (DMA), or ultra-DMA).
The computer system500also can include special purpose logic devices515, such as application specific integrated circuits (ASICs), full custom chips, configurable logic devices (e.g., simple programmable logic devices (SPLDs), complex programmable logic devices (CPLDs), field programmable gate arrays (FPGAs), etc.), etc., for performing special processing functions, such as signal processing, image processing, speech processing, voice recognition, communications functions, etc.
The computer system500also can include a display controller517coupled to the bus501to control a display519, such as a cathode ray tube (CRT), liquid crystal display (LCD), active matrix display, plasma display, touch display, etc., for displaying or conveying information to a computer user. The computer system can include input devices, such as a keyboard521including alphanumeric and other keys and a pointing device523, for interacting with a computer user and providing information to the processor503. The pointing device523can include, for example, a mouse, a trackball, a pointing stick, etc., or voice recognition processor, etc., for communicating direction information and command selections to the processor503and for controlling cursor movement on the display519. In addition, a printer can provide printed listings of the data structures/information of the system shown inFIG. 1, or any other data stored and/or generated by the computer system500.
The computer system500can perform a portion or all of the processing steps of the invention in response to the processor503executing one or more sequences of one or more instructions contained in a memory, such as the main memory505. Such instructions can be read into the main memory505form another computer readable medium, such as the hard disk511or the removable media drive513. Execution of the arrangement of instructions contained in the main memory505causes the processor503to perform the process steps described herein. One or more processors in a multi-processing arrangement also can be employed to execute the sequences of instructions contained in the main memory505. In alternative embodiments, hard-wired circuitry can be used in place of or in combination with software instructions. Thus, embodiments are not limited to any specific combination of hardware circuitry and/or software.
Stored on any one or on a combination of computer readable media, the embodiments of the present invention can include software for controlling the computer system500, for driving a device or devices for implementing the invention, and for enabling the computer system500to interact with a human user (e.g., users of the system100ofFIG. 1, etc.). Such software can include, but is not limited to, device drivers, firmware, operating systems, development tools, applications software, etc. Such computer readable media further can include the computer program product of an embodiment of the present invention for performing all or a portion (if processing is distributed) of the processing performed in implementing the invention. Computer code devices of the embodiments of the present invention can include any interpretable or executable code mechanism, including but not limited to scripts, interpretable programs, dynamic link libraries (DLLs), Java classes and applets, complete executable programs, Common Object Request Broker Architecture (CORBA) objects, etc. Moreover, parts of the processing of the embodiments of the present invention can be distributed for better performance, reliability, and/or cost.
The computer system500also can include a communication interface525coupled to the bus501. The communication interface525can provide a two-way data communication coupling to a network link527that is connected to, for example, a local area network (LAN)529, or to another communications network533(e.g. a wide area network (WAN), a global packet data communication network, such as the Internet, etc.). For example, the communication interface525can include a digital subscriber line (DSL) card or modem, an integrated services digital network (ISDN) card, a cable modem, a telephone modem, etc., to provide a data communication connection to a corresponding type of telephone line. As another example, the communication interface525can include a local area network (LAN) card (e.g., for Ethernet™, an Asynchronous Transfer Model (ATM) network, etc.), etc., to provide a data communication connection to a compatible LAN. Wireless links can also be implemented. In any such implementation, the communication interface525can send and receive electrical, electromagnetic, or optical signals that carry digital data streams representing various types of information. Further, the communication interface525can include peripheral interface devices, such as a Universal Serial Bus (USB) interface, a PCMCIA (Personal Computer Memory Card International Association) interface, etc.
The network link527typically can provide data communication through one or more networks to other data devices. For example, the network link527can provide a connection through the LAN529to a host computer531, which has connectivity to the network533or to data equipment operated by a service provider. The LAN529and the network533both can employ electrical, electromagnetic, or optical signals to convey information and instructions. The signals through the various networks and the signals on the network link527and through the communication interface525, which communicate digital data with computer system500, are exemplary forms of carrier waves bearing the information and instructions.
The computer system500can send messages and receive data, including program code, through the network529and/or533, the network link527, and the communication interface525. In the Internet example, a server can transmit requested code belonging to an application program for implementing an embodiment of the present invention through the network533, the LAN529and the communication interface525. The processor503can execute the transmitted code while being received and/or store the code in the storage devices511or513, or other non-volatile storage for later execution. In this manner, computer system500can obtain application code in the form of a carrier wave. With the system ofFIG. 5, the embodiments of the present invention can be implemented on the Internet as a Web Server500performing one or more of the processes according to the embodiments of the present invention for one or more computers coupled to the web server500through the network533coupled to the network link527.
The term “computer readable medium” as used herein can refer to any medium that participates in providing instructions to the processor503for execution. Such a medium can take many forms, including out not limited to, non-volatile media, volatile media, transmission media, etc. Non-volatile media can include, for example, optical or magnetic disks, magneto-optical disks, etc., such as the hard disk511or the removable media drive513. Volatile media can include dynamic memory, etc., such as the main memory505. Transmission media can include coaxial cables, copper wire and fiber optics, including the wires that make up the bus501. Transmission media can also take the form of acoustic, optical, or electro-magnetic waves, such as those generated during radio frequency (RF) and infrared (IR) data communications.
As stated above, the computer system500can include at least one computer readable medium or memory for holding instructions programmed according to the teachings of the invention and for containing data structures, tables, records, or other data described herein. Common forms of computer-readable media can include, for example, a floppy disk, a flexible disk, hard disk, magnetic tape, any other magnetic medium, a CD-ROM, CDRW, DVD, any other optical medium, punch cards, paper tape, optical mark sheets, any other physical medium with patterns of holes or other optically recognizable indicia, a RAM, a PROM, and EPROM, a FLASH-EPROM, any other memory chip or cartridge, a carrier wave, or any other medium from which a computer can read.
Various forms of computer-readable media can be involved in providing instructions to a processor for execution. For example, the instructions for carrying out at least part of the embodiments of the present invention can initially be borne on a magnetic disk of a remote computer connected to either of the networks529and533. In such a scenario, the remote computer can load the instructions into main memory and send the instructions, for example, over a telephone line using a modem. A modem of a local computer system can receive the data on the telephone line and use an infrared transmitter to convert the data to an infrared signal and transmit the infrared signal to a portable computing device, such as a personal digital assistant (PDA), a laptop, an Internet appliance, etc. An infrared detector on the portable computing device can receive the information and instructions borne by the infrared signal and place the data on a bus. The bus can convey the data to main memory, from which a processor retrieves and executes the instructions. The instructions received by main memory can optionally be stored on storage device either before or after execution by processor.
Although the present invention is described in terms or applications in online gaming over a communications network123and/or125, such as the Internet, the present invention can be applied to online gaming over other communications networks, such as intranets, extranets, Local Area Networks (LANs), etc., as will be appreciated by those skilled in the relevant art(s). For example, the communications network125can be an intranet for hosting a LAN online gaming session. In this case, cheaters identified by the anti-cheat software115can be transmitted to the master server101via the cheater prevention client program113over the communications network123, including the Internet.
Although the present invention is described in terms of cheating prevention client and server programs separate from cheat detection and/or gaming server programs, the cheating prevention client and/or server programs can be implemented as modules included within the cheat detection and/or gaming server programs, as will be appreciated by those skilled in the relevant art(s).
While the present invention have been described in connection with a number of embodiments and implementations, the present invention is not so limited but rather covers various modifications and equivalent arrangements, which fall within the purview of the appended claims.
Claims
- A system for preventing cheating during online gaming, the system comprising: a first online gaming server computer system configured to gather information regarding cheaters detected during online gaming;a second online gaming server computer system configured to receive the information regarding cheaters detected during online gaming gathered by the first online gaming server computer system;and a central database configured to aggregate the received information regarding cheaters detected during online gaming gathered by the first online gaming server computer system along with information stored on the central database regarding cheaters detected during online gaming gathered from a plurality of online gaming server computer systems, wherein the aggregated information from the central database regarding cheaters detected during online gaming is made available to the second online gaming server computer system, whereby cheaters identified in the aggregated information from the central database are prevented from online gaming on the second online gaming server computer system based on the aggregated information from the central database.
- The system of claim 1 , further comprising a plurality of cheater detection programs configured to gather the received information, wherein the received information is made available to at least one of an online gaming cheater detection program and online gaming server program running on the second online gaming server computer system.
- The system of claim 1 , further comprising: a cheater detection program running on the second online gaming server computer system configured to detect cheaters during online gaming, wherein the second online gaming server computer system is configured to extract information regarding cheaters during online gaming from output of the cheater detection program running on the second online gaming server computer system, and the second online gaming server computer system is configured to transmit the extracted information regarding cheaters during online gaming to the first online gaming server computer system.
- The system of claim 3 , wherein the second online gaming server computer system is configured to interface with the cheater detection program to extract the information regarding cheaters during online gaming.
- The system of claim 3 , wherein the extracted information regarding cheaters during online gaming includes at least one of timestamps of when cheaters were detected, user names of detected cheaters, types of cheats used by detected cheaters, and internet protocol addresses of computers systems used by detected cheaters.
- The system of claim 3 , wherein the extracted information regarding cheaters during online gaming includes online gaming identification numbers of detected cheaters.
- The system of claim 1 , further comprising a master file in the central database configure to store the aggregated information.
- The system of claim 7 , further comprising means for adding only cheaters who are actually banned from a game server to the master file.
- The system of claim 1 , further comprising a cheating prevention server module configured to aggregate the received information and including one or more master servers and master databases, and a cheater prevention server program or software.
- The system of claim 9 , further comprising a cheating prevention client module configured to receive the information regarding cheaters and including one or more individual game servers, a cheater prevention client program or software and a cheat detection program.
- The system of claim 10 , further comprising a game server plugin configure to perform cheater detection on the game servers.
- The system of claim 10 , wherein the cheater prevention client program works in conjunction with an automatic execution scheduling program for scheduled execution operation.
- The system of claim 10 , wherein if a game server is rented from a hosting company, the hosting company supports the cheater prevention program by providing system and program access and use of the cheater prevention program.
- The system of claim 10 , wherein the cheater prevention client program is installed by storing a corresponding executable program file script on a game server where anti-cheat program cheater log files are stored.
- The system of claim 10 , wherein the cheater prevention client program distributes cheater entries to several different files to reduce lag.
- The system of claim 10 , wherein the cheater prevention client program or software connects to the master server to transmit the cheater information.
- The system of claim 16 , wherein the cheater prevention client program is programmed to wait for the cheater prevention server program to perform an authentication process that is selectably turned on or off.
- The system of claim 17 , wherein the authentication process is performed by the cheater prevention server program comparing an IP address associated with a corresponding game server running the cheater prevention client program with a list of authorized game servers and/or by checking a security password.
- The system of claim 18 , wherein the cheater prevention server program listens for or gets connection requests from the cheater prevention client program running on the corresponding game server.
- The system of claim 1 , wherein the received information regarding cheaters includes an Internet Protocol (IP) addresses of the cheating players.
- The system of claim 1 , wherein the received information regarding cheaters includes in-game names or handles of the cheating players.
- The system of claim 1 , wherein the received information regarding cheaters includes unique online gaming identifications of the cheating players.
- The system of claim 1 , further comprising means for logging of relevant information about the cheater to a cheater log file by cheat detection or logging software upon detection of a cheating client or player.
- The system of claim 23 , further comprising a standard log format for the cheater log file, and including a date field, a cheater's name field, a cheater's gaming software identification field, and a cheat type field.
- The system of claim 1 , wherein the system is implemented with one or more hardware and software components.
- An apparatus, comprising: means for receiving information regarding cheaters detected during online gaming gathered by a second online gaming server computer system;means for aggregating the received information regarding cheaters detected during online gaming gathered by the second online gaming server computer system in a central database along with information stored on the central database regarding cheaters detected during online gaming gathered from a plurality of online gaming server computer systems;and means for making the aggregated information from the central database regarding cheaters detected during online gaming available to the first online gaming server computer system.
- The apparatus of claim 26 , wherein cheaters identified in the aggregated information from the central database are prevented from online gaming on the first online gaming server computer system based on the aggregated information from the central database.
- The apparatus of claim 26 , wherein received information is gathered from a plurality of cheater detection programs;and the received information is made available to at least one of an online gaming cheater detection program and online gaming server program running on the first online gaming server computer system.
- The apparatus of claim 26 , further comprising: detecting cheaters during online gaming via a cheater detection program running on the first online gaming server computer system;extracting information regarding cheaters during online gaming from output of the cheater detection program running on the first online gaming server computer system;and transmitting the extracted information regarding cheaters during online gaming to the second online gaming server computer system.
- The apparatus of claim 26 , wherein the extracting step includes interfacing with the cheater detection program to extract the information regarding cheaters during online gaming.
- The apparatus of claim 30 , wherein the extracted information regarding cheaters during online gaming includes at least one of timestamps of when cheaters were detected, user names of detected cheaters, types of cheats used by detected cheaters, and internet protocol addresses of computers systems used by detected cheaters.
- A computer-readable storage medium for storing computer-executable instructions that, when executed, perform a method for preventing cheating during online gaming, the method comprising: receiving information regarding cheaters detected during online gaming from a first online gaming server computer system;aggregating the received information regarding cheaters detected during online gaming from the first online gaming server computer system in a central database along with information regarding cheaters detected during online gaming gathered from a plurality of online gaming server computer systems stored on the central database;and transmitting the aggregated information regarding cheaters detected during online gaming from the central database to the first online gaming server computer system, whereby cheaters identified in the aggregated information from the central database are prevented from online gaming on the first online gaming server computer system based on the aggregated information from the central database.
- The computer-readable storage medium of claim 32 , wherein the received information is from output of a cheater detection program running on the first online gaming server computer system;and the transmitted information is gathered from a plurality of cheater detection programs running on the plurality of online gaming server computer systems.
- The computer-readable storage medium of claim 9 , wherein the transmitted information regarding cheaters during online gaming includes at least one of timestamps of when cheaters were detected, user names of detected cheaters, types of cheats used by detected cheaters, and internet protocol addresses of computers systems used by detected cheaters.
Disclaimer: Data collected from the USPTO and may be malformed, incomplete, and/or otherwise inaccurate.