U.S. Pat. No. 11,986,737
SYSTEM AND METHOD FOR FRAUD PREVENTION IN ESPORTS
AssigneeANYBRAIN, S.A.
Issue DateJune 29, 2021
Illustrative Figure
Abstract
A method and apparatus to objectively identify and classify cheating behaviors in players of virtual games, namely identity fraud or any type of software-based fraud or other unsportsmanlike or unethical behaviors. A method to use that information to inform the players, the game, the game servers, or any other external entity of the cheating behaviors found, allowing these entities to trigger disciplinary or punitive actions as per the regulations of the game or competition.
Description
DETAILED DESCRIPTION OF THE INVENTION The invention will now be described on the basis of the drawings. It will be understood that the embodiments and aspects of the invention described herein are only examples and do not limit the protective scope of the claims in any way. The invention is defined by the claims and their equivalents. It will be understood that features of one aspect or embodiment of the invention can be combined with a feature of a different aspect or aspects and/or embodiments of the invention. The terms “fraud”, “fraudulent”, “cheat” and “cheating” are used alternatively and interchangeably in this document to describe the same type of behavior which is not compliant with the honest playing of the game and can also be determined “unsportsmanlike”. The apparatus of the present document is shown inFIG.1and comprises a personal computing device10, connected to a pointer device20, a keyboard30, and a display unit40. The pointer device20and the keyboard30are collectively termed “input peripherals”. The term “input peripherals” includes other types of devices not shown here. The personal computing device10has a processing system10pand a storage device or local memory15. The personal computing device10is executing in its processing system10pa specific data collection software12that collects interaction data12dand, optionally, an online video or computer game14that is being played. The data collection software12and the computer game14are stored in the memory15. The personal computing device10is further connected a central computer server50through a network60. The central computer server50has a network storage area55. Further computers70a-cmay also be connected to the personal computing device10or to the central computer server60. The data storage device or local memory15may include a machine-accessible non-transitory medium on which is stored one or more sets of software program instructions embodying any one or more of the methodologies or functions described herein. The software may also reside, completely ...
DETAILED DESCRIPTION OF THE INVENTION
The invention will now be described on the basis of the drawings. It will be understood that the embodiments and aspects of the invention described herein are only examples and do not limit the protective scope of the claims in any way. The invention is defined by the claims and their equivalents. It will be understood that features of one aspect or embodiment of the invention can be combined with a feature of a different aspect or aspects and/or embodiments of the invention.
The terms “fraud”, “fraudulent”, “cheat” and “cheating” are used alternatively and interchangeably in this document to describe the same type of behavior which is not compliant with the honest playing of the game and can also be determined “unsportsmanlike”.
The apparatus of the present document is shown inFIG.1and comprises a personal computing device10, connected to a pointer device20, a keyboard30, and a display unit40.
The pointer device20and the keyboard30are collectively termed “input peripherals”. The term “input peripherals” includes other types of devices not shown here.
The personal computing device10has a processing system10pand a storage device or local memory15. The personal computing device10is executing in its processing system10pa specific data collection software12that collects interaction data12dand, optionally, an online video or computer game14that is being played. The data collection software12and the computer game14are stored in the memory15. The personal computing device10is further connected a central computer server50through a network60. The central computer server50has a network storage area55. Further computers70a-cmay also be connected to the personal computing device10or to the central computer server60.
The data storage device or local memory15may include a machine-accessible non-transitory medium on which is stored one or more sets of software program instructions embodying any one or more of the methodologies or functions described herein. The software may also reside, completely or at least partially, within the local memory15and/or within the processor10pduring execution thereof by the computer system10, the local memory15and the processor10palso constituting machine-accessible storage media. The software may further be transmitted or received over the network60via the network interface or communications subsystem.
The machine-accessible non-transitory medium may also be used to store data structure sets that define player interaction profiles. Data structure sets and interaction profiles may also be stored in other sections of computer system10, such as static memory.
While the machine-accessible non-transitory medium is shown in an exemplary embodiment to be a single medium, the term “machine-accessible non-transitory medium” should be taken to include a single medium or multiple media (e.g., a centralized or distributed database, and/or associated caches and servers) that store the one or more sets of instructions. The term “machine-accessible non-transitory medium” shall also be taken to include any medium that is capable of storing, encoding or carrying a set of instructions for execution by the machine and that cause the machine to perform any one or more of the methodologies of the present invention. The term “machine-accessible non-transitory medium” shall accordingly be taken to include, but not be limited to, solid-state memories, optical and magnetic media, and carrier wave signals.
The pointer device20includes any input peripheral device connected to the personal computing device10, cabled or wireless, or detectable by a computer, which can transmit instructions from the player as to where a pointer or other indicator should be on a screen of the display unit40and receive instructions from the player to select the area of the screen covered by the pointer or other indicator. The term “pointer device” includes, but is not limited to, a mouse, a joystick, a touchpad, a trackball, a stylus, the player's eyes or fingers or any other sensing, pointing or tracking device with the function of placing a pointer in a given location in the display unit40or in any unit giving pointer location information to the player. Additionally, pointer devices may have mechanical or other types of buttons, switches or touch-sensitive areas which the player can click, tap, press or actuate to launch a programmed action over the selected area of the computer screen or display unit. Throughout this application, the terms “pointer” and “mouse” may be used interchangeably and they both refer to the term “pointer” defined above.
The keyboard30includes any input device connected to a computer, cabled or wireless, or detectable by a computer, which comprise keys representing letters, numbers, symbols and function keys and which are selectable by the player and transmitted to the computer and optionally to the display unit of the computer. The keyboards can be mechanical, touch-sensitive and/or virtual, as in a touch-screen computer tablets or in any other device not invented yet but fulfilling the same function of keyboards, to the exclusion of voice commands, which are not covered by the present invention.
The data collection application12comprises a real-time monitoring system12mrunning in the background (i.e. removed from the player's view) of the player's personal computing device10, which collects the interaction data12dabout the interaction events of the player with the personal computing device10using the aforementioned input peripherals20and30. While the data collection application12may collect the interaction data from the interaction with any device, input peripheral, or application running in the personal computing device10, the goal is to collect the interaction data12dfrom the player's interaction dynamics with the input peripheral(s)20and30whilst the player is using the input peripherals. This real-time monitoring system12mis divided into three distinct components as will now be set out.
Collection of the input from player's interaction with the input peripheral(s) of the personal computing device10. This real-time monitoring system12mof the data collection software12is continuously running in the background, while the player interacts with the personal computing device10and the input peripherals20and30while the computer game application14is running in the foreground. The monitoring part12mof the data collection software12collects the interaction data12dregarding the events resulting from the use of or general interaction with the peripherals, such as the mouse and keyboard devices20and30; When a player is interacting with the personal computing device10the player needs to apply a set of cognitive skills in the player's mind to be able to process the information that is received from the personal computing device10. This received information includes sound, video or images on the display unit40. The interaction with the personal computing device10usually is a result of a set of interactions as a result of a commands given to the personal computing device10(in a passive or active way);
One or more application programming interfaces (API)12ato process the inputs from the input peripherals20,30(this is a set of services hosted in a server that calculate top level information describing player interaction, also called interaction features) or the processing of inputs in the machine itself. As will be explained below, the amount of interaction data12dcollected is reduced by using compression algorithms.
Presentation panel of cheating monitoring results12i, which presents the interaction data12dcollected and processed from the player, as well as the results of the cheating monitoring; Optionally, this component may also trigger punitive actions such as temporarily banning the player from the session.
The computer game application14is any game that the player is running and playing on the personal computing device10and which requires movements of the input peripherals, such as the mouse20or the keyboard30for its operation. The computer game application14is an online video game, such as a competitive esports game, but also could be other types of games, such as role-playing games.
The central server50is any computer networked with the player's personal computing device10and which stores the players' interaction profiles and may be required to do some additional processing. The central server50is divided into two distinct components:
A profile building module50pwhich continuously receives the interaction data12dfrom the player and builds and updates the player's interaction profile, using statistical tools. This interaction profile represents the way in which a player generally interacts with the input peripherals20and30. Moreover, this profile building module50palso builds interaction profiles of groups of players (e.g. teams or all players of a game), for example using the further computers70a-c. The interaction profiles are stored in a player interaction profile database55p.
A cheating detection module50cthat, given the interaction data12dof one player, determines if the interaction data12drepresents or indicates a cheating/fraudulent behavior or not. This cheating detection module50cuses statistical tools, Machine Learning, Artificial Intelligence and/or other approaches to analyze the interaction data against the player's known interaction profile. Optionally, when the interaction data12dis classified as representing cheating, this cheating detection module50cmay communicate with the information panel12iof the player's personal computing device10to inform the player, so that the computer game application14can be informed about the unsporting behavior of the player. Other external modules (e.g. game servers) may also receive information from this cheating detection module50c.
In use, the apparatus and method of the present application analyze the dynamics of the player's interaction with the input peripheral(s)20,30of the personal computing device10being used as the gaming apparatus, which translate into game actions. The proposed apparatus and method thus consider the input peripherals, such as the pointer device20or the keyboard30and interpret their dynamics/movements. It will be appreciated that at this stage a large amount of data will be collected. Some of this data will be repetitive and can be compressed using a string compression algorithm, such as run length encoding.
The apparatus and method reduce the amount of interaction data12dthat needs to be saved by converting these pointer and keyboard dynamics into a normalized group of numbers (the interaction features) indicative of the player's interaction patterns.
The apparatus and method then compare the player's interaction pattern to those of the same player or of other internet-connected players (interaction profiles) using the same apparatus and method for further precision. The apparatus and method may then trigger an intervention within the computer game application14(or other software) to adapt or regulate its function to the player's interaction pattern, or to a command system external to the personal computing device to trigger further actions to inform or warn the player, another application (e.g. game server) or a supervisor (e.g. judge in a competition) about the suspected cheating or fraudulent behavior. It is not necessary for the intervention to happen in real time. It would be possible to reduce the use of resources for the intervention to only happen at periodic intervals, e.g. every day or every week or at the end of a competition.
In terms of data flow, two main processes can be identified: the first process is for building and updating players' interaction profiles (detailed inFIG.2) and the second process is for detecting and classifying cheating behaviors (detailed inFIG.3). These processes are described here:
FIG.2describes, step by step, the process through which individual or group interaction profiles are built. The player installs the data collection software12(step200) in her/his personal computing device10. Alternatively, the game publisher integrates an SDK that contains the necessary functionality in the computer game application14. The player provides authentication information (step210) to identify herself/himself in the system, i.e. on the personal computing device10and/or the central computer server50. The data collection software12, as noted above, continuously captures the interaction events from the player's interaction with the input peripherals10and30(step220). The interaction data12dcaptured includes relevant information such as a timestamp (in ticks or milliseconds) or coordinates of the pointer on the screen of the display device40. The following are non-limiting examples of the interaction events that can be captured and tracked, although any other interaction event with any input peripheral can be used:MOV, an event describing the movement of the mouse20, at a given time, to coordinates (posX, posY) in the screen of the display device40;MOUSE_DOWN, [Left|Right],—this event describes the first half of a click (when the mouse button is pressed down), at a given time. It also describes which of the buttons was pressed (left or right) and the position of the mouse20in that instant;MOUSE_UP, [Left|Right],—an event similar to the previous one but describing the second part of the click, when the mouse button is released;MOUSE_WHEEL,—this event describes a mouse wheel scroll of amount, at a given time;KEY_DOWN,—identifies a given key from the keyboard30being pressed down, at a given time;KEY_UP—describes the release of a given key from the keyboard30, at a given time.
An excerpt and example of the collected data is presented below. In this excerpt, the player moves the mouse20(first two lines) from the coordinates (451, 195) to (451, 197), then performs the first half of a click with the left button (third line) in coordinates (451, 199), then moves the mouse20a bit to coordinates (452, 200) (fourth line), then ends the click by releasing the button in the same coordinates and finally keeps moving the mouse20to coordinates (454, 205). All this takes place between timestamps 635296941683402953 and 635296941685803193:MOV, 635296941683402953, 451, 195MOV, 635296941684123025, 451, 197MOUSE_DOWN, 635296941684443057, Left, 451, 199MOV, 635296941685273140, 452,200MOUSE_UP, 635296941685283141, Left, 452, 200MOV, 635296941685723185, 452, 203MOV, 635296941685803193, 454, 205
Some of the above interaction events are for a conventional mouse20. In the case of a touch pad, which does not have any moving parts, certain tracked events would be different (e.g. pressing force would be one of the different tracked events). It will be appreciated that the person skilled in the art would have no problem in identifying these different tracked interaction events and adjusting the data collection software12to make use of the new types of interaction events to track. The same would apply to a joystick, stylus or to any other type of pointer device.
These six categories of the interaction events produce the interaction data12dwhile the player is playing the computer game application14running in the foreground. In step230these data are processed to generate the so-called interaction features, which are a group of high-level variables that thoroughly describe the interaction of the player with the input peripherals20,30. The following list contains examples of interaction features that could be produced by the data collection software12while the player is interacting simultaneously with the mouse20and the keyboard30. The proposed apparatus and method is however not limited to these interaction features and includes any other features interaction that describes the dynamics of a player interacting with any input peripheral of the personal computing device10being used as the gaming apparatus, while playing any computer game application14.Time spent between the key down and key up (or key release) events;Time spent between different keys on the keyboard30;Acceleration in pressing a key on the keyboard30;Velocity in pressing a key on the keyboard30;Number of times the backspace key is pressed, versus the keys pressed;Velocity at which the cursor travels;Acceleration of the pointer at a given time;The duration of each pointer click;A measure of the number of clicks on active controls versus the number of clicks in passive areas;Excess of distance travelled by the pointer between a pair of two consecutive clicks;Average of the excess distance travelled by the pointer between a pair of two consecutive clicks;Speed of the double click;Number of double clicks in a time frame;Distance travelled by the pointer while dragging objects;How much the pointer “turned” left or right during its travel;Measures, absolutely, how much the pointer “turned” during its travel;Measures the distance between all the points of the path travelled by the mouse between each two consecutive clicks, and the closest point in a straight line (that represents the shortest path) between the coordinates of the two clicks;Same as above, but provides an average value of the distance to the straight line.
The above-mentioned interaction features are calculated at regular intervals by the data collection software12. For the sake of clarity, we shall now describe the process for computing the most complex interaction features proposed, in order to detail their relevance and meaning in the context of interaction dynamics and fraud detection.
In the case of Distance of the Mouse to the Straight Line (DMSL), this feature measures the sum of distance of the mouse to the straight line defined between two consecutive clicks. Let us assume two consecutive MOUSE_UP and MOUSE_DOWN events, mup and mdo, respectively in the coordinates (x1,y1) and (x2, y2). Let us also assume two vectors posx and posy, of size n, holding the coordinates of the consecutive MOUSE_MOV events between mup and mdo. The sum of the distances between each position and the straight line defined by the points (x1, y1) and (x2,Y2) is given by equation 1 below, in which ptLineDist returns the distance between the specified point and the closest point on the infinitely-extended line defined by (x1, y1) and (x2, y2).
sdists=∑i=0n-1ptLinedist(posxi,posyi),(Eqn1)
Another interaction feature generated by the data collection software12is mouse velocity. This is the distance travelled by the mouse20(in pixels) over the time (in milliseconds). The velocity is computed for each interval defined by two consecutive MOUSE_UP and MOUSE_DOWN events. Let us assume two consecutive MOUSE_UP and MOUSE_DOWN events, mup and mdo, respectively in the coordinates (x1, y1) and (x2,Y2), that took place respectively in the instants time1and time2. Let us also assume two vectors posxand posy, of size n, holding the coordinates of the consecutive MOUSE_MOV events between mup and mdo. The velocity between the two clicks is given by
rdist(time2-time1),
in which rdistrepresents the distance travelled by the mouse and is given by equation 2:
rdist=∑i=0n-1(posxi+1-posxi)2+(posyi+1-posyi)2(Eqn.2)
One last example of interaction feature described here is the absolute sum of angles. This feature seeks to find how much the mouse20“turned”, independently of the direction to which the mouse20turned (FIG.5). In that sense, the interaction feature is computed as the absolute of the value returned by function degree(x1, y1, x2, y2, x3, y3), as depicted in equation 3.
An efficient mouse movement is characterized by lines of movement that are almost straight. Therefore, higher values of this feature indicate a less efficient movement of the mouse.
sangle=∑i=0n-2degree(posxi;posyi;posxi+1;posyi+1;posxi+2;posyi+2)(Eqn.3)
An example will also show how the logs of the keyboard data are transformed into keyboard-related interaction features, like key down time, time between keys, etc. Consider the following snippet of pseudocode:Data: Keyboard InputsResult: List of KeyDownTime recordswhile Keyboard Inputs have records doGet timestamp of a KEY_DOWN:Get code of KEY_DOWN:while Keyboard Inputs have records doGet timestamp of KEY_UP:Get code of KEY_UP:if KEY_DOWN code and KEY_UP code are the same then Save the difference between KEY_UP timestamp and KEY_DOWN timestamp;endendendAlgorithm 1: Key down time algorithm
This pseudocode determines the amount of down time of the key on the keyboard30, i.e. how long the key is pressed (also known as typing latency). Similar code can be used to determine values of other interaction features and, given its relative simplicity, will not be detailed here.
An example of processed data will serve to better describe the type of information generated by this process. The data presented below describes all the interaction features calculated for a given player (Player X) at a given moment in time.{“TimeStamp”: NumberLong(1506373243375),“Player”: “Player X”,“Performance”: {“TimeStamp”: 1506373242732,“KDTVar”: 1033.9388571428572,“KDTMean”: 125.5952380952381,“MAMean”: 0.5366564446226314,“MAVar”: 0.36105299630493787,“MVMean”: 0.4912874973741709,“MVVar”: 0.29093708004098856,“TBCMean”: 9089.82142857143,“TBCVar”: 152705577.48544973,“DDCMean”: 21.252471533256006,“DDCVar”: 1111.4930124743523,“DMSLean”: 18972550.8,“DMSLVar”: 664834398497875.0,“AEDMean”: 3.0064312681905263,“AEDVar”: 6.020307987912261,“ADMSLMean”: 184632.7142857143,“ADMSLVar”: 65030255404.582,“TBKVar”: 18145.18881118881,“TBKMean”: 147.36363636363637,“LeftClicks”: 29.0,“RightClicks”: 0.0,“KeysPressed”: 88.0,“WVMean”: 28.333333333333332,“MouseDistance”: 7.833947450529339,“MouseExcessDistance”: 1.2101157953969313,“MousePrecision”: 78.52464254995121,“ErrorPerKey”: 22.727272727272727}}
The processed interaction data12dis then sent to the central computer server50, which records it locally in its network storage are 55 (step240). Thus, the interaction data12dabout each player continuously grows as each player plays the computer game application14.
When a sufficient amount of the interaction data12dabout a given player with the peripheral devices20,30is available, the system proceeds to build an interaction profile of said player (step250). Several different approaches can be used to build the interaction profile, including but not limited to: A) Statistics and B) Artificial intelligence techniques such as machine learning algorithms:
A) The player interaction profile can be built using statistical tools using the following method. The player interaction profile is constituted by two limit values (lower and upper) for each of the interaction features described above. These limits are computed using a statistical approach and, in their conjunction, represent the “normal” interaction dynamics of one player or group of players being considered (e.g. team, top-tier players). The meaning of the “normal” interaction dynamics can be understood by the following example concerning the mouse moving velocity: Player X generally moves the mouse at a speed between 0.02 px/ms and 0.34 px/ms. When these limits are calculated for all of the interaction features, a unique interaction profile is obtained for each of the individual players. Thus, this unique interaction profile can be used not only to find statistically significant deviations from the “normal” behavior of one player but also to identify when a player is behaving in an entirely different way (such as when another player is using the first player's character).
The following method is applied to compute these limits. For each player, all of the available interaction data is considered. For each interaction feature, the Inter-Quartile Range (IQR) is calculated. For each interaction feature, the first and third quantiles are calculated (Q1 and Q3, respectively). The upper limit of an interaction feature f is obtained by Eqn4. The lower limit of an interaction feature f is obtained by Eqn5. Together, these two limits establish the boundaries of the “normal” behavior of a given player.
ULimf=Q3f+1.5*IQRf(4)
LLimf=Q1f−1.5*IQRf(Eqn. 5)
The statistical player interaction profiles are saved in a table-like format, in the player interaction profile database55pconnected to the central computer server50(step260).
Among other data such as identifying information, the interaction profile contains two values for each interaction feature (upper and lower limits).
FIG.7visually depicts a simplification of the interaction profile of one player (identified as Player2). For the sake of readability, only five interaction features are depicted. The two lines show the lower and upper limits of these variables.
FIG.10shows a similar visualization but for the interaction data of another player (identified as Player5): the differences in the shapes of both visualizations are evident and result from different interaction patterns of both players. The interaction profiles are so different that they can be used to identify the player, as described further below. It will be appreciated at this stage that neither of the interaction profiles contain “personal” data
B) Alternatively, an approach based on artificial intelligence techniques such as, but not limited to, machine learning, can be followed to create the player's interaction profile.
Following this approach, artificial intelligence algorithms are trained to distinguish between what is considered a normal and an abnormal behavior for the players. To this end, a method similar to A) is employed. However, the upper and lower limits defined are now used to automatically label each instance of data from a given player as being normal or not. This results in a dataset with a categorical variable (“normal”/“abnormal”) that can be used to train binomial classification or regression models.
These models, once trained, can be used to attribute a class (“normal”/“abnormal”), and/or a number that depicts the certainty level, to a new instance of data and thus determine if the new instance of data may or may not represent a cheating behavior (including, if defined, the certainty level). An example of this learning algorithm is the nearest neighbor's algorithm see (https://en.wikipedia.org/wiki/K-nearest_neighbors algorithm).
Another method is by creating functions of approximation values as in the case of artificial neural networks (https://en.wikipedia.org/wiki/Artificial_neural_network), or through any other algorithm capable of recognizing patterns. These machine learning algorithms enable the interpretation of a large amount of data in a reduced space of time for substantially real-time monitoring.
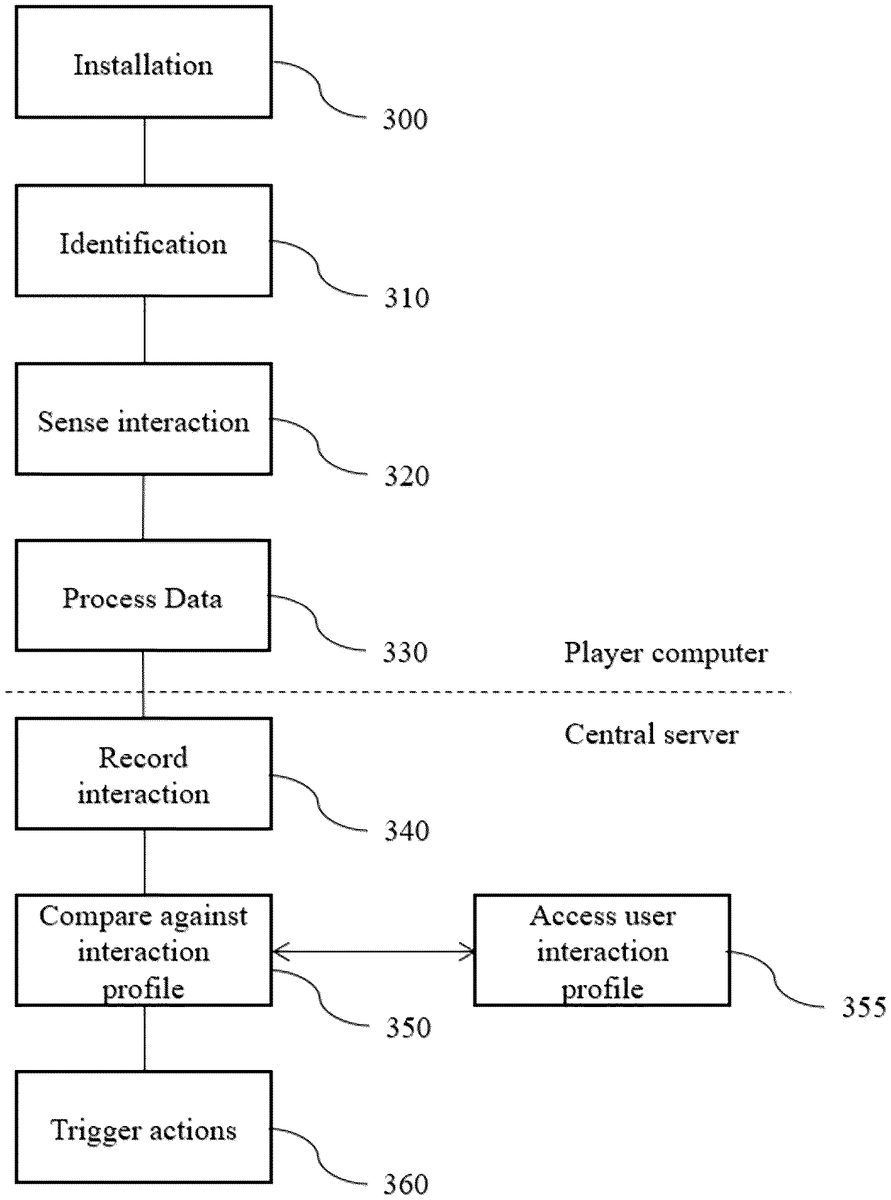
Let us now describe the second of the two most relevant processes proposed in this application, as detailed inFIG.3. The main goal of this process is to determine if a given player is or is not cheating, at any computer game application being played at any given moment. This process executes regularly after the first successful conclusion of the process described inFIG.2, i.e., after there is an interaction profile for the player stored in the player interaction profile database55pof the central computer server55.
The first five steps are similar to those of the previously described process: the player installs the data collection software12in the personal computing system10if the data collection software12is not already installed (step300) or if the computer game application14does not integrate the SDK. The player provides the identifying information so that she/he can be recognized in the system (step310), the data collection software12starts collecting the interaction data12dfrom the player while playing (step320), the interaction data12dis processed so that the interaction features previously described are generated and sent to the central server (step330) and the interaction features are stored in the network storage area55of the central computer server50(step340).
The next step (step350) is the one to determine if the interaction data of the player with the peripheral devices20,30received from the personal computing device10represents or not a cheating or fraudulent behavior. This step is different depending on the way in which the interaction profile was built. Below, for the sake of clarity, we shall detail the process for the two methods previously addressed: A) Statistical Tools or B) Artificial Intelligence. However, other similar processes may be defined and can be included in this method and apparatus, which are adaptations according to the way the interaction profile was built.
A) To accomplish this task using a statistical interaction profile, the central computer server50first retrieves the corresponding player interaction profile from the player interaction profile database55p. Then, for each interaction feature, the central computer server50verifies if the value of the received data falls within the limits of the feature in the player profile. The central computer server50thus computes the percentage of the interaction features that fall within the limits defined in the player interaction profile. A high percentage indicates that the player is not cheating as she/he is interacting in a normal way. A lower percentage indicates that the player is behaving abnormally according to the known player interaction profile and might be cheating.
FIG.8depicts this graphically. For the sake of readability, the figure represents graphically part of the profile of Player2(upper and lower limits of five interaction features shown with the solid lines). The figure also represents one set of data being checked for cheating (dashed line) of the same player. In this example, all the interaction features are within the limits of the player interaction profile, which indicates that the identity of the player is correct and that she/he is not cheating. In this scenario, the central computer server55provides as a result the value 100%, which indicates that the interaction of the player matches the known player interaction profile.
FIG.9, on the other hand, shows an instance of data that does not comply with the interaction profile. Specifically, three of the interaction features (MV, MD and CD) are outside the limits of the player interaction profile, which results in the central computer server50returning the value 40%. This indicates either that the player is cheating or that another player is playing with the registered player's character. In this example, the second case happens since data from a different player was used to exemplify the concept.
It needs to be pointed out, once again, that this is only a simplified version of the process that considers only five interaction features for facilitating the visualization of the process. The invention proposed in this application considers many other features when building the player interaction profile and when checking for unsportsmanlike behaviors, not limited to those that were detailed in this application for the sake of clarity.
B) To accomplish this task using models obtained through artificial intelligence algorithms, the process is more straightforward as these models can be executed and, given an unlabeled instance of data, will provide in return a label for that data. In this case, the central computer server50retrieves the corresponding artificial intelligence model that was stored in the network storage area55and obtains a classification label (“normal”/“abnormal”) and/or a number that depicts the certainty level on the prediction, and that characterizes the instance of data being analyzed.
Finally, in step360, certain actions can be triggered according to the result of the fraud prediction. Namely, the central computer server50may implement one or more actions such as record the event, notify the client, terminate the connection with the client, or apply any disciplinary measures such as temporary or permanent bans, removing in-gaming resources from the player's avatar, highlighting the position of the player's avatar, impairing the player's avatar (e.g. slowing down movement), among others.
A second use of this invention would be to continuously inform the game server about cheating behaviors of the players or teams, so that the game server may take additional punitive actions such as temporarily or permanently banning the player as per the game rules.
A third use of this invention would be to prevent and detect cheating behaviors during online esports competitions in which the players and the judges participate remotely, from different geographical locations. In this case, the system could inform the judges about any suspected cheating behavior observed in any of the players so that disciplinary measures could be taken as per the regulation.
A fourth use of this invention would be to prevent and detect cheating behaviors during esports competitions in which the players and the judges are in the same geographical location, as when esports competitions are held in a stadium or similar building. In this scenario, the system could inform the judges about any suspected cheating behavior so that the software/hardware being used by the player could be further inspected and so that any disciplinary measures could be taken as per the regulations.
A fifth use of this invention would be to maintain an online list of the players that were found to cheat while playing a given computer game application. This list could be updated automatically and, optionally, include the penalty or disciplinary action applied in each case. Such a list would have a deterrent effect on the cheating behavior of other players.
All of these uses of the proposed system can be combined without limitation and signals and triggers originating in the central server can be any of those identified above, to cause any desired action in the main software applications, in the playing environment or in informing the player, judge or other supervisor.
The method of the present invention uses the above described apparatus and method to objectively detect cheating behaviors as it records, analyzes and compares player actions and behaviors using a pointer and a keyboard, performed during normal gameplay, which it then uses to signal or trigger preset actions in the main software application or in the game itself, changes to the game environment or relaying of information to the player, judge or other supervisor.
EXAMPLE
Here it is described a use of the invention for the purpose of player identification.
The apparatus was implemented as previously described, using one computer acting as a central server (containing all the aforementioned components) and five computers acting as clients.
Five different professional players played several instances of a given game while the data collection software12was active in their personal computing devices used as the gaming computers.
In total, 9309 instances of data were collected from each of the players. In this case, and given that each instance of data contains the averaged values of the last five minutes, the data considered represents more than 700 hours of interaction.
Using this data, a protocol to evaluate the ability of the method and apparatus to identify each of the players was tested and validated. In order to ensure the validity of the findings, data were divided in two groups: train and validation.
The training dataset contains approximately 75% of the data, selected randomly, and was used to create the player interaction models following a statistical approach, as described previously. This resulted in the creation of five player interaction profiles (one for each player), each containing 39 variables: one that identifies the player and two for each of the interaction features described previously (the upper and lower limits, determined following the statistical approach described).
The validation dataset contains the remaining 25% of the data and was used to assess the classification accuracy of the invention when it comes to identify the correct player.
The methodology followed for assessing the accuracy of the invention was as follows. For each instance of the validation dataset, it was calculated the percentage of interaction features that complied with the interaction profile of each player. Thus, for each interaction instance, the central server returned the likeliness of those data belonging to each of the five players.
Next, the player with the highest likeliness was selected to be the prediction result. This prediction result was then compared against the actual player (which in this case is known). The count of correct vs. wrong predictions gives us the percentage of correctly classified players.
FIG.11depicts the confusion matrix created after the use of this system to identify each player using the trained models on the validation dataset.
It will be appreciated that the present invention is being submitted as a provisional patent application and within the priority year the definitive application shall be submitted, complying with the appropriate technical and legal requirement and proper correspondence between the content of the specification and the individual claims. We believe however, that the inventive case is made and is fully disclosed here, and will be properly written in the definitive application, together with the appropriate dependent claims and correct drawing reference.
REFERENCE NUMERALS
10Personal computing device10pProcessing system12Data collection software12aApplication programming interfaces12iIntervention module12mReal-time monitoring system14Computer game application15Memory16Database18Internal table20Pointer device30Keyboard40Display unit50Central computer server50cCheating classification module50pProfile building module55Network storage area55pPlayer interaction profile database60Network70a-cFurther computers
Claims
- A computer-implemented method for detection of fraudulent behavior of a player in an online video game, wherein the fraudulent behavior is one of replacement of the player by another player or the use of performance-enhancing software or hardware by the player the method comprising: collecting at a personal computer device a plurality of interaction data relating to a plurality of interactions of the player with a plurality of peripheral devices connected to the personal computer device;transmitting the interaction data to a central computer server;performing at the central computer server a comparison between the transmitted interaction data and a general player interaction profile stored in a player interaction database;performing at the central computer server a comparison between the transmitted interaction data and one or more specific player interaction profiles stored in the player interaction database to verify an identity of one of the player and the another player;identifying a risk of fraudulent behavior based on the comparison between the transmitted interaction data and the stored player interaction profile as well as one or more specific player interaction profiles;and receiving from the central computer server a message indicative of the risk of fraudulent behavior, wherein at least one of the general player interaction profile or the one or more specific player interaction profile is derived from at least one of a statistically based normal interval level or a model derived from machine learning;the interaction data comprises movement distances of a movable one of the peripheral devices moved by the player;and the normal interval level is between a maximum usual movement distance and a minimum usual movement distance and wherein the comparison to identify the risk of fraudulent behavior is determined by comparing one of more of the movement distances to determine whether they fall within the normal interval level.
- The method of claim 1, wherein the interaction data comprises at least one of reaction times between the player and one or more of the peripheral devices, velocity of movement of the movable one of the peripheral devices, or force applied to one or more of the peripheral devices.
- The method of claim 2, wherein the normal interval level is between a maximum usual reaction time with one or more of the peripheral devices and a minimum usual reaction time with one or more of the peripheral devices and wherein the comparison to identify the risk of fraudulent behavior is determined by comparing one of more of the reaction times to determine whether they fall within the normal interval level.
- The method of claim 1, further comprising continuously updating the player interaction profile based on the transmitted interaction data.
- The method of claim 1, further comprising an updating of the stored general player interaction profile and the one or more specific player interaction profile based on the received interaction data.
- The method of claim 1 wherein the fraudulent behavior comprises at least one of engaging additional software tools, taking performance-enhancing drugs, or swapping player profiles.
- The method of claim 1, further comprising triggering preset actions based on the message indicative of the risk of fraudulent behavior.
- The method of claim 1, wherein the interaction data captures an interaction event of the player with the plurality of peripherals devices, wherein the interaction event is at least one of: an event describing a movement of a mouse at a given time;an event describing a mouse click, a pointer click or a press of a given key from a keyboard, at a given time;an event describing a release of the given key from the keyboard, at a given time;an event describing a first half, or a second half of the mouse click at a given time;an event describing a press of at least one of mouse buttons;an event describing coordinates of the mouse at a given time;an event describing a mouse wheel scroll of amount at a given time.
- The method of claim 1, further comprising processing the interaction data to generate a plurality of interaction features, where the plurality of interaction features is at least one of: coordinates of a pointer on a screen of a display device;a timestamp of a mouse click or a press of a given key from a keyboard;a time spent between a press or release of the given key or different keys from the keyboard;an acceleration or a velocity in pressing the given key on the keyboard;a number of times a backspace key is pressed, versus keys pressed;a velocity at which a cursor travels;an acceleration of the pointer at a given time;a duration of a pointer click, a mouse click or the press of the given key from the keyboard;a number of clicks on active controls versus a number of clicks in passive areas;an excess or an average of distance travelled by the pointer between a pair of two consecutive clicks of the given keys;a speed of a double click;a number of the double clicks in a time frame;a distance travelled by the pointer while dragging objects.
- A system for detection of fraudulent behavior of a player in an online video game, wherein the fraudulent behavior is one of replacement of the player by another player or the use of performance-enhancing software or hardware by the player, the system comprising: a central computer server connected over a network to one or more personal computer devices, the one or more personal computer devices being connected to a plurality of peripheral devices;a player interaction database storing a plurality of player interaction profiles;wherein the stored player interaction profiles comprise a general player interaction profile and one or more specific player interaction profiles;and the central computer server is adapted to receive interaction data from the plurality of peripheral devices and identify a risk of fraudulent behavior based on a comparison between the received interaction data and the stored general player interaction profile, wherein at least one of the general player interaction profile or the one or more specific player interaction profile is derived from at least one of a statistically based normal interval level or a model derived from machine learning: the interaction data comprises movement distances of a movable one of the peripheral devices (20,30) moved by the player;and the normal interval level is between a maximum usual movement distance and a minimum usual movement distance and wherein the comparison to identify the risk of fraudulent behavior is determined by comparing one of more of the movement distances to determine whether they fall within the normal interval level.
- The system of claim 10, wherein the plurality of peripheral devices comprises one or more of a mouse, a keyboard, a joystick, motion detector, or an eye-tracking device.
- The system of claim 10, wherein the interaction data comprises at least one of reaction times between the player and one or more of the peripheral devices, velocity of movement of the movable one of the peripheral devices, or force applied to one or more of the peripheral devices.
- The system of claim 10, wherein the central computer server is adapted to create one or more of the player interaction profiles based on the interaction data.
- The system of claim 10, further comprising a messaging system to generate a message indicative of the risk of fraudulent behavior.
- The system of claim 10, wherein the interaction data captures an interaction event of the player with the plurality of peripherals devices, wherein the interaction event is at least one of: an event describing a movement of a mouse at a given time;an event describing a mouse click, a pointer click or a press of a given key from a keyboard, at a given time;an event describing a release of the given key from the keyboard, at a given time;an event describing a first half, or a second half of the mouse click at a given time;an event describing which of mouse buttons was pressed;an event describing coordinates of the mouse at a given time;an event describing a mouse wheel scroll of amount at a given time.
- At least one non-transitory machine-readable storage medium having logic instructions stored thereon, the logic instructions when executed by a central server processor cause the central server processor to: receive from a personal computer device a plurality of interaction data relating to a plurality of interactions of the player with a plurality of peripheral devices connected to the personal computer device;to perform at the central computer server a comparison between the transmitted interaction data and a general player interaction profile as well as one or more specific player interaction profiles stored in a player interaction database;and identify a risk of fraudulent behavior based on the comparison between the transmitted interaction data and the stored player interaction profile, wherein the fraudulent behavior is one of replacement of the player by an impostor or the use of performance-enhancing software or hardware by the player, wherein at least one of the general player interaction profile or the one or more specific player interaction profile is derived from at least one of a statistically based normal interval level or a model derived from machine learning, the interaction data comprises movement distances of a movable one of the peripheral devices moved by the player;and the normal interval level is between a maximum usual movement distance and a minimum usual movement distance and wherein the comparison to identify the risk of fraudulent behavior is determined by comparing one of more of the movement distances to determine whether they fall within the normal interval level.
- The storage medium of claim 16, further comprising logic instruction to cause the central computer server to issue a message indicative of the risk of fraudulent behavior.
Disclaimer: Data collected from the USPTO and may be malformed, incomplete, and/or otherwise inaccurate.