U.S. Pat. No. 9,781,219
INTERACTIVE TRACKING VIRTUAL WORLD SYSTEM
Issue DateJuly 10, 2014
Illustrative Figure
Abstract
An Interactive Tracking Virtual World (ITVW) system, may be utilized with other systems accessible through the Internet and/or a communications network. The ITVW system may be operable as an online game and/or to provide a virtual environment. ITVW system users (i.e., ITVW users) may be individuals or groups, such as parents and/or their children, which utilize the ITVW system for tracking an identity within the ITVW system. The ITVW system may also include ITVW system participants (i.e., ITVW participants), such as commercial business establishments, individuals and/or other entities associated with the ITVW system. The ITVW system collects an ITVW user's location information and location history.
Description
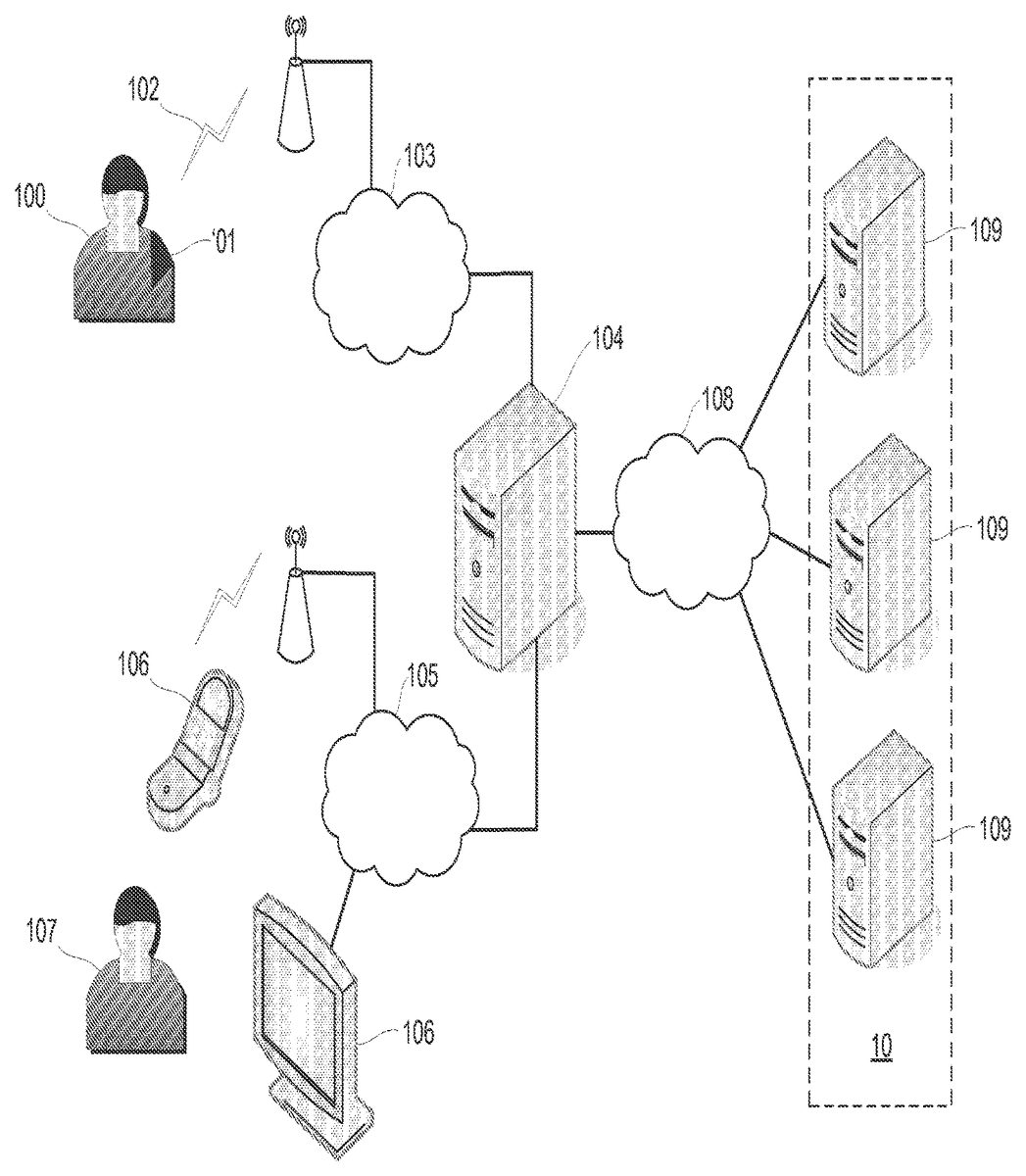
DETAILED DESCRIPTION FIG. 1illustrates an example of an ITVW system10including ITVW servers109. The ITVW system10may receive input data from various sources outside the ITVW system10. An ITVW system child user100wears a tracking device101, which is registered in advance with the ITVW system10. The tracking device101transmits location information via a wireless link102and communications network103to a communications server104which transmits the location information over the Internet108to the ITVW system10, where it is stored on the ITVW servers109. The ITVW servers109include storage and software which prepare a representation of a virtual world. A representation of the virtual world may be transmitted from the ITVW system10to the Internet108. The transmitted virtual world representation is received by an ITVW system user107via a communications network105and various human interface devices106. The communications server104may also receive participant data from ITVW system participants and transmit this over the Internet108to the ITVW system10. FIG. 2illustrates a system200configured to provide a virtual space to users. System200may be configured such that the virtual space may be impacted by real-world actions of the users. Real-world actions of the users may be tracked, for example, tracking the real-world locations of the users. Certain real-world actions may be incentivized by providing a positive impact associated with such real-world actions in the virtual space. Information related to the real-world locations of the users may be provided to supervisors of the users, such as parents and/or other supervisors. Providing the virtual space may include hosting the virtual space over a network. In some implementations, system200may include a server202. The server202may be configured to communicate with one or more client computing platforms204according to a client/server architecture. The users may access system200and/or the virtual space via client computing platforms204. Server202may be configured to execute one or more computer program modules. The computer program modules may include one or more of ...
DETAILED DESCRIPTION
FIG. 1illustrates an example of an ITVW system10including ITVW servers109. The ITVW system10may receive input data from various sources outside the ITVW system10. An ITVW system child user100wears a tracking device101, which is registered in advance with the ITVW system10. The tracking device101transmits location information via a wireless link102and communications network103to a communications server104which transmits the location information over the Internet108to the ITVW system10, where it is stored on the ITVW servers109. The ITVW servers109include storage and software which prepare a representation of a virtual world. A representation of the virtual world may be transmitted from the ITVW system10to the Internet108. The transmitted virtual world representation is received by an ITVW system user107via a communications network105and various human interface devices106. The communications server104may also receive participant data from ITVW system participants and transmit this over the Internet108to the ITVW system10.
FIG. 2illustrates a system200configured to provide a virtual space to users. System200may be configured such that the virtual space may be impacted by real-world actions of the users. Real-world actions of the users may be tracked, for example, tracking the real-world locations of the users. Certain real-world actions may be incentivized by providing a positive impact associated with such real-world actions in the virtual space. Information related to the real-world locations of the users may be provided to supervisors of the users, such as parents and/or other supervisors. Providing the virtual space may include hosting the virtual space over a network.
In some implementations, system200may include a server202. The server202may be configured to communicate with one or more client computing platforms204according to a client/server architecture. The users may access system200and/or the virtual space via client computing platforms204.
Server202may be configured to execute one or more computer program modules. The computer program modules may include one or more of a user module206, a space module208, a relationship module210, a location module212, a space trigger module214, a notification module216, and/or other modules.
User module206may be configured to manage user information associated with users of system200. The user information may include user accounts and/or other user information associated with users of the system200. The user accounts and/or other user information may include information stored by server202, one or more of the client computing platforms204, and/or other storage locations. The user accounts may include, for example, information identifying users (e.g., a username or handle, a number, an identifier, and/or other identifying information) within the virtual space, security login information (e.g., a login code or password), virtual space account information, subscription information, virtual currency account information (e.g., related to currency held in credit for a user), relationship information (e.g., information related to relationships between users in the virtual space), virtual space usage information, demographic information associated with users, interaction history among users in the virtual space, information stated by users, purchase information of users, browsing history of users, a client computing platform identification associated with a user, a phone number associated with a user, and/or other information related to users.
The space module208may be configured to implement the instance of the virtual space executed by the computer modules to determine views of the virtual space. The views may then be communicated (e.g., via streaming, via object/position data, and/or other information) from server202to client computing platforms204for presentation to users. The view determined and transmitted to a given client computing platform204may correspond to a user character, or avatar, being controlled by a user via the given client computing platform204. The view determined and transmitted to a given client computing platform204may correspond to a location in the virtual space (e.g., the location from which the view is taken, the location the view depicts, and/or other locations), a zoom ratio, a dimensionality of objects, a point-of-view, and/or view parameters. One or more of the view parameters may be selectable by the user.
The instance of the virtual space may comprise a simulated space that is accessible by users via clients (e.g., client computing platforms204) that present the views of the virtual space to a user. The simulated space may have a topography, express ongoing real-time interaction by one or more users, and/or include one or more objects positioned within the topography that are capable of locomotion within the topography. In some instances, the topography may be a 2-dimensional topography. In other instances, the topography may be a 3-dimensional topography. The topography may include dimensions of the space, and/or surface features of a surface or objects that are “native” to the space. In some instances, the topography may describe a surface (e.g., a ground surface) that runs through at least a substantial portion of the space. In some instances, the topography may describe a volume with one or more bodies positioned therein (e.g., a simulation of gravity-deprived space with one or more celestial bodies positioned therein). The instance executed by the computer modules may be synchronous, asynchronous, and/or semi-synchronous.
The above description of the manner in which views of the virtual space are determined by space module208is not intended to be limiting. The space module208may be configured to express the virtual space in a more limited, or more rich, manner. For example, views determined for the virtual space may be selected from a limited set of graphics depicting an event in a given place within the virtual space. The views may include additional content (e.g., text, audio, pre-stored video content, and/or other content) that describes particulars of the current state of the place, beyond the relatively generic graphics. For example, a view may include a generic battle graphic with a textual description of the opponents to be confronted. Other expressions of individual places within the virtual space are contemplated.
Within the instance(s) of the virtual space executed by space module208, users may control characters, objects, simulated physical phenomena (e.g., wind, rain, earthquakes, and/or other phenomena), and/or other elements within the virtual space to interact with the virtual space and/or each other. The user characters may include avatars. As used herein, the term “user character” may refer to an object (or group of objects) present in the virtual space that represents an individual user, such as an avatar. The user character may be controlled by the user with which it is associated. The user controlled element(s) may move through and interact with the virtual space (e.g., non-user characters in the virtual space, other objects in the virtual space). The user controlled elements controlled by and/or associated with a given user may be created and/or customized by the given user. The user may have an “inventory” of virtual goods and/or currency that the user can use (e.g., by manipulation of a user character or other user controlled element, and/or other items) within the virtual space.
The users may participate in the instance of the virtual space by controlling one or more of the available user controlled elements in the virtual space. Control may be exercised through control inputs and/or commands input by the users through client computing platforms204. The users may interact with each other through communications exchanged within the virtual space. Such communications may include one or more of textual chat, instant messages, private messages, voice communications, and/or other communications. Communications may be received and entered by the users via their respective client computing platforms204. Communications may be routed to and from the appropriate users through server202(e.g., through space module208).
The relationship module210may be configured to establish relationships between users within the virtual210. Such relationships may include one or more of friendships, guilds (with guild-mates), alliances, connections, followers, and/or other relationships. The relationship module210may establish relationships based on relationship requests and acceptances received from users. Establishment of a relationship may be initiated by a single communication (e.g., a request) initiated by a given user requesting a relationship between the given user and one or more other users. Establishment of a relationship may require a first communication from the given user to be approved by the one or more other users. Relationships may include one or more types of relationships that have a functional purpose or impact within the virtual space, and/or one or more types of relationships that a social construct within the virtual space that does not have a functional result.
In some implementations, one of the classes of relationships provided by a system200may include an observer/target relationship. An observer may include a user that has privileges within the virtual space and/or system200generally to observe information related to use of system200by one or more target users. For example, an observer may be a parent that has privileges that facilitate observation of information related to user of system200by one or more of the parents children, which may be target users. As is described herein, in some implementations, an observer may have control over the access of a target to the virtual space, use of the virtual space by the target, and/or control over the experience of the target within the virtual space. An observer/target relationship may be established between users at the time of user account creation (e.g., by a parent or guardian authorizing the new account of a child user), and/or at other times.
Location module212may be configured to obtain location information indicating the real-world locations of the users of system200(e.g., as described above, or elsewhere herein). Location module212may be configured to obtain such location information from devices being carried by the users. In some implementations, the devices may include client computing platforms204, and/or other devices (e.g., dedicated tracking/geolocation devices). The location information may include information obtained by the devices, and then communicated to location module server202(e.g., wirelessly). The location information may indicate times at which the users were at the indicated locations.
Space trigger module214may be configured to trigger events within the virtual space based on the location information obtained by location module212. By way of illustration, a first event may be triggered based on a first user breaching a geofence surrounding or associated with a location in the real-world. Determination that the first user has breached the geofence may be made by space trigger module214based on location information for the first user. The first event may have an impact within the virtual space. The impact may include, for example, an award (or loss) of points, gold, experience points, gems, jewels, and/or other virtual currency; unlocking of content within the virtual space (e.g., one or more additional areas, buildings, rooms, and/or other content); reception of a virtual item; alteration of the visual expression of the virtual space in views provided to the user (e.g., with the addition of branding or badges in the views), and/or other impacts. One or more impacts of the first event triggered by space trigger module214may be apparent in the views of the virtual space provided to the first user by space module208. One or more of the impacts of the first event may apparent in views of the virtual space provided to other users by space module208. For example, an avatar associated with the first user may bear a visual indicator (and/or some other indicator) of one or more impacts of the first event.
The triggering of the first event may be conditioned on a time at which the geofence was breached. For example, there may be a time period during which the breach of geofence results in the triggering of the first event. As an example, there may be a time period during which breach of the geofence does not result in the triggering of the first event (e.g., if it would otherwise).
Space trigger module214may be configured such that one or more of the events, the circumstances that cause the one or more events, the impact of the one or more events, and/or other aspects of the one or more events are configured by users. For example, an observer may configure one or more events that incentivize a target user (e.g., with positive or desirable impacts in the virtual space) to perform real-world tasks. As another example, a real-world merchant, brand, or service provider may configure one or more events that incentivize users generally to perform real-world tasks that are beneficial to the real-world merchant, brand, or service provider (e.g., visit a place of business and/or other tasks). Space trigger module214may be configured such that configuration of an event may require monetary compensation from the user configuring the event. Space trigger module214may be configured to provide a user interface to users that facilitates the configuration of an event to be triggered by space trigger module214.
By way of illustration,FIG. 3illustrates a view220of a graphical user interface provided to users to configure an event in the virtual space. View220may include a title field222, a user field224, one or more trigger parameter fields226, one or more event impact fields228, and/or other fields or information. Title field222may be configured to receive entry and/or selection of a title for the event. User field224may be configured to receive entry and/or selection of a user (or group of users) for whom the event may be triggered in the virtual space. Entry and/or selection of a user (or group of users) may include one or more specification of a specific user, specification of one or more characteristics of users, and/or other specifications. Trigger parameter fields226may be configured to receive entry and/or selection of one or more trigger parameter that are used to trigger the event. A trigger parameter may include an real-world location parameter, an real-world time parameter, and/or other parameter. Event impact fields228may be configured to receive entry and/or selection of the parameter of the impact of the event. Provision of view220to users of a system (e.g., such as system200) may enhance the engagement of users with the virtual space, may enhance user control and/or customization of the user experience, and/or may provide other enhancements to the virtual space.
Returning toFIG. 2, notification module216may be configured to provide notifications to observers related to the real-world activities of the corresponding target users. Notification module216may trigger notifications based on the location information for the target users obtained by space trigger module214. For example, a first notification to a first observer may be triggered responsive to a first target user breaching a geofence surrounding or associated with a location in the real-world. Determination that the first user has breached the geofence may be made by notification module216based on location information for the first target user. The first notification may indicate to the first observer the breaching of the geofence. The notification may include a phone call, an email, a text message (e.g., an SMS message or other text message), a message within the virtual space, a message in a social networking platform (e.g., Facebook®, MySpace®, OpenFeint, and/or other social networking platforms), a game center message, a micro-blogging service message (e.g., such as a message in the platform provided by Twitter®, the platform provided by Tumblr®, and/or other micro-blogging platforms), and/or other notifications.
The triggering of the first notification may be conditioned on a time at which the geofence was breached. For example, there may be a time period during which the breach of geofence results in the triggering of the first notification. As an example, there may be a time period during which breach of the geofence does not result in the triggering of the first notification (e.g., if it would otherwise).
Notification module216may be configured such that one or more of the notifications, the circumstances that cause the one or more notifications, the impact of the one or more notifications, and/or other aspects of the one or more notifications are configured by users (e.g., the observers). For example, an observer may configure one or more notifications for one or more specific target users to monitor the real-world activities of the one or more specific target users. Notification module216may be configured to provide a user interface to observers that facilitates the configuration of a notification to be triggered by notification module216.
By way of illustration,FIG. 4illustrates a view230of a graphical user interface provided to users to configure an event in the virtual space. View230may include a title field232, a target user field234, one or more trigger parameter fields236, one or more notification delivery fields238, and/or other fields or information. Title field232may be configured to receive entry and/or selection of a title for the notification. Target user field234may be configured to receive entry and/or selection of a target user (or group of target users) for whom the notification may be triggered in the virtual space. Entry and/or selection of a target user (or group of target users) may include one or more specification of a specific target user, specification of one or more characteristics of target users, and/or other specifications. Trigger parameter fields236may be configured to receive entry and/or selection of one or more trigger parameter that are used to trigger the notification. A trigger parameter may include an real-world location parameter, an real-world time parameter, and/or other parameter. Notification delivery fields238may be configured to receive entry and/or selection of the form in which the notification should be delivered to the observer. Provision of view230to observer users of a system (e.g., such as system200) may provide a practical mechanism for monitoring the real-world activities of target users that is engaging and rewarding for the target users. This may enhance the likelihood of target users agreeing to participate in the monitoring activity, and/or provide other enhancements.
Returning toFIG. 2, In some implementations, server202, client computing platforms204, location devices (if separate from client computing platforms204, not shown), and/or external resources240may be operatively linked via one or more electronic communication links. For example, such electronic communication links may be established, at least in part, via a network such as the Internet and/or other networks. It will be appreciated that this is not intended to be limiting, and that the scope of this disclosure includes implementations in which servers202, client computing platforms204, and/or external resources240may be operatively linked via some other communication media.
A given client computing platform204may include one or more processors configured to execute computer program modules. The computer program modules may be configured to enable an expert or user associated with the given client computing platform204to interface with system200and/or external resources240, and/or provide other functionality attributed herein to client computing platforms204. By way of non-limiting example, the given client computing platform204may include one or more of a desktop computer, a laptop computer, a handheld computer, a NetBook, a Smartphone, a gaming console, and/or other computing platforms.
The external resources240may include sources of information, hosts and/or providers of virtual environments outside of system200, external entities participating with system200, and/or other resources. In some implementations, some or all of the functionality attributed herein to external resources38may be provided by resources included in system200.
The server202may include electronic storage242, one or more processors244, and/or other components. The server202may include communication lines, or ports to enable the exchange of information with a network and/or other computing platforms. Illustration of server202inFIG. 2is not intended to be limiting. The server202may include a plurality of hardware, software, and/or firmware components operating together to provide the functionality attributed herein to server202. For example, server202may be implemented by a cloud of computing platforms operating together as server202.
Electronic storage242may comprise electronic storage media that electronically stores information. The electronic storage media of electronic storage242may include one or both of system storage that is provided integrally (i.e., substantially non-removable) with server202and/or removable storage that is removably connectable to server202via, for example, a port (e.g., a USB port, a firewire port, etc.) or a drive (e.g., a disk drive, etc.). Electronic storage242may include one or more of optically readable storage media (e.g., optical disks, etc.), magnetically readable storage media (e.g., magnetic tape, magnetic hard drive, floppy drive, etc.), electrical charge-based storage media (e.g., EEPROM, RAM, etc.), solid-state storage media (e.g., flash drive, etc.), and/or other electronically readable storage media. The electronic storage242may include one or more virtual storage resources (e.g., cloud storage, a virtual private network, and/or other virtual storage resources). Electronic storage242may store software algorithms, information determined by processor244, information received from server202, information received from client computing platforms204, and/or other information that enables server202to function properly.
Processor(s)244is configured to provide information processing capabilities in server202. As such, processor244may include one or more of a digital processor, an analog processor, a digital circuit designed to process information, an analog circuit designed to process information, a state machine, and/or other mechanisms for electronically processing information. Although processor244is shown inFIG. 2as a single entity, this is for illustrative purposes only. In some implementations, processor244may include a plurality of processing units. These processing units may be physically located within the same device, or processor244may represent processing functionality of a plurality of devices operating in coordination. The processor244may be configured to execute modules206,208,210,212,214, and/or216. Processor244may be configured to execute modules206,208,210,212,214, and/or216by software; hardware; firmware; some combination of software, hardware, and/or firmware; and/or other mechanisms for configuring processing capabilities on processor244.
It should be appreciated that although modules206,208,210,212,214, and/or216are illustrated inFIG. 2as being co-located within a single processing unit, in implementations in which processor244includes multiple processing units, one or more of modules206,208,210,212,214, and/or216may be located remotely from the other modules. The description of the functionality provided by the different modules206,208,210,212,214, and/or216described below is for illustrative purposes, and is not intended to be limiting, as any of modules206,208,210,212,214, and/or216may provide more or less functionality than is described. For example, one or more of modules206,208,210,212,214, and/or216may be eliminated, and some or all of its functionality may be provided by other ones of modules206,208,210,212,214, and/or216. As another example, processor244may be configured to execute one or more additional modules that may perform some or all of the functionality attributed below to one of modules206,208,210,212,214, and/or216.
FIG. 5illustrates a method250of hosting a virtual space in which events may be triggered by real-world activities of the users. The operations of method250presented below are intended to be illustrative. In some embodiments, method250may be accomplished with one or more additional operations not described, and/or without one or more of the operations discussed. Additionally, the order in which the operations of method250are illustrated inFIG. 5and described below is not intended to be limiting.
In some embodiments, method250may be implemented in one or more processing devices (e.g., a digital processor, an analog processor, a digital circuit designed to process information, an analog circuit designed to process information, a state machine, and/or other mechanisms for electronically processing information). The one or more processing devices may include one or more devices executing some or all of the operations of method250in response to instructions stored electronically on an electronic storage medium. The one or more processing devices may include one or more devices configured through hardware, firmware, and/or software to be specifically designed for execution of one or more of the operations of method250.
At an operation252, event information related to a first event may be obtained. The event information may include one or more trigger parameters, one or more event impacts, a title, a user, and/or other information. The event information may be obtained, for example through a user interface presented to users to configure customized events. In some implementations, operation252may be performed by a space trigger module the same as or similar to space trigger module214(shown inFIG. 2and described herein).
At an operation254, user location information for a first user may be obtained. the user location information may indicate a real-world location of the first user. The user location information may include time information. In some implementations, operation254may be performed by a location module the same as or similar to location module212(shown inFIG. 2and described herein).
At an operation256, the first event may be triggered for the first user based on the obtained user location information. The first event may be triggered responsive to the obtained user location information indicating the first user has satisfied event criteria specified by the event information obtained at operation252. In some implementations, operation256may be performed by a space trigger module the same as or similar to space trigger module214(shown inFIG. 2and described herein).
At an operation258, responsive to the triggering of the first event, event impact associated with the first event may be manifested for the first user in the virtual space. The impact may include, without limitation, an award, a change in the visual depiction of the virtual space, an enhance access to content in the virtual space, and/or other impacts in the virtual space. The impact may be dictated by the event information obtained at operation252. In some implementations, operation258may be performed by a space trigger module the same as or similar to space trigger module214(shown inFIG. 2and described herein) in conjunction with a space module the same as or similar to space module208(shown inFIG. 2and described herein).
FIG. 6illustrates a method260of hosting a virtual space in which notifications to observers may be triggered by real-world activities of target users of the virtual space. The virtual space may include events triggered based on the real-world activities of the target users (e.g., according to method250shown inFIG. 5) in order to enhance participation in the monitoring by the target users. The operations of method260presented below are intended to be illustrative. In some embodiments, method260may be accomplished with one or more additional operations not described, and/or without one or more of the operations discussed. Additionally, the order in which the operations of method260are illustrated inFIG. 6and described below is not intended to be limiting.
In some embodiments, method260may be implemented in one or more processing devices (e.g., a digital processor, an analog processor, a digital circuit designed to process information, an analog circuit designed to process information, a state machine, and/or other mechanisms for electronically processing information). The one or more processing devices may include one or more devices executing some or all of the operations of method260in response to instructions stored electronically on an electronic storage medium. The one or more processing devices may include one or more devices configured through hardware, firmware, and/or software to be specifically designed for execution of one or more of the operations of method260.
At an operation262, notification information related to a first notification may be obtained. The notification information may include one or more trigger parameters, one or more delivery mechanisms, a title, a target user, and/or other information. The notification information may be obtained, for example through a user interface presented to a first observer to configure customized notifications. In some implementations, operation262may be performed by a notification module the same as or similar to notification module216(shown inFIG. 2and described herein).
At an operation264, user location information for a first target user may be obtained. the user location information may indicate a real-world location of the first target user. The user location information may include time information. In some implementations, operation264may be performed by a location module the same as or similar to location module212(shown inFIG. 2and described herein).
At an operation266, the first notification may be triggered based on the obtained user location information. The first notification may be triggered responsive to the obtained user location information indicating the first target user has satisfied event criteria specified by the notification information obtained at operation262. In some implementations, operation266may be performed by a notification module the same as or similar to notification module216(shown inFIG. 2and described herein).
At an operation268, responsive to the triggering of the first notification, notification may be transmitted to the first observer. The notification may include an email, a text message, a virtual space message, a phone call, and/or other messages or notifications. The notification may indicate the first notification has been triggered. In some implementations, operation268may be performed by a notification module the same as or similar to notification module216(shown inFIG. 2and described herein).
Although the present technology has been described in detail for the purpose of illustration based on what is currently considered to be the most practical and preferred implementations, it is to be understood that such detail is solely for that purpose and that the technology is not limited to the disclosed implementations, but, on the contrary, is intended to cover modifications and equivalent arrangements that are within the spirit and scope of the appended claims. For example, it is to be understood that the present technology contemplates that, to the extent possible, one or more features of any implementation can be combined with one or more features of any other implementation.
Claims
- A system configured to trigger events in a client application, the system comprising: one or more processors configured to execute computer program modules to: obtain real-world location information specifying a real-world location of a first user;obtain event information defining real-world location criteria that will trigger an event within an interactive client application hosted over the network, the real-world location criteria defining a set of real-world locations;compare the real-world location of the first user as specified by the real-world location information for the first user with the real-world location criteria for the event to determine whether the real-world location of the first user as specified by the real-world location information for the first user satisfies the real-world location criteria by being within the set of real-world locations defined by the real-world location criteria;and responsive to the real world location of the first user as specified by the real-world location information satisfying the real-world location criteria for the event, triggering the event for the first user in the client application;wherein obtaining the event information for the event triggered for the first user includes obtaining the event information that defines the real-world location criteria via a graphical user interface configured to receive entry or selection of the event information from a second user that is different from the first user.
- The system of claim 1 , wherein the computer program modules further configured to obtain notification information defining real-world location criteria that will trigger a notification within an interactive client application hosted over a network, to compare the real-world location information for the first user with the real-world location criteria for the notification, and, responsive to the real-world location information indicating the first user has satisfied the real-world location criteria for the notification, transmitting a notification transmission to an observer of the first user.
- The system of claim 2 , wherein the real-world location criteria for the notification is different from the real-world location criteria for the event.
- The system of claim 2 , wherein the real-world criteria for the notification is the same as the real-world criteria for the event.
- The system of claim 1 , wherein obtaining notification information defining real-world location criteria that will trigger a notification is configured to obtain the notification information via a graphical user interface configured to receive entry or selection of the notification information from the observer.
- The system of claim 1 , wherein the notification transmission includes one or more of an email, a message in a social networking platform, a message in a micro-blogging service, a text message, a phone call, or a client application message.
- A system configured to trigger the manifestation of one or more impacts in a client application, the system comprising: one or more processors configured to execute computer program modules to: obtain real-world location information specifying a real-world location of a first user;obtain impact information defining real-world location criteria that will trigger a manifestation of one or more impacts within an interactive client application hosted over a network, the real-world location criteria defining a set of real-world locations;compare real-world location information that indicates the real-world location of the first user with the real-world location criteria for the one or more impacts to determine whether the real-world location of the first user as specified by the real-world location information for the first user satisfies the real-world location criteria by being within the set of real-world locations defined by the real-world location criteria;and responsive to the real-world location information the real world location of the first user satisfying the real-world location criteria for the one or more impacts, triggering the manifestation of the one or more impacts in the client application for the first user;wherein obtaining the impact information that defines the real-world location criteria for the real-world location criteria triggered for the first user including obtaining the one or more impacts via a graphical user interface configured to receive entry or selection of the one or more impacts from a second user.
- The system of claim 7 , wherein obtaining impact information defining real-world location criteria that will trigger a manifestation of one or more impacts is configured such that the one or more impacts are only apparent in views of the client application provided to the first user.
- The system of claim 7 wherein obtaining impact information defining real-world location criteria that will trigger a manifestation of one or more impacts is configured such that the one or more impacts are apparent in views of the client application provided to a third user.
- A computer-implemented method of triggering events a client application, the method being implemented in a computer system that includes one or more processors configured to execute computer program modules, the method comprising: obtaining real-world location information specifying a real-world location of a first user;obtaining notification information defining real-world location criteria that will trigger a notification within an interactive client application hosted over a network, the real-world location criteria defining a set of real-world locations;comparing the real-world location information for the first user with the real-world location criteria for the notification to determine whether the real-world location of the first user as specified by the real-world location information for the first user satisfies the real-world location criteria by being within the set of real-world locations defined by the real-world location criteria;and responsive to the real world location of the first user as specified by the real-world location information satisfying the real-world location criteria for the notification, transmitting a notification transmission to an observer of the first user.
- The method of claim 10 , further comprising: obtaining event information defining real-world location criteria that will trigger an event within the client application;comparing the real-world location information for the first user with the real-world location criteria for the event;and responsive to the real-world location information indicating the first user has satisfied the real-world location criteria for the event, triggering the event for the first user in the client application, wherein the event information for the event triggered for the first user is obtained via a graphical user interface configured to receive entry or selection of the event information from the a second user that is different from the first user.
- The method of claim 11 , wherein the real-world location criteria for the notification is different from the real-world location criteria for the event.
- The method of claim 11 , wherein the real-world criteria for the notification is the same as the real-world criteria for the event.
- The method of claim 10 , wherein the notification information is obtained via a graphical user interface configured to receive entry or selection of the notification information from the observer.
- The method of claim 10 , wherein the notification transmission includes one or more of an email, a message in a social networking platform, a message in a micro-blogging service, a text message, a phone call, or a client application message.
- The method of claim 11 , wherein the observer is the second user.
Disclaimer: Data collected from the USPTO and may be malformed, incomplete, and/or otherwise inaccurate.