DETAILED DESCRIPTION Techniques described herein can be performed on any type of computer system including a personal computer, a home video game machine, a portable video game machine, a networked server and display, a cellular telephone, a personal digital assistant, or any other type of device or arrangement having computation and graphical display capabilities. One exemplary illustrative non-limiting implementation includes a home video game system such as the Nintendo Wii 3D video game system, a Nintendo DS or other 3D capable interactive computer graphics display systems. One exemplary illustrative non-limiting implementation is described below, but other implementations are possible. In an exemplary embodiment, a player using video game machine100is connected to the internet or other network130and plays games online. The player game consoles100can communicate with the central service computer140through the internet network in a known manner. A server140hosts a game environment the player's avatar can operate within. As shown inFIG. 1, a plurality of video game consoles100, each connected to TV monitors110are connected to the internet130through an internet server provider (ISP)120or by other means. Each of the players operating the game consoles100has access to a central service computer140. Access to computer140results in the establishment of user identification information available to the central service computer140such as creation of identification records (assuming the user has given permission to disclose confidential information). The user game console100can be coupled to the central service computer in ways other than through the internet. For example, telephone wire connection may be used through modulator/demodulators (modem) or any other data communications means can be used. Each player using a game machine100can log into the network130and be connected to the central service computer140so that he/she can start playing a single player game. Once started, each player sees the same game scene150on his/her monitor110. The central service computer can offer ...
DETAILED DESCRIPTION
Techniques described herein can be performed on any type of computer system including a personal computer, a home video game machine, a portable video game machine, a networked server and display, a cellular telephone, a personal digital assistant, or any other type of device or arrangement having computation and graphical display capabilities. One exemplary illustrative non-limiting implementation includes a home video game system such as the Nintendo Wii 3D video game system, a Nintendo DS or other 3D capable interactive computer graphics display systems. One exemplary illustrative non-limiting implementation is described below, but other implementations are possible.
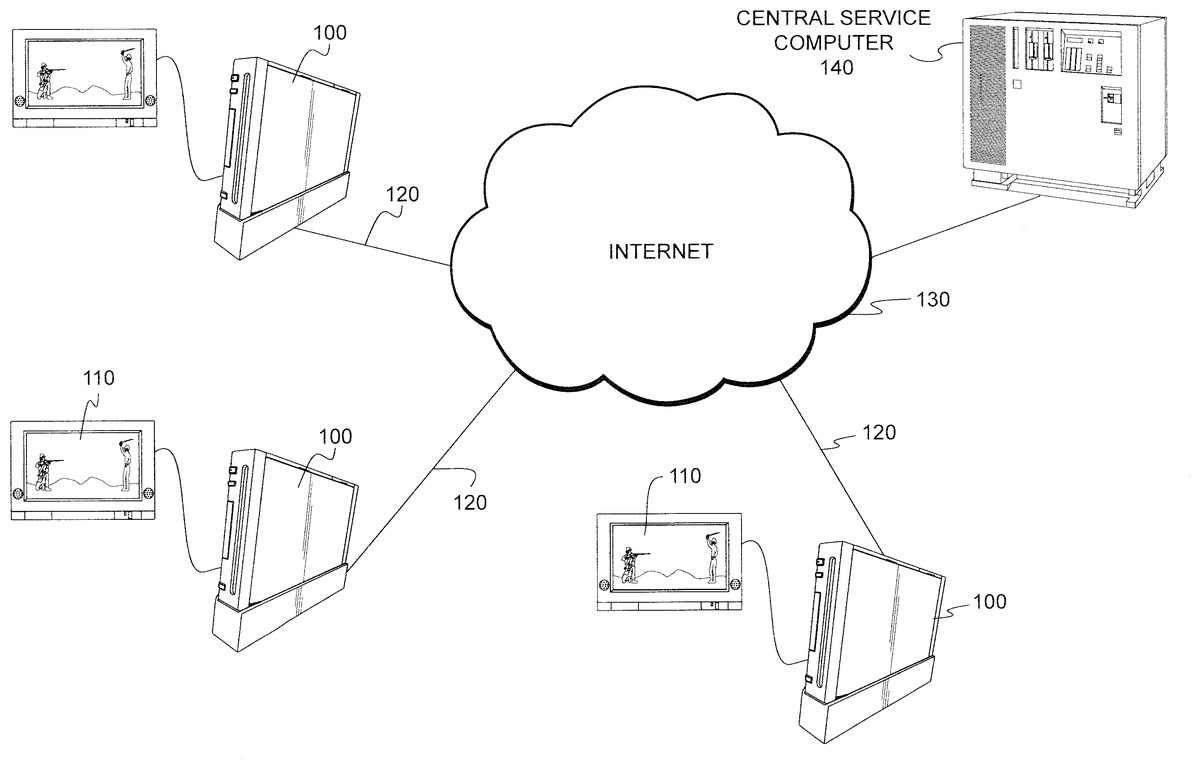
In an exemplary embodiment, a player using video game machine100is connected to the internet or other network130and plays games online. The player game consoles100can communicate with the central service computer140through the internet network in a known manner. A server140hosts a game environment the player's avatar can operate within.
As shown inFIG. 1, a plurality of video game consoles100, each connected to TV monitors110are connected to the internet130through an internet server provider (ISP)120or by other means. Each of the players operating the game consoles100has access to a central service computer140. Access to computer140results in the establishment of user identification information available to the central service computer140such as creation of identification records (assuming the user has given permission to disclose confidential information).
The user game console100can be coupled to the central service computer in ways other than through the internet. For example, telephone wire connection may be used through modulator/demodulators (modem) or any other data communications means can be used.
Each player using a game machine100can log into the network130and be connected to the central service computer140so that he/she can start playing a single player game. Once started, each player sees the same game scene150on his/her monitor110. The central service computer can offer the same game features, capabilities and general game background to each of the plurality of players who have access to it through the network130.
FIG. 2Ashows a typical game scene that a first human player sees when he/she plays a single player game on his/her game console100. The scene includes a game character210which is controlled by the first player. The central service computer has data comprising game related information such as game characters associated to various players stored in its data base. When a player accesses the central service computer to start playing a game, all the game related data stored in the central service computer becomes available to the player.
Turning back toFIG. 2A, the game character210carries tools230. The game character210, controlled by the first player, can build a structure such as a house. The game character210sees building materials240and decides to build a house. Hence, as can be seen inFIG. 2B, the first player builds a house250. As a result of the actions of the game character210, the house is constructed and becomes part of the environment. After game character210successfully accomplishes his/her goal, then he/she moves on to other parts of the game world available to game character210.
According to the exemplary embodiment, the house constructed by player210becomes part of the virtual environment available to any other player who wishes to play the game. Therefore, when the second player who controls a game character220plays the same game that was played by the first player, he/she encounters his/her game character220in the state shown inFIG. 2B, that is the house constructed by game character210is available to player220. From this point on, the second player can continue playing the game, controlling his/her character220and affecting virtual objects and other game characters in the game world.
As another example, player character210can gossip to a non-player character who can then report the story to a player character220without player characters210,220ever seeing or interacting with one another—even though they may be in the same room at the same time.
In another exemplary embodiment, the actions of a player playing in a single-player game may trigger events that affect the playing of other players playing the same single-player game at the same or a later time.
For example, a certain item in the game, for example, a purse in a store that sells high fashion items may get very popular, as many players playing their single-player online games decide to buy that item. This event then may trigger the price of the item to increase or the item becoming unavailable for players who play their games subsequently. Or, in a simulation of a world market online game, the price of a certain commodity, such as oil, may fluctuate depending on various actions of players playing their single-player online games, for example, a country controlled by a player invading another oil-rich country. The effect of these actions then are felt by other players who play the same game later, as they experience market conditions that reflect the increased price of oil, e.g., higher cost of living, higher inflation, etc.
In another embodiment, a player can interact only with other player avatars the player has “friended” or otherwise authorized interaction with. In this implementation, even though the player is affected indirectly (through the environment including non-player characters) by all other player avatars in a massively multiplayer environment, the player avatar only needs to interact with avatars of those other players he or she knows beforehand, thus preserving privacy and protecting the player from unknown or undesired interactions.
FIG. 3shows a flowchart of an exemplary illustrative non-limiting process performed by the central server140to dynamically operate a single-player online game so that the actions of one player playing the game can affect the status of the game being played by other players at the same time or a later time.
After a single-player game starts, the central server140determines whether the particular game has been played within a predetermined time period (step S10). If the answer is negative, then the central server140initializes all key data in its database in step S20. Key data my include, for example, the lifetime of each game character that has been created in the particular game, the strength of each game character, the financial status of each game character, etc. However, if the answer is affirmative, then the central server accesses key data that is stored in its key data database (step S30) and moves to step S40(described later). After initialization, or after step S30, the server140polls the game at the current time in step S40. In this step, the server140records the current value of the various predetermined key data parameters, a value that is directly affected by the actions of the player that plays the single-player game. Subsequently, in step S50, the server140updates the key data database based on the polled values. This polling and updating process occurs at predetermined regular time intervals, for example, a few msec, so that the central server140takes a reasonably representative sampling of the dynamic evolution of the single-player game. Following step S50, the central server triggers various events in the game space depending on the values of the key data being updated, including setting global variables (step S60). Next, it is determined if the single player game has ended (step S70). If the game continues, then the process goes back to step S40to perform more polling of the game key parameters. On the other hand, if it is determined that the game has reached its end, then the central server stores the current key data in the key data database (step S80) and the programs ends.
The above disclosed technique and system allows a player to play games that are more dynamic and are not pre-scripted like conventional single-player games. Moreover, the player does not need to directly interact with other people and is provided with a measure of appreciated privacy. Hence, the disclosed online game offers play involving other players without actually requiring interacting with others in real time.
While the technology herein has been described in connection with exemplary illustrative non-limiting implementations, the invention is not to be limited by the disclosure. The invention is intended to be defined by the claims and to cover all corresponding and equivalent arrangements whether or not specifically disclosed herein.