U.S. Pat. No. 8,738,533
Real-world items unlocking virtual items online and in video games
AssigneeDisney Enterprises, Inc.
Issue DateNovember 19, 2009
Illustrative Figure
Abstract
There is provided a system and method for providing access to a virtual object corresponding to a real object. There is provided a method comprising authenticating a user account for a networked application, confirming a validity of a user provided code, wherein the code is visible on the real object or on accompanying materials of the real object, and granting the user account access to the virtual object for use in the networked application in response to the confirming of the validity. As a result, users are enabled to enjoy interactions with real objects as well as corresponding virtual objects both in an offline video game context and in an online network application context.
Description
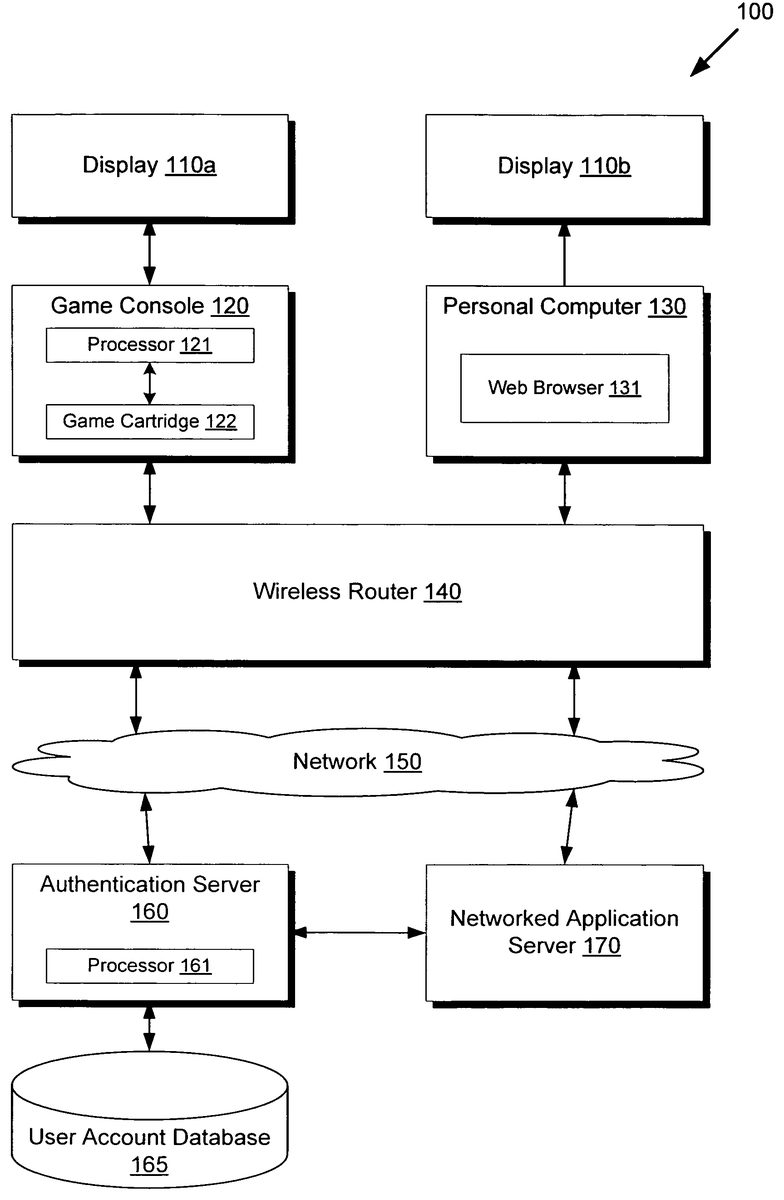
DETAILED DESCRIPTION OF THE INVENTION The present application is directed to a system and method for providing access to a virtual object corresponding to a real object. The following description contains specific information pertaining to the implementation of the present invention. One skilled in the art will recognize that the present invention may be implemented in a manner different from that specifically discussed in the present application. Moreover, some of the specific details of the invention are not discussed in order not to obscure the invention. The specific details not described in the present application are within the knowledge of a person of ordinary skill in the art. The drawings in the present application and their accompanying detailed description are directed to merely exemplary embodiments of the invention. To maintain brevity, other embodiments of the invention, which use the principles of the present invention, are not specifically described in the present application and are not specifically illustrated by the present drawings. FIG. 1presents a diagram of a system for providing access to a virtual object corresponding to a real object, according to one embodiment of the present invention. Diagram100ofFIG. 1includes displays110a-110b, game console120, personal computer130, wireless router140, network150, authentication server160, user account database165, and networked application server170. Game console120includes processor121and game cartridge122. Personal computer130includes web browser131. Authentication server160includes processor161. Game console120may be designed for home use, in which case display110amay comprise an externally connected display such as a television, or game console120may be designed for portable use, in which case display110amay comprise a touch sensitive internal display. Game console120may use processor121to execute game cartridge122, containing program and asset data for a video game application, and also storing user settings such as saved game progress. While game console120may be used independently of any network connections, game console120may also support network connectivity. ...
DETAILED DESCRIPTION OF THE INVENTION
The present application is directed to a system and method for providing access to a virtual object corresponding to a real object. The following description contains specific information pertaining to the implementation of the present invention. One skilled in the art will recognize that the present invention may be implemented in a manner different from that specifically discussed in the present application. Moreover, some of the specific details of the invention are not discussed in order not to obscure the invention. The specific details not described in the present application are within the knowledge of a person of ordinary skill in the art. The drawings in the present application and their accompanying detailed description are directed to merely exemplary embodiments of the invention. To maintain brevity, other embodiments of the invention, which use the principles of the present invention, are not specifically described in the present application and are not specifically illustrated by the present drawings.
FIG. 1presents a diagram of a system for providing access to a virtual object corresponding to a real object, according to one embodiment of the present invention. Diagram100ofFIG. 1includes displays110a-110b, game console120, personal computer130, wireless router140, network150, authentication server160, user account database165, and networked application server170. Game console120includes processor121and game cartridge122. Personal computer130includes web browser131. Authentication server160includes processor161.
Game console120may be designed for home use, in which case display110amay comprise an externally connected display such as a television, or game console120may be designed for portable use, in which case display110amay comprise a touch sensitive internal display. Game console120may use processor121to execute game cartridge122, containing program and asset data for a video game application, and also storing user settings such as saved game progress. While game console120may be used independently of any network connections, game console120may also support network connectivity. For example, game console120may support WiFi communications, thus allowing a wireless connection to wireless router140providing access to network150.
Similarly, personal computer130may comprise a desktop computer connected to an external display110b, or may comprise a portable notebook computer having an internal display120b. Personal computer130may also connect to wireless router140by WiFi, providing access to web servers connected to network150, such as networked application server170.
Wireless router140may comprise a Wi-Fi compatible router with a broadband uplink to network150. The broadband uplink, not shown inFIG. 1, may be provided by a DSL modem, cable modem, fiber optic line, satellite link, or another connection method. Network150may comprise a publicly accessible network such as the Internet.
Authentication server160may provide user authentication services for networked application server170and game cartridge122executing on processor121of game console120, providing secure access to user account database165. User account database165may store data regarding user accounts for a persistently online social networking application supported by networked application server170, which may provide a web based interface accessible by web browsers such as web browser131executing on personal computer130.
After receiving an unlocking code printed directly on or accompanying a real object, a user of game console120may enter the code while game cartridge122is executing to unlock a corresponding virtual version of the real object. This virtual object may then be usable while game cartridge122is executing, or while the user is playing the game. However, if a connection to network150is available as shown inFIG. 1, and if the user provides login credentials such as a username or account number and password, then the same virtual object might also be unlocked for a networked application, such as a social networking application, executing on networked application server170. For example, game cartridge122may be programmed to verify user provided credentials using authentication server160, if a connection to network150is available. If authentication server160reports that the user is authorized, then authentication server160may be directed to modify the corresponding user account in user account database165to provide access to the newly unlocked virtual object.
Alternatively, the user may enter the unlocking code on a website. For example, the user may use personal computer130to direct web browser131to networked application server170. Networked application server170may then provide an interface to the social networking application, which may include a section to enter unlocking codes. After the user provides user account authentication credentials and the unlocking code to networked application server170, authentication server160may be used to access and modify a corresponding user account, similar to the process used by game console120above. In some cases, authentication might be expedited by depositing a session cookie with web browser131, allowing the user to bypass re-entry of user account authentication credentials such as a username and password.
Whether the code is entered on game console120executing game cartridge122or through personal computer130executing web browser131accessing networked application server170, a virtual version of a real object can be unlocked in user account database165, allowing the use of the virtual object within a social networking application supported by networked application server170. The virtual object may comprise, for example, an article of clothing or an accessory wearable or usable by an avatar of the user, a decoration or piece of furniture for placement in a virtual space or property, or any other object.
WhileFIG. 1only shows a single game console120, a single personal computer130, a single authentication server160, and a single networked application server170, alternative embodiments may support multiple connected game consoles and personal computers for multiplayer and multi-user interactivity, and multiple servers may be deployed for load balancing and improved network responsiveness.
FIGS. 2A and 2Bshow exemplary real objects, according to embodiments of the present invention. Diagram200ofFIG. 2Ashows jigsaw puzzle280ahaving a code285aprinted directly upon it. Diagram200ofFIG. 2Bshows dress280bincluding an attached tag281with a printed code285b.
Although shown as blank when fully assembled inFIG. 2A, jigsaw puzzle280amay, for example, show a cross-promotional image related to the contents of game cartridge122. For example, both game cartridge122and jigsaw puzzle280amay depict characters, scenes, and settings from a shared film, animation, book, or other creative work. After jigsaw puzzle280ais fully assembled by a user, a code285amay be clearly visible to the user. Although code285ais shown printed directly on a single jigsaw piece inFIG. 2A, alternative embodiments might spread code285aacross adjacent jigsaw pieces to encourage full completion of the jigsaw puzzle. Promotional materials for jigsaw puzzle280a, such as retail packaging or advertising copy, may emphasize that code285ais included with the jigsaw puzzle to unlock a virtual jigsaw puzzle in a corresponding video game, such as game cartridge122ofFIG. 1, or to unlock a virtual jigsaw puzzle for a social networking application supported by networked application server170ofFIG. 1. The virtual jigsaw puzzle may depict the same image as jigsaw puzzle280a, and may allow the user to play a virtual jigsaw puzzle game on game console120or personal computer130ofFIG. 1. The virtual jigsaw puzzle might also be shared or traded with other users.
While code285aand code285bare shown as a four digit numerical codes, alternative embodiments might use alphanumeric digits, artistic symbols, or other representations. For example, code285amight be shown as a one-dimensional or two-dimensional barcode, which may then be read by a camera of a mobile phone or another optical scanning device.
Dress280bmay, for example, comprise a dress sized for children or adults, or a smaller version suitable for dolls or figures. As shown inFIG. 2B, tag281may be attached to dress280b, explaining that code285bmay be used to unlock a virtual version of the dress “in-game” while playing game cartridge122ofFIG. 1or “on-site” while using the web based social networking application supported by networked application server170ofFIG. 1. Although code285is shown on tag281inFIG. 2B, code285might also be visible on other accompanying materials such as retail packaging for dress280b. The virtual version of dress280bmay comprise a visual replica of dress280b, having the same appearance, design, colors, and other visual features. Thus, when viewed on display110aor110bofFIG. 1, the virtual version of the dress may visually look like dress280b, subject to technological limitations such as low resolution or limited graphics hardware on game console120or personal computer130.
FIG. 3presents the exemplary output of displays in a system for providing access to a virtual object corresponding to a real object, according to one embodiment of the present invention. Diagram300ofFIG. 3includes displays310a-310b. With regards toFIG. 3, it should be noted that display310acorresponds to display110afromFIG. 1, and that display310bcorresponds to display110bfromFIG. 1.
As shown in display310a, which corresponds to a screen of game console120inFIG. 1, the user may be prompted to enter a code to unlock in-game items. After confirming that the entered code is valid, the virtual object, “Elegant Dress,” is accessible to the user, having the effect of increasing the user's “Charm” value by 10 points while playing game cartridge122ofFIG. 1. As previously discussed, if game console120has access to an Internet connection, the same “Elegant Dress” might also be unlocked for a networked application such as a web based social networking application. For example, game cartridge122may allow the user to enter in user credentials, such as a username and password, for authenticating and linking with the social networking application.
Thus, assuming the example above where an Internet connection is available to game console120, if the user decides to log in to her social networking account on personal computer130ofFIG. 1, she may see a screen similar to display310bofFIG. 3. Besides new information concerning her social network, she may also be notified that the “Elegant Dress” that was previously unlocked in the video game is also accessible for her avatar, as shown to the right in display310b. For example, game console120may have previously used authentication server160to store data in user account database165indicating the unlocking of the “Elegant Dress” for the user account. When networked application server170uses authentication server160to retrieve details concerning the user account, the virtual object “Elegant Dress” may also be retrieved. In this manner, the unlocked item is usable both within the video game in a non-networked environment and also in the social networking application within a networked environment.
FIG. 4shows a flowchart describing the steps, according to one embodiment of the present invention, by which access to a virtual object corresponding to a real object may be provided. Certain details and features have been left out of flowchart400that are apparent to a person of ordinary skill in the art. For example, a step may comprise one or more substeps or may involve specialized equipment or materials, as known in the art. While steps410through440indicated in flowchart400are sufficient to describe one embodiment of the present invention, other embodiments of the invention may utilize steps different from those shown in flowchart400.
Referring to step410of flowchart400inFIG. 4and diagram100ofFIG. 1, step410of flowchart400comprises processor161of authentication server160authenticating a user account stored in user account database165for a social networking application supported by networked application server170. For example, game console120or personal computer130may have established a connection to authentication server160over network150via a Wi-Fi connection to wireless router140, so that a user provided username and password can be checked for validity. As previously discussed, alternative user account credentials such as web browser cookies may be accepted in lieu of a user provided username and password. Processor161may then confirm that the provided credentials are valid by querying user account database165.
Referring to step420of flowchart400inFIG. 4, diagram100ofFIG. 1, and diagram200ofFIG. 2B, step420of flowchart400comprises processor161of authentication server160confirming a validity of code285b, wherein code285bis visible on tag281accompanying dress280b. Alternatively, referring toFIG. 2A, step420may confirm the validity of code285a, wherein code285ais visible as directly printed on jigsaw puzzle280a. For the present example, code285bshall be assumed. As with step410, step420may be in response to user input received from either game console120or personal computer130, but for the present example, user input from game console120shall be assumed. Thus, a user may enter in the digits “2345” representing code285busing, for example, touch sensitive display110a. This scenario is also depicted on display310aofFIG. 3. Game cartridge122may then contain a list of valid codes, which processor121can use to check against the user entry. If the verification is positive, then authentication server160may be notified. Alternatively, game console120may forward code285ato authentication server160, which may then verify code285aagainst its own internal list of valid codes. In either case, authentication server160is then able to confirm the validity of the user provided code285bfor unlocking a virtual version of dress280b.
Referring to step430of flowchart400inFIG. 4, diagram100ofFIG. 1, and diagram200ofFIG. 2B, step430of flowchart400comprises processor161of authentication server160, in response to step420, granting the user account authenticated in step410access to the virtual version of dress280bfor use in the social networking application supported by networked application server170. For example, a data object may be placed in the user account of user account database165, wherein the data object indicates access to a virtual “Elegant Dress” corresponding to dress280b.
Referring to step440of flowchart400inFIG. 4, diagram100ofFIG. 1, and diagram200ofFIG. 2B, step440of flowchart400comprises processor161of authentication server160to cause the social networking application supported by networked application server170to show the virtual “Elegant Dress” corresponding to dress280bon display110b. For example, the user may decide to log in to the social networking application on personal computer130, as previously described. Networked application server170may then query authentication server160for details regarding the user account, including any virtual items. Processor161may then discover that the user account has access to the virtual “Elegant Dress” in user account database165, thus notifying networked application server170to cause the “Elegant Dress” to show on display110bas part of the user's inventory or worn by an avatar of the user, as shown in display310bofFIG. 3. As a result, the user is enabled to enjoy virtual use of the virtual “Elegant Dress” corresponding to the real dress280b, both within the offline game cartridge122and the online social networking application. Of course, this is also applicable to any other item, such as jigsaw puzzle280aofFIG. 2A, opening up new cross-promotional opportunities and providing greater value and enjoyment for users, both in real and virtual worlds.
From the above description of the invention it is manifest that various techniques can be used for implementing the concepts of the present invention without departing from its scope. Moreover, while the invention has been described with specific reference to certain embodiments, a person of ordinary skills in the art would recognize that changes can be made in form and detail without departing from the spirit and the scope of the invention. As such, the described embodiments are to be considered in all respects as illustrative and not restrictive. It should also be understood that the invention is not limited to the particular embodiments described herein, but is capable of many rearrangements, modifications, and substitutions without departing from the scope of the invention.
Claims
- A method, for use by a hardware processor, for providing access to a virtual object corresponding to a real object having a code stored thereon, wherein a user enters the code into a game console, the method comprising: receiving, by the hardware processor, the code from the game console;confirming, by the hardware processor, a validity of the code;granting to the game console, by the hardware processor, access to the virtual object, in response to confirming the validity of the code;receiving, by the hardware processor, from the game console, account information associated with an account of the user;authenticating, by the hardware processor, the account information received from the game console;associating, by the hardware processor, the virtual object with the account of the user, in response to authenticating the account information received from the game console;receiving, by the hardware processor, the account information associated with the account of the user from a networked application server in communication with a computer over a network, wherein the computer is separate from the game console;authenticating, by the hardware processor, the account information received from the networked application server;and granting to the computer, by the hardware processor, access to the virtual object associated with the account of the user, in response to authenticating the account information received from the networked application server.
- The method of claim 1 , further comprising: causing the networked application to show the virtual object on a display.
- The method of claim 1 , wherein the code is obtained by the user from the real object in response to the user playing a game using the real object.
- The method of claim 1 , wherein the virtual object corresponds to the real object by comprising, in the networked application, a visual replica of the real object.
- The method of claim 1 , wherein the code is visible on the real object by being printed on the real object.
- The method of claim 1 , wherein the code becomes visible on the real object in response to the user playing the game using the real object.
- The method of claim 1 , wherein the real object is a puzzle, and wherein the code becomes visible by solving the puzzle.
- The method of claim 1 , wherein the code comprises a string of numeric digits.
- The method of claim 1 , wherein the code comprises a string of alphanumeric digits.
- The method of claim 1 , wherein the code comprises a bar code.
- The method of claim 1 , wherein the real object comprises a piece of clothing, and wherein the virtual object comprises a visual replica wearable by an avatar of the user account in the networked application.
- The method of claim 1 , wherein the networked application comprises a persistently online social networking application.
Disclaimer: Data collected from the USPTO and may be malformed, incomplete, and/or otherwise inaccurate.