U.S. Pat. No. 8,151,191
MANAGING OBJECTIONABLE MATERIAL IN 3D IMMERSIVE VIRTUAL WORLDS
AssigneeActivision Publishing Inc
Issue DateDecember 7, 2007
Illustrative Figure
Abstract
A method of and system for managing objectionable content in a virtual world associates a tag with an attribute associated with an avatar in the virtual world. The method places a limitation on the avatar in the virtual world based upon information in the tag while the tagged attribute is associated with the avatar.
Description
DETAILED DESCRIPTION OF THE PREFERRED EMBODIMENT Referring now to the drawings, and firstFIG. 1, a system according to the present invention is designated generally by the numeral100. System100includes a virtual world server101. Virtual world server101is typically a large computer system in which the virtual world exists. Virtual world server101is connected to a network103, such as the Internet. Virtual world server101is also coupled a database105, which contains all of the objects in the virtual world and their associated attributes. A plurality of user computers107are connected to network103. User computers107may be a computing device, such as personal computers, notebook computers, personal digital assistants, cell phones, and the like. Each user computer107has installed thereon a virtual world client application109. Virtual world client107renders a portion of the virtual world on user computer107and allows the user to control the actions of his or her avatar. FIG. 2illustrates a view into a virtual world from a user computer. The user of the computer is represented in the virtual world by an avatar201. The user's avatar201is identified in the virtual world by the name AVATAR A. A second avatar203is identified in the virtual world by the name AVATAR B. Avatar203is associated with another human user. As is known to those skilled in the art, users can move about, communicate, transact business, and essentially live in the virtual world through their associated avatars. In the example ofFIG. 2, the user associated with avatar201finds the clothing worn by avatar203to be inappropriate in some way. The clothing may be obscene, indecent, or scandalous, per se, inappropriate for a particular situation, inappropriate for view by persons in particular groups, such as children, or persons having particular social or cultural norms, or otherwise objectionable to the user associated with avatar201. It should be recognized that clothing is only an example of one ...
DETAILED DESCRIPTION OF THE PREFERRED EMBODIMENT
Referring now to the drawings, and firstFIG. 1, a system according to the present invention is designated generally by the numeral100. System100includes a virtual world server101. Virtual world server101is typically a large computer system in which the virtual world exists. Virtual world server101is connected to a network103, such as the Internet. Virtual world server101is also coupled a database105, which contains all of the objects in the virtual world and their associated attributes. A plurality of user computers107are connected to network103. User computers107may be a computing device, such as personal computers, notebook computers, personal digital assistants, cell phones, and the like. Each user computer107has installed thereon a virtual world client application109. Virtual world client107renders a portion of the virtual world on user computer107and allows the user to control the actions of his or her avatar.
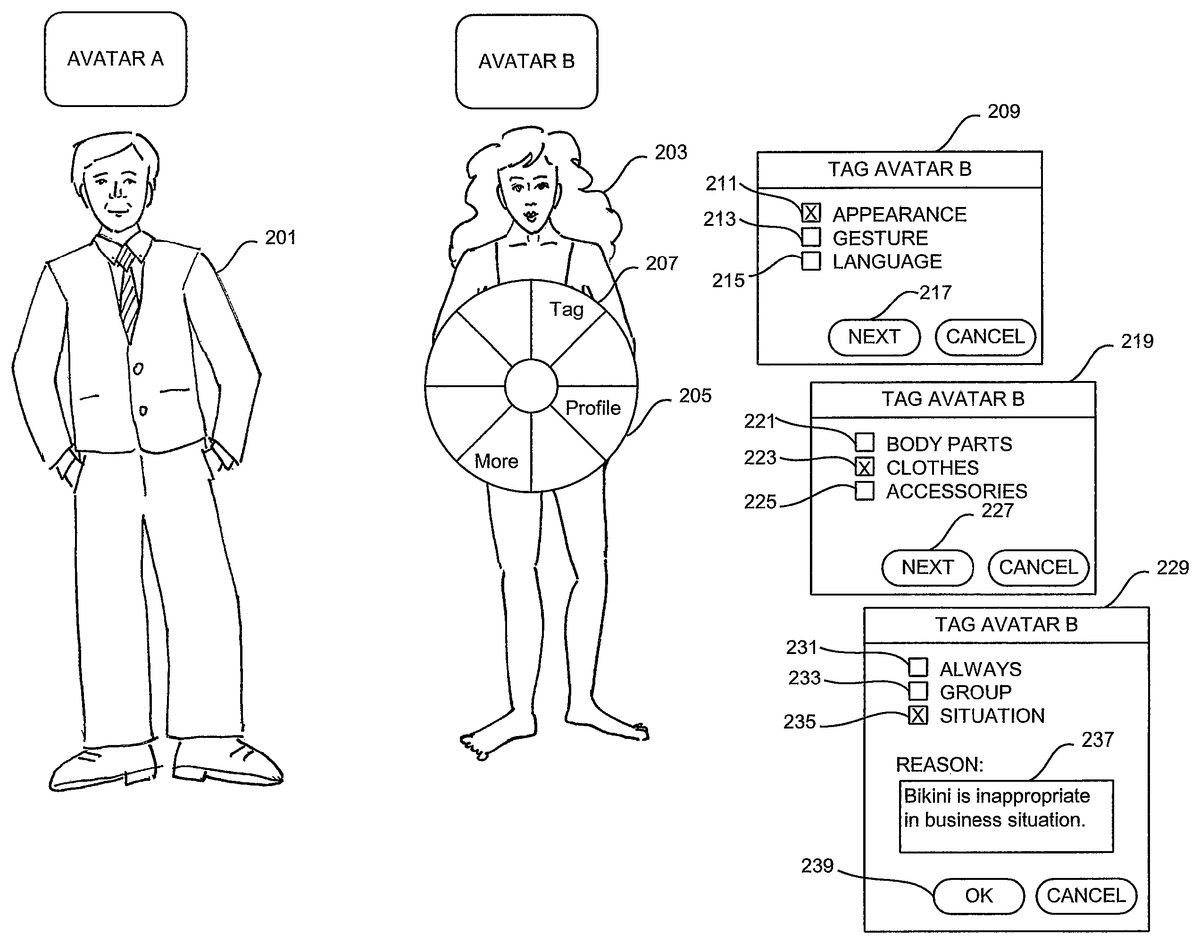
FIG. 2illustrates a view into a virtual world from a user computer. The user of the computer is represented in the virtual world by an avatar201. The user's avatar201is identified in the virtual world by the name AVATAR A. A second avatar203is identified in the virtual world by the name AVATAR B. Avatar203is associated with another human user. As is known to those skilled in the art, users can move about, communicate, transact business, and essentially live in the virtual world through their associated avatars.
In the example ofFIG. 2, the user associated with avatar201finds the clothing worn by avatar203to be inappropriate in some way. The clothing may be obscene, indecent, or scandalous, per se, inappropriate for a particular situation, inappropriate for view by persons in particular groups, such as children, or persons having particular social or cultural norms, or otherwise objectionable to the user associated with avatar201. It should be recognized that clothing is only an example of one type of attribute associated with an avatar that the user may deem to be inappropriate. Those skilled in the art will recognize that other objectionable attributes, such as bodily or facial appearance, accessories, gestures, language, or the like, may be controlled according to the present invention.
According to the present invention, the user associated with avatar201can tag the objectionable clothing worn by avatar203. As will described in detail hereinafter, tagging an attribute places limitations on the avatar while the attribute is associated with the avatar. In one embodiment of the present invention, the user associated with avatar201can place his or her mouse pointer on avatar203. Right clicking his or her mouse causes a control205to be displayed. According to the present invention, control205includes a tag button207. Left clicking on tag button207causes a tagging menu209to be displayed. Tagging menu209includes an appearance checkbox211, a gesture checkbox213, and the language checkbox215. The user associated with avatar201can identify the category of objectionable content by checking one of check boxes211-215and actuating a next button217.
Actuation of next button217causes an appearance tagging menu219to be displayed. Appearance tagging menu219includes a body parts checkbox221, a clothing checkbox223, and an accessories checkbox225. The user associated with avatar201can identify the objectionable appearance attribute by checking one of checkboxes221-225and actuating a next button227. Actuation of next button227causes a clothing tagging dialog229to be displayed. Clothing tagging dialog229enables the user associated with avatar201to specify how or when the limitations imposed by the tag will be applied.
Clothing tagging dialog229includes an always checkbox231, a group checkbox233, and the situation checkbox235. If the user checks always checkbox223, the limitations of the tag will always be applied when avatar201encounters avatar203wearing the tagged clothing. If the user checks group checkbox223, the limitations of the tag will be applied whenever an avatar associated with a member of the group encounters avatar203wearing the tagged clothing. If the user checks situation checkbox235, the limitations of tag will be applied whenever avatar be approaches a specified situation. Examples of situations include business situations, worship situations, and other situations in which the tagged clothing would be offensive or distracting. Clothing tagging dialog229includes a reason text entry field237into which the user can enter information about why the tagged clothing is objectionable. When the user actuates OK button239, a tag is added to the tag article of clothing. The user associated with avatar203may be notified that the article of clothing has been tag and the reason for the tagging. The creator of the article of clothing may also be notified. The creator of the clothing may add the tag to future versions of the article of clothing or change the appearance of future versions. The seller, if any, of the clothing may also be notified of the tagging so that the seller may add the tag to clothing in inventory. It should be recognized that the sequence of menus illustrated in, and describe with reference to,FIG. 2are only examples in which the offending attribute is an article of clothing. Those skilled in the art will recognize that other sequences of menus would be displayed in connection with tagging other types of attributes.
FIG. 3illustrates a view into the virtual world. When avatar203, wearing the tagged clothing, approaches avatar201, who may be the tagging avatar or an avatar representing a member of class of users or an avatar in a particular situation, the system may display a warning dialog301to the user associated with avatar201. In certain situations, the system may not display a warning dialog. For example, where the tagged attribute is always offensive to the user, the system may execute the limitation of the tag, such as blocking avatar203from approaching avatar201automatically, without informing the user.
Warning dialog301includes a block the avatar checkbox303and a change the avatar's clothing checkbox305. If the user associated with avatar201checks checkbox303and actuates OK button307, avatar203is blocked from entering the field of view of the user associated with avatar201. If the user checks checkbox305and actuates OK button307, the clothing worn by avatar203will be changed to something not offending. For example, when a user first joins a virtual world, the user is typically dressed in plain clothing. According to the present invention, the clothing worn by avatar203can be changed to the generic plain clothing provided by the virtual world. The user associated with avatar201can ignore warning dialog301by actuating cancel button309. Parental controls or the like may not give the user who is a member of a group, such as children, a choice about how to handle avatar203. In such cases, avatar203would be automatically blocked. When avatar203is blocked, the system displays to the user associated with avatar203a message311advising the user of the block and the reason for the block.
FIG. 4is a flow chart of an embodiment of tagging process according to the present invention. The system waits for user input. If as determined at decision block401, the user input is a right-click on avatar, the system displays control205ofFIG. 2, as indicated at block403. If the user input is not a right-click on avatar, the system performs other user input processing, as indicated generally at block405. If, as determined at decision block407, the user actuates tag button207ofFIG. 2, the system displays tagging menu209ofFIG. 2, as indicated at block409. If the user does not actuate tag button, the system performs other control processing, as indicated at block411. If, as determined at decision block413, the user selects appearance checkbox211of tagging menu409ofFIG. 2, the system displays appearance tagging menu219ofFIG. 2, as indicated at block415. If not, the system performs other tagging processing, as indicated generally at block417. If, as determined at decision block419, the user checks clothing checkbox223of appearance tagging menu219ofFIG. 2, the system displays clothing tagging dialog229ofFIG. 2, as indicated at block421. If not, the system performs other appearance tagging processing, as indicated generally at block423. The system determines the type of, and reason for, the tagging, from clothing tagging dialog229, as indicated at block423. Then, the system notifies the user associated with the tagged article of clothing of the tagging and the reason for the tagging, as indicated at block425. The system may update the tagging user's profile, at block427. The system adds the tag to the clothing attributes, at block429. The system may notify the person who created the clothing of the tagging and the reason for the tagging, as indicated at block431. The system may also notify the seller of the clothing of the tagging and the reason for the tagging, as indicated at block433.
FIG. 5is a flow chart of an embodiment of tagged attribute processing according to the present invention. When an avatar with a tagged attribute approaches another avatar, as determined at decision block501, the system determines, at decision block503, if the tagged attribute is always offensive to the user associated with the approached avatar. If so, in the embodimentFIG. 5, the system presents limitation control choices to the user, as indicated at block505. If, as determined at decision block507, the user chooses to block the avatar, the system blocks and notifies the approaching avatar, at block509. If, as determined at decision block511, the user elects to change the appearance of the approaching avatar, the system changes the appearance of and notifies the approaching avatar, as indicated at block513. In alternative embodiments, the system may be configured to block and notify the approaching avatar automatically without presenting limitation control choices to the user. If, as determined at decision block515, the tagged attribute is situational, the system determines, at decision block517, if the approached avatar is in the situation. If so, processing proceeds to block505. Alternatively, the system may automatically block and notify the approaching avatar. If, as determined at decision block515the tagging is not situational, or as determined at decision block517, the approach to avatar is not in the situation, the system determines, at decision block521, if the attribute is tagged as being inappropriate for members of a particular group. If so, the system determines at, decision block523, if the approached avatar is a member of that group. If so, processing proceeds to block505. Alternatively, the user's system may be configured to block and notify the approaching avatar automatically without present limitation control choices to the user. For example, in the case child users parental controls may be set so that the child is not given a choice about whether to see avatars with tagged attributes.
Referring now toFIG. 6, there is illustrated a block diagram of a generic information handling system600capable of performing the operations described herein. Computer system600includes processor601which is coupled to host bus603. Processor601preferably includes an onboard cache memory. A level two (L2) cache memory605is also coupled to host bus603. A Host-to-PCI bridge607is coupled to host bus603. Host-to-PCI bridge607, which is coupled to main memory609, includes its own cache memory and main memory control functions. Host-to-PCI bridge607provides bus control to handle transfers among a PCI bus611, processor601, L2 cache605, main memory609, and host bus603. PCI bus611provides an interface for a variety of devices including, for example, a local area network (LAN) card613, a PCI-to-ISA bridge615, which provides bus control to handle transfers between PCI bus611and an ISA bus617, a universal serial bus (USB)619, and an IDE device621. PCI-to-ISA bridge615also includes onboard power management functionality. PCI-to-ISA bridge615can include other functional elements not shown, such as a real-time clock (RTC), DMA control, interrupt support, and system management bus support.
Peripheral devices and input/output (I/O) devices can be attached to various interfaces or ports coupled to ISA bus617. Such interfaces or ports may include a parallel port623, a serial port625, an infrared (IR) interface627, a keyboard interface629, a mouse interface631, and a hard disk drive (HDD)633.
A BIOS635is coupled to ISA bus617. BIOS635incorporates the necessary processor executable code for a variety of low-level system functions and system boot functions. BIOS635can be stored in any computer readable medium, including magnetic storage media, optical storage media, flash memory, random access memory, read only memory, and communications media conveying signals encoding the instructions (e.g., signals from a network). In order to couple computer system600to another computer system to copy files or send and receive messages over a network, LAN card613may be coupled to PCI bus611. Similarly, a Fibre Channel card may be coupled to PCI bus613. Additionally, a modem639may be coupled to ISA bus617through serial port625to support dial-up connections.
While the computer system described inFIG. 6is capable of executing the invention described herein, the illustrated system is simply one example of a computer system. Those skilled in the art will appreciate that many other computer system designs are capable of performing the invention described herein.
One of the preferred implementations of the invention is an application, namely, a set of instructions (program code) in a code module that may, for example, be in the random access memory of the computer. Until required by the computer, the set of instructions may be stored in another computer memory, for example, on a hard disk drive, or in removable storage such as an optical disk (for eventual use in a CD ROM) or floppy disk (for eventual use in a floppy disk drive), or downloaded via the Internet or other computer network. Thus, the present invention may be implemented as a computer program product for use in a computer. In addition, although the various methods described are conveniently implemented in a general purpose computer selectively activated or reconfigured by software, one of ordinary skill in the art would also recognize that such methods may be carried out in hardware, in firmware, or in more specialized apparatus constructed to perform the required method steps.
From the foregoing, it will be apparent to those skilled in the art that systems and methods according to the present invention are well adapted to overcome the shortcomings of the prior art. While the present invention has been described with reference to presently preferred embodiments, those skilled in the art, given the benefit of the foregoing description, will recognize alternative embodiments. Although invention has been illustrated and described in detail with respect to mashups, those skilled in the art will appreciate that embodiments of the present invention are applicable to other web-based applications. Accordingly, the foregoing description is intended for purposes of illustration and not of limitation.
Claims
- A method comprising: receiving an input through a computer input device from a first user that is controlling a first avatar in a virtual world, the input configured to tag an attribute of a second avatar in the virtual world, wherein the attribute is defined to be at least one of an attribute that the first user does not want to view in the virtual world and an attribute that the first user is not allowed to view in the virtual world based on a parental control, wherein the attribute comprises at least one of clothing, body gesture and language of the second avatar;associating the tag with the attribute of the second avatar in the virtual world;placing a limitation on the second avatar in the virtual world in response to associating the tag with the attribute of the second avatar, wherein the placing of the limitation comprises, responsive to the second avatar attempting to enter a field of view of the first avatar, blocking the second avatar from entering the field of view of the first avatar in the virtual world;and notifying a second user that is controlling the second avatar regarding the associating of the tag with the attribute.
- The method as claimed in claim 1 , wherein placing the limitation on the second avatar in the virtual world comprises: responsive to second avatar attempting to enter a field of view of at least one avatar representing a member of a class of users, blocking the second avatar from entering the field of view of the at least one avatar.
- The method as claimed in claim 1 , wherein placing the limitation on the second avatar in the virtual world comprises: responsive to second avatar attempting to enter a field of view of the first avatar in a specified situation, blocking the second avatar from entering the field of view of the first avatar.
- The method as claimed in claim 1 , wherein the attribute comprises clothing, wherein placing the limitation on the second avatar in the virtual world comprises: responsive to the second avatar attempting to enter a field of view of the first avatar, changing the clothing of the second avatar prior to the second avatar entering the field of view of the first avatar.
- The method as claimed in claim 1 , wherein the attribute comprises clothing, wherein the method comprises: notifying at least one of a creator and a seller of the clothing regarding the associating of the tag with the attribute.
- The method as claimed in claim 1 , wherein placing the limitation on the second avatar in the virtual world comprises: notifying the first user that is controlling the first avatar of an approach by the second avatar in the virtual world;and, enabling the first user to control the second avatar.
- The method as claimed in claim 6 , wherein said control comprises: blocking the second avatar from entering a field of view of the first avatar in the virtual world.
- The method as claimed in claim 6 , wherein said control comprises: changing said attribute prior to entry of the second avatar into a field of view of the first avatar in the virtual world.
- A computer program product for providing content and services, the computer program product comprising: a computer readable storage medium having computer usable program code embodied therewith the computer usable program code comprising a computer usable program code configured to: receive an input through a computer input device from a first user that is controlling a first avatar in a virtual world, the input configured to tag an attribute of a second avatar in the virtual world, wherein the attribute is defined to be at least one of an attribute that the first user does not want to view in the virtual world and an attribute that the first user is not allowed to view in the virtual world based on a parental control, wherein the attribute comprises at least one of clothing, body gesture and language of the second avatar;associate the tag with the attribute of the second avatar in the virtual world;place a limitation on the second avatar in the virtual world in response to associating the tag with the attribute of the second avatar, wherein the computer usable program code configured to place of the limitation comprises, responsive to the second avatar attempting to enter a field of view of the first avatar, computer program code configured to block the second avatar from entering the field of view of the first avatar in the virtual world;and notify a second user that is controlling the second avatar regarding the associating of the tag with the attribute.
- The computer program product as claimed in claim 9 , wherein the computer usable program code configured to place of the limitation on the second avatar in the virtual world comprises: computer usable program code configured to, responsive to second avatar attempting to enter a field of view of at least one avatar representing a member of a class of users, block the second avatar from entering the field of view of the at least one avatar.
- The computer program product as claimed in claim 9 , wherein the computer usable program code configured to place the limitation on the second avatar in the virtual world comprises: computer usable program code configured to, responsive to second avatar attempting to enter a field of view of the first avatar in a specified situation, block the second avatar from entering the field of view of the first avatar.
Disclaimer: Data collected from the USPTO and may be malformed, incomplete, and/or otherwise inaccurate.