U.S. Pat. No. 7,798,905
METHOD AND APPARATUS FOR ASSOCIATING DATA WITH ONLINE GAME RATINGS
AssigneeMicrosoft Corporation
Issue DateMay 9, 2003
Illustrative Figure
Abstract
A procedure receives a game result from a game console. A rating is determined for the game result. If the rating for the game result meets a predetermined criteria, the recorded game associated with the game result is received from the game console. The recorded game is attached to the rating of the game result such that other players can access the recorded game through an online gaming service.
Description
DETAILED DESCRIPTION The following discussion is directed to a system and method for associating data with a user's online game rating. The discussion assumes that the reader is familiar with basic cryptography principles, such as encryption, decryption, authentication, hashing, and digital signatures. For a basic introduction to cryptography, the reader is directed to a text written by Bruce Schneier and entitled, “Applied Cryptography: Protocols, Algorithms, and Source Code in C,” published by John Wiley & Sons, copyright 1994 (second edition 1996), which is hereby incorporated by reference. Discussions herein refer to a “rating”, a “leaderboard” and an “attachment”. A rating is a score assigned to a player or a team as a result of some aspect of gameplay. A leaderboard is a ranked collection of ratings that resulted from some aspect of gameplay stored in a statistics service. An attachment is any data associated with a rating on a statistics leaderboard. For example, an attachment may be a recorded game (also referred to as a “saved game”), a saved action or movement in a game, an audio file containing the voice of a player explaining how a high score was achieved, etc. An attachment may also be an aggregated collection of several items such as a recorded game and an audio file containing player commentary, etc. An attachment may also be referred to as “attached data” or “associated data”. FIG. 1is a block diagram of an exemplary online gaming environment100. Multiple game consoles102(1),102(2), . . . ,102(n) are coupled to a security gateway104via a network106. Network106represents any one or more of a variety of conventional data communications networks. Network106will typically include packet switched networks, but may also include circuit switched networks. Network106can include wired and/or wireless portions. In one exemplary implementation, network106includes the Internet and may optionally include one or ...
DETAILED DESCRIPTION
The following discussion is directed to a system and method for associating data with a user's online game rating. The discussion assumes that the reader is familiar with basic cryptography principles, such as encryption, decryption, authentication, hashing, and digital signatures. For a basic introduction to cryptography, the reader is directed to a text written by Bruce Schneier and entitled, “Applied Cryptography: Protocols, Algorithms, and Source Code in C,” published by John Wiley & Sons, copyright 1994 (second edition 1996), which is hereby incorporated by reference.
Discussions herein refer to a “rating”, a “leaderboard” and an “attachment”. A rating is a score assigned to a player or a team as a result of some aspect of gameplay. A leaderboard is a ranked collection of ratings that resulted from some aspect of gameplay stored in a statistics service. An attachment is any data associated with a rating on a statistics leaderboard. For example, an attachment may be a recorded game (also referred to as a “saved game”), a saved action or movement in a game, an audio file containing the voice of a player explaining how a high score was achieved, etc. An attachment may also be an aggregated collection of several items such as a recorded game and an audio file containing player commentary, etc. An attachment may also be referred to as “attached data” or “associated data”.
FIG. 1is a block diagram of an exemplary online gaming environment100. Multiple game consoles102(1),102(2), . . . ,102(n) are coupled to a security gateway104via a network106. Network106represents any one or more of a variety of conventional data communications networks. Network106will typically include packet switched networks, but may also include circuit switched networks. Network106can include wired and/or wireless portions. In one exemplary implementation, network106includes the Internet and may optionally include one or more local area networks (LANs) and/or wide area networks (WANs). At least a part of network106is a public network, which refers to a network that is publicly-accessible. Virtually anyone can access the public network.
In some situations, network106includes a LAN (e.g., a home network), with a routing device situated between game console102and security gateway104. This routing device may perform network address translation (NAT), allowing the multiple devices on private network108(or a LAN) to share the same IP address on the Internet, and also operating as a firewall to protect the device(s) from access by malicious or mischievous users via the Internet.
Security gateway104operates as a gateway between public network106and private network108. Private network108can be any of a wide variety of conventional networks, such as a local area network. Private network108, as well as other devices discussed in more detail below, is within a data center110that operates as a secure zone. Data center110is made up of trusted devices communicating via trusted communications. Thus, encryption and authentication within secure zone110is not necessary. The private nature of network108refers to the restricted accessibility of network108—access to network108is restricted to only certain individuals (e.g., restricted by the owner or operator of data center110).
Security gateway104is a cluster of one or more security gateway computing devices. These security gateway computing devices collectively implement security gateway104. Security gateway104may optionally include one or more conventional load balancing devices that operate to direct requests to be handled by the security gateway computing devices to appropriate ones of those computing devices. This directing or load balancing is performed in a manner that attempts to balance the load on the various security gateway computing devices approximately equally (or alternatively in accordance with some other criteria).
Also within data center110are: one or more monitoring servers112; one or more presence and notification front doors114, one or more presence servers116, and one or more notification servers118(collectively implementing a presence and notification service); one or more match front doors120and one or more match servers122(collectively implementing a match service); and one or more statistics front doors124and one or more statistics servers126(collectively implementing a statistics service). The servers116,118,122, and126provide services to game consoles102, and thus can be referred to as service devices. Other service devices may also be included in addition to, and/or in place of, one or more of the servers116,118,122, and126. Additionally, although only one data center is shown inFIG. 1, alternatively multiple data centers may exist with which game consoles102can communicate. These data centers may operate independently or alternatively may operate collectively (e.g., to make one large data center available to game consoles102).
Game consoles102are situated remotely from data center110, and access data center110via network106. A game console102desiring to communicate with one or more devices in data center110establishes a secure communication channel between the console102and security gateway104. Game console102and security gateway104encrypt and authenticate data packets being passed back and forth, thereby allowing the data packets to be securely transmitted between them without being understood by any other device that may capture or copy the data packets without breaking the encryption. Each data packet communicated from game console102to security gateway104, or from security gateway104to game console102can have data embedded therein. This embedded data is referred to as the content or data content of the packet. Additional information may also be inherently included in the packet based on the packet type (e.g., a heartbeat packet or traversal packet, discussed in more detail below).
The secure communication channel between a console102and security gateway104is based on a security ticket. Console102authenticates itself and the current user(s) of console102to a key distribution center128and obtains, from key distribution center128, a security ticket. Console102then uses this security ticket to establish the secure communication channel with security gateway104. In establishing the secure communication channel with security gateway104, the game console102and security gateway104authenticate themselves to one another and establish a session security key that is known only to that particular game console102and the security gateway104. This session security key is used as a basis to encrypt data transferred between the game console102and the security gateway cluster104, so no other devices (including other game consoles102) can read the data. The session security key is also used as a basis to authenticate a data packet as being from the security gateway104or game console102that the data packet alleges to be from. Thus, using such session security keys as a basis, secure communication channels can be established between the security gateway104and the various game consoles102.
Once the secure communication channel is established between a game console102and the security gateway104, encrypted data packets can be securely transmitted between the two. When the game console102desires to send data to a particular service device in data center110, the game console102encrypts the data and sends it to security gateway104requesting that it be forwarded to the particular service device(s) targeted by the data packet. Security gateway104receives the data packet and, after authenticating and decrypting the data packet, encapsulates the data content of the packet into another message to be sent to the appropriate service via private network108. Security gateway104determines the appropriate service for the message based on the requested service(s) targeted by the data packet.
Similarly, when a service device in data center110desires to communicate data to a game console102, the data center sends a message to security gateway104, via private network108, including the data content to be sent to the game console102as well as an indication of the particular game console102to which the data content is to be sent. Security gateway104embeds the data content into a data packet, and then encrypts the data packet so it can only be decrypted by the particular game console102and also authenticates the data packet as being from the security gateway104.
Although discussed herein as primarily communicating encrypted data packets between security gateway104and a game console102, alternatively some data packets may be partially encrypted (some portions of the data packets are encrypted while other portions are not encrypted). Which portions of the data packets are encrypted and which are not can vary based on the desires of the designers of data center110and/or game consoles102. For example, the designers may choose to allow voice data to be communicated among consoles102so that users of the consoles102can talk to one another—the designers may further choose to allow the voice data to be unencrypted while any other data in the packets is encrypted. Additionally, in another alternative, some data packets may have no portions that are encrypted (that is, the entire data packet is unencrypted). It should be noted that, even if a data packet is unencrypted or only partially encrypted, the data packet is still authenticated.
Each security gateway device in security gateway104is responsible for the secure communication channel with typically one or more game consoles102, and thus each security gateway device can be viewed as being responsible for managing or handling one or more game consoles. The various security gateway devices may be in communication with each other and communicate messages to one another. For example, a security gateway device that needs to send a data packet to a game console that it is not responsible for managing may send a message to all the other security gateway devices with the data to be sent to that game console. This message is received by the security gateway device that is responsible for managing that game console and sends the appropriate data to that game console. Alternatively, the security gateway devices may be aware of which game consoles are being handled by which security gateway devices—this may be explicit, such as each security gateway device maintaining a table of game consoles handled by the other security gateway devices, or alternatively implicit, such as determining which security gateway device is responsible for a particular game console based on an identifier of the game console.
Monitoring server(s)112operate to inform devices in data center110of an unavailable game console102or an unavailable security gateway device of security gateway104. Game consoles102can become unavailable for a variety of different reasons, such as a hardware or software failure, the console being powered-down without logging out of data center110, the network connection cable to console102being disconnected from console102, other network problems (e.g., the LAN that the console102is on malfunctioning), etc. Similarly, a security gateway device of security gateway104can become unavailable for a variety of different reasons, such as hardware or software failure, the device being powered-down, the network connection cable to the device being disconnected from the device, other network problems, etc.
Each of the security gateway devices in security gateway104is monitored by one or more monitoring servers112, which detect when one of the security gateway devices becomes unavailable. In the event a security gateway device becomes unavailable, monitoring server112sends a message to each of the other devices in data center110(servers, front doors, etc.) that the security gateway device is no longer available. Each of the other devices can operate based on this information as it sees fit (e.g., it may assume that particular game consoles being managed by the security gateway device are no longer in communication with data center110and perform various clean-up operations accordingly). Alternatively, only certain devices may receive such a message from the monitoring server112(e.g., only those devices that are concerned with whether security gateway devices are available).
Security gateway104monitors the individual game consoles102and detects when one of the game consoles102becomes unavailable. When security gateway104detects that a game console is no longer available, security gateway104sends a message to monitoring server112identifying the unavailable game console. In response, monitoring server112sends a message to each of the other devices in data center110(or alternatively only selected devices) that the game console is no longer available. Each of the other devices can then operate based on this information as it sees fit.
Presence server(s)116holds and processes data concerning the status or presence of a given user logged in to data center110for online gaming. Notification server(s)118maintains multiple queues of outgoing messages destined for a player logged in to data center110. Presence and notification front door114is one or more server devices that operate as an intermediary between security gateway104and servers116and118. One or more load balancing devices (not shown) may be included in presence and notification front door114to balance the load among the multiple server devices operating as front door114. Security gateway104communicates messages for servers116and118to the front door114, and the front door114identifies which particular server116or particular server118the message is to be communicated to. By using front door114, the actual implementation of servers116and118, such as which servers are responsible for managing data regarding which users, is abstracted from security gateway104. Security gateway104can simply forward messages that target the presence and notification service to presence and notification front door114and rely on front door114to route the messages to the appropriate one of server(s)116and server(s)118.
Match server(s)122hold and process data concerning the matching of online players to one another. An online user is able to advertise a game available for play along with various characteristics of the game (e.g., the location where a football game will be played, whether a game is to be played during the day or at night, the user's skill level, etc.). These various characteristics can then be used as a basis to match up different online users to play games together. Match front door120includes one or more server devices (and optionally a load balancing device(s)) and operates to abstract match server(s)122from security gateway104in a manner analogous to front door114abstracting server(s)116and server(s)118.
Statistics server(s)126hold and process data concerning various statistics for online games. The specific statistics used can vary based on the game designer's desires (e.g., the top ten scores or times, a world ranking for all online players of the game, a list of users who have found the most items or spent the most time playing, etc.). Statistics front door126includes one or more server devices (and optionally a load balancing device(s)) and operates to abstract statistics server(s)126from security gateway104in a manner analogous to front door114abstracting server(s)116and server(s)118.
Thus, it can be seen that security gateway104operates to shield devices in the secure zone of data center110from the untrusted, public network106. Communications within the secure zone of data center110need not be encrypted, as all devices within data center110are trusted. However, any, information to be communicated from a device within data center110to a game console102passes through security gateway cluster104, where it is encrypted in such a manner that it can be decrypted by only the game console102targeted by the information.
FIG. 2is a block diagram illustrating specific components of a system for associating data with online game ratings. Certain components (such as components ofFIG. 1) are omitted fromFIG. 2for purposes of explanation. In a particular embodiment, the components shown inFIG. 2are used in combination with the components ofFIG. 1to provide a full-featured online gaming environment. The components ofFIG. 2that are common toFIG. 1share common reference numbers.
The system ofFIG. 2shows two game consoles102(1) and102(2), security gateway104and statistics front door124, as discussed above with respect toFIG. 1. Statistics front door124is coupled to a storage server202, a statistics database206, and a signature server210. Storage server202controls the storage and retrieval of data, such as attachments associated with game ratings, in one or more storage databases204. Storage server202communicates with signature server210and with game consoles102via security gateway104.
Statistics front door124controls various functions related to maintaining statistics related to game play, such as leaderboards associated with various game programs. Statistics database206coupled to statistics front door124stores various statistics and other information used by statistics front door124and other components. For example, statistics database206maintains data associated with multiple leaderboards, such as player ratings, references to data (e.g., saved games or highlights) associated with a player's rating, and the like.
Name resolver208is used when data is stored across multiple storage devices. A data request from game console102is not typically aware of the storage facilities used by the online gaming system. Thus, name resolver208maps a generic identifier used by game console102to the actual storage location of the data. Additional details regarding name resolver208are provided below. Signature server210contains a set of keys used to secure communications between game consoles102and other components of the system. In one embodiment, statistics server124is unaware of name resolution issues handled by name resolver208. Statistics server124builds references that include all of the metadata that name resolver208would use to locate the proper storage server, but the statistics server doesn't know how data is partitioned among different locations or different storage devices. When an game console102actually uploads or downloads attachments generated by statistics server124, name resolver208will be contacted.
The data associated with online game ratings is not necessarily stored in the statistics service itself. Instead, the statistics service may keep a reference to the data which is stored in a separate storage service. The storage service may store data associated with online game ratings as well as other data.
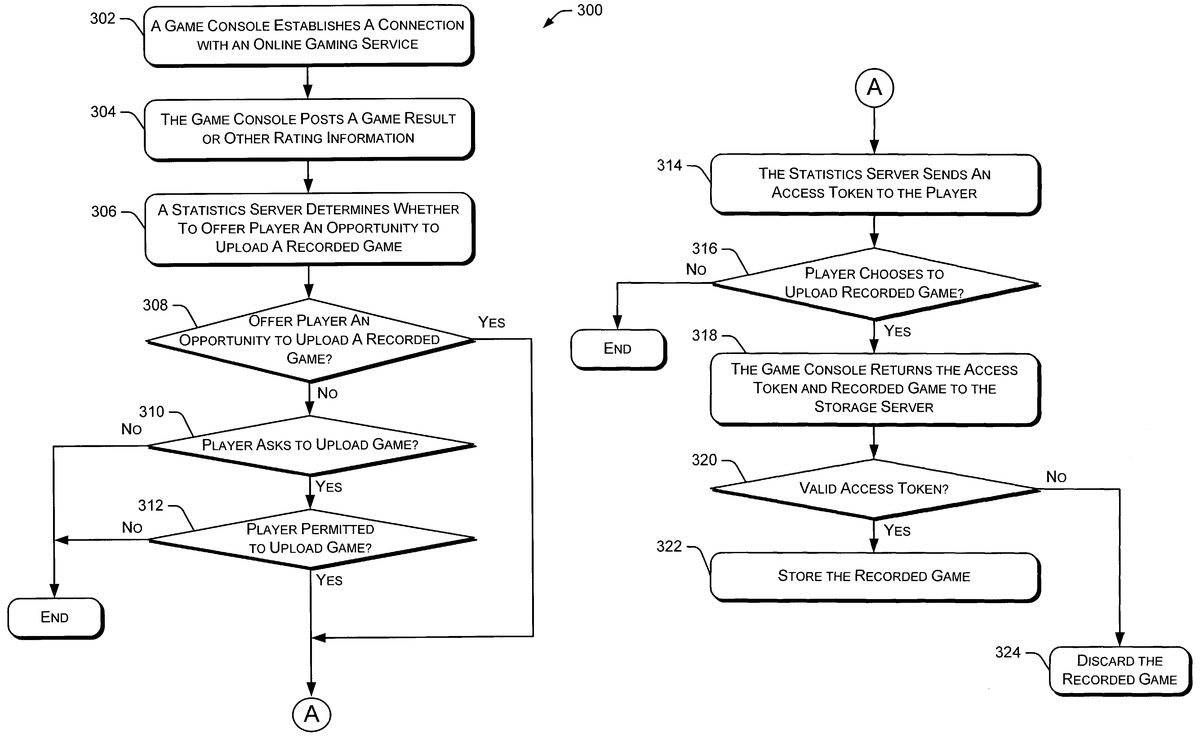
FIGS. 3A and 3Brepresent a flow diagram illustrating an embodiment of a procedure300for associating data with online game ratings. Initially, a game console establishes a connection with an online gaming service (block302). The game console then posts a game result (such as a game score) or other information used to rate the player's performance to the statistics front door (block304) or the statistics server. A statistics server determines whether to offer the player an opportunity to upload a recorded game (i.e., the recorded game associated with the posted game score) to be associated with the player's rating (block306). A recorded game may also be referred to as a “ghost race”, a “highlight”, a “highlight race”, or a “saved game”. The statistics server may limit the number of recorded games that can be associated with a particular game to control the amount of storage space required for such recorded games. For example, the statistics server may allow recorded games to be associated with the top ten or top twenty ratings for a particular game (or the top 5% of all ratings). The number of recorded games that can be stored with a particular game may vary depending on the number of players submitting scores and/or the size of the typical recorded game data.
If the statistics server decides to offer the player an opportunity to upload the recorded game (block308), the procedure branches to block314where the statistics server sends an access token to the player to be used in submitting the recorded game. If the statistics server decides not to offer the player an opportunity to upload the recorded game, the player may enter a request to upload the recorded game (block310). A statistics server may allow a certain number of recorded games to be uploaded by players that do not otherwise qualify to upload the recorded game. If the player enters such a request, the procedure determines whether the player is permitted (e.g., by the statistics server) to upload the recorded game (block312). If so, the procedure continues to block314where the statistics server sends an access token to the player to be used in submitting the recorded game. Otherwise, the procedure terminates.
From block314, the game console determines whether the player has chosen to upload the recorded game (block316). If not, the procedure terminates. If the player chooses to upload the recorded game at block316, the game console returns the access token and the recorded game to the storage server (block318). The storage server receives the access token and the recorded game and validates the access token (block320). This validation is used to ensure that the recorded game sent by the game console is the proper recorded game (i.e., the recorded game that “earned” the access token). If the access token is valid, the recorded game is stored to a storage device (block322). If the access token is not valid, the recorded game is discarded by the storage server (block324).
To protect the integrity of the recorded game data being uploaded, any game data that has the potential to be an attachment is digitally signed by the game console player using signature server210. This signature is tracked in the storage service along with the attachment data. Any time a game console user downloads an attachment from the storage service, it verifies the signature using the storage service. This approach allows signatures to be revoked in case a malicious attachment is uploaded and discovered at a later time. Since some game console users may have already downloaded the attachment when its malicious nature is discovered, requiring the game console users to validate the signature before the attachment is used allows improper content to be disabled even when game console users have a legitimate copy.
In the example ofFIGS. 3A and 3B, the statistics server provides the player with an opportunity to upload a recorded game. In alternate embodiments, the game console automatically uploads the recorded game to the storage server if the statistics server wants to offer the recorded game to other players (e.g., the recorded game is a top score).
Recorded games and other saved data can be retrieved and downloaded and used by numerous players through an online gaming service from, for example, a game console, personal computer, or other device. Players can watch the recorded games or “ride along” during a replay of the recorded game to learn how the best players obtain their top scores. Additionally, with certain recorded games, players can compete against the recorded game to test or improve their own skills.
Particular examples discussed herein relate to storing saved game data associated with player ratings. However, in alternate embodiments, any type of data may be associated with player ratings, such as portions of a recorded game, a longest run in a football game, a biggest explosion, a clever golf shot, best bloopers (i.e., mistakes), and the like. Additionally, games could record a “highlight” film of particularly interesting items and make them available on leader boards. Sports games could compel players to play frequently by providing a highlight show where players can watch the best plays such as longest interception, longest home run, etc. Similarly, action games can record films for interesting events, such as largest explosions, most crashes in a given time period, etc.
FIG. 4illustrates an example of data contained in an access token402. Access token402provides “permission” to a player (or game console user) to upload data to, for example, the storage server. Access token402is designed to prevent tampering by a player and provide assurances to the storage server that the statistics server granted permission for the upload. Access token402includes the name of the attached data file that the player is permitted to upload, the name of the player permitted to perform the data upload, an identifier associated with the machine that generated the data being uploaded, and the maximum size of the data that can be uploaded from the game console. Access token402also includes a digital signature obtained from the signature server by the statistics server granting the permission. This digital signature prevents the user from tampering with the data contained in the access token. Other access tokens may include other types of data, such as the operation permitted, the location of the file being uploaded, etc.
FIG. 5illustrates an example of data contained in a leaderboard500associated with a particular game. In this example, leaderboard500is associated with an auto racing game and maintains a list of the best lap times. In other embodiments, other types of games may capture different types of information. Also, a leaderboard may capture multiple types of information, such as fastest lap, fastest three-lap race, fewest collisions, etc. The leaderboard information is typically available to all players associated with an online gaming service.
A first column502in leaderboard500identifies a particular ranking (e.g., 1-10). A second column504identifies a player name associated with the ranking. The player name may be a real name (e.g., Bob Smith) or a nickname (e.g., Master Gamer). A third column506identifies the player's best lap time that is at least partially responsible for the player's ranking. A fourth column508contains a reference identifier that identifies data (such as a recorded game or a best shot) associated with the player's ranking. For example, the reference identifier (abbreviated Ref. ID) may identify a recorded game in which the lap time identified in column506was produced. Other players can select a recorded game or other associated data using the reference identifier. In certain situations, there may be no reference identifier, meaning that there is no additional data associated with the particular ranking. In an alternate embodiment, the reference identifier is a uniform resource locator (URL).
A fifth column510identifies whether the data identified in the fourth column508is available for downloading and/or viewing. If the data identified by the reference identifier is available on, for example, the storage server, the fifth column510will indicate the availability of the data as “Yes” or “Y”. However, if the data has been deleted, was never uploaded to the storage server, or is in the process of being uploaded to the storage server, the fifth column510will indicate the availability of the data as “No” or “N”. Thus, a player can view the leaderboard and identify which attachments are available to download.
A sixth column512identifies a timestamp indicating the last time the player identified in column504played the game associated with leaderboard500. The timestamp information is updated each time the, player reports a game result to the statistics server. This timestamp information is used to determine the age of statistical data. Further, the statistics server may “age out” old entries. In one embodiment, entries that were created by a player who has not played the game for 30 or 60 days may be removed from the leaderboard to provide spaces for players actively playing the game. In another embodiment, the following formula ages entries in leaderboard500based on the timestamp.
An example decay formula is provided below (m represents the number of months since the player's last game session.
RATINGnew={RATINGold*(1-m12),0≤m=12}
This formula will degrade the player's rating linearly over time until the player has been inactive for 12 months. After 12 months of inactivity by the player, the rating is set to zero and subsequently removed from the leaderboard. Alternate embodiments may use other types of decay formulas that reduce ratings over time.
Although leaderboard500illustrates the top ten players for a particular game, other leaderboards may illustrate any number of players, such as the top five, the top twenty, or the top 100.
Each row (i.e., rating) in leaderboard500may have multiple associated data attachments. For example, a particular rating in leaderboard500may have an associated recorded game and an associated audio file of a player's voice describing how they achieved their high score.
In an alternate embodiment, a subset of the players associated with an online gaming service, such as a group of friends or a club, may exchange attachments. Thus, a group of friends may post recorded games to a particular storage area (e.g., a friends leaderboard) for other friends to download and view or compete against. This allows two or more friends to play against each other even if they are not available to play at the same time.
FIG. 6is a flow diagram illustrating an embodiment of a procedure600in which a game console retrieves data associated with a player's rating. Initially, a game console establishes a connection with an online gaming service (block602). The game console user (or player) requests display of a leaderboard associated with a particular game (block604). In alternate embodiments, the game console user (or player) requests display of ratings of various friends that also use the online gaming system. This display of friends' ratings may contain information similar to that discussed above with respect to leaderboard500inFIG. 5.
At block606, the online gaming service provides the leaderboard data to the game console. The game console then displays the received leaderboard data to the game console user (block608). The game console user selects data attached to (or associated with) an entry in the leaderboard (block610). The selected data may be a recorded game, favorite shot, etc. The online gaming service downloads the selected data to the game console (block612). The game console then displays or otherwise utilizes the downloaded data (block614). As mentioned above, the game console user may view recorded game data or game highlights to learn from the techniques of other players.
As mentioned above, name resolver208(FIG. 2) maps a generic identifier used by a game console to an actual storage location of the desired data. Data stored by the online gaming system may be stored on a variety of different storage systems in different geographic areas. Attachment data can be partitioned into subsets based on game programs, players' geographic area, etc. These different storage devices and storage locations need to be available to a game console user without requiring that the user understand the layout of the data storage architecture. Various other data-related functions, such as the addition of new data, migration of data between storage devices and/or storage locations, and reallocation of storage facilities should be transparent to the game console user as well as the game program itself. Since the game program can be redirected (e.g., by name resolver208), the various functions mentioned above can occur without any modification of the game code.
By storing data across multiple data storage locations, data download time may be improved by downloading data from a storage location close to the game console user. Data can also be moved from one location to another without disruption to the game console user or requiring updates to the references identifying data stored in, for example, the statistics database. When the statistics service generates the reference for a new data attachment, it embeds information in the reference that identifies the particular game title used and the player responsible for the data attachment. This information can be used to partition the attachments across multiple data storage locations.
When the storage service is started, it queries a central configuration database to discover the groups of attachments for which it is responsible. A storage server determines from, for example, a reference identifier, whether the attachment is among the group it is responsible for or if the user needs to be directed to a different storage server.
In one embodiment, one data storage location is designated as the primary data storage location. All user requests for data are first sent to the primary data storage location. If the storage service at the primary data storage location redirects the user based on the reference identifier, the user will cache this information and, will direct subsequent data requests to the proper data storage location. If a group of data needs to be moved from one data storage location to another, after copying the data, the configuration data used by the name resolver is updated and the storage services will then redirect requests to the new data storage location.
Periodically, the online gaming service analyzes the data in the statistics database and identifies all valid attachments. This list of valid attachments is sent to the storage server, which deletes any stored attachments that are not on the list of valid attachments. Additionally, the storage server may identify attachments on the list that are not stored in the storage system, thereby allowing the statistics server to update its data. In an alternate embodiment, the statistics server generates a list of attachments that should be deleted. The storage server then deletes the attachments on the list from the storage system.
The various settings and parameters discussed herein can be modified in, for example, the statistics server and/or the storage server. These parameters and settings include criteria for determining whether to offer a player an opportunity to upload a recorded game, the number of rankings displayed on the leaderboard, and the like. Thus, parameters and settings can be modified after a particular game program has been shipped by the game manufacturer. These parameters and settings may be modified based on the popularity of the game or other factors. For example, if a particular game is very popular, an administrator of the online gaming service may increase the number of ratings that may have attached data.
FIG. 7illustrates a general computer environment700, which can be used to implement the techniques described herein. The computer environment700is only one example of a computing environment and is not intended to suggest any limitation as to the scope of use or functionality of the computer and network architectures. Neither should the computer environment700be interpreted as having any dependency or requirement relating to any one or combination of components illustrated in the exemplary computer environment700.
Computer environment700includes a general-purpose computing device in the form of a computer702. Computer702can be, for example, a statistics front door124or a security gateway104ofFIG. 1, or a storage server202or a name resolver208ofFIG. 2, or a signature server210ofFIG. 2. The components of computer702can include, but are not limited to, one or more processors or processing units704(optionally including a cryptographic processor or co-processor), a system memory706, and a system bus708that couples various system components including the processor704to the system memory706.
The system bus708represents one or more of any of several types of bus structures, including a memory bus or memory controller, a peripheral bus, an accelerated graphics port, and a processor or local bus using any of a variety of bus architectures. By way of example, such architectures can include an Industry Standard Architecture (ISA) bus, a Micro Channel Architecture (MCA) bus, an Enhanced ISA (EISA) bus, a Video Electronics Standards Association (VESA) local bus, and a Peripheral Component Interconnects (PCI) bus also known as a Mezzanine bus.
Computer702typically includes a variety of computer readable media. Such media can be any available media that is accessible by computer702and includes both volatile and non-volatile media, removable and non-removable media.
The system memory706includes computer readable media in the form of volatile memory, such as random access memory (RAM)710, and/or non-volatile memory, such as read only memory (ROM)712. A basic input/output system (BIOS)714, containing the basic routines that help to transfer information between elements within computer702, such as during start-up, is stored in ROM712. RAM710typically contains data and/or program modules that are immediately accessible to and/or presently operated on by the processing unit704.
Computer702may also include other removable/non-removable, volatile/non-volatile computer storage media. By way of example,FIG. 7illustrates a hard disk drive716for reading from and writing to a non-removable, non-volatile magnetic media (not shown), a magnetic disk drive718for reading from and writing to a removable, non-volatile magnetic disk720(e.g., a “floppy disk”), and an optical disk drive722for reading from and/or writing to a removable, non-volatile optical disk724such as a CD-ROM, DVD-ROM, or other optical media. The hard disk drive716, magnetic disk drive718, and optical disk drive722are each connected to the system bus708by one or more data media interfaces726. Alternatively, the hard disk drive716, magnetic disk drive718, and optical disk drive722can be connected to the system bus708by one or more interfaces (not shown).
The disk drives and their associated computer-readable media provide non-volatile storage of computer readable instructions, data structures, program modules, and other data for computer702. Although the example illustrates a hard disk716, a removable magnetic disk720, and a removable optical disk724, it is to be appreciated that other types of computer readable media which can store data that is accessible by a computer, such as magnetic cassettes or other magnetic storage devices, flash memory cards, CD-ROM, digital versatile disks (DVD) or other optical storage, random access memories (RAM), read only memories (ROM), electrically erasable programmable read-only memory (EEPROM), and the like, can also be utilized to implement the exemplary computing system and environment.
Any number of program modules can be stored on the hard disk716, magnetic disk720, optical disk724, ROM712, and/or RAM710, including by way of example, an operating system726, one or more application programs728, other program modules730, and program data732. Each of such operating system726, one or more application programs728, other program modules730, and program data732(or some combination thereof) may implement all or part of the resident components that support the distributed file system.
A user can enter commands and information into computer702via input devices such as a keyboard734and a pointing device736(e.g., a “mouse”). Other input devices738(not shown specifically) may include a microphone, joystick, game pad, satellite dish, serial port, scanner, and/or the like. These and other input devices are connected to the processing unit704via input/output interfaces740that are coupled to the system bus708, but may be connected by other interface and bus structures, such as a parallel port, game port, or a universal serial bus (USB).
A monitor742or other type of display device can also be connected to the system bus708via an interface, such as a video adapter744. In addition to the monitor742, other output peripheral devices can include components such as speakers (not shown) and a printer746which can be connected to computer702via the input/output interfaces740.
Computer702can operate in a networked environment using logical connections to one or more remote computers, such as a remote computing device748. By way of example, the remote computing device748can be a personal computer, portable computer, a server, a router, a network computer, a peer device or other common network node, game console, and the like. The remote computing device748is illustrated as a portable computer that can include many or all of the elements and features described herein relative to computer702.
Logical connections between computer702and the remote computer748are depicted as a local area network (LAN)750and a general wide area network (WAN)752. Such networking environments are commonplace in offices, enterprise-wide computer networks, intranets, and the Internet.
When implemented in a LAN networking environment, the computer702is connected to a local network750via a network interface or adapter754. When implemented in a WAN networking environment, the computer702typically includes a modem756or other means for establishing communications over the wide network752. The modem756, which can be internal or external to computer702, can be connected to the system bus708via the input/output interfaces740or other appropriate mechanisms. It is to be appreciated that the illustrated network connections are exemplary and that other means of establishing communication link(s) between the computers702and748can be employed.
In a networked environment, such as that illustrated with computing environment700, program modules depicted relative to the computer702, or portions thereof, may be stored in a remote memory storage device. By way of example, remote application programs758reside on a memory device of remote computer748. For purposes of illustration, application programs and other executable program components such as the operating system are illustrated herein as discrete blocks, although it is recognized that such programs and components reside at various times in different storage components of the computing device702, and are executed by the data processor(s) of the computer.
Various modules and techniques may be described herein in the general context of computer-executable instructions, such as program modules, executed by one or more computers or other devices. Generally, program modules include routines, programs, objects, components, data structures, etc. that perform particular tasks or implement particular abstract data types. Typically, the functionality of the program modules may be combined or distributed as desired in various embodiments.
An implementation of these modules and techniques may be stored on or transmitted across some form of computer readable media. Computer readable media can be any available media that can be accessed by a computer. By way of example, and not limitation, computer readable media may comprise “computer storage media” and “communications media.”
“Computer storage media” includes volatile and non-volatile, removable and non-removable media implemented in any method or technology for storage of information such as computer readable instructions, data structures, program modules, or other data. Computer storage media includes, but is not limited to, RAM, ROM, EEPROM, flash memory or other memory technology, CD-ROM, digital versatile disks (DVD) or other optical storage, magnetic cassettes, magnetic tape, magnetic disk storage or other magnetic storage devices, or any other medium which can be used to store the desired information and which can be accessed by a computer.
“Communication media” typically embodies computer readable instructions, data structures, program modules, or other data in a modulated data signal, such as carrier wave or other transport mechanism. Communication media also includes any information delivery media. The term “modulated data signal” means a signal that has one or more of its characteristics set or changed in such a manner as to encode information in the signal. By way of example, and not limitation, communication media includes wired media such as a wired network or direct-wired connection, and wireless media such as acoustic, RF, infrared, and other wireless media. Combinations of any of the above are also included within the scope of computer readable media.
FIG. 8shows functional components of a game console102in more detail. Game console102has a central processing unit (CPU)800and a memory controller802that facilitates processor access to various types of memory, including a flash ROM (Read Only Memory)804, a RAM (Random Access Memory)806, a hard disk drive808, and a portable media drive809. CPU800is equipped with a level 1 cache810and a level 2 cache812to temporarily store data and hence reduce the number of memory access cycles, thereby improving processing speed and throughput.
CPU800, memory controller802, and various memory devices are interconnected via one or more buses, including serial and parallel buses, a memory bus, a peripheral bus, and a processor or local bus using any of a variety of bus architectures. By way of example, such architectures can include an Industry Standard Architecture (ISA) bus, a Micro Channel Architecture (MCA) bus, an Enhanced ISA (EISA) bus, a Video Electronics Standards Association (VESA) local bus, and a Peripheral Component Interconnects (PCI) bus also known as a Mezzanine bus.
As one suitable implementation, CPU800, memory controller802, ROM804, and RAM806are integrated onto a common module814. In this implementation, ROM804is configured as a flash ROM that is connected to the memory controller802via a PCI (Peripheral Component Interconnect) bus and a ROM bus (neither of which are shown). RAM806is configured as multiple DDR SDRAM (Double Data Rate Synchronous Dynamic RAM) that are independently controlled by the memory controller802via separate buses (not shown). The hard disk drive808and portable media drive809are connected to the memory controller via the PCI bus and an ATA (AT Attachment) bus816.
A 3D graphics processing unit820and a video encoder822form a video processing pipeline for high speed and high resolution graphics processing. Data is carried from the graphics processing unit820to the video encoder822via a digital video bus (not shown). An audio processing unit824and an audio codec (coder/decoder)826form a corresponding audio processing pipeline with high fidelity and stereo processing. Audio data is carried between the audio processing unit824and the audio codec826via a communication link (not shown). The video and audio processing pipelines output data to an A/V (audio/video) port828for transmission to the television or other display. In the illustrated implementation, the video and audio processing components820-828are mounted on the module814.
Also implemented on the module814are a USB host controller830and a network interface832. The USB host controller830is coupled to the CPU800and the memory controller802via a bus (e.g., PCI bus) and serves as host for the peripheral controllers836(1)-836(4). The network interface832provides access to a network (e.g., Internet, home network, etc.) and may be any of a wide variety it of various wire or wireless interface components including an Ethernet card, a modem, a Bluetooth module, a cable modem, and the like.
The game console102has two dual controller support subassemblies840(1) and840(2), with each subassembly supporting two game controllers power button831and a media drive eject button833, as well as any LEDs (light emitting diodes) or other indicators exposed on the outer surface of the game console. The subassemblies840(1),840(2), and842are coupled to the module814via one or more cable assemblies844.
Eight memory units834(l)-834(8) are illustrated as being connectable to the four controllers836(1)-836(4), i.e., two memory units for each controller. Each memory unit834offers additional storage on which games, game parameters, and other data may be stored. When inserted into a controller, the memory unit834can be accessed by the memory controller802.
A system power supply module850provides power to the components of the game console102. A fan852cools the circuitry within the game console102.
A console user interface (UI) application860is stored on the hard disk drive808. When the game console is powered on, various portions of the console application860are loaded into RAM806and/or caches810,812and executed on the CPU800. Console application860presents a graphical user interface that provides a consistent user experience when navigating to different media types available on the game console.
Game console102implements a cryptography engine to perform common cryptographic functions, such as encryption, decryption, authentication, digital signing, hashing, and the like. The cryptography engine may be implemented as part of the CPU800, or in software stored on the hard disk drive808that executes on the CPU, so that the CPU is configured to perform the cryptographic functions. Alternatively, a cryptographic processor or co-processor designed to perform the cryptographic functions may be included in game console102.
Game console102may be operated as a standalone system by simply connecting the system to a television or other display. In this standalone mode, game console102allows one or more players to play games, watch movies, or listen to music. However, with the integration of broadband connectivity made available through the network interface832, game console102may further be operated as a participant in online gaming, as discussed above.
It should be noted that although the game console discussed herein is described as a dedicated game console (not a general-purpose PC running computer games), the game console may also incorporate additional functionality. For example, the game console may include digital video recording functionality so that it can operate as a digital VCR, the game console may include channel tuning functionality so that it can tune and decode television signals (whether they be broadcast signals, cable signals, satellite signals, etc.), and so forth. Further, in alternate embodiments, the game console is replaced with a set top box or other computing device.
Although the description above uses language that is specific to structural features and/or methodological acts, it is to be understood that the invention defined in the appended claims is not limited to the specific features or acts described. Rather, the specific features and acts are disclosed as exemplary forms of implementing the invention.
Claims
- A method, comprising: at a statistics server, receiving an access token including a digital signature and a game result from a game console;determining, by the statistics server, a rating for the game result;if the rating for the game fails to meet a predetermined criteria, preventing, by the statistics server, receiving a recorded game associated with the game result wherein the recorded game is a recording of a previously played game;validating, by the statistics server, the access token including the digital signature;and if the rating for the game result meets the predetermined criteria, receiving, by the statistics server, the recorded game associated with the game result from the game console and if the access token including the digital signature is valid attaching the recorded game to the rating, wherein the recorded game includes an audio file containing a recorded voice of a user of the game console, and wherein other players can access the recorded game through the online gaming service.
- A method as recited in claim 1 wherein the game result is a game score.
- A method as recited in claim 1 wherein the predetermined criteria is a rating in the top n scores.
- A method as recited in claim 1 wherein receiving a recorded game is in response to a request sent to the game console.
- A method as recited in claim 1 further comprising providing a list of recorded games available for download to a requesting player.
- A method as recited in claim 1 further comprising providing a list of recorded games available for download to a requesting game console.
- A method as recited in claim 1 further comprising modifying the predetermined criteria.
- A method as recited in claim 1 further comprising attaching additional game-related data to the rating.
- A method as recited in claim 1 further comprising saving the game result and the attached recorded game in a storage device.
- A method as recited in claim 1 further comprising deleting the game result and the attached recorded game after a predetermined period of inactivity by the game console user.
- A method as recited in claim 1 further comprising reducing the rating of the game result over a period of time.
- A method as recited in claim 1 further comprising saving the game result and an identifier associated with the recorded game in a leaderboard.
- One or more computer-readable memories containing a computer program that is executable by a processor to perform the method recited in claim 1 .
- A method, comprising: at a statistics server, receiving a game result from a game console;determining, by the statistics server, whether to allow the game console user to upload game-related data associated with the game result;if the game console user is not allowed to upload the game-related data: preventing, by the statistics server, the user from uploading the game-related data;and if the game console user is allowed to upload the game-related data: sending, by the statistics server, an access token including a digital signature to the game console;receiving, by the statistics server, the access token and the game-related data associated with the game result, wherein the game-related data includes an audio file containing a recorded voice of a user of the game;validating, by the statistics server, the access token including the digital signature;and if the access token including the digital signature is valid, associating, by the statistics server, the game-related data with the game result, wherein other users can access the game-related data through an online gaming service.
- A method as recited in claim 14 further comprising determining a rating for the game result.
- A method as recited in claim 15 further comprising associating the game-related data with the rating.
- A method as recited in claim 14 wherein the game result is a game score.
- A method as recited in claim 14 wherein the access token includes a name of the game-related data.
- A method as recited in claim 14 wherein the access token includes an identity of the game console user.
- A method as recited in claim 14 wherein the access token includes a game console identifier.
- A method as recited in claim 14 wherein the access token includes a maximum size of the game-related data.
- A method as recited in claim 14 wherein the game-related data includes a recorded game and wherein the recorded game is a recording of a previously played game.
- A method as recited in claim 14 wherein the game-related data includes at least one highlight from a game.
- One or more computer-readable memories containing a computer program that is executable by a processor to perform the method recited in claim 14 .
- A method, comprising: at a statistics server, receiving a game score from a game console;determining, by the statistics server, a rating for the game score;entering, by the statistics server, the rating in a leaderboard;if the rating satisfies a predetermined criteria: receiving, by the statistics server, an access token including a digital signature and the game-related data associated with the game score, wherein the game-related data includes an audio file containing a recorded voice of a user of the game console;validating, by the statistics server, the access token including the digital signature;if the access token including the digital signature is valid: entering, by the statistics server, a reference identifier in the leaderboard, wherein the reference identifier is associated with the game-related data;and entering, by the statistics server, an indicator in the leaderboard, wherein the indicator is associated with the game-related data and indicates whether the game-related data is available for download;and if the rating fails to satisfy the predetermined criteria, discarding, by the statistics server, the game-related data associated with the game score.
- A method as recited in claim 25 wherein users of the online gaming service can access the game-related data through the leaderboard.
- A method as recited in claim 25 wherein determining a rating for the game score includes comparing the game score to other game scores in the leaderboard.
- A method as recited in claim 25 wherein the leaderboard is associated with a particular game program.
- A method as recited in claim 25 wherein the predetermined criteria is a rating in the top n percent of all ratings.
- An apparatus, comprising: means for receiving a game result at a statistics server from a game console;means for determining a rating associated with the game result;means for receiving an access token including a digital signature and a recorded game associated with the game result if the rating associated with the game result meets a predetermined criteria wherein the recorded game is a recording of a previously played game;means for discarding the recorded game associated with the game result if the rating associated with the game result fails to meet the predetermined criteria;means for validating the access token including the digital signature;means for attaching the recorded game to the rating if the access token including the digital signature is valid, wherein other players can access the recorded game through an online gaming service;and means for attaching an audio file containing a recorded voice of a user of the game console to the rating.
- An apparatus as recited in claim 30 further comprising means for attaching additional game-related data to the rating.
- An apparatus as recited in claim 30 further comprising means for storing the recorded game and an identifier associated with the recorded game.
- One or more computer-readable media having stored thereon a computer program that, when executed by one or more processors, causes the one or more processors to: receive game results at a statistics server and from a game console;determine, by the statistics server, a rating associated with the game results;if the rating exceeds a predetermined threshold value: digitally sign, by the statistics server, an access token;send, by the statistics server, the signed access token to the game console;receive, by the statistics server, the signed access token and game-related data associated with the rating, wherein the game-related data includes an audio file containing a recorded voice of a user of the game console;validate, by the statistics server, the signed access token;and if the signed access token is valid, associate, by the statistics server, the game-related data with the rating, wherein other users of an online gaming service can download the game-related data;if the rating fails to exceed a predetermined threshold value, discarding, by the statistics server, the game-related data associated with the rating;analyzing a plurality of game related data at the statistics server to identify valid game related data;and deleting, by the statistics server, any invalid game related data.
- One or more computer-readable media as recited in claim 33 wherein the game related-data is a recorded game and wherein the recorded game is a recording of a previously played game.
Disclaimer: Data collected from the USPTO and may be malformed, incomplete, and/or otherwise inaccurate.