U.S. Pat. No. 6,764,402
IMAGE-DISPLAY GAME SYSTEM AND INFORMATION STORAGE MEDIUM USED THEREFOR
AssigneeNintendo Co., Ltd.
Issue DateJanuary 23, 2002
U.S. Patent No. 6,764,402: Image-Display Game System And Information Storage Medium Used Therefor
Summary:
Nintendo describes the multi-player, portable version of its Pokemon game in this patent. In the pokemon game, each player collects and trains pokemon. When another player is encountered, the pokemon battle each other and the winner captures the loser’s pokemon. Capturing a pokemon includes transferring information about its appearance, strength, etc. to the wining player’s game machine.
Battling other actual players, as opposed to simulated opponents, is encouraged by allowing pokemon captured from another player to have a “virus” that allows them to be more effective in battle. The virus spreads quickly, thus helping a player’s entire collection of pokemon. The patent explains that players whose pokemon have the “virus” will become popular: “The player who luckily captures a virus-infected pokemon … becomes busy with other players’ requests for pokemon data exchange, thereby increasing popularity among other players. As such, the game is useful for cultivating friendship with other players.”
Although the game may bring you new friends, those friends don’t have to stick around once they’re done using you. It is possible to receive information about player and his cadre of Pokemon, and then do virtual battle with him later on. There may be some disadvantages to this approach, however. The properties of the pokemon change with the time of day, and a battle that takes place at night may come out differently than a battle that takes place during the day.
The patent also describes a system for allowing players of different versions of the game to battle each other: Whatever information about a captured pokemon is unavailable from the old version of the game gets made up (assigned randomly) at the time of data transfer. Conversely, data about a pokemon from the new version that cannot be received by the old version is discarded. This ingenious system can also be used to allow users who upgrade to the new version to transfer their old collection of pokemon.
Exemplary Claim:
A method of operating a multiplayer video game system for playing a video game involving characters that may be captured by a player comprising the steps of:
establishing communication between a first player’s video game device and a second player’s video game device;
associating time related data with at least a first video game character that may be captured by a player;
controlling the display of said first video game character based upon said time related data;
receiving by said first player’s video game device identification information identifying said second player; and
storing data in said first player’s video game device relating to said at least one video game character associated with said second player including said time related data.
Illustrative Figure
Abstract
No abstract is available for this record.
Description
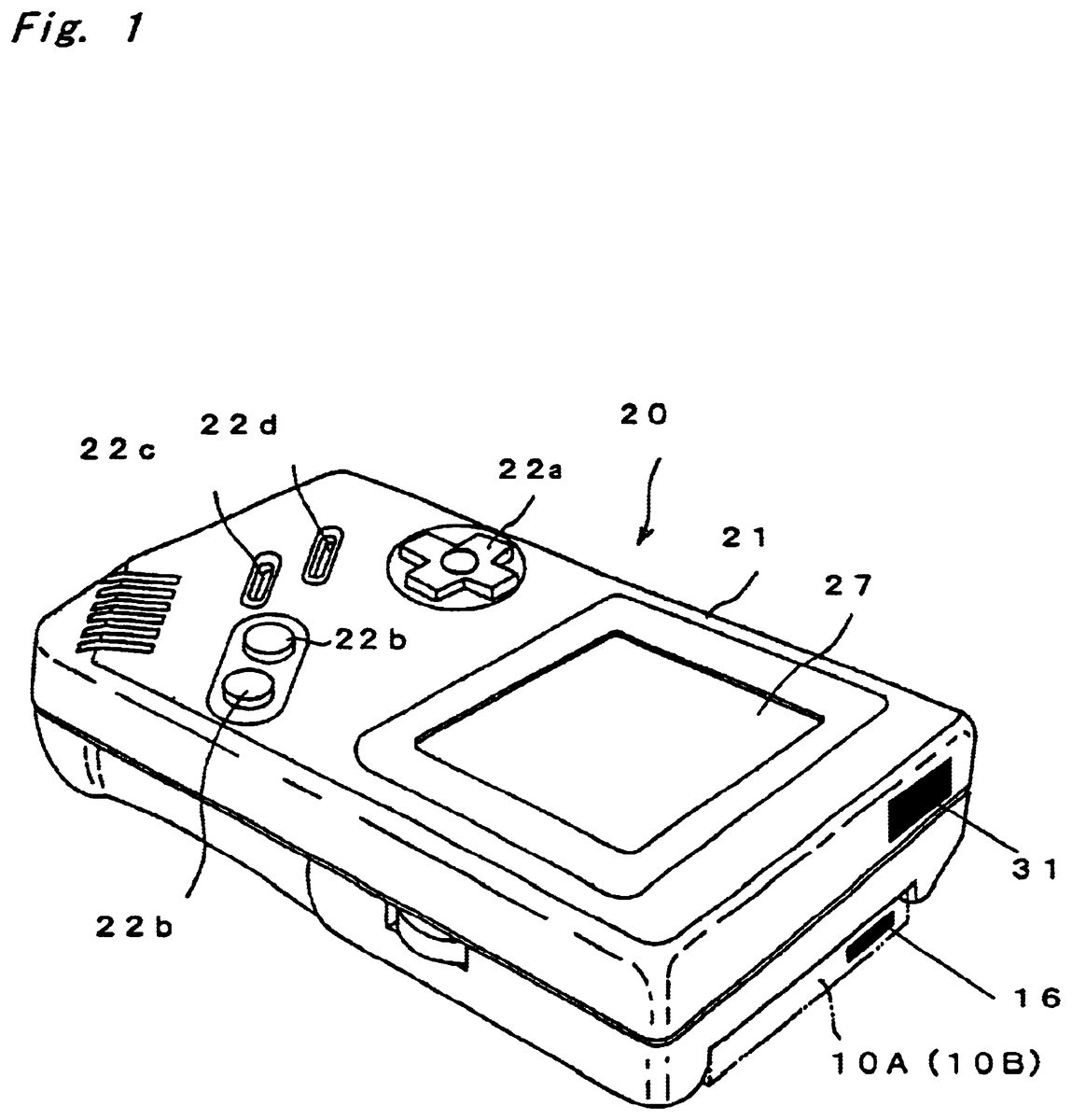
DESCRIPTION OF THE PREFERRED EMBODIMENTS In FIG. 1 , an external view of a portable game machine to which an image-display game system according to an embodiment of the present invention applied is shown. In FIG. 2 , the structure of the portable game machine in FIG. 1 is shown. As shown in FIG. 1 , the image-display game system according to the present embodiment is structured by a game cartridge 10 A, which is an example of information storage medium, and a portable game machine 20 , which is an example of image-display game machine engageable with the game cartridge 10 A in a detachable manner. There are at least two portable game machines 20 , each attached with the game cartridge 10 A or a conventional game cartridge 10 B. The game cartridge (or ROM cartridge; hereinafter, referred simply to as cartridge ) 10 A includes, as shown in FIG. 2 , program storage means, exemplarily implemented by nonvolatile memory (hereinafter, ROM ) 11 ; temporal storage means by readable/writable memory (hereinafter, RAM ) 12 ; a connector 13 ; a clock circuit (timer) 14 ; a memory bank switch control circuit 15 ; and communications means (circuit) exemplarily implemented by infrared transmitter/receiver 16 , and all of which are mounted on a substrate (not shown). The substrate is housed in a case or a housing (not shown). ROM 11 , RAM 12 , clock circuit 14 , memory bank switch control circuit 15 , and infrared transmitter/receiver 16 are respectively coupled to terminals of the connector 13 through data bus and address bus, and then are coupled to a connector 24 of the portable game machine 20 . As is known from a left in FIG. 2 , the conventional cartridge 10 B includes the ROM 11 ...
DESCRIPTION OF THE PREFERRED EMBODIMENTS
In FIG. 1 , an external view of a portable game machine to which an image-display game system according to an embodiment of the present invention applied is shown. In FIG. 2 , the structure of the portable game machine in FIG. 1 is shown. As shown in FIG. 1 , the image-display game system according to the present embodiment is structured by a game cartridge 10 A, which is an example of information storage medium, and a portable game machine 20 , which is an example of image-display game machine engageable with the game cartridge 10 A in a detachable manner. There are at least two portable game machines 20 , each attached with the game cartridge 10 A or a conventional game cartridge 10 B.
The game cartridge (or ROM cartridge; hereinafter, referred simply to as cartridge ) 10 A includes, as shown in FIG. 2 , program storage means, exemplarily implemented by nonvolatile memory (hereinafter, ROM ) 11 ; temporal storage means by readable/writable memory (hereinafter, RAM ) 12 ; a connector 13 ; a clock circuit (timer) 14 ; a memory bank switch control circuit 15 ; and communications means (circuit) exemplarily implemented by infrared transmitter/receiver 16 , and all of which are mounted on a substrate (not shown). The substrate is housed in a case or a housing (not shown). ROM 11 , RAM 12 , clock circuit 14 , memory bank switch control circuit 15 , and infrared transmitter/receiver 16 are respectively coupled to terminals of the connector 13 through data bus and address bus, and then are coupled to a connector 24 of the portable game machine 20 . As is known from a left in FIG. 2 , the conventional cartridge 10 B includes the ROM 11 , RAM 12 , and connector 13 .
The nonvolatile memory 11 unalterably stores a game program, and exemplarily implemented by ROM, flash memory, or EE-PROM. The ROM 11 includes, as shown in FIG. 3 , storage regions of I 11 to I 17 each for storing various program data, image data, or setting data.
More specifically, a program region Ill stores programs relevant to game details such as main program, switch processing program, object (or character) control program, image processing program, audio processing program, and the like. If the game includes capturing and training pokemons, exemplary programs relevant to the game details including a capturing program and a training program are stored. In addition thereto, a program for storing DOT (image) data for the respective pokemons and exchanging data among other game machines 20 (not shown), and a program for ensuring compatibility with the conventional cartridges 10 B are stored.
An image data region I 12 is for storing, separately, image data for every pokemon to be appeared in the game and that for other objects (characters) such as human being, background, or items to be displayed. A pokemon data region I 13 stores property data for distinguishing every pokemon by name, kind, height (stature), weight, habitat, time range for appearance, possible technique, characteristic, cry, and the like.
A sound data region I 14 stores data for sound effects and BGM for the game. In detail, BGM data depending on the game scene such as an opponent's appearing, or in the daytime or at night, and digital data for pokemons' cry and sound effects are stored.
A pokemon appearance probability table storage region I 15 stores, for every pokemon, both habitat and appearance probability data. The appearance probability data is stored such that the appearance probability varies between daytime and night, as required.
A zone map storage region I 16 stores a zone range where a main character activated by the player can move, and data for a map of the zone.
A miscellaneous storage region I 17 stores miscellaneous data, such as a processing program for determining, exemplarily on the basis of ID data, or an item to present as a gift (or give) to a player, who is a partner of data exchange or communications.
Hereinafter, when there is no need to discriminate the cartridge between new-type or conventional, the cartridge is collectively denoted by a reference numeral 10 .
The RAM 12 has a region for storing property data varied in type respectively for the characters captured in the course of the game. Such storage region on the RAM 12 includes, as shown in FIG. 4 , a captured pokemon data region 12 A for storing any captured (or obtained) pokemon, an on-hand pokemon storage region 12 B, a battle data storage region 12 C, a table region 12 D, and a miscellaneous storage region 12 E.
The captured pokemon data region 12 A includes areas 120 to 128 and 12 a to 12 d for every pokemon character, which is a fictionally-created monster.
The area 120 is an area for storing pokemon codes (or pokemon numbers).
The area 121 stores a hit point (HP), for each pokemon code, which indicates the pokemon's power.
The area 122 stores the pokemon's experience point.
The area 123 stores the pokemon's level.
The area 124 stores the pokemon's status.
The area 125 stores data relevant to the pokemon's possible attack (technique).
The area 126 stores parental ID data indicating who captured the pokemon (the player's name or ID data).
The area 127 stores ability value of attack, defense, special attack, special defense, speed, and the like.
The area 128 is an area left vacant for storing data not defined yet.
The area 12 a stores the pokemon's sex.
The area 12 b stores items on hand, exemplarily weapons available for the pokemon to fight against opponents.
The area 12 c stores data (virus data) indicating whether the pokemon has been infected by any virus, data indicating the virus type if infected, or both.
The area 12 d is an area left vacant for storing miscellaneous data.
The areas 120 to 128 are storage areas provided to both of the new-type cartridge 10 A and the conventional cartridge 10 B, and any data stored therein is compatible. The areas 12 a to 12 d are unique only to the new-type cartridge 10 A.
The on-hand pokemon data storage region 12 B stores six pokemon codes or pokemon numbers assigned to those selected by the player among from those stored in the captured pokemon data region 12 A. These six pokemons can travel with the main character.
The battle data storage region 12 C stores another player's (trainer's) name, with whom the player is having a battle with through a communications cable 40 , and various data relevant to his/her pokemons joined in the battle (e.g., pokemon number, HP, level). The battle data storage region 12 C includes an area for storing battle character data (pokemons' names), and an area for storing data, for every pokemon joined the battle, corresponding to the areas 120 to 12 d.
The table region 12 D stores table data for determining an item to be presented in response to ID code communicated or exchanged by using the infrared transmitter/receiver 16 , and data for determining an item to be presented, based on the number of steps, in response to step-number data provided through communications with a pedometer-incorporated game machine 50 .
The miscellaneous storage region 12 E includes areas 12 f , 12 g , 12 h , and 12 i . The area 12 f is an area for storing the player's name data as a part of the ID data. Soon after the time of purchase, the player actuates operation switches 22 a and 22 b to store his/her name or nickname therein.
The area 12 g includes an area for storing the player's own ID data and an area for storing other ID data for a predetermined number of players (5 players). To the area for storing the player's own ID data in the area 12 g , ID data determined based on the player's name or nickname stored after the purchase of the cartridge 10 A and random numbers is automatically written. To the area for storing other players' ID data in the area 12 g , their ID data (ID codes) transmitted from their portable game machines 20 is successively written for a predetermined number of players. With respect to each ID data stored in the area, time data (e.g., time, date) indicating when data communications was made is also written.
By additionally storing time data for each ID data, the area 12 g receives ID data limited on a one-person-one-ID-data basis, thereby preventing any identical ID data from being received many times in a single day. Further, by setting the upper limit for the ID data to be stored, for example, to 5, the area 12 g stops storing ID data once reached the upper limit regardless of the number of players communicating (or exchanging data) for the day. In this manner, the player is thus encouraged to have communications with various players for each day, rather than sticking to only one player. As such, the game can help players to make friends and further, to improve communications thereamong.
To the area 12 h , item data relevant to, for example, helping items is written. The helping items are presented based on random numbers generated in accordance with other players' ID data obtained through communications or numbers obtained by computing such ID data with a predetermined equation. These helping items are beneficial in the course of the game, and include medicine for accelerating pokemons' growth or evolution, protective gear against opponents' attack, medicine for restoring pokemons' lives, and the like.
Such helping items (helping data) provided based on the ID data are preferably not obtainable only by playing the game. Accordingly, the player becomes willing to communicate with other players to exchange ID data, and thus data communications among players is encouraged.
The area 12 i stores data for other player's pokemons having the battle with, for example six, and the player's name. After once written into the area 12 i through data communications, such pokemon data becomes available for the user's battle strategy throughout the battle.
The clock circuit 14 includes a timer at least counting time, and if required, indicating date (month/day) and day of the week. When a memory chunk of the ROM 11 is too large for an address bus to address, the memory bank switch control circuit 15 divides the memory chunk into a plurality of memory banks, and generates bank data for the higher address in the ROM 11 and for addressing a memory chunk on the RAM 12 . It is herein preferable to integrate the clock circuit 14 and the memory bank switch control circuit 15 on a one-chip integrated circuit (IC) so as to reduce the number of chips and cost.
As shown in FIG. 1 , the portable game machine 20 includes the operation switches 22 arranged on the lower part of the surface (plane) of a housing 21 , and a liquid crystal display 27 placed on the upper part thereof. In the housing 21 , the circuit board having the constituents as shown in FIG. 2 mounted thereon is accommodated. The operation switches 22 include a direction switch 22 a used to move a cursor and direct any character available for the player in desired directions, an action switch 22 b used for an action command, a start switch 22 c , and a selection switch 22 d.
To be more specific, the portable game machine 20 is equipped with a central processing unit (CPU) 23 . The connector 24 is connected to the CPU 23 for connection with the cartridge 10 . A working RAM 25 for temporarily storing data for game processing, and a display control circuit 26 are also connected thereto. When a mode (continue mode) of continuing the previously-played game is selected at the start of the game, the RAM 25 is supplied with backup data stored on the RAM 12 in the cartridge 10 A. Therefore, the RAM 25 is allocated with the same storage regions or areas as with the RAM 12 . In the following description, the storage region or area for the RAM 25 is under the same name and reference numeral provided to that of the RAM 12 .
The liquid crystal display (LCD) 27 is connected to the display control circuit 26 . A connector 29 is connected to the CPU 23 via an interface 28 . The connector 29 is connected to a connector 29 provided to other portable game machine 20 via a cable which is the communications means for pokemon trading with the owner (player) of the portable game machine 20 . As an alternative to such cable, the infrared transmitter/receiver 16 in the cartridge 10 A is a possibility. Or instead of the infrared transmitter/receiver 16 , an infrared transmitter/receiver 31 may be integrally attached to the housing of the portable game machine 20 .
FIGS. 5 and 6 exemplarily show how two game machines according to the embodiment of the present invention are connected for data communications or data exchange. In FIG. 5 , two portable game machines 20 are exemplarily connected to each other via the cable 40 for data communications.
In FIG. 6 , two game machines 20 perform data communications therebetween with the infrared transmitter/receivers 16 . These two game machines 20 are wirelessly connected by means of the infrared transmitter/receivers 16 . In such case, even if the conventional game machine 20 is not equipped with any cable connector or the infrared transmitter/receiver 16 , there only need to provide the infrared transmitter/receiver 16 to the cartridge 10 A to perform data communications. Alternatively, the infrared transmitter/receiver 16 may be integrally provided somewhere in the housing of the game machine 20 .
FIG. 7 shows a case where the infrared transmitter/receiver 16 in the game machine 20 and an infrared transmitter/receiver 51 in the pedometer-incorporated game machine 50 perform data communications therebetween.
Next, with reference to an exemplary game map in FIG. 8 , how the game proceeds on the image-display game system of this embodiment is described. For an exemplary game for capturing (collecting) and training the fictionally-created pokemons, and letting such pokemons have battles with other players' pokemons, a main character assumed to be the player himself/herself sets off to capture and collect pokemons. In such a game, the main character travels into pond, woods, or grassy areas where pokemons live, and runs into one of them. There, the player lets his or her own captured/trained pokemon fight against the encountered pokemon. If the player's pokemon beats the other, the player captures the defeated pokemon and adds it to his collection. By repeating this, the player captures pokemons up to the limit (maximum) set in the program, and completes his or her pokemon collection. Herein, the main character can bring along a predetermined number of pokemons (e.g., 6), and such pokemons are designated on-hand pokemons.
In detail, the player depresses the start switch 22 c to start the game. After the title screen, the player sees an initial screen for the game (a part of FIG. 8 ) showing a part of a map for a certain stage shown in FIG. 8 . The player moves a player character (or player object) on the map by actuating the direction switch 22 a , allowing travel into any possible area where the pokemons live to permit capture thereof. The pokemons ' habitats vary according to the pokemons' kinds, for example, in pond or sea for water pokemons, or in grassy area, field, woods for grass pokemons.
The pokemons have unique characteristics, and some come out only at a specific area and time. For example, when the clock circuit 14 indicates the program-set time or time range, appropriateness of such pokemon's appearance, appearance probability, or both is conditionally changed.
By taking nocturnal pokemons (e.g., owl pokemon or bat pokemon) as an example, the appearance probability thereof starts to increase at nightfall or stays at a certain level for a set duration and then becomes higher at midnight. The probability then starts to decrease as dawn approaches, and reaches minimum in the daytime (e.g., appearance probability 0).
Conversely, for diurnal pokemons, the appearance probability thereof reaches its maximum in the daytime, and 0 at midnight. For pokemons changing their hiding areas depending on time range or time, program setting is change accordingly. Specifically, for pokemons living in water in the daytime but on the land at nighttime, program setting is set such that those pokemons change or relocate their habitats depending on time.
Once the player captures a pokemon, its pokemon number is written into the vacant area in the captured pokemon data region 12 A. Simultaneously, the pokemon's current hit point (HP), experience point, level, state, technique, ability, and the like, are written into the areas 120 to 128 , respectively. If the player's cartridge is a type that includes pokemon's property data of sex, item, and virus, for example, such data is written respectively into the areas 12 a , 12 b , and 12 c.
Note that the virus-infected pokemon is rare, and, thus, its rate of increase for HP, experience point, level, or ability value obtained through the training is set higher than a non-virus-infected pokemons'. Accordingly, the player desires to find the virus-infected pokemon to accelerate his or her pokemons' growth or training. If found, the player acquires the newly-captured virus-infected pokemon as his or her on-hand pokemons (or put all in a training box), and virus-infected pokemon infects his or her own not-yet-infected pokemons, allowing them to grow quicker. As such, with the help of such a trick for accelerating pokemons' growth or level-up as virus infection, the player can advantageously shorten training time taken for the pokemons to reach a certain level.
When the game is played with the game cartridge 10 A including pokemons' sex data, the player can select a male and a female from among the captured pokemons of a kind (those having the same pokemon code) and put those in the training box. The time or day is temporarily stored in a register. When the clock circuit 14 indicates that a program-determined number of days has passed, the pokemon couple have a baby, which inherits their property data (e.g., ability, power). The baby is counted as one of the player's own pokemons and is tradable with other players.
Accordingly, the pokemons can be easily collected and the game proceeds quicker. The player can enjoy, with full expectations, training the baby pokemon from its childhood. When the player has several pokemons of a kind, he or she can trade any of those with other players' pokemons of a different kind.
For pokemon trading between owners of new-type cartridge 10 A and conventional cartridge 10 B, it is preferable to ensure compatibility to the extent possible therebetween as to data for pokemons' sex, item, virus infection, and the like, stored in the areas 12 a to 12 c . For such purpose, at the time of data transfer from the new-type cartridge 10 A to the conventional cartridge 10 B, the vacant area 128 stores, with one bit, whether the areas 12 a to 12 c have any data therein.
If the game is played with the conventional cartridge 10 B, the game proceeds without such additional data as pokemons' sex, item, and virus-infection. After data transfer is made from the conventional cartridge 10 B to the new-type cartridge 10 A, the owner of the new-type cartridge 10 A can use such additional data for the game.
When data transfer is made from the conventional cartridge 10 B to the new-type cartridge 10 A, conversely, sex data not available in the conventional cartridge 10 B is determined in accordance with a predetermined rule, and is written into the area 12 a of the new-type cartridge 10 A. Such predetermined rule may function such that a number in the last digit of the time indicated by the clock circuit 14 determines the sex, for example, male for odd numbers, and female for even numbers.
In this manner, the conventional cartridge 10 B and the new-type cartridge 10 A can be compatible to the extent possible with each other for pokemon trading, and such compatibility allows a large number of players to exchange data. Furthermore, if the owner of the conventional cartridge 10 B additionally purchases the new-type cartridge 10 A, he or she can transfer every single pokemon trained in the conventional cartridge 10 B to the new-type cartridge 10 A and use those transferred pokemons.
As such, captured pokemons, those generated from pokemon couples, and those traded with other players are used to have battles with other players' pokemons.
To have a battle, the connector 29 and 29 of the portable game machines 20 and 20 are connected by a cable. Each player then designates a pokemon and puts it on a battle ground. Exemplary game screens are shown in FIGS. 19 and 20 , which will be described later.
Described below is the operation of the game machine 20 with the cartridge 10 A attached by referring to FIGS. 9 , 10 , 11 , 12 , 13 , 14 , 15 , and 16 . FIG. 9 is a flowchart for the entire process (main routine); FIG. 10 shows a flowchart for normal game processing; FIG. 11 shows a flowchart for virus infection processing; FIG. 12 shows a flowchart for virus elimination processing; FIG. 13 shows a flowchart for battle game processing; FIG. 14 shows a flowchart for mysterious gift processing in which the items (helping items) that are beneficial in the course of the game are presented through ID data communications; FIG. 15 shows the relationship between the numbers obtained by computation in the gift processing and the items; FIG. 16 shows a flowchart for communication processing made with the pedometer; and FIG. 17 shows the relationship between the step-number data provided by the communications processing made with the pedometer and the items.
FIGS. 18 , 19 , 20 , and 21 show various game screens displayed in the course of the above game.
First of all, with reference to the flowchart for the entire process in FIG. 9 , it is briefly described how the image-display game system of this embodiment operates.
In step S 1 , after the start switch 22 c is depressed, the CPU 23 carries out processing with respect to a program stored in the ROM 11 . In the following description, the CPU 23 is not mentioned for any program processing carried out thereby.
The procedure is started with the game start processing. In the game start processing, a mode selection screen is first displayed for mode commands' selection. The mode selection screen shows menus including a game start mode to start the game from initial position, a continue mode to start the game from the position discontinued when previously played, a mysterious gift mode to present the items (helping items) that are beneficial in the course of the game through ID data communications with other players, and a mode to perform data communications with the pedometer.
When the game start mode is selected, the internally-stored RAM 25 is cleared to start the game.
When the continue mode is selected, after the internally-stored RAM 25 is cleared, the RAM 12 in the cartridge 10 A is read out for backup data indicating the previous game's process. The backup data is written into the RAM 25 . In this manner, the data stored on the RAM 25 at the start of the game is the backup data read out from the RAM 12 , and the data stored on RAM 25 is updated as the game proceeds.
In step S 2 , the player object (or character) processing subroutine is carried out. This processing allows the player object to move in response to the direction switch 22 a , and to change in shape in response to the action switch 22 c.
In step S 3 , this processing subroutine is carried out for objects but not for the player object. This processing allows opponent objects to come out or alley objects to be displayed as the player objects moves, in accordance with the program setting.
In step S 4 , background image processing is carried out. This processing allows background images to change as the player object moves or acts.
In step S 5 , the normal game processing subroutine is carried out. The details thereof are later described by referring to FIG. 10 .
In step S 6 , the virus elimination (or removal) processing subroutine is carried out. This virus elimination processing is done with respect to any pokemon virus infected in later-described step S 13 in FIG. 10 . Herein, the virus-infected pokemon(s) are put back to the state before virus infection after a predetermined length of time has passed. The details of the virus elimination processing subroutine in this step are later described by referring to FIG. 12 .
In step S 7 , the battle game processing subroutine is carried out. The battle game processing is done with respect to a mode of having an online battle with the other player's game machine 20 connected through the cable 40 , as exemplarily shown in FIG. 5 . The details of this subroutine are later described by referring to FIG. 13 .
In step S 8 , the gift processing subroutine is carried out. This gift processing subroutine is carried out when the helping items beneficial in the course of the game are presented through ID data exchange between the game machines 20 by using the infrared transmitter/receivers 16 , as exemplarily shown in FIG. 6 . The details of this subroutine are later described by referring to FIG. 14 .
In step S 9 , the pedometer communications processing subroutine is carried out. This subroutine processing is done with respect to a mode of transmitting the step-number data from the pedometer-incorporated game machine 50 to the game machine 20 via the infrared transmitter/receivers 15 and 16 , as exemplarily shown in FIG. 7 . The details of this subroutine are later described by referring to FIG. 16 .
With reference to FIG. 10 , how the normal game processing in step S 5 occurs is shown. In step S 11 , it is determined whether the main character has encountered any pokemon during his or her travels on the map. As exemplarily shown in the game screen of FIG. 18 , if the main character runs into a pokemon (battle character), a determination is so made.
Thereafter, in step S 12 , the battle processing is carried out. This battle processing allows pokemons (captured and trained) traveling with the main character have battles with wild pokemons hiding on the way. By beating the wild pokemon (battle character), the main character's pokemon increases its experience points, or the wild pokemon is captured.
Thereafter, the virus infection processing subroutine is carried out in step S 13 . The details thereof are later described with reference to FIG. 11 . The processing in step S 13 is the end of this subroutine (S 5 ), and the procedure goes to step S 6 (FIG. 9 ).
If the main character is determined as not having encountered with pokemon in step S 11 , the procedure goes to step S 14 .
In step S 14 , it is determined whether the main character has met any person in general (rival called trainer, who captures and trains pokemons). If the main character is determined as having met any person in general during his or her travels on the map as exemplarily shown in the game screen of FIG. 8 , the procedure goes to step S 15 .
In step S 15 , various data for six pokemons travelling with the main character and fighting for him or her is read out to prepare for a battle. Specifically, the data read out is the one stored in the areas 120 to 12 d of the captured pokemon data region 12 A under the 1st to 6th pokemon numbers stored in the on-hand pokemon storage region 12 B.
The next processing in step S 16 is carried out for a battle between the main character (player) and a rival trainer. Therein, images of both the rival trainer and the main character are displayed to indicate that the battle mode has commenced ( FIG. 19 shows an exemplary game screen for the battle).
Thereafter, a pokemon is selected each from among those six to fight for the main character and the rival trainer, respectively, and the selected pokemons are displayed on the battle ground face-to-face ( FIG. 20 shows an exemplary game screen for the battle). At this time, each pokemon is displayed with its name, hit point (HP), life, and the like. Additional messages are displayed, indicating each action of the offensive side and defense side. This message changes every time the offensive side and defensive side are switched. As for the battle, the player can see the pokemons' ability (status) by actuating a switch for screen change ( FIG. 21 shows an exemplary game screen displaying such status). With the help thereof, the player can know how those six pokemons traveling with the main character will manage the battles. During the battle, if the main character's pokemon successfully beat the rival trainer's, the pokemon increases its experience points. Thereafter, the procedure goes to step S 13 , and the virus infection processing is carried out.
In step S 14 , if the main character is determined as not having met any person in general (trainer) the procedure goes to step S 17 .
In step S 17 , it is determined whether the main character has met any specific person (a trainer belonging to a player with which a previous online battle occurred. If determined yes, the rival trainer's pokemon data is read out in step S 18 , and the procedure goes to step S 16 for the battle processing. Then, the procedure goes to step S 13 . If this is the case, the rival trainer's name to be displayed is the other player's name stored in the area 12 i (or parental ID data corresponding to the parental ID stored in the area 126 ). In this manner, by storing the other player's pokemon data in the area 12 i at the time of online battle, the player can later play the game as if having a real battle with the other player.
When determined no in step S 17 , the procedure goes to step S 19 for miscellaneous processing, and ends this subroutine (S 5 ). The procedure is now through with this subroutine (S 5 ), and goes to step S 6 (FIG. 9 ).
Next, by referring to FIG. 11 , the virus infection processing subroutine in step S 13 is described. In this embodiment, a probability of pokemons' virus infection is set to one out of 20,000 battles. If a pokemon is infected, the preceding and subsequent pokemons are virus-infected with a probability of . The length of time for virus infection (virus-infected endurance period or virus-infected persistent period) is set to vary according to the virus type. In this embodiment, virus infection is not detrimental to the player, and it is welcomed as a conditional or environmental trick for accelerating pokemons' growth or evolution. The operation in step S 13 is now described in detail next below.
In step S 21 , it is determined whether the area 12 c of the captured pokemon data region 12 A has data (virus data) indicating any pokemon whose pokemon number is stored in the on-hand pokemon storage region 12 B on the RAM 25 has been virus infected. If the area 12 c is determined as having no data, that means no on-hand pokemon is virus infected, the procedure goes to step S 22 .
In step S 22 , it is determined whether any of the rival's pokemons have been virus infected. Such determination is made, in the online communication mode, based on the data stored in the area 12 c corresponding to the pokemon numbers stored on the RAM 25 in the rival player's portable game machine 20 . Other than in the online battle, the pokemons are set to virus infect through a naturally-virus-infected pokemon (Pokerus) with a probability of {fraction (1/20,000)}. When the rivals' pokemons are determined as not having been virus infected, the procedure is now through with the virus infection processing subroutine in step S 13 , and then goes to step S 9 (FIG. 9 ).
In step S 22 , if any of the rival's pokemons is determined as having been virus infected, the procedure goes to step S 23 and onwards. Therein, the player's on-hand pokemons are subjected to processing to be virus infected with a predetermined probability, and details thereof are as follows.
In step S 23 , the CPU 23 generates a random number R 1 according to the program. Herein, the random number R 1 is an integer in the range from 0 to 19999, and is generated at random. Accordingly, it becomes possible to let any pokemon potential for virus infection be a probability of {fraction (1/20000)}.
In step S 24 , it is determined whether the random number R 1 is 0. If not, virus infection is determined as not having occurred, and the procedure is now through with the virus infection processing subroutine (step S 13 in FIG. 10 , the flowchart in FIG. 11 : steps S 21 to S 34 ). The procedure now goes to step S 9 (FIG. 9 ).
On the other hand, if the random number R 1 is determined as being 0 in step S 24 , that means any of the on-hand pokemons is virus infected, the player's area 12 c under the virus-infected pokemon's pokemon number is provided with data (virus data) in step S 25 . Since the virus is varied in type, the virus data (virus type data) specifies the virus type. Each virus type differs in virus-infected endurance period or consequence (impact or power) brought about thereby.
In the next step S 26 , such virus-infected endurance period (Cn; or virus-infected time and endurance period) is written into the miscellaneous area 12 d of the captured pokemon data region 12 A on the RAM 25 under the virus-infected pokemon's pokemon number, and accordingly a virus-infected period count value Cn is set. This virus-infected period count value Cn varies according to the virus type and is set to 48 if the virus-infected endurance period is 48 hours. The virus-infected period count value is decreased by unit time, and when 0 is reached, the virus loses its infection power. This virus-infected period count value Cn is not restricted to hours but may be days, minutes, seconds, or any other predetermined countable value unit. Furthermore, the region for storing the count value is not restricted to the miscellaneous area 12 d but any area on the RAM 25 as long as the area is relevant to the virus-infected pokemon(s).
In the next step S 27 , another random number R 2 is generated based on the program. This random number R 2 is an integer not less than 0 and not more than 2, for example, and is used to virus infect other pokemons ranked (arranged) immediately before and after the virus-infected pokemon with the probability of . In this embodiment, with the random number R 2 is 0, those other pokemons ranked immediately before and after the virus-infected pokemon are presumably both virus infected.
In step S 28 , it is determined whether the random number R 2 is 0. If the random number R 2 is determined as being 0, that means some of the on-hand pokemons have been virus-infected (Yes in step S 24 ), the procedure goes to step S 29 to subject not infected on-hand pokemons predetermined in number to virus infection processing with the predetermined probability.
In step S 29 , the area 12 c is provided with the virus data for the pokemon numbers assigned to those arranged immediately before and after the virus-infected pokemon among those six. In detail, assuming that the pokemon third in order in the on-hand pokemon storage region 12 B is virus-infected, the pokemons second and fourth in order are also virus infected. Consequently, the virus data storage area 12 c of the captured pokemon data region 12 A is provided with the virus data for the pokemon numbers assigned to those second and fourth pokemons.
In step S 30 , in a similar manner to step S 26 , the virus-infected period data (Cn) is set to the area 12 d of the captured pokemon data region 12 A corresponding to the pokemon numbers assigned to the second and fourth pokemons. Herein, if the random number R 2 is determined as not being 0 (i.e., R 2 1 or 2) in step S 28 , those arranged immediately before and after the virus-infected pokemon are presumably not virus infected. Accordingly, the procedure is now through with the virus infection processing subroutine (S 13 ), and goes to step S 9 .
When any of the on-hand pokemons is determined as having been virus infected in step S 21 , the procedure goes to step S 31 to subject the other on-hand pokemons in predetermined number to virus infection. The processing carried out in steps S 31 to S 34 is similar to that in steps S 27 to S 30 , and those arranged immediately before and after the virus-infected pokemon are subjected to the virus infection processing with the predetermined probability. Thereafter, the procedure goes to step S 9 .
As already described above, the virus-infected pokemon starts to grow or evolve at a quicker rate, and that is advantageous for the game process. To achieve that, when a pokemon is qualified for level-up in the normal game processing, a level-up value to be added for one specification varies depending on whether the pokemon has been virus infected. As another example of providing the virus-infected pokemon with some ability advantageous in the course of the game, depending on the virus type, the pokemon may suffer less damage when attacked by an opponent (or its defense power is increased) or its attack power is increased.
Next, by referring to FIG. 12 , the virus elimination processing subroutine in step S 6 ( FIG. 9 ) having the virus eliminated (removed) after the virus-infected endurance time has passed is described in detail. In step S 41 , a variable n is set to 1 for storage in a register region (not shown) on the RAM 25 .
In step S 42 , the on-hand pokemon storage region 12 B is selected for the pokemon number assigned to the 1 st pokemon, which is equivalent to the variable n (1 at the beginning). Thereafter, the area 12 c of the captured pokemon data region 12 A whether there is any virus data under the 1st pokemon's pokemon number is determined. If no virus data is stored, the procedure goes to step S 43 .
In step S 43 , it is determined whether the variable n is 6. If not n 6, the procedure goes to step S 44 .
In step S 44 , n is incremented by 1, and the procedure returns to step S 42 . In step S 42 , the area 12 c of the captured pokemon data region 12 A whether there is any virus data under the 2nd pokemon's pokemon number is determined. If stored, the procedure goes to step S 45 .
In step S 45 , the virus-infected period count value (Cn) is decreased by a predetermined value ( ) (Cn Cn ). As already described in step S 26 (FIG. 11 ), the virus-infected period count value Cn indicates how long the pokemon specified by the pokemon number designated by the variable n has been virus infected. The predetermined value corresponds to a length of time taken to repeat the processing in step S 45 . As an example, assuming that the virus-infected period count value Cn is exactly 48 hours and the processing in step S 45 is repeated every second, the virus-infected period count value Cn is decreased by a second on the basis of 1 second.
In step S 46 , it is determined whether the virus-infected period count value Cn became 0 or smaller, and if not 0, the procedure goes to step S 43 . In step S 43 , it is determined whether the variable n is 6. If not n 6, n is incremented by 1 in step S 44 , and the procedure returns to step S 42 .
As such, by repeating a series of operation including steps S 42 , S 43 , and S 44 , or a series of operation including steps S 42 , S 45 , S 46 , S 43 , and S 44 , each of the six pokemons is successively subjected to virus infection determination processing and processing of decreasing the virus infected time. When the variable n becomes 6 in step S 43 , each of the six pokemons is determined as being subjected to virus infection determination processing and decreasing the virus infected time processing, and the procedure then goes to step S 7 .
When the virus-infected period count value Cn is determined as being 0 or smaller in step S 46 , the area 12 c of the captured pokemon data region 12 A on the RAM 25 is cleared of virus data for the pokemon number specified by the variable n. In other words, data indicating no virus infection is written thereto. Thereafter, in step S 43 , it is determined whether the variable n is 6, and if not n 6, n is incremented by 1 in step S 44 . The procedure then returns to step S 42 . The operation of steps S 45 , S 46 , S 43 , and S 44 or the operation of steps S 45 , S 46 , S 47 , and S 43 is repeated until each of the six pokemons is subjected to the virus elimination processing. The procedure then goes to step S 7 .
The operation of steps S 45 and S 46 may be alternatively done as follows. Assuming that a count value C 1 indicates a time when the virus loses its power instead of the virus-infected period count value Cn and indicates a length of time after virus infection, determination is made in one step whether C 1 is 0 or smaller.
A player who captures a virus-infected pokemon is free to lend it to another player within the virus-infected endurance time and get it back after the other player's pokemon is virus-infected. Since the virus-infected pokemon is superior in ability compared with the non-virus infected, many players are eager to let their pokemons become virus infected. Accordingly, the player who luckily captures a virus-infected pokemon with a considerably low probability becomes busy with other players' requests for pokemon data exchange, thereby increasing popularity among other players. As such, the game is useful for cultivating friendship with other players.
Next, by referring to FIG. 13 , the online battle game processing subroutine in step S 7 is described in detail. For the online battle game, two game machines 20 are connected to each other through the cable 40 , and each player selects the online battle mode on the mode selection screen.
In response thereto, in step S 51 , it is determined whether the place where the main character stands is a battle ground. If determined yes, the procedure goes to step S 52 .
In step S 52 , it is determined whether those two game machines 20 connected through the cable 40 are under normal link condition. If yes, the procedure goes to step S 53 .
If the place where the main character stands is determined as not the battle ground in step S 51 (No), or if the link condition is determined as not normal in step S 52 (No), the procedure skips the operation of later-described steps S 53 to S 57 , and goes to step S 8 of the main routine shown in FIG. 9 .
In the online battle mode (Yes both in steps S 51 and S 52 ), the ID data is transmitted to and from the rival player's game machine 20 through the communications cable in step S 53 .
In step S 54 , the rival player's ID data is stored in the player's battle character data area of the battle data storage region 12 C on the RAM 25 .
In step S 55 , the rival player's pokemon data for six pokemons is read.
In step S 56 , the pokemon data for six pokemons is stored in the battle pokemon data area of the battle data storage region 12 C on the RAM 25 .
In step S 57 , the online battle processing is carried out. The procedure then goes to step S 8 of the main routine.
So far, the system in which two game machines 20 are connected through the cable 40 is exemplarily described. As an alternative to the cable 40 , as exemplarily shown in FIG. 6 , those two game machines 20 can certainly be connected through the infrared transmitter/receivers 16 .
Next, by referring to FIG. 14 for the mysterious gift processing subroutine S 8 , how the mysterious gift (helping item) is presented based on other player's ID code obtained through communications is described. Prior to starting the gift mode, two players place their game machines 20 so that the infrared transmitter/receivers 31 or the infrared transmitter/receivers 16 of the cartridge 10 are opposed to each other, establishing infrared communications. Next, both players select a mode of presenting the mysterious gift through ID data communication or exchange between the game machines 20 on the above-described mode selection screen. In response thereto, the gift processing subroutine shown in FIG. 14 is started.
That is, in step S 61 , it is determined whether the gift mode is selected. If yes, the procedure goes to step S 62 .
In step S 62 , it is determined whether the date is changed. If yes, new date is written into a new data storage area 12 i on the RAM 25 in step S 63 .
In step S 64 , the rival players ID data in the area 12 g is cleared. In step S 65 , a register L (not shown, but included in the area 12 i ) is cleared for the number of players with whom ID communications or exchange is performed for the day (or 0 is written).
In step S 66 , it is determined whether the register L indicates 5 or smaller. Such determinations made in steps S 62 and S 66 are for keeping the upper limit allowed for presenting gift (or ID data communications) is 5 players in a day.
In step S 67 , it is determined whether the link for communications using the infrared transmitter/receiver is normally secured. If secured, the player's (his/her own) ID data is transmitted in step S 68 .
In step S 69 , the ID data (IDn) transmitted from the other player is received, and is written into the miscellaneous area 12 g.
In step S 70 , whether the received ID data (IDn) is identical to the ID data (IDn) already stored in the area 12 g is determined. If identical, the gift processing is terminated (returned) and the procedure goes to step S 9 . This is because the ID data exchange is allowed only once for the same player in a day. On the other hand, if determined as not identical the value of the register L is incremented by 1 in step S 71 , and the number of players with whom ID data has been exchanged for the day is counted.
Furthermore, in the following steps S 72 to S 85 , processing provides rare items or items beneficial in the course of the game based on the ID data (IDn).
In detail, a random number R 3 is generated in step S 72 . The random number generated in this step and those R 4 and R 5 generated in steps S 75 and S 78 are all in the range of 0 to 255.
In step S 73 , it is determined whether the random number R 3 is 50 or larger, and if determined as being 50 or larger, a most-common item group (group in the first column in FIG. 15 ) is selected. Herein, a probability for the random number being 50 or larger at the first stage is 205/255 bout , and accordingly the most-common item group is selected.
If the random number R 3 is determined as being 50 or smaller in step S 73 , the probability for such random number R 3 is about . Therefore, as the procedure goes through step S 76 and then S 79 , the probability will be multiplied by every time the procedure reaches a stage of generating a random number (steps S 75 , 78 , S 82 ), and a rarer item is provided as the probability of such a number is decreased.
For this purpose, the random number R 4 is generated in step S 75 . In step S 76 , it is then determined whether the random number R 4 is 50 or larger, and if yes, a popular item group (group in the second column in FIG. 15 ) is selected.
If the random number R 4 is 50 or smaller, the random number R 5 is generated in step S 78 .
In step S 79 , it is determined whether the random number R 5 is 50 or larger, and if yes, a least-common item group (group in the third column in FIG. 15 ) is selected.
If the random number R 5 is 50 or smaller, a rare item group (group in the last column in FIG. 15 ) is selected in step S 81 .
In such manner, among the item groups classified according to the probability of random numbers R 3 , R 4 , and R 5 in steps S 74 , S 77 , S 80 , and S 81 , an item to be presented based on the ID data (IDn) is determined through the later-described processing.
Furthermore, a random number R 6 is generated in step S 82 . The random number R 6 is data varied in type, and is assigned 8 numbers from 0 to 7. The random number is selected with a probability of .
In step S 83 , the area 12 g is referred to for the other player's ID data (IDn) having ID data communications or exchange with, and based on the lower 8-bit data of the ID data, a variable D is determined. Specifically, out of the lower 8-bit of the ID data IDn, the value arranged in the numerical order specified by the random number R 6 is set to the variable D. In FIG. 14 , an expression is found as the random number R 6 -th lower bit of D IDn.
In step S 84 , the variable D and the random number R 6 as a part of the ID data (IDn) are computed with a predetermined equation (e.g., C R 6 2 D) so as to obtain an item number C.
In step S 85 , item data corresponding to the determined item number C is written into the item storage area 12 h for storage. At the same time, an object and/or symbol of the item is displayed on the liquid crystal display 27 to let the player know what item is presented. Such items to be presented based on the communicated or exchanged ID data are shown in the right table in FIG. 15 , and are preferably impossible or difficult to obtain through the normal game play.
Furthermore, in order to not always present the same item to one ID data (IDn), the item type may be programmed to be based on data. Such data is obtained by dividing the ID data (IDn) into a plurality of bytes and inverting bit data in a byte specified by the random number, or bit-shifting the ID data for the number of times of the random number. Additionally, in order to determine the item type to be presented through ID data exchange with the other player, the ID data does not have to be correlated with the random number as described above, but may be independently used to determine the item type.
As described in the foregoing, by making the items beneficial in the course of the game (helping data or items) available through the ID data communications or exchange with other players, the players become very enthusiastic about communicating/exchanging ID data with other players to find the rare items. Thus, communications and exchange become active. As a result, the players become communicative and enjoy the company of others by sharing the same interest in the game. Even unsocial kids become more social through discussion about the game.
Furthermore, since both of the ID data and random numbers are determination factors for item type, one ID data may not lead to the same item even if the player exchanges ID data with the same player on another day. Therefore, the players may not easily bore, and thus can play the game over and over for a long time.
So far, the system in which two game machines 20 are connected utilizing the infrared transmitter/receiver 16 is exemplarily described. As an alternative to the infrared transmitter/receiver 16 , as exemplarily shown in FIG. 5 , those two game machines 20 can certainly be connected through the cable 40 .
Next, by referring to FIG. 16 , a case where the step-number data is received through infrared communications from the pedometer-incorporated game machine 50 is described. In the step-number communications mode, the player walks with the pedometer for the purpose of taking steps as many as possible, and he or she presents the number of steps to the main character or pokemons in the game. In this manner, the player can enjoy a mode not available by playing the game only with the game cartridge 10 A. That is, the game available from the cartridge 10 A is diversified to a further extent by being connected with the game machine different in type, and keeps stimulating the players to challenge the game.
Prior to starting the step-number data communications mode, as exemplarily shown in FIG. 7 , the player places the infrared transmitter/receiver 51 of the pedometer-incorporated game machine 50 in such manner as to be opposed to the infrared transmitter/receiver 31 internally-provided in the game machine 20 or the infrared transmitter/receiver 16 provided to the cartridge 10 A, and establishes an environment for infrared Communications. Thereafter, the player selects the step-number data communications mode on the above-described mode selection screen (step S 1 ). In response thereto, the pedometer communications subroutine in step S 9 is started. Hereinafter, the operation thereof is described in detail with reference to FIG. 16 .
In step S 91 , it is determined whether the pedometer communication mode is selected.
In step S 92 , it is determined whether the infrared transmitter/receivers 31 and 51 are securely linked, and if securely linked, the procedure goes to step S 93 .
In step S 93 , the area 12 i on the RAM 25 is provided, for storage, with step-number data W (or data relevant to the step number obtained by dividing the step-number data by a predetermined step number) transmitted from the pedometer-incorporated game machine 50 .
In step S 94 , based on the equation shown in the table of FIG. 17 , the item type is determined for the step-number data W.
In step S 95 , the item data is stored in the area 12 h on the RAM 25 . In this case, the larger the value of the step-number data W becomes, the more rare the item type in the normal game play is presented according to the step-number data. Accordingly, the player will not remain stationary while playing the game, rather is encouraged to exercise, e.g., walk as a part of the game.
During or at the end of the game, a command save data is displayed, and if selected, the CPU 23 transfers the data stored in the storage regions 12 A to 12 E on the RAM 25 in the game machine 20 to the RAM 12 for writing. In this manner, the RAM 12 is provided with the data relevant to the game process, and the data is backed up exemplarily by battery (not shown) for the next play.
In step S 91 , on the other hand, if determined that the communications mode with the pedometer-incorporated game machine 50 is not selected, the steps S 92 to S 95 are skipped to terminate this subroutine (S 9 ). The procedure then returns to the player object processing subroutine in step S 2 .
By referring to the table in FIG. 17 , it is now briefly described how the item type presented relevant to the step-number data W is determined.
First, when the step-number data W is smaller than a predetermined value b 1 , an item b 1 is presented. When the step-number data W is larger than the predetermined value b 1 but smaller than a predetermined value b 2 , an item b 2 is presented. When the step-number data W is larger than the predetermined value b 2 but smaller than a predetermined value b 3 , an item b 3 is presented. When the step-number data W is larger than the predetermined value b 3 but smaller than a predetermined value b 4 , an item b 4 is presented. And when the step-number data W is larger than the predetermined value b 4 , an item b 5 is presented. Although a predetermined value bN (arbitrary integer) is set to b 1 to b 4 in this embodiment, the range for the value may be increased or decreased as required, or the predetermined value bN may be arbitrarily set. In such a case, the game becomes more interesting.
Note that the description in the foregoing is made for a roll playing game exemplarily played for capturing and training pokemons. However, the present invention is technically applicable to other type of games such as action game or sports game. If this is the case, the item type to be presented based on the ID data and/or the step-number data is changed according to the type of the game.
Further, according to the type of the game, pokemons' virus infection may be altered to disease contagious to person or animal favorable for the game process if infected, and such favorableness is also appropriately altered.
Still further, in the above-described embodiment, although the image-display game device is exemplarily implemented by the portable game machine and a corresponding game cartridge, a video game machine connected to a television receiver will also do. In such case, the information storage medium may be implemented by a game cartridge, optical storage medium such as CD-ROM or DVD, or magnetic disk.
While the invention has been described in detail, the foregoing description is in all aspects illustrative and not restrictive. It is understood that numerous other modifications and variations can be devised without departing from the scope of the invention.
Claims
- A method of operating a multiplayer video game system for playing a video game involving characters that may be captured by a player comprising the steps of: establishing communication between a first player's video game device and a second player's video game device;associating time related data with at least a first video game character that may be captured by a player;controlling the display of said first video game character based upon said time related data;receiving by said first player's video game device identification information identifying said second player;and storing data in said first player's video game device relating to said at least one video game character associated with said second player including said time related data.
- A method according to claim 1 , further including the step of storing property data associated with a character that may be captured during the course of said video game including help data for helping the player during video game play.
- A method according to claim 1 , further including the step of changing the stored property data in response to user actuation of at least one control member associated with said first player's video game device.
- A method according to claim 1 , wherein said step of controlling the display of said first video game character based upon said time related data includes the steps of determining whether a predetermined length of time has passed, and prohibiting the generation of help data until said predetermined length of time has passed.
- A method according to claim 1 , wherein said step of establishing communication includes the step of communicating via an infrared transmitter/receiver.
- A method according to claim 1 , further including the step of capturing a plurality of characters, each character associated with a distinct habitat.
- A method according to claim 1 , further including the step of controlling the display of at least one character that may be captured by a player such that said character is displayed only when said time related data has a predetermined relationship with the current time.
- A method according to claim 7 , further including the step of controlling the display of said at least one character such that the probability of display begins to increase as of a predetermined time of day.
- A method according to claim 1 , further including the step of associating virus related data with a character.
- A method according to claim 9 , further including the step of increasing the rate of assigning game scoring related values with characters that are virus infected.
- A method according to claim 1 , wherein said step of storing data in said first player's video game device includes the step of storing a rival player's ID data in a battle character data area of memory.
- A method according to claim 1 , wherein the step of storing data in said first player's video game device includes the step of storing data relating to a plurality of characters in a battle area of memory.
- A method of operating a multiplayer video game for playing a video game involving characters that may be captured by a player comprising the steps of: establishing communication between a first player's video game device having an associated program for storing a first game program for playing a game involving characters that may be captured by the player;and at least a second player's removable memory for storing a second video game program involving characters that may be captured by the second player;wherein said first program includes at least one function that is not available in accordance with the second game program, transferring data relating to a captured character from the second player to said first player;and processing the captured character data received from the second player to create data relating to a function not available in accordance with said second game program.
- A method according to claim 13 , wherein said second game program does not process data relating to the sex of the character;and further including the step of processing the data received from the second player's removable memory such that sex data is generated based upon data received from said second removable memory.
- A method according to claim 13 , further including the steps of associating time related data with at least a first video game character that may be captured by a player;and controlling the display of said first video game character based upon said time related data.
- A method according to claim 15 , further including the step of storing data in said first player's video game device relating to said at least one video game character associated with said second player including said time related data.
- A method according to claim 15 , wherein the step of controlling the display of a first video game character based upon said time related data includes the steps of determining whether a predetermined length of time has passed, and prohibiting the generation of data for helping a player during game play until said predetermined length of time has passed.
- A method according to claim 15 , further including the step of controlling the display of at least one character that may be captured by a player such that said character is displayed only when said time related data has a predetermined relationship with the current time.
- A method according to claim 13 , further including the step of receiving by said first player's video game device identification information identifying said second player.
- A method according to claim 13 , further including the step of storing property data associated with a character that may be captured during the course of said video game including help data for helping the player during video game play.
- A method according to claim 13 , further including the step of changing the stored data relating to a captured character in response to user actuation of at least one control member associated with said first player's video game device.
- A method according to claim 13 , wherein said step of establishing communication includes the step of communicating via an infrared transmitter/receiver.
- A method according to claim 13 , further including the step of capturing a plurality of characters, each character associated with a distinct habitat.
- A method according to claim 13 , further including the steps of associating time of day data with a character and controlling the display of said at least one character such that the probability of display begins to increase as of a predetermined time of day.
- A method according to claim 13 , further including the step of associating virus related data with a character.
- A method according to claim 25 , further including the step of increasing the rate of assigning game scoring related values with characters that are virus infected.
- A method according to claim 13 , wherein said step of transferring data includes the step of storing a rival player's ID data in a battle character data area of memory.
- A method according to claim 13 , wherein the step of transferring data includes the step of storing data relating to a plurality of characters in a battle area of memory.
Disclaimer: Data collected from the USPTO and may be malformed, incomplete, and/or otherwise inaccurate.