U.S. Pat. No. 12,299,758
SECURE MATCHMAKING, ASSET TRANSFER, AND USABILITY RECONFIGURATION PLATFORM
AssigneeSony Interactive Entertainment LLC
Issue DateMay 31, 2022
Illustrative Figure
Abstract
Systems and methods for authorization reconfiguration for digital asset usability are described. An asset management system identifies an asset associated with a video game. A first user device is authorized to use the asset. The first user device is associated with a first user. The asset management system identifies a second user, for instance through a shared characteristic with the first user. A second user device associated with the second user lacks authorization to use the asset. The asset management system receives an indication of a transfer of usability of the asset, such as an indication that the second user has paid for the transfer, or that the conditions of a smart contract have been met. In response to receiving the indication, the asset management system automatically disables authorization for the first user device to use the asset and enables authorization for the second user device to use the asset.
Description
DETAILED DESCRIPTION The detailed description set forth below is intended as a description of various configurations of the subject technology and is not intended to represent the only configurations in which the technology can be practiced. The appended drawings are incorporated herein and constitute a part of the detailed description. The detailed description includes specific details for the purpose of providing a more thorough understanding of the technology. However, it will be clear and apparent that the technology is not limited to the specific details set forth herein and may be practiced without these details. In some instances, structures and components are shown in block diagram form in order to avoid obscuring the concepts of the subject technology. Techniques and technologies are described for creating, modifying, tracking, authenticating, and/or transferring usability of digital assets associated with video game(s). In some examples, an asset management system identifies an asset associated with a video game, such as an instance of the video game itself, or some in-game content (e.g., downloadable content (DLC), in-app purchases (IAP), characters, items, environments, save files, gameplay recordings, and the like). In some examples, the asset includes a non-fungible token (NFT) associated with the video game. A first user device is authorized to use the asset. For instance, if the asset is an instance of the video game, the first user device is authorized to launch and/or play the video game on the first user device. If the asset is in-game content for the video game, the first user device is authorized to use in-game content within the video game as the video game is played on the first user device. The first user device is associated with a first user. The asset management system identifies a second user. In some examples, the asset management system identifies the ...
DETAILED DESCRIPTION
The detailed description set forth below is intended as a description of various configurations of the subject technology and is not intended to represent the only configurations in which the technology can be practiced. The appended drawings are incorporated herein and constitute a part of the detailed description. The detailed description includes specific details for the purpose of providing a more thorough understanding of the technology. However, it will be clear and apparent that the technology is not limited to the specific details set forth herein and may be practiced without these details. In some instances, structures and components are shown in block diagram form in order to avoid obscuring the concepts of the subject technology.
Techniques and technologies are described for creating, modifying, tracking, authenticating, and/or transferring usability of digital assets associated with video game(s). In some examples, an asset management system identifies an asset associated with a video game, such as an instance of the video game itself, or some in-game content (e.g., downloadable content (DLC), in-app purchases (IAP), characters, items, environments, save files, gameplay recordings, and the like). In some examples, the asset includes a non-fungible token (NFT) associated with the video game. A first user device is authorized to use the asset. For instance, if the asset is an instance of the video game, the first user device is authorized to launch and/or play the video game on the first user device. If the asset is in-game content for the video game, the first user device is authorized to use in-game content within the video game as the video game is played on the first user device. The first user device is associated with a first user. The asset management system identifies a second user. In some examples, the asset management system identifies the second user during a matchmaking process, for instance based on one or more shared characteristics with the first user (e.g., same favorite game, same most-played game, same region, same age group, or some combination thereof). A second user device associated with the second user lacks authorization to use the asset. The asset management system receives an indication of a transfer of usability of the asset. For instance, the indication of the transfer of usability can include an indication that the second user has paid for the transfer, that the second user has agreed to pay for the transfer, that the transfer was authorized by another user (e.g., a parent or guardian of the first user or of the second user), that the conditions of a smart contract have been met, or a combination thereof. In response to receiving the indication, the asset management system automatically disables authorization for the first user device to use the asset, and automatically enables authorization for the second user device to use the asset, thereby effecting the transfer of usability of the asset. Thus, after the transfer of usability of the asset, the second user device is authorized to use the asset, and the first user device is no longer authorized to use the asset. In some examples, the asset management system also causes a second transfer to also take effect in parallel with, or before, or after, the transfer of usability of the asset. The second transfer can include, for instance, a transfer of a second asset (e.g., funds, content associated with the same video game, content associated with a different video game) from the second user to the first user, from the second user to the asset management system, from the asset management system to the first user, or a combination thereof.
In some examples, the asset may be an instance of the video game. In some examples, the asset may be in-game content, such as in-game items, characters, environments (e.g., levels, stages, worlds), objectives, save files, DLC, IAP, or combinations thereof. The asset may be video game digital media asset with media representations of moments of gameplay of a video game, such as video clips, images, and/or audio clips. In some examples, a distributed ledger tracking a history of the asset is created and stored across a plurality of devices of a distributed system. In some examples, a unique token (e.g., an NFT) may be generated for the asset, with a unique identifier for the asset and metadata identifying properties of the asset. The transfer of usability of the asset can include a transfer of ownership, a transfer of a license, a rental, a lease, a demo, or a combination thereof. In some examples, the asset management system can update a distributed ledger, such as a blockchain ledger or a direct acyclic graph (DAG) ledger, with an indication of the transfer of the usability of the asset, for instance in a new block that is appended to the distributed ledger. The new block can include one or more hashes of at least portions of one or more previous blocks in the distributed ledger.
The techniques and technologies described herein expand the capabilities of systems that manage usability of digital assets associated with video games by providing a process through which such systems to transfer usability of such digital assets, for instance by disabling usability of an asset at one user device and enabling usability of the asset at another user device in response to a trigger condition. The techniques and technologies described herein represent a safe and secure platform to effect such transfers of usability of assets, for instance by using smart contracts to securely effect such transfers, distributed ledgers to securely track such transfers, non-fungible tokens (NFTs) to convert assets from fungible to non-fungible, and/or authentication from a third user (e.g., parent and/or guardian) for such transfers. The techniques and technologies described herein allow for secure and comprehensive tracking of the history of a digital asset, for instance tracking when, how, and by whom the digital asset was created, used, modified, rented to, rented by, sold to, purchased by, licensed to, licensed by, exchanged to, exchanged by, transferred to, transferred by, and/or other actions.
FIG.1illustrates an example network environment100in which a system for tracking a digital asset associated with a video game using a distributed ledger may be implemented, according to an aspect of the present disclosure. The network environment100may include one or more interactive content servers110that provide streaming content (e.g., interactive video, podcasts, video game content, etc.), one or more platform servers120, one or more user devices130, one or more data structures140, one or more distributed ledgers150. The one or more distributed ledgers150can be stored across a distributed network115, which can include the one or more interactive content servers110, the one or more platform servers120, the one or more user devices130, the one or more data structures140, or a combination thereof.
Interactive content servers110may maintain, stream, and host interactive media available to stream on a user device130over a communication network. Such interactive content servers110may be implemented in the cloud (e.g., one or more cloud servers). Each media may include one or more sets of object data that may be available for participation with (e.g., viewing or interacting with an activity) by a user. Data about the object shown in the media may be stored by the interactive content servers110, platform servers120and/or the user device130, in an object file216(“object file”).
The platform servers120may be responsible for communicating with the different interactive content servers110, data structures140, and user devices130. Such platform servers120may be implemented on one or more cloud servers. The interactive content servers110may communicate with multiple platform servers120, though the media interactive content servers110may be implemented on one or more platform servers120. The platform servers120may also carry out instructions, for example, receiving a user request from a user to stream streaming media (i.e., video games, activities, video, podcasts, User Generated Content (“UGC”), publisher content, etc.). The platform servers120may further carry out instructions, for example, for streaming the streaming media content titles. Such streaming media may have at least one object set associated with at least a portion of the streaming media. Each set of object data may have data about an object (e.g., activity information, zone information, actor information, mechanic information, game media information, etc.) displayed during at least a portion of the streaming media.
The streaming media and the associated at least one set of object data may be provided through an application programming interface (API)160, which allows various types of interactive content servers110to communicate with different platform servers120and different user devices130. API160may be specific to the particular computer programming language, operating system, protocols, etc., of the interactive content servers110providing the streaming media content titles, the platform servers120providing the media and the associated at least one set of object data, and user devices130receiving the same. In a network environment100that includes multiple different types of interactive content servers110(or platform servers120or user devices130), there may likewise be a corresponding number of APIs160.
The user device130may include a plurality of different types of computing devices. For example, the user device130may include any number of different gaming consoles, mobile devices, laptops, and desktops. In another example, the user device130may be implemented in the cloud (e.g., one or more cloud servers). Such user device130may also be configured to access data from other storage media, such as, but not limited to memory cards or disk drives as may be appropriate in the case of downloaded services. Such devices130may include standard hardware computing components such as, but not limited to network and media interfaces, non-transitory computer-readable storage (memory), and processors for executing instructions that may be stored in memory. These user devices130may also run using a variety of different operating systems (e.g., iOS, Android), applications or computing languages (e.g., C++, JavaScript). An example user device130is described in detail herein with respect toFIG.13.
The data structures140can include, for example, one or more databases (DBs), one or more distributed hash tables (DHTs), one or more interplanetary file systems (IPFSs), one or more interplanetary linked data (IPLD) structures, one or more tables, one or more hash tables, one or more heaps, one or more trees, one or more lists, one or more arrays, one or more arraylists, one or more dictionaries, one or more matrices, or a combination thereof. The data structures140may be stored on the platform server120, the interactive content servers110, any of the servers218(shown inFIG.2A), across one or more different servers, on a single server, across different servers, on any of the user devices130, within the distributed ledgers150, on devices identified by network locations identified by pointers (e.g., uniform resource identifiers) stored in the distributed ledgers150, or a combination thereof. Such data structures140may store digital assets associated with video games, such as the streaming media, portions thereof, and/or associated set(s) of object data. Such streaming media may depict one or more objects (e.g., activities) that a user can participate in and/or UGC (e.g., screen shots, videos, commentary, mashups, etc.) created by peers, publishers of the media content titles and/or third party publishers. Portions of the streaming media may include images, video clips, audio clips, or combinations thereof. Such UGC may include metadata by which to search for such UGC. Such UGC may also include information about the media and/or peer. Such peer information may be derived from data gathered during peer interaction with an object of an interactive content title (e.g., a video game, interactive book, etc.) and may be “bound” to and stored with the UGC. Such binding enhances UGC as the UGC may deep link (e.g., directly launch) to an object, may provide for information about an object and/or a peer of the UGC, and/or may allow a user to interact with the UGC. One or more user profiles may also be stored in the data structures140. Each user profile may include information about the user (e.g., user progress in an activity and/or media content title, user id, user game characters, etc.) and may be associated to media.
In some examples, an object and/or an object file216is an example of a digital asset associated with a video game that is tracked using one or more of the distributed ledgers150. In some examples, a portion of media, such as a video clip or image or audio clip of one or more moments of gameplay, is an example of a digital asset associated with a video game that is tracked using one or more of the distributed ledgers150. The portion of media may be generated, recorded, and/or streamed using the interactive content servers110, platform servers120, and/or the user device130.
In some examples, the distributed ledger150may be public. In some examples, the distributed ledger150may be private. In some examples, the distributed ledger150may be partly public and partly private. In some examples, the distributed ledgers150can be controlled by, and restricted to, use for a single video game. In some examples, the distributed ledgers150can be controlled by, and restricted to, use for a set of video games, such as a particular series of video games. In some examples, the distributed ledgers150can be controlled by, and restricted to, use for a single video game console or video game platform. In some examples, the distributed ledgers150can be controlled by, and restricted to, use for a set of video game consoles or video game platforms. In some examples, the set of video game consoles or video game platforms can be associated with a single manufacturer, device type, form factor, operating system (OS), or combination thereof. For instance, the distributed ledgers150can be controlled by, and restricted to, use for one or more Sony® platforms and/or one or more Sony® PlayStation® platforms corresponding to one or more types of Sony® devices, such as the Sony® PlayStation® 4, the Sony® PlayStation® 5, the Sony® PlayStation® Vita®, another Sony® PlayStation® portable gaming console, another Sony® PlayStation® home gaming console, a Sony® PlayStationVR® Virtual Reality (VR) system, a Sony® PlayStationTV® home entertainment system, a Sony® tablet, a Sony® mobile handset, or a combination thereof. In some examples, the set of video game consoles or video game platforms can include video game consoles or video game platforms that are associated with more than one manufacturer, device type, form factor, operating system (OS), or combination thereof, for example allowing cross-platform support, cross-device-type support, cross-OS support, or a combination thereof. The blockchain ledger300is an example of the distributed ledgers150.
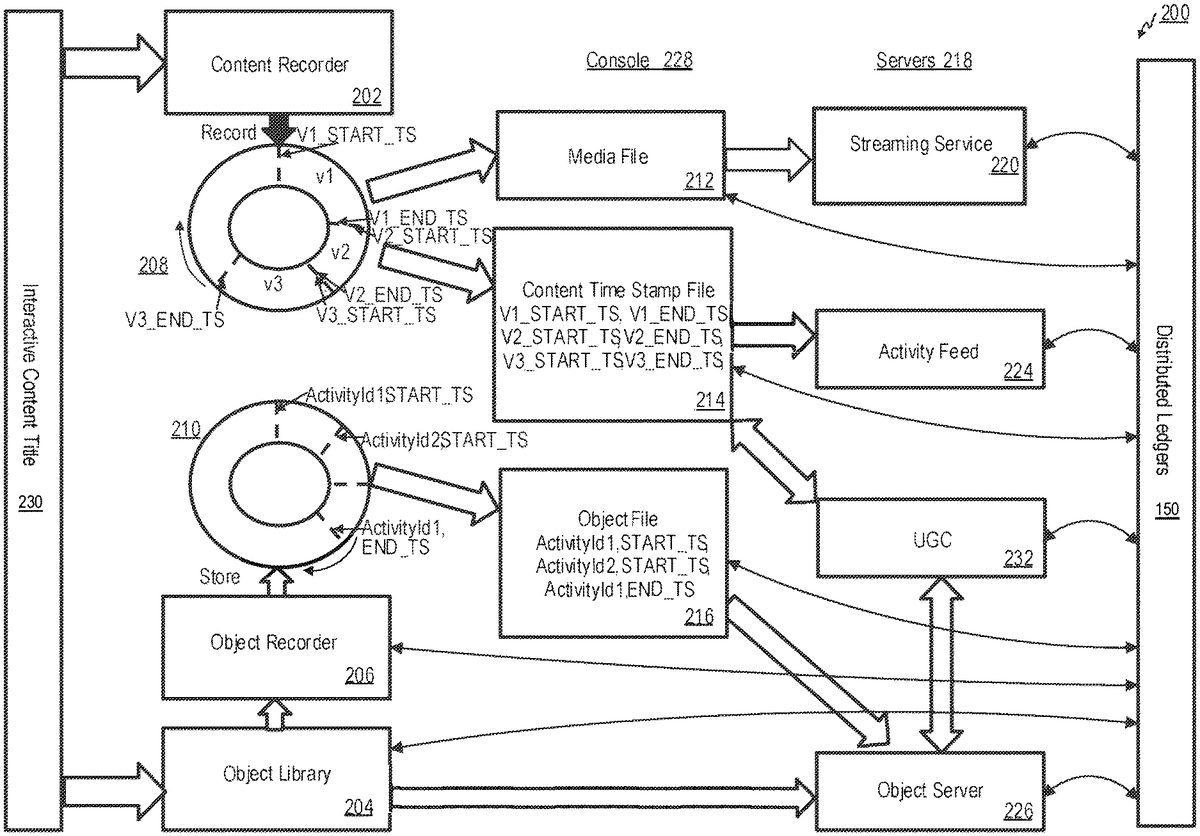
FIG.2Ais a block diagram illustrating an example network environment200in which a system for binding object data from a universal data system to media content may be implemented, according to an aspect of the present disclosure. In the example network environment200ofFIG.2A, an example console228(e.g., a user device130) and example servers218(e.g., streaming server220, activity feed server224, UGC server232, and an object server226) are shown. The console228may be implemented on the platform server120, a cloud server, or on any of the servers218. The console228may further includes a content recorder202and an object recorder210, described in more detail below, where content (e.g., media) may be recorded and/or output through the console228. The interactive various content titles230may be executed on the console228. Alternatively or in addition to, the content recorder202may be implemented on the platform server120, a cloud server, or on any of the servers218. Such content recorder202may receive and record content (e.g., media) from an interactive content title230(e.g., interactive content source servers110) onto a content ring-buffer208. Such ring-buffer208may store multiple content segments (e.g., v1, v2 and v3), start times for each segment (e.g., V1_START_TS, V2_START_TS, V3_START_TS), and end times for each segment (e.g., V1_END_TS, V2_END_TS, V3_END_TS). Such segments may be stored as a media file212(e.g., MP4, WebM, etc.) by the console228. Such media file212(e.g., a portion of the streaming media) may be uploaded to the streaming server220for storage and subsequent streaming or use, though the media file212may be stored on any server, a cloud server, any console228, or any user device130. The media file212may be uploaded periodically and/or in real-time or close to real-time. Such start times and end times for each segment may be stored as a content time stamp file214by the console228. Such content time stamp file214may also include a streaming ID, which matches a streaming ID of the media file212, thereby associating the content time stamp file214to the media file212. Such content time stamp file214may be uploaded and stored to the activity feed server224and/or the UGC server232, though the content time stamp file214may be stored on any server, a cloud server, any console228, or any user device130.
In some examples, the media file212may be converted, by the console228and/or by the servers218, into a non-fungible video game digital media asset using a non-fungible token, such as the token400ofFIG.4, that is stored in and whose history is tracked across one or more of the distributed ledgers150. The token corresponding to the media file212may include metadata associated with the streaming service220, the content time stamp file214, the activity feed224, the UGC server232, and/or the object server226. In some examples, at least some of the actions or activities identified in the activity feed224and/or the content time stamp file214can be identified in the history of the non-fungible video game digital media asset tracked in the distributed ledgers150.
Concurrent to the content recorder202receiving and recording content from the interactive content title230, an object library204receives object data from the interactive content title230, and an object recorder206tracks the object data to determine when an object beings and ends. Such object data may be uploaded periodically and/or in real-time or close to real-time. The object library204and the object recorder206may be implemented on the platform server120, a cloud server, or on any of the servers218. When the object recorder206detects an object beginning, the object recorder206receives object data (e.g., if the object were an activity, user interaction with the activity, activity ID, activity start times, activity end times, activity results, activity types, etc.) from the object library204and records the activity data onto an object ring-buffer210(e.g., ActivityID1, START_TS; ActivityID2, START_TS; ActivityID3, START_TS). Such activity data recorded onto the object ring-buffer210may be stored in an object file216. Such object file216may also include activity start times, activity end times, an activity ID, activity results, activity types (e.g., competitive match, quest, task, etc.), user or peer data related to the activity. For example, an object file216may store data regarding an item used during the activity. Such object file216may be stored on the object server226, though the object file216may be stored on any server, a cloud server, any console228, or any user device130.
Such object data (e.g., the object file216) may be associated with the content data (e.g., the media file212and/or the content time stamp file214). In one example, the object server226stores and associates the content time stamp file214with the object file216based on a match between the streaming ID of the content time stamp file214and a corresponding activity ID of the object file216. In another example, the object server226may store the object file216and may receive a query from the UGC server232for the object file216. Such query may be executed by searching for an activity ID of the object file216that matches a streaming ID of a content time stamp file214transmitted with the query. In yet another example, a query of stored content time stamp files214may be executed by matching a start time and end time of a content time stamp file214with a start time and end time of a corresponding object file216transmitted with the query. Such object file216may also be associated with the matched content time stamp file214by the UGC server232, though the association may be performed by any server, a cloud server, any console228, or any user device130. In another example, an object file216and a content time stamp file214may be associated by the console228during creation of each file214,216.
In some examples, an object identified by the object library204, by the object recorder206, by the object ring-buffer210, by the object file216, and/or by the object server226may be converted, by the console228and/or by the servers218, into a non-fungible in-game digital asset using a non-fungible token, such as the token400ofFIG.4, that is stored in and whose history is tracked across one or more of the distributed ledgers150. The token corresponding to the media file212may include metadata associated with the object recorder206, the object ring-buffer210, the object file216, the object server226, the UGC server232, the streaming service220, the content time stamp file214, and/or the activity feed224. In some examples, at least some of the actions or activities identified in the activity feed224, the content time stamp file214, and/or the object file216can be identified in the history of the non-fungible in-game digital asset tracked in the distributed ledgers150.
FIG.2Bis a conceptual diagram illustrating an example table of various objects and associated events, according to an aspect of the present disclosure. As shown in the example table250ofFIG.2B, such object data (e.g., the object file216) may be associated with event information regarding activity availability change and may be related to other objects with associated object information. Media-object bindings may form telemetry between the objects shown in at least a portion of the streaming media and the streaming media. For example, such object data may be activity data files251, zone data files252, actor data files254, mechanics data files256, game media data files258, and other gameplay-related data files.
Such activity data files251(e.g., the object file216) may be categorized as in in progress, open-ended, or competitive. Such activity data files251may include optional properties, such as a longer description of the activity, an image associated with the activity, if the activity is available to players before launching the game, whether completion of the activity is required to complete the game, whether the activity can be played repeatedly in the game, and whether there are nested tasks or associated child activities. Such activity data files251may include an activity availability change event for, which may indicate a list or array of currently available activities for the player. For example, this may be used to decide what activities to display in a game plan.
Such zone data files252may indicate an area of an associated game world with a single coordinate system wherein the zone may have a 2-D map associated with it, and may be used to display locations on the zone. If zone data files252are applicable, each zone may include a zone ID and a short localizable name of the Zone. Such zone data files252may be associated with a view projection matrix (4×4) to convert from 3-D world coordinates to a 2-D map position. Such zone data files252may be associated with a location change event that indicates an update to a current in-game location of the player. Such location change event may be posted regularly, or whenever the player's in-game location changes significantly. The platform server120may store a latest value in ‘state.’ Such zone data files252may include an x, y, z position of the player's character in the zone as well as an a, b, c vector indicating the player's characters orientation or direction. Such zone data files252may be associate with an activity start event and/or an activity end event and for the activity end event, an outcome of completed, failed, or abandoned may be associated to the activity (e.g., activity ID).
Such actor data files254may be associated with an entity with behaviors in the game, and can be player-controller or game-controlled, and can change dynamically during gameplay. Such actor data files254may include an actor ID for the actor, a localizable name for the actor, an image of the actor, and/or a short description of the actor. Such actor data files254may be associated with an actor select event that indicates that the player's selected actor(s) have changed. The selected actor(s) may represent the actors the player is controlling in the game and may be displayed on the player's profile and other spaces via the platform server120. There may be more than one actor selected at time and each game may replace its list of actors upon loading save data.
Such mechanics data files256may be associated with an item, skill, or effect that can be used by the player or the game to impact gameplay (e.g., bow, arrow, stealth attack, fire damage) and may exclude items that do no impact gameplay (e.g., collectibles). Such mechanics data files256may include a mechanic ID of the mechanic, a short name of the mechanic, an image of the mechanic, and/or a short description of the mechanic. Such mechanics data files256may be associated with a mechanic availability change event that indicates that the mechanics available to the player have changed. Available may mean that the mechanic is available in the game world for the player to use, but may require the player to go through some steps to acquire it into inventory (e.g., buy from a shop, pick up from the world) before using it. Each game may replace its list of mechanics upon loading save data.
Such mechanics data files256may be associated with a mechanic inventory change event that indicates that the player's inventory has changed. Inventory may refer to mechanics that are immediately usable to the player without having to take additional steps in the game before using it. Inventory information is used to estimate a player's readiness for various activities, which may be forwarded to the platform server120. Games may replace its list of mechanic inventory upon loading save data. Mechanics on cool down may be considered part of the inventory. Mechanic counts (e.g., ammunition, healing points) with any non-zero value may be treated as “in inventory.” Inventory mechanics may be considered a subset of available mechanics.
Such mechanics data files256may be associated with a mechanic use event that indicates that a mechanic has been used by or against the player and may be used to be displayed as mechanic usage in a UGC context. Such mechanics data files256may include a list or array of mechanics that were used (e.g, fire arrow, fire damage) or whether an initiator is the player, such that whether the mechanics were used by or against the player. Such mechanics data files256may include an initiator actor ID, a current zone ID of the initiator actor, and/or a current x, y, z position of the initiator actor. Such mechanics data files256may be associated with a mechanic impact event that indicates that a mechanic had impact on gameplay (e.g., an arrow hit an enemy) and may be used to display mechanic image in a UGC context. Mechanic use and mechanic image events may be not linked. Such mechanics data files256may include the initiator action ID, the current zone ID of the initiator actor, the current x, y, z position of the initiator actor, a target actor ID, a current zone ID of the target actor, a current x, y, z of the target actor, and a mitigation mechanic that may mitigate the initiator mechanic.
Such game media data files258may be include a game media ID of the game media, a localizable name for the game media, a media format (e.g., image, audio, video, text, etc.), a category or type of media (cut-scene, audiolog, poster, developer commentary, etc.), a URL or a server-provisioned media file, and/or whether the game media is associated with a particular activity. Such game media data files258may be associated with a game media start event that indicates that a particular piece of game media has started in the game right now and a game media end event that indicates that the particular piece of game media has ended.
In some examples, an object data file216, an activity data file251, a zone data file252, an actor data file254, a mechanic data file256, and/or a game media data file258may be converted into a non-fungible in-game digital asset using a non-fungible token, such as the token400ofFIG.4, that is stored in and whose history is tracked across one or more of the distributed ledgers150. The token may include metadata associated with the object data file216, the activity data file251, the zone data file252, the actor data file254, the mechanic data file256, and/or the game media data file258. In some examples, at least some of the events identified in the table250as associated with at least one of the object data file216, the activity data file251, the zone data file252, the actor data file254, the mechanic data file256, and/or the game media data file258can be identified in the history of the non-fungible in-game digital asset tracked in the distributed ledgers150.
FIG.3is a block diagram illustrating three consecutive blocks of a blockchain ledger300that may be used to track a digital asset associated with a video game, according to an aspect of the present disclosure. Three blocks of the blockchain ledger300are illustrated inFIG.3, including Block A305, Block B335, and Block C365.
Each block includes a block header310/340/370and a list of one or more payloads330/360/390. In some examples, block header310/340/370includes a hash315/345/375of the previous block and/or a hash310/340/370of the block header of the previous block. For instance, the header370of block C365includes a hash375of the header340of block B335. The header340of block B335likewise includes a hash345of the header310of block A305. The header310of block A305likewise includes a hash315of a header (not pictured) of previous block (not pictured) that is before block A305in the blockchain ledger300. Including the hash of the previous block's header secures the blockchain ledger300by preventing modification of any block of the blockchain ledger300after the block has been entered into the blockchain ledger300, as any change to a particular block would cause that block header's hash315/345/375in the next block to be incorrect. Further, modification of that block header's hash in the next block would make the next block's header's hash315/345/375in the block after the next block incorrect, and so forth. A verifying device can verify that a block has not been modified by computing the hash of block and/or of the block header, then comparing the computed hash to the stored hash315/345/375that is stored in the next block. In some distributed ledgers, a block header310/340/370can include hashes of multiple previous blocks and/or block headers of multiple previous blocks, as in a distributed acyclic graph (DAG) ledger.
Each block's block header310/340/370can include a Merkle root320/350/380. The Merkle root320/350/380can be is generated based on hashes of each of the tokens, transactions, smart contracts, and/or other elements identified in the payload330/360/390for that block. Any attempt to modify a payload after the block has been entered would change the Merkle root. A verifying device can verify that the payload(s)330/360/390have not been modified by computing the Merkle root, then comparing the computed Merkle root to the stored Merkle root320/350/380that is stored in the block header310/340/370. Changes to the payload330/360/390and/or to the Merkle root320/350/380would also change the hash for the block and/or for the block header, for which a value is stored in the next block as the hash315/345/375. Each payload of each block may include one or more tokens (e.g., token400), one or more transactions, one or more smart contracts, other content, or combinations thereof.
Each block's block header310/340/370may also include various elements of metadata, such as a version number for the blockchain ledger platform, a version number for the block itself, a timestamp for verification of each payload, a timestamp for generation of the block, a timestamp for entry of the block into the blockchain ledger300, a timestamp for request of generation of the block, a difficulty target value (e.g., adjusting difficulty of mining), one or more randomized nonce values, a counter identifying how many nonces have been tried, a title of the blockchain ledger300, an identifier as to what the blockchain ledger300is tracking (e.g., a history of a digital asset associated with a video game), or a combination thereof. Each individual element added can further serve as information that can be verified by a verifying device to identify if the block, and the payload within, is accurate and authorized. The one or more randomized nonce values can serve to further complicate the hashes, improving security.
Each block305/335/365of the blockchain ledger300also includes a payload330/360/390. The payload330/360/390for each block305/335/365can include one or more tokens (e.g., token400), one or more transactions, one or more smart contracts, one or more other elements, metadata related to any of the previously-listed elements, or combinations thereof. A token may be, for example, a non-fungible token. The token400may be an example of a token that is stored in the payload330/360/390for a block305/335/365. As discussed with respect to the token400, certain parts of the token400are stored within the payload330/360/390of the blockchain ledger300, and are thus stored “on-chain.” As discussed with respect to the token400, certain parts of the token400include on-chain pointers that point to data outside of the blockchain ledger300, such as a data structure140, with such data being stored “off-chain.” The payload330/360/390of the blockchain ledger300may store hashes of off-chain data, so that a verifying device can compute a hash of the off-chain data and compare the computed hash to the stored hash that is stored on-chain to verify that the off-chain data is accurate. In some examples, the payload330/360/390includes one or more smart contracts. The block may include the code of the smart contract stored within the payload330/360/390of the blockchain ledger300, thus storing the code on-chain. If the payload330/360/390includes a smart contract, the block may include a hash of the code of the smart contract and/or a pointer to an off-chain data structure140storing the code of the smart contract, thus storing the code off-chain. In some examples, some of the smart contract's code may be stored on-chain, while some of the smart contract's code may be stored off-chain. In some examples, smart contracts can be used to create, modify, transfer, or otherwise manage tokens. In some examples, the payload330/360/390includes transactions. In some examples, transactions may include transfers of tokens from one account to another account. In some examples, transactions may include changes to certain properties of tokens or the associated digital assets, such as changes to ownership, in-game visual appearance, in-game attributes, authorship, licenses to use, rentals, or combinations thereof.
In one illustrative example, a first computing device can store a blockchain ledger including a plurality of blocks. Each of a plurality of computing devices (e.g., in a distributed architecture) also stores a copy of the blockchain ledger. The first computing device can receive a message identifying an intended payload element (e.g., token and/or transaction and/or smart contract). For example, the intended payload element may be a token related to one of the digital assets associated with one or more video games described herein. The first computing device can verify that the intended payload element is valid. In some blockchain ledger300implementations, the first computing device can verify that sufficient funds are allocated in order to pay for execution fee charges for the intended payload element, for instance in the form of gas on an Ethereum blockchain ledger. For a transaction, the first computing device can verify whether the transferor has a sufficient quantity of an asset (e.g., whether the transferor owns the token to be transferred) for the transaction to take place. For a smart contract, the first computing device can verify that the smart contract refers to valid accounts that include sufficient quantity of an asset (e.g., token) to execute the smart contract (e.g., to transfer the token), verify that the code of the smart contract can be executed (e.g., does not include syntax errors or other errors), verify that all parties involved in the smart contract have submitted agreement to the terms of the smart contract, or a combination thereof. For a token, the first computing device can verify that the token refers to a valid digital asset, for instance a valid type of digital asset.
The first computing device can generate a hash of a most recent block or block header of the blockchain ledger300. The first computing device can generate a new block header for a new block. The new block header can include at least the hash of the most recent block or block header of the blockchain ledger300. The first computing device can generate the new block, the new block including the new block header and a payload with one or more payload elements. The one or more payload elements include at least the intended payload element discussed above (e.g., token, smart contract, transaction). The first computing device can generate a Merkle root based on the payload elements, and include the Merkle root in the new block header. The first computing device can generate a metadata and a nonce value based on the payload elements, and include the metadata and the nonce value in the new block header. The first computing device can append the new block to the plurality of blocks of the blockchain ledger300in response to verifying the intended payload element. The first computing device can transmit the new block to the plurality of computing devices that each store the blockchain ledger300in response to verifying the intended payload element. Each of the plurality of computing devices also appends the new block to their respective copy of the blockchain ledger300.
In another illustrative example, a first computing device can store a blockchain ledger300including a plurality of blocks. Each of a plurality of computing devices (e.g., in a distributed architecture) also stores a copy of the blockchain ledger300. The first computing device can receive a UI input identifying an intended payload element (e.g., transaction and/or smart contract). The first computing device can generate a message identifying the intended payload element. The first computing device can retrieve a private key associated with an account corresponding to the first computing device. The first computing device can modify the message by encrypting at least a portion of the message with the private key. The first computing device can transmit the message to the plurality of computing devices other than the first computing device. A second computing device of the plurality of computing devices verifies that the intended payload element is valid, for instance as described in the previous paragraph. The first computing device receives a new block from the second computing device. The new block identifies and/or includes the intended payload element (e.g., in its payload). The first computing device appends the new block to the plurality of blocks of the blockchain ledger300at the first computing device.
WhileFIG.3only illustrates three blocks305/335/365of the blockchain ledger300, it should be understood that any blockchain discussed herein may be longer or shorter in that it may have more or fewer than three blocks. Furthermore, it should be understood that another type of distributed ledger, such as a directed acyclic graph (DAG) ledger, can be used instead of, or in addition to, the blockchain ledger300.
In some examples, a distributed ledger may have a non-linear ledger structure, such as that of a directed acyclic graph (DAG) ledger. Such a DAG ledger may be used instead of or in addition to the blockchain ledger300discussed herein. The term “distributed ledger” as used herein should be understood to refer to at least one of a blockchain ledger300(as inFIG.3), a DAG ledger, or a combination thereof. In a DAG ledger, each block header includes the hashes of blocks (or block headers) of a number of other “parent” blocks in the DAG ledger, selected either at random or in some other non-linear manner, rather than just the hash315/345/375of a single previous block (or block header) as in the blockchain ledger300. Where each block header includes multiple hashes corresponding to different parent blocks or their headers, these hashes can be combined together (e.g., using a Merkle root). In some examples, the number of parent blocks of a given block in a DAG ledger is predetermined. In some examples, the number of parent blocks of a given block in a DAG ledger is greater than or equal to a predetermined minimum number of parent blocks, such as a two-parent minimum or a one-parent minimum, meaning that each block has at least the predetermined minimum number of parent blocks. In some cases, each block in a DAG ledger may only identify only a single payload element (e.g., a smart contract, a token400, a transaction) rather than multiple payload elements, and may therefore forego a Merkle root320/350/380of payload elements and/or replace it with a hash of the single payload element. In other implementations, each block may identify multiple payload elements associated with a predetermined time period, and/or may include a Merkle root320/350/380of the payload elements. In some examples, DAG ledgers may provide benefits over a blockchain ledger300, for instance by providing parallelized validation, which may provide higher throughput and/or improved security compared to a blockchain ledger300.
FIG.4is a block diagram illustrating an example token400that can be non-fungible and that can represent a digital asset405associated with a video game as tracked in a distributed ledger, according to an aspect of the present disclosure. In some examples, the token400is a non-fungible token (NFT). In some examples, the token400is an ERC721 token, an ERC1155 token, an ERC-20 token, or a combination thereof. In some examples, the token400is tracked in a blockchain ledger300. In some examples, the token400is tracked in an Ethereum-based blockchain ledger300.
The digital asset405that the token400represents can be an instance of a video game. The digital asset405that the token400represents can be an in-game digital asset, such as an in-game item, and in-game character (which can be referred in-game actor), an in-game costume for an in-game character, an in-game area, a save file for a game, a configuration for a game, a DLC, an IAP, or a combination thereof. An in-game digital asset can be referred to as an in-game object, as in the object ofFIGS.2A-2B. An in-game character can be referred to as an in-game actor, as in the actor254ofFIG.2B. An in-game area can be referred to as an in-game zone, as in the zone252ofFIG.2B. In some examples, the in-game character can be a player character controlled by a player, a non-player character (NPC) that the player cannot control (but in some cases can interact with), or some combination thereof. In some examples, an in-game costume can include in-game representations of clothing, outfits, armor, suits, hats, helmets, tops, shirts, jackets, bottoms, pants, skirts, gloves, gauntlets, shoes, boots, fins, eyewear, headwear, handwear, legwear, footwear, jewelry, accessories, another article of clothing, or combinations thereof. In some examples, in-game items can include ranged weapons, melee weapons, potions, food, consumables, armors, shields, ammunition, magic abilities, health-restorative items, mana-restorative items, vehicles, power-ups, extra lives, extra continues, items that modify the attributes of other items (e.g., upgrading a bow and arrow to shoot fire arrows), or combinations thereof.
The digital assets may be video game digital media assets with media representations of one or more moments of gameplay of a video game, such as video clips, images, or audio clips. For instance, an image may be a representation of a single moment of gameplay of a video game. An image can include, for example, a screenshot. A video clip or audio clip can be a representation of a series of consecutive moments of gameplay of a video game. For instance, each moment of the consecutive moments may be represented by an individual video frame of the video clip, or by a particular set of one or more frequencies and amplitudes of sound in the audio clip. Not all moments must be consecutive, as the video clip or audio clip may cut from one set of moments to another, as in a highlight reel. In some examples, an image can be a representation of multiple moments of gameplay of a video game, for example as in a collage of images or a long-exposure-style image that includes a representation of a path along which one or more characters or items moved over one or more durations of time. An image, video clip, and/or audio clip can be captured from a view, perspective, and/or vantage point that a particular player has during gameplay. An image, video clip, and/or audio clip can be captured from a different view, perspective, and/or vantage point than any individual player has.
In some examples, the digital asset can include a save file that saves progress in a video game at a particular point in the progression (e.g., in the story) of the video game. The save file can be identified as an in-game digital asset, since it is usable in-game. The save file can be identified as a video game digital media asset, since it functions as a representation of a moment of gameplay at which the save file was saved.
In some examples, the digital asset can include a “ghost” that can be imported into a game in a way that is visible to a player of the game. The ghost can follow a path of a previous player's gameplay. For example, in a racing game, a ghost can show up in a player's game following a previously-raced route that was raced by the same player at an earlier time, or by another player, at the pace that that route was previously-raced. The ghost can be identified as an in-game digital asset, since it is usable in-game. The ghost can be identified as a video game digital media asset, since it functions as a representation of multiple moments (a duration of time) of the previous player's gameplay.
One or more token smart contracts445can be associated with the token400. For instance, the one or more token smart contracts445manage creation (or “minting”) of the token400. The one or more token smart contracts445can pay miner devices that create (“mint”) a token400, or batches of tokens, for computing time and resources taken to mint the token400. The one or more token smart contracts445can control how ownership of the token400is decided and/or transferred. For instance, the one or more token smart contracts445can indicate an initial owner of the token400and/or can identify conditions under which ownership automatically transfers, for instance an offer meeting or exceeding an owner-mutable threshold amount. The one or more token smart contracts445can indicate conditions under which the token400can be rented out or licensed out for use by licensee users/players, for instance an offer meeting or exceeding an owner-mutable threshold amount. The one or more token smart contracts445can control conditions under which the token400can be burnt, or irreversibly destroyed and/or unlisted. The elements identified as part of the token400inFIG.4—including the token identifier410, the token unit quantity415, the token ownership420, the on-chain immutable metadata425, the on-chain mutable metadata430, the on-chain pointers to off-chain media435, the on-chain pointers to off-chain metadata440—can be stored as part of the token400, can be part of the token smart contracts445, or both. In some examples, the code of the token smart contracts445is stored at least partly on-chain. In some examples, the code of the token smart contracts445is stored at least partly off-chain at off-chain location(s) such as the data structures140, with the off-chain location(s) identified by on-chain pointers to the off-chain location(s). The smart contract ofFIGS.11A-11Bcan be an example of the token smart contracts445.
The token400includes a token identifier410, which may be referred to as a tokenID. The token identifier410can be a unique identifier for the token400and/or for the digital asset405. The token identifier410can be used to distinguish the particular instance of the digital asset405that the token400corresponds to from any other instance of the digital asset405. In some examples, token identifiers can be created by a computing system creating (or “minting”) the token400by incremented sequentially compared to token identifiers of previously-created tokens, to ensure that each token identifier is unique.
The token400can include a token unit quantity415. The token unit quantity415can identify a quantity of the token400that has been or is set to be minted. In some examples, the token unit quantity415is one, in which case a single token400exists for a given digital asset405. In some examples the token unit quantity415is greater than one. For example, if the token unit quantity415is 5, then there are effectively 5 copies of this token400representing this unique digital asset405that can be owned and/or transferred separately. Those 5 copies may be fungible between one another, or indistinguishable from one another. However, those 5 copies are still non-fungible, unique, distinct, and/or distinguishable relative to any other instance or version or variant of the digital asset405. The token unit quantity415can control how rare the token400, and by extension the digital asset405, is. If the token unit quantity415is one, then the token400and corresponding digital asset405is unique. If the token unit quantity415is more than one but less than a rarity threshold, then the token400and corresponding digital asset405is rare. If the token unit quantity415is more than one but more than a rarity threshold, then the token400and corresponding digital asset405is common. In some examples, there may be any number of ranges of rarity, in addition to or instead of unique, rare, and common—such as legendary, very rare, slightly rare, uncommon, and other categories of rarity. In some cases, the token unit quantity415can be decided as part of the minting process and/or identified in one of the token smart contracts445that manages the minting process.
The token400may identify a token ownership420, which may identify who owns the token400, and by extension, the corresponding digital asset405. The token ownership420may initially be assigned to a creator of the digital asset405. The token smart contracts445can control rules for transfer of token ownership420. Token ownership420can be transferred as a transaction that is recorded as a payload element in a payload of a block of a blockchain ledger or other distributed ledger.
The token400may include on-chain immutable metadata425. The on-chain immutable metadata425can include, for example, a description of the token400, a description of the digital asset405that the token400represents, some immutable attributes or properties of the digital asset405and/or the token400, or some combination thereof. The on-chain immutable metadata425can use properties of the distributed ledger and/or of the token smart contracts445to ensure that the on-chain immutable metadata425remains unchanged. In some examples, the on-chain immutable metadata425can identify which game the data asset405is from, is a representation (e.g., recording) of, or is otherwise related to. In some examples, the on-chain immutable metadata425can identify a creator of the digital asset405and/or of the token400. In some examples, the on-chain immutable metadata425can identify statistics for the digital asset405and/or of the token400(e.g., this in-game item provides +2 attack power).
The token400may include on-chain mutable metadata430. The on-chain mutable metadata430can include, for example, a description of the token400, a description of the digital asset405that the token400represents, some immutable attributes or properties of the digital asset405and/or the token400, or some combination thereof. The on-chain mutable metadata430can be mutable or changeable. In some examples, a change to the on-chain mutable metadata430can be recorded as a transaction that is recorded as a payload element in a payload of a block of a blockchain ledger or other distributed ledger. In some examples, the on-chain immutable metadata425can identify how many times the digital asset405has been used in-game and/or how many different players have used the digital asset405.
The token400may include on-chain pointers to off-chain media435. The off-chain media can include the digital asset405and/or one or more representations of the digital asset405. For example, the off-chain media can include one or more images, 3D models, video clips, audio clips, or combinations thereof. These types of media can require a lot of storage space to store, and can thus be expensive to store on-chain in terms of execution fee charges (such as gas on an Ethereum blockchain ledger). Thus, it may be more efficient to store this media off-chain in one or more off-chain locations, such as the data structures140. The on-chain pointer can include a uniform resource identifier (URI), such as a uniform resource locator (URL), that points to the one or more network locations of the one or more off-chain locations. In some examples, hashes can be stored of the off-chain media, so that a verifying device can compute a hash of the off-chain media and compare the computed hash to the stored hash that is stored on-chain to verify that the off-chain media is accurate. In some examples, the off-chain media may be immutable. In some examples, the off-chain media may be mutable. In some examples, the pointer may be immutable. In some examples, the pointer may be mutable.
The token400may include on-chain pointers to off-chain metadata440. The off-chain metadata430can include, for example, a description of the token400, a description of the digital asset405that the token400represents, some immutable attributes or properties of the digital asset405and/or the token400, or some combination thereof. Some digital assets405and/or tokens400may require significant quantities of metadata, which can require a lot of storage space to store, and can thus be expensive to store on-chain in terms of execution fee charges (such as gas on an Ethereum blockchain ledger). Thus, it may be more efficient to store this metadata off-chain in one or more off-chain locations, such as the data structures140. The on-chain pointer can include a uniform resource identifier (URI), such as a uniform resource locator (URL), that points to the one or more network locations of the one or more off-chain locations. In some examples, hashes can be stored of the off-chain metadata, so that a verifying device can compute a hash of the off-chain metadata and compare the computed hash to the stored hash that is stored on-chain to verify that the off-chain metadata is accurate. In some examples, the off-chain metadata may be immutable. In some examples, the off-chain metadata may be mutable. In some examples, the pointer may be immutable. In some examples, the pointer may be mutable.
FIG.5is a block diagram500illustrating a transfer of usability of an asset530from a first user device515to a second user device525. The first user device515is associated with a first user510, while the second user device525is associated with a second user520. The first user device515and the second user device525can each be examples of the user device130, the console228, the entertainment systems1300, or a combination thereof. An asset management system505can manage the transfer of usability of the asset530from the first user device515to the second user device525. The asset management system505can include the interactive content servers110, the platform servers120, the data structures140, the distributed ledgers150, the APIs160, one or more user devices130, the distributed network105, the console228, the entertainment systems1300, or a combination thereof.
The asset management system505is communicatively coupled to the first user device515and the second user device525, for instance through one or more networks. In some examples, the asset management system505has a level of control over the first user device515and the second user device525, for instance having the ability to enable or disable a digital entitlement (e.g., usability of a certain digital asset) at the first user device515and/or the second user device525. The asset management system505can use this to manage a transfer of usability of the asset530.
The first user device515may have obtained an asset530, may have the asset530, and may have authorization to use the asset530. For instance, the first user device515may have purchased the asset530from a software repository (e.g., of the asset management system505) or from a third user device. In the example illustrated inFIG.5, the asset530is a digital instance of a video game titled “Call of Speed: Police Chase.” The asset management system505may receive a request from the first user device515indicating that the first user510wishes to sell, rent, loan, license, and/or transfer the asset530, and/or the authorization to use the asset530. The transfer may be permanent, as in a sale, or temporary, as in a rental or loan.
In some examples, the request may identify the second user520and/or the second user device525associated with the second user520. In some examples, the asset management system505may identify the second user520and/or the second user device525associated with the second user520, for example as part of a matchmaking process such as the matchmaking process illustrated inFIG.6. Before the transfer of usability of the asset530, the second user device525does not have authorization to use the asset530. To transfer usability of the asset530from the first user device515to the second user device525, the asset management system505can disable authorization to use the asset530at the first user device515, and can enable authorization to use the asset530at the second user device525. After the transfer, the second user device525has authorization to use the asset530, and the first user device515no longer has authorization to use the asset530.
The asset management system505can manage one or more transfers of other assets corresponding to the transfer of usability of the asset530from the first user device515to the second user device525. For instance, the asset management system505can receive a transfer of an asset545from the second user device525and/or the second user520. The asset management system505can transfer an asset540to the first user device515and/or the first user510. In some examples, the asset540, and/or the asset545, include fiat currency funds, platform-specific funds (e.g., gift cards and/or store points), another instance of the same video game as in the asset530, an instance of a different video game than in the asset530, in-game content for the same video game as in the asset530, in-game content for a different video game than in the asset530, or a combination thereof. In some examples, the asset540includes at least a portion of the asset545. In some examples, the asset545includes at least a portion of the asset540.
For instance, in one illustrative example, the asset management system505can receive a request from the first user device515to transfer the asset530, can disable authorization to use the asset530at the first user device515, and can provide the asset540(e.g., a predetermined amount of funds) to the first user device515and/or the first user510in exchange for the authorization to use the asset530. The asset management system505can then, at a later time, identify the second user520and/or second user device525, for instance by receiving a request from the second user520and/or second user device525seeking to acquire authorization to use the asset530, by sending a query to the second user520and/or second user device525to inquire as to whether the second user520would be interested in acquiring authorization to use the asset530, and/or via the matchmaking process ofFIG.6. The second user520and/or second user device525can provide the asset545(e.g., a second predetermined amount of funds) to the asset management system505, and the asset management system505can enable authorization to use the asset530at the second user device525in exchange. In some examples, the asset545can include a greater amount of funds than the asset540. In some examples, a portion of the asset545(e.g., a portion of the amount of funds of the asset545) can be provided to other entities550than the two users or their devices, such as one or more developers of the asset530, one or more publishers of the asset530, one or more former owners of the asset530, the asset management system505itself, or a combination thereof.
In another illustrative example, the asset management system505can receive a request from the first user device515to transfer the asset530, causing the asset management system505to initiate a matchmaking process to identify the second user520and/or the second user device525, such as the matchmaking process illustrated inFIG.6. Through the matchmaking process, the asset management system505can provide information about the second user520and/or the second user device525to the first user510and/or the first user device515. Through the matchmaking process, the asset management system505can provide information about the first user510and/or the first user device515to the second user520and/or the second user device525. In some examples, the first user510and/or the first user device515can select the second user520and/or the second user device525to be the recipient of the authorization to use the asset530, after which the asset management system505can automatically perform the transfer of authorization to use the asset530from the first user device515to the second user device525upon provision of the asset545by the second user520and/or the second user device525. In some examples, the second user520and/or the second user device525can select the first user510and/or the first user device515to be the seller from whom they choose to purchase the authorization to use the asset530, after which the asset management system505can automatically perform the transfer of authorization to use the asset530from the first user device515to the second user device525upon provision of the asset545by the second user520and/or the second user device525. In some examples, the asset management system505can automatically perform the transfer of authorization to use the asset530from the first user device515to the second user device525as soon as the asset management system505identifies both the second user520and/or the second user device525and the first user510and/or the first user device515, and the asset545is provided by the second user520and/or the second user device525. In some examples, once the asset management system505receives the asset545, the asset management system505transfers at least a portion of the asset545to the first user510and/or the first user device515as the asset540, and in some cases another portion of the asset545to the other entities550. In some examples, the management platform505does not store the asset545, but immediately conveys at least a portion of the asset545over to the first user510and/or the first user device515as the asset540, and in some cases another portion of the asset545to the other entities550. In some examples, the asset540is the asset545. In some cases, the asset540is less than (e.g., includes fewer funds than) the asset545. In some cases, the asset540is greater than (e.g., includes more funds than, or additional other asset(s)) than the asset545, with the additional asset(s) provided by the asset management system505and/or the other entities550, for instance to encourage use of the asset management system505for such transfers.
In some examples, the first user510and/or the first user device515may also provide additional asset(s) along with the asset530. For instance, the first user510and/or the first user device515may provide an amount of funds to the asset management system505. The additional asset(s), in some examples, can be provided from the asset management system505to the other entities550.
In some examples, the asset management system505includes a distributed ledger, such as a blockchain ledger300. In some examples, transactions recording the transfers of the asset530, the asset540, and/or the asset545can be stored by the asset management system505in the distributed ledger. In some examples, smart contracts corresponding to the transfers of the asset530, the asset540, and/or the asset545can be stored by the asset management system505in the distributed ledger, and can be executed to perform the transfers of the asset530, the asset540, and/or the asset545once certain conditions are met, such as transfer of the asset530being automatically executed upon verification that the transfer(s) of the asset540and/or the asset545are complete. In some examples, tokens corresponding to the asset530, the asset540, and/or the asset545can be stored by the asset management system505in the distributed ledger and/or transferred by the asset management system505using the distributed ledger.
In some examples, the asset management system505can change what content is, and/or can be, stored on the first user device515and/or the second user device525as a result of the transfer. For example, as part of disabling the authorization to use the asset530at the first user device515, the asset management system505can delete the asset530from the first user device515, or cause the first user device515to delete the asset530. As part of enabling the authorization to use the asset530at the second user device525, the asset management system505can send the asset530to the second user device525, or cause the second user device525to download the asset530, for example from a software repository. In some examples, the authorization to use the asset530also includes an authorization to download the asset530from the software repository of the asset management system505.
In some examples, the asset management system505is tied to a managing assets, transfers, and/or user devices related to a specific platform or ecosystem, such as the Sony® PlayStation® platform or ecosystem. In some examples, the asset management system505can manage assets, transfers, and/or user devices of multiple platforms or ecosystems. For instance, the first user510can trade an instance of a video game for PC (e.g., as the asset530) for a different instance of the same video game for a Sony® PlayStation® console (e.g., as the first user device515) of the first user510(e.g., as the asset540and/or the asset545).
FIG.6is a conceptual diagram illustrating an example of an interface600for matchmaking between users for transferring usability of an asset630. In the exemplary illustration ofFIG.6, the asset630is in-game content, specifically downloadable content (DLC), for a video game titled “Pirate's Flag III.” The asset630is being sold by a user640with the username BugHero62.
In the matchmaking process illustrated inFIG.6, the asset management system505identifies various users that may be interested in purchasing the asset630from the user640, including a user605, a user610, a user615, and a user620. Each of the various users identified by the asset management system505include at least one characteristic in common with the user640. For instance, the user605, whose username is Burger85, shares a game of interest characteristic with the user640, titled “Bounty Hunter IV.” In particular, the asset management system505identifies that the “Bounty Hunter IV” is the most played game for user605, and also appears on a wish list for the user640. A “propose a trade” button650appears beside the entry for the user605, allowing the user640to propose a trade between the asset630and the “Bounty Hunter IV” game.
The user610, whose username is Jessica72 and whose most played game is “Bombs Away,” is identified by the asset management system505as sharing a friend circle characteristic, as the user610belongs to the user640's friends list. The user615, whose username is SteveRacer1 and whose most played game is “Call of Speed: Police Chase,” is identified by the asset management system505as sharing a most played game characteristic, as the game “Call of Speed: Police Chase” is also the user640's most played game. The user620, whose username is SeaCaptain9 and whose most played game is “Pirate's Flag III,” is identified by the asset management system505as sharing a game ownership characteristic, as the user620and user640both own the game “Pirate's Flag III,” with this being particularly relevant because the asset630is in-game content (DLC) for the game “Pirate's Flag III.” The interface600illustrated inFIG.6shows a selection pointer highlighting the user620, indicating that the user640is interested in selling the asset630to the user620, for instance based on the shared game ownership characteristic between the user620and the user640.
FIG.7is a conceptual diagram illustrating an example of an interface700for purchasing authorization to use a digital asset630associated with a video game. The interface700is an example interface for a potential purchaser of the asset630, such as the second user520, the second user device525, the user605, the user610, the user615, and/or the user620. The interface700includes asset information705that identifies the asset630as being in-game content, specifically downloadable content (DLC) titled “Premium Ships” for a video game titled “Pirate's Flag III.” The asset information705also identifies that the seller (e.g., the user640) has requested a price of $9.99 for the asset630, that the original “new” price for the asset630was $14.99, and that the average “used” price for the asset630is $10.99. The interface700includes buttons allowing the purchasing user to buy the asset630now at $9.99, to bid a different amount (such as the $5.99 amount entered into the bid field), to propose a trade for the asset630(e.g., in exchange for a different game or in-game content element), or to add the asset630to the purchasing user's wish list. If the purchasing user buys the asset630now at $9.99, the $9.99 can be an example of the asset545, and the transfer can proceed immediately. In some examples, the asset management system505can manage bids for the asset630, for instance automatically selecting the highest bidder at the end of a bid time period. The winning bid can then be an example of the asset545.
The interface700also includes seller information710identifying information about the user640who is selling the asset630. For example, the seller information710identifies that the username for the user640is BugHero62, that average feedback (e.g., from other purchasing users who have purchased from the user640using the asset management system505) for the user640is 97.9% positive, that the user640is located in North America, that the user640's most played games include “Call of Speed: Police Chase” and “Pirate's Flag III,” and that the user640and the purchasing user have user610Jessica72 as a friend in common. The interface700includes a button to contact the seller, which allows the asset management system505to open a channel of communication between the user640and the purchasing user. The interface700includes a button to see other assets being sold by the user640, which can allow the asset management system505to identify to the purchasing user other assets being sold by the user640other than the asset630.
FIG.8is a conceptual diagram illustrating an example of an interface800for appraising a value of a digital asset630associated with a video game. The interface800ofFIG.8may be an interface for a seller user, such as the user640. The interface800identifies some of the same asset information705as the interface700ofFIG.7, such as the original “new” price for the asset630being $14.99, and the average “used” price for the asset630being $10.99. This information can be used for appraisal of a price requested by the user640, for instance to identify whether the price requested by the user640is average, lower than average, or higher than average. The interface800includes a “price requested” field805where the user640can enter a price that the user640wishes to sell the asset630for. In some examples, the price requested can be a “buy now” price at which a purchasing user can immediately buy the asset630without undergoing a bidding process. In some examples, the price requested can be a minimum bid that a purchasing user can place for the asset630, with the asset management system505still managing the bidding process after placement of the bid. The interface800includes a price of $9.99 in the “price requested” field805, and includes an alert indicating that this $9.99 price is lower than the average “used” price for the asset630of $10.99.
The interface800also includes a graph840of the “new” price of the asset630over time, for instance from an official software repository or marketplace. The graph840shows that the “new” price of the asset630has fluctuated over time, for instance based on various sales, price drops, price hikes, and the like. The interface800includes a graph845of the average “used” price of the asset630over time, for instance based on various transfers such as the transfer ofFIG.5that are managed by the asset management system505. The graph845shows that the average “used” price of the asset630has fluctuated over time, somewhat similarly to the “new” price of the asset630over time in the graph840, but somewhat independently as well. Both the graph840and the graph845include a dashed horizontal line representing the $9.99 price requested by the user640.
FIG.9is a conceptual diagram illustrating an example of an interface900for onboarding a user onto a platform and assisting the user with conversion of video game assets905associated with other platforms to corresponding video game assets910associated with the platform. As noted previously, in some examples, the asset management system505can manage assets, transfers, and/or user devices of multiple platforms or ecosystems. The interface900identifies video game assets905that a user owns on other platforms or ecosystems, such as PC or Game Box platforms or ecosystems. The video game assets905include an instance of video game “Call of Speed: Police Chase” for the PC platform, an instance of video game “Bounty Hunter IV” for the Game Box platform, and an instance of video game “Pirate's Flag III” for the Game Box platform. The asset management system505, which in the example ofFIG.9is associated with the Sony® PlayStation® platform or ecosystem, identifies corresponding instances of the same video games that are available for the Sony® PlayStation® platform or ecosystem as the video game assets910. For instance, in the interface900, the asset management system505identifies an instance of video game “Call of Speed: Police Chase” for the Sony® PlayStation® 5 platform, an instance of video game “Bounty Hunter IV” for the Sony® PlayStation® 5 platform, and an instance of video game “Pirate's Flag III” for the Sony® PlayStation® 5 platform.
The interface includes a query930asking the user whether the user would like to automatically sell the video game assets905for the other platforms and use the funds from these sales to go toward the video game assets910for the Sony® PlayStation® platform that the user is joining. The query930includes a “yes” button that causes the asset management system505to sell the video game assets905for the other platforms to one or more other users and/or user devices, such as the user920and/or user device925, as discussed with respect toFIG.5. For instance, the video game assets905can be examples of the asset530, the user920can be an example of the second user520, and the user device925can be an example of the second user device525. Funds from the user920and/or the user device925can be examples of the asset540and/or the asset545, and can be automatically applied to purchase of the video game assets910by the asset management system505. In some examples, the asset management system505can purchase the video game assets910as new video game assets from an official software repository or marketplace. In some examples, the asset management system505can purchase the video game assets910as used video game assets from seller users and/or seller user devices. In such examples, the video game assets910can be examples of the asset530, the seller users can be examples of the second user520, and the seller user device can be examples of the second user device525. The query930includes a “no” button that does not perform the suggested transfer of the video game assets905for the video game assets910.
FIG.10is a block diagram1000illustrating an authorization process managing user authorization of a transfer of usability of an asset. The first user device1015is associated with a first user1010, while the second user device1025is associated with a second user1020. The first user device1015and/or the first user1010submits a request1035for transfer of authorization for use of an asset1030to the asset management system505. In some examples, the request1035is a request to transfer authorization to use the asset1030away from the first user device1015. In such examples, the first user1010and the first user device1015are examples of the first user510and the first user device515, respectively. In some examples, the request1035is a request to transfer authorization to use the asset1030the first user device1015from another user device. In such examples, the first user1010and the first user device1015are examples of the second user520and the second user device525, respectively.
The second user1020can be a parent, guardian, supervisor, co-worker, friend, and/or family member of the first user1010. The asset management system505identifies settings and/or rules associated with the first user1010, the first user device1015, the second user1020, the second user device1025, and/or the asset1030. The settings and/or rules can identify conditions under which the second user1020and/or the second user device1025must provide authorization before a requested transfer can be performed by the asset management system505. If the conditions are met, the asset management system505sends an alert to the second user device1025of the second user1020. The second user device1025can be an example of the user device130, the console228, the entertainment systems1300, or a combination thereof. In some examples, the second user device1025is a smart phone, a mobile handset, and/or a wireless communication device. The second user device1025can display the alert1040. The alert1040can identify the request1035, the asset1030, the details of the requested transfer of the asset1030, further information about the asset1030(e.g., type of game or in-game content), or a combination thereof. For example, the alert1040can indicate an age rating for the asset1030, such as an Entertainment Software Rating Board (ESRB) rating for the asset1030. In some examples, the alert1040can indicate user ratings and/or reviews for the asset1030.
If the asset1030is an asset that the first user device1015is authorized to use and that the request1035seeks to transfer that authorization to use away from the first user device1015, then the alert1040may identify a usage history of the asset1030on the first user device1015, for instance to ensure that the first user1010is not trying to sell a favorite game or piece of in-game content. The alert1040can identify a price that the first user1010seeks to sell, rent, license, or otherwise transfer the asset1030for, such as the price requested in the price requested field805. The alert1040can identify any of the asset information705and/or the seller information710in the interface700and/or the interface800.
The second user device1025can send a response1045to the asset management system505. The response1045is responsive to the alert1040, and indicates whether the user1020authorizes or declines the request1035. If the response1045indicates that the user1020authorizes the request1035, then the asset management system505can perform the transfer requested in the request1035as discussed with respect to the transfer ofFIG.5, and can send a confirmation1050to the first user1010and/or the first user device1015indicating that the response1045is received and that the response1045is an authorization. If the response1045indicates that the user1020declines the request1035, then the asset management system505can cancel and/or prohibit the transfer requested in the request1035, and can send a confirmation1050to the first user1010and/or the first user device1015indicating that the response1045is received and that the response1045declines the request1035.
FIG.11Ais a conceptual diagram1100illustrating generation of a smart contract and entry of the smart contract into a distributed ledger, according to an aspect of the present disclosure. The distributed computing architecture includes multiple computing systems (referred to here as computers), which may be entertainment systems1300, that store and modify the distributed ledger. A first computer submits a request1105requesting entry of a smart contract with particular rules into distributed ledger. A second computer submits a response1110indicating that the second computer has generated a new block to enter into the distributed ledger with the requested smart contract. Third, fourth, and fifth computers submit verification1120A-1120C indicating that they have verified that the block correctly implements the smart contract, that the code of the smart contract can be executed (e.g., does not include syntax errors or other errors), that all parties involved in the smart contract have submitted agreement to the terms of the smart contract, that on-chain pointers correctly point to valid off-chain smart contract code, and/or that sufficient funds are allocated in order to pay for execution fee charges for the intended payload element. The second computer submits and entry confirmation indicating that the new block is successfully entered into the distributed ledger with the requested smart contract in response to a quorum of devices verifying.
A similar process to the process illustrated inFIG.11Amay be used to enter tokens, with the corresponding verification1120A-1120C verifying, for instance, that the token refers to a valid type of digital asset, that on-chain pointers correctly point to valid off-chain media or metadata, and/or that sufficient funds are allocated in order to pay for execution fee charges for the intended payload element. A similar process to the process illustrated inFIG.11Amay be used to enter transaction, with the corresponding verification1120A-1120C verifying, for instance, whether the transferor has a sufficient quantity of an asset (e.g., whether the transferor owns the token to be transferred) for the transaction to take place and/or that sufficient funds are allocated in order to pay for execution fee charges for the intended payload element.
FIG.11Bis a conceptual diagram1150illustrating execution of a smart contract, according to an aspect of the present disclosure. A first computer submits an identification1155that the first computer has executed the smart contract code, identified that the condition in this smart contract has been met, and identified the action to be taken. Second, third, and fourth computers submit verifications1110A-1110C that identify that the second, third, and fourth computers have executed the smart contract code, verified that the condition in this smart contract has been met, and verified the action to be taken. A fifth computer indicates an error1115with no verification. The third computer indicates an action1120, indicating that the third computer has executed the smart contract code and performed the action in response to a quorum of devices verifying (e.g. the verifications1110A-1110C).
FIG.12is a flow diagram illustrating operations1200for authorization reconfiguration for digital asset usability, according to an aspect of the present disclosure. At least a subset of the operations1200can be performed by an authorization management system, which may include, for example, the network environment100, the one or more interactive content servers110, the one or more platform servers120, the one or more user devices130, the one or more data structures140, one or more distributed ledgers150, the network environment200, the console228, the one or more servers218, the blockchain ledger300, the asset management system505, the first user device515, the second user device525, a user device of any of the users605-620, a user device of the user640, the user device925, the first user device1015, the second user device1025, the computing devices ofFIGS.11A-11B, the entertainment system1300, a system, an apparatus, a non-transitory computer readable storage medium having embodied thereon a program to be executed by a processor, or a combination thereof.
At operation1205, the authorization management system is configured to, and can, identify an asset associated with a video game. A first user device is authorized to use the asset. The first user device is associated with a first user. Examples of the asset include the media filed202, the object file216, the activity251, the zone252, the actor254, the mechanic256, the game media258, an asset identified in the payload330, an asset identified in the payload360, an asset identified in the payload390, the token400, the asset530, the asset630, the video game assets905, the video game assets910, the asset1030, an asset whose transfer is controlled using the smart contract(s) ofFIGS.11A-11B, or a combination thereof. Examples of the first user include the first user510, the second user520, the user605, the user610, the user615, the user620, the user640, the user920, the first user1010, the second user1020, or a combination thereof. Examples of the first user device include the user devices130, the console228, the first user device515, the second user device525, the user device925, the first user device1015, the second user device1025, the computing devices ofFIGS.11A-11B, the entertainment system1300, or a combination thereof.
In some examples, the asset is an instance of the video game, such as any of the video games illustrated inFIGS.5-10.
In some examples, the asset includes in-game content associated with the video game. The in-game content is usable by a player of the video game within the video game during gameplay of the video game by the player. The player may be, for example, the first user of operation1205, before the transfer of operations1215-1220. The player may be, for example, the second user of operation1210, after the transfer of operations1215-1220.
At operation1210, the authorization management system is configured to, and can, identify a second user. A second user device associated with the second user lacks authorization to use the asset. Examples of the second user include any of the example users listed above as examples of the first user of operation1205. Examples of the second user device include any of the example users listed above as examples of the first user device of operation1205. In some examples, the authorization management system identifies the second user through a matchmaking process as illustrated inFIG.6.
In an illustrative example, the first user of operation1205is an example of the first user510, the first user device of operation1205is an example of the first user device515, the second user of operation1210is an example of the second user520, and the second user device of operation1210is an example of the second user device525.
In some examples, the authorization management system is configured to, and can, identify a characteristic of the first user. The authorization management system can identify a plurality of characteristics of a plurality of users. The plurality of users includes the second user. The authorization management system can identify from among the plurality of characteristics of the plurality of users, that the second user also shares the characteristic of the first user. In such examples, identifying the second user in operation1210is based on the characteristic being shared by the first user and the second user. Examples of the characteristics include the characteristics identified in the matchmaking process and interface600ofFIG.6.
At operation1215, the authorization management system is configured to, and can, receive an indication of a transfer of usability of the asset.
In some examples, the indication of the transfer of usability of the asset includes receipt of a confirmation for the transfer from the first user device. For example, the confirmation can be a response to a query asking the first user whether the first user is sure that he/she wants to transfer this asset. The confirmation can be a selection of a price, for instance through the price requested field805.
In some examples, the indication of the transfer of usability of the asset includes receipt of an indication of a second transfer of a second asset from an account of the second user. The second transfer is in exchange for the transfer of usability of the asset. Examples of the second transfer include a transfer of the asset545as inFIG.5and/or a transfer of the asset540as inFIG.5. In some examples, the second asset is an amount of funds that pays for the transfer of usability of the asset. In some examples, the authorization management system is configured to, and can, receive a bid from the second user device for the amount of funds, and receive an acceptance of the bid from the first user device, as in the bidding process illustrated in the interface700ofFIG.7and/or the interface800ofFIG.8. In some examples, the authorization management system is configured to, and can, identify an appraisal value associated with the transfer of usability of the asset, wherein the amount of funds is based on the appraisal value, as illustrated in the appraisal process and interface800ofFIG.8.
In some examples, the authorization management system is configured to, and can, identify a second asset associated with the video game. The asset is associated with a first platform that the first user device belongs to, while the second asset is associated with a second platform that a third user device belongs to. The third user device is associated with the first user. The authorization management system can, in response to receiving the indication, automatically enable authorization for the third user device to use the second asset. An example of this is illustrated in the interface900ofFIG.9. For instance, the Sony® PlayStation® 5 console of the interface900can be an example of the third user device, while the PC or Game Box of the interface900can be examples of the first user device. Similarly, the Sony® PlayStation® platform of the interface900can be an example of the second platform, while the PC or Game Box platforms of the interface900can be examples of the first platform. In some examples, the second asset is a variant of the asset that is usable on the second platform, while the asset is usable on the first platform. For example, the video game assets910are variants of the video game assets905that are usable by the Sony® PlayStation® platform, while the video game assets905are usable by other platforms.
In some examples, the authorization management system is configured to, and can, identify that a type of the asset matches a specified type in a rule. In response to identifying that the type of the asset matches the specified type in the rule, the authorization management system can automatically request authorization for the transfer from a third user device associated with a third user. The authorization management system can receive the authorization for the transfer from the third user device associated with the third user, wherein the indication includes the authorization for the transfer. Examples of the authorization include the authorization in the response1045and/or the confirmation1050. In some examples, the third user is a family member of the first user, such as a parent, guardian, or sibling of the first user.
At operation1220, the authorization management system is configured to, and can, automatically disable authorization for the first user device to use the asset in response to receiving the indication.
At operation1225, the authorization management system is configured to, and can, automatically enable authorization for the second user device to use the asset in response to receiving the indication.
In some examples, the authorization management system is configured to, and can, identify a distributed ledger that includes a plurality of blocks. Each block of at least a subset of the plurality of blocks includes a hash of at least a portion of another block of the plurality of blocks. The authorization management system can cause an additional block to be appended to the distributed ledger. A payload of the additional block includes a record of the transfer of usability of the asset. The additional block includes a hash of at least a portion of one the plurality of blocks in the distributed ledger. In some examples, the authorization management system is configured to, and can, generate the additional block. In some examples, the distributed ledger is a blockchain ledger. For instance, examples of the distributed ledger include the blockchain ledger300and/or a DAG ledger. In some examples, the asset includes a non-fungible token (NFT) associated with the video game, such as the token400. In some examples, one or more blocks of the plurality of blocks in the distributed ledger identify a smart contract identifying a condition. Detection of the condition is configured to trigger the transfer of usability of the asset according to the smart contract. The indication can includes verification of detection of the condition, for example as in the verification of the smart contract illustrated inFIGS.11A-11B.
FIG.13is an example user electronic entertainment system that may be used in launching interactive content and providing dynamic interfaces, according to an aspect of the present disclosure. The entertainment system1300ofFIG.13includes a main memory1305, a central processing unit (CPU)1310, vector unit1315, a graphics processing unit1320, an input/output (I/O) processor1325, an I/O processor memory1330, a peripheral interface1335, a memory card1340, a Universal Serial Bus (USB) interface1345, and a communication network interface1350. The entertainment system1300further includes an operating system read-only memory (OS ROM)1355, a sound processing unit1360, an optical disc control unit1370, and a hard disc drive1365, which are connected via a bus1375to the I/O processor1325.
Entertainment system1300may be an electronic game console. Alternatively, the entertainment system1300may be implemented as a general-purpose computer, a set-top box, a hand-held game device, a tablet computing device, a virtual reality device, an augmented reality device, or a mobile computing device or phone. Entertainment systems may contain more or less operating components depending on a particular form factor, purpose, or design.
The CPU1310, the vector unit1315, the graphics processing unit1320, and the I/O processor1325ofFIG.13communicate via a system bus1385. Further, the CPU1310ofFIG.13communicates with the main memory1305via a dedicated bus1380, while the vector unit1315and the graphics processing unit1320may communicate through a dedicated bus1390. The CPU1310ofFIG.13executes programs stored in the OS ROM1355and the main memory1305. The main memory1305ofFIG.13may contain pre-stored programs and programs transferred through the I/O Processor1325from a CD-ROM, DVD-ROM, or other optical disc (not shown) using the optical disc control unit1370. I/O Processor1325ofFIG.13may also allow for the introduction of content transferred over a wireless or other communications network (e.g., 4G, LTE, 1G, and so forth). The I/O processor1325ofFIG.13primarily controls data exchanges between the various devices of the entertainment system1300including the CPU1310, the vector unit1315, the graphics processing unit1320, and the peripheral interface1335.
The graphics processing unit1320ofFIG.13executes graphics instructions received from the CPU1310and the vector unit1315to produce images for display on a display device (not shown). For example, the vector unit1315ofFIG.13may transform objects from three-dimensional coordinates to two-dimensional coordinates, and send the two-dimensional coordinates to the graphics processing unit1320. Furthermore, the sound processing unit1360executes instructions to produce sound signals that are outputted to an audio device such as speakers (not shown). Other devices may be connected to the entertainment system1300via the USB interface1345, and the communication network interface1350such as wireless transceivers, which may also be embedded in the system1300or as a part of some other component such as a processor.
A user of the entertainment system1300ofFIG.13provides instructions via the peripheral interface1335to the CPU1310, which allows for use of a variety of different available peripheral devices (e.g., controllers) known in the art. For example, the user may instruct the CPU1310to store certain game information on the memory card1340or other non-transitory computer-readable storage media or instruct a character in a game to perform some specified action.
The present disclosure pertain to an application that may be operable by a variety of end user devices. For example, an end user device may be a personal computer, a home entertainment system (e.g., Sony PlayStation2® or Sony PlayStation3® or Sony PlayStation4® or Sony PlayStation5®), a portable gaming device (e.g., Sony PSP® or Sony Vita®), or a home entertainment system of a different albeit inferior manufacturer. The present methodologies described herein are fully intended to be operable on a variety of devices. Aspects of the present disclosure may also be implemented with cross-title neutrality and/or may be utilized across a variety of titles from various publishers.
Aspects of the present disclosure may be implemented in an application that may be operable using a variety of devices. Non-transitory computer-readable storage media refer to any medium or media that participate in providing instructions to a central processing unit (CPU) for execution. Such media can take many forms, including, but not limited to, non-volatile and volatile media such as optical or magnetic disks and dynamic memory, respectively. Common forms of non-transitory computer-readable media include, for example, a floppy disk, a flexible disk, a hard disk, magnetic tape, any other magnetic medium, a CD-ROM disk, digital video disk (DVD), any other optical medium, RAM, PROM, EPROM, a FLASHEPROM, and any other memory chip or cartridge.
Various forms of transmission media may be involved in carrying one or more sequences of one or more instructions to a CPU for execution. A bus carries the data to system RAM, from which a CPU retrieves and executes the instructions. The instructions received by system RAM can optionally be stored on a fixed disk either before or after execution by a CPU. Various forms of storage may likewise be implemented as well as other network interfaces and network topologies to implement the same.
In some aspects of the present disclosure, computer-readable storage devices, mediums, and memories can include a cable or wireless signal containing a bit stream and the like. However, when mentioned, non-transitory computer-readable storage media expressly exclude media such as energy, carrier signals, electromagnetic waves, and signals per se.
The foregoing detailed description of the technology has been presented for purposes of illustration and description. It is not intended to be exhaustive or to limit the technology to the precise form disclosed. Many modifications and variations are possible in light of the above teaching. The described aspects of the present disclosure were chosen in order to adequately explain the principles of the technology, its practical application, and to enable others skilled in the art to utilize the technology along with various modifications as are suited to the particular use contemplated. It is intended that the scope of the technology be defined by the claim.
Claims
- A system of in-stream digital asset usability for automated game stream modifications, the system comprising: a memory that stores instructions and a data structure;a communication interface that streams a game stream associated with a video game over a communication network to a first video game console;and a processor that executes instructions stored in memory to: generate a smart contract that is executable to automatically transfer in-stream usability of a digital asset when a trigger condition is met, wherein the smart contract is included within a payload of a most recent block of a distributed ledger;verify that the most recent block of the distributed ledger indicates that the first video game console has authorization from a video game platform to use the digital asset within the game stream during a first time period and that a second video game console lacks authorization from the video game platform to use the digital asset within the game stream during the first time period;generate a display of a portion of the game stream that includes an image depicting the digital asset during the first time period of gameplay by the first video game console in accordance with the first video game console having the authorization, wherein generating the display includes importing the image of the digital asset into the portion of the game stream;track gameplay activity data of the first video game console in the data structure, the gameplay activity data regarding use of the digital asset to modify gameplay depicted within the game stream during the first time period;verify that the data structure includes the tracked gameplay activity data indicating that the trigger condition of the smart contract is met based on a detected interaction between the first video game console and the second video game console through the video game platform;automatically execute the smart contract to initiate an automatic transfer of the in-stream usability of the digital asset, wherein the automatic transfer includes: generating a new block to append to the distributed ledger, wherein a payload of the new block reflects transfer of token information representing the digital asset from a first account associated with the first video game console to a second account associated with the second video game console, the token information including data corresponding to the image, deleting an instance of the digital asset stored at the first video game console in accordance with the new block, wherein deleting the instance is associated with automatically disabling the authorization provided by the video game platform for the first video game console to use the digital asset, wherein the first video game console is no longer authorized to use the image of the digital asset within the game stream during a second time period after the first time period in accordance with the disabled authorization, and generating a display of a second portion of the game stream that includes the image depicting the digital asset during the second time period of gameplay by the second video game console, wherein generating the display is associated with automatically enabling the authorization from the video game platform for the second video game console to use the digital asset, wherein the second video game console is authorized to use the image of the digital asset for gameplay within the game stream during the second time period in accordance with the enabled authorization;and track, in the data structure, further gameplay activity involving the digital asset based on use by the second video game console of the digital asset to modify gameplay depicted within the game stream during the second time period;wherein the communication interface streams the portion of the game stream during the second time period from the video game platform to the second video game console, and wherein the second video game console imports the image into the portion of the game stream for gameplay using the digital asset during the second time period.
- The system of claim 1, wherein the digital asset is an instance of the video game.
- The system of claim 1, wherein the digital asset includes in-game content associated with the video game, wherein the in-game content is usable by a player of the video game within the video game during gameplay of the video game by the player through the video game platform, wherein the player is associated with at least one of the first video game console or the second video game console.
- The system of claim 1, wherein the verification that the data structure includes the tracked gameplay activity data indicating that the trigger condition is met includes a confirmation for the transfer from the first video game console.
- The system of claim 1, wherein verifying that the data structure includes the tracked gameplay activity data indicating that the trigger condition is met is further based on an indication of a second automatic transfer of a second asset from an account associated with the second video game console, wherein the second automatic transfer is in exchange for the transfer of usability of the digital asset.
- The system of claim 5, wherein the second asset is an amount of funds.
- The system of claim 5, wherein the execution of the instructions by the processor causes the processor to: receive a bid from the second video game console for the second asset;and receive an acceptance of the bid from the first video game console.
- The system of claim 6, wherein execution of the instructions by the processor causes the processor to: identify an appraisal value associated with the automatic transfer of usability of the digital asset, wherein the amount of funds is based on the appraisal value.
- The system of claim 1, wherein the execution of the instructions by the processor causes the processor to: identify a characteristic of a first user associated with the first video game console;identify a plurality of characteristics of a plurality of users, wherein the plurality of users includes a second user associated with the second video game console;identify, based on a comparison between the characteristic of the first user and the plurality of characteristics of the plurality of users, that the second user shares the characteristic of the first user;and select the second video game console for the automatic transfer of usability of the digital asset based on the characteristic being shared by the first user and the second user.
- The system of claim 1, wherein the execution of the instructions by the processor causes the processor to: identify a second asset associated with the video game, wherein the second digital asset is associated with a second video game platform that a third video game console belongs to, wherein the third video game console lacks authorization from the second video game platform to use the second digital asset for gameplay on the second video game platform during the first time period;and in response to the verification that the data structure includes the tracked gameplay activity data indicating that the trigger condition is met, automatically enable the authorization from the second video game platform for the third video game console to use the second digital asset for gameplay on the second video game platform during the second time period.
- The system of claim 10, wherein the second asset is a variant of the digital asset that is usable on the second video game platform, wherein the digital asset is usable on the first video game platform, wherein the first video game console and the third video game console are both associated with a user.
- The system of claim 1, wherein execution of the instructions by the processor causes the processor to: identify that a type of the digital asset matches a specified type indicated in a rule;automatically request authorization from a user device for the automatic transfer of usability of the digital asset;and receive the authorization for the user device, wherein verifying that the data structure includes the tracked gameplay activity data indicating that the trigger condition is met is further based on the authorization from the user device.
- The system of claim 12, wherein the user device is associated with at least one of a first user or a family member of a first user, wherein the first user is associated with the first video game console.
- The system of claim 1, wherein the distributed ledger includes a plurality of blocks, wherein each block of at least a subset of the plurality of blocks includes a hash of at least a portion of another block of the plurality of blocks, wherein the new block includes a hash of at least a portion of one the plurality of blocks in the distributed ledger.
- The system of claim 1, wherein the execution of the instructions by the processor causes the processor to generate at least a portion of the most recent block.
- The system of claim 1, wherein the distributed ledger is a blockchain ledger.
- The system of claim 1, wherein the token information is associated with a non-fungible token (NFT).
- The system of claim 1, wherein the distributed ledger includes at least one reference to off-chain data external to the distributed ledger.
- A method of in-stream digital asset usability for automated game stream modifications, the method comprising: streaming a game stream associated with a video game over a communication network to a first video game console during a first time period;generating a smart contract that is executable to automatically transfer in-stream usability of a digital asset when a trigger condition is met, wherein the smart contract is included within a payload of a most recent block of a distributed ledger;verifying that the most recent block of the distributed ledger also indicates that the first video game console has authorization from a video game platform to use a digital asset for gameplay within the game stream during the first time period and that a second video game console lacks authorization from the video game platform to use the digital asset within the game stream during the first time period;generating a display of a portion of the game stream that includes an image depicting the digital asset during the first time period of gameplay by the first video game console in accordance with the first video game console having the authorization, wherein generating the display includes importing the image of the digital asset into the portion of the game stream;tracking gameplay activity data of the first video game console in the data structure, the gameplay activity data regarding use of the digital asset to modify gameplay depicted within the game stream during the first time period;verifying that the data structure includes the tracked gameplay activity data indicating that the trigger condition of the smart contract is met based on a detected interaction between the first video game console and the second video game console through the video game platform;automatically executing the smart contract to initiate an automatic transfer of the in-stream usability of the digital asset, wherein the automatic transfer includes: generating a new block to append to the distributed ledger, wherein a payload of the new block reflects transfer of token information representing the digital asset from a first account associated with the first video game console to a second account associated with the second video game console, the token information including data corresponding to the image, deleting an instance of the digital asset stored at the first video game console in accordance with the new block, wherein deleting the instance is associated with automatically disabling the authorization provided by the video game platform for the first video game console to use the digital asset, wherein the first video game console is no longer authorized to use the image of the digital asset within the game stream during a second time period after the first time period in accordance with the disabled authorization, and generating a display of a second portion of the game stream that includes the image depicting the digital asset during the second time period of gameplay by the second video game console, wherein generating the display is associated with automatically enabling the authorization from the video game platform for the second video game console to use the digital asset, wherein the second video game console is authorized to use the image of the digital asset within the game stream during the second time period in accordance with the enabled authorization;tracking, in the data structure, further gameplay activity involving the digital asset based on use by the second video game console of the digital asset to modify gameplay depicted within the game stream during the second time period;and streaming the portion of the game stream during the second time period from the video game platform to the second video game console, and wherein the second video game console imports the image into the portion of the game stream for gameplay using the digital asset during the second time period.
- A non-transitory computer-readable storage medium having embodied thereon a program, wherein the program is executable by a processor to perform a method of in-stream digital asset usability for automated game stream modifications, the method comprising: streaming a game stream associated with a video game over a communication network to a first video game console during a first time period;generating a smart contract that is executable to automatically transfer in-stream usability of a digital asset when a trigger condition is met, wherein the smart contract is included within a payload of a most recent block of a distributed ledger;verifying that the most recent block of the distributed ledger also indicates that the first video game console has authorization from a video game platform to use a digital asset for gameplay within the game stream during the first time period and that a second video game console lacks authorization from the video game platform to use the digital asset within the game stream during the first time period;generating a display of a portion of the game stream that includes an image depicting the digital asset during the first time period of gameplay by the first video game console in accordance with the first video game console having the authorization, wherein generating the display includes importing the image of the digital asset into the portion of the game stream;tracking gameplay activity data of the first video game console in a data structure, the gameplay activity data regarding use of the digital asset to modify gameplay depicted within the game stream during the first time period;verifying that the data structure includes the tracked gameplay activity data indicating that the trigger condition of the smart contract is met based on a detected interaction between the first video game console and the second video game console through the video game platform;automatically executing the smart contract to initiate an automatic transfer of the in-stream usability of the digital asset, wherein the automatic transfer includes: generating a new block to append to the distributed ledger, wherein a payload of the new block reflects transfer of token information representing the digital asset from a first account associated with the first video game console to a second account associated with the second video game console, the token information including data corresponding to the image, deleting an instance of the digital asset stored at the first video game console in accordance with the new block, wherein deleting the instance is associated with automatically disabling the authorization provided by the video game platform for the first video game console to use the digital asset, wherein the first video game console is no longer authorized to use the image of the digital asset within the game stream during a second time period after the first time period in accordance with the disabled authorization, and generating a display of a second portion of the game stream that includes the image depicting the digital asset during the second time period of gameplay by the second video game console, wherein generating the display is associated with automatically enabling the authorization from the video game platform for the second video game console to use the digital asset, wherein the second video game console is authorized to use the image of the digital asset within the game stream during the second time period in accordance with the enabled authorization;tracking, in the data structure, further gameplay activity involving the digital asset based on use by the second video game console of the digital asset to modify gameplay depicted within the game stream during the second time period;and streaming the portion of the game stream during the second time period from the video game platform to the second video game console, and wherein the second video game console imports the image into the portion of the game stream for gameplay using the digital asset during the second time period.
Disclaimer: Data collected from the USPTO and may be malformed, incomplete, and/or otherwise inaccurate.