U.S. Pat. No. 12,265,596
VIDEO GAME INTEGRATION OF CRYPTOGRAPHICALLY SECURED DIGITAL ASSETS
AssigneeNIKE, Inc.
Issue DateDecember 13, 2023
Illustrative Figure
Abstract
A method of integrating a cryptographic digital asset into a digital software application, includes receiving a digital asset identification (ID) code, the digital asset ID code existing together with a unique owner ID code on a distributed blockchain ledger. The digital asset ID code represents the cryptographic digital asset, and the cryptographic digital asset comprises a plurality of attributes. A virtual object is then represented on the display via the digital software application. The virtual object has an appearance that is based on the plurality of attributes of the cryptographic digital asset, and the virtual object includes a plurality of object attributes. The method further includes modifying at least one of the object attributes according to an aspect of the digital software application or interaction between the character avatar and the virtual object and representing a modified virtual object on the display via the digital software application.
Description
The present disclosure is amenable to various modifications and alternative forms, and some representative embodiments are shown by way of example in the drawings and will be described in detail herein. It should be understood, however, that the novel aspects of this disclosure are not limited to the particular forms illustrated in the above-enumerated drawings. Rather, the disclosure is to cover all modifications, equivalents, combinations, subcombinations, permutations, groupings, and alternatives falling within the scope of this disclosure as encompassed by the appended claims. DETAILED DESCRIPTION This disclosure is susceptible of embodiment in many different forms. Representative examples of the disclosure are shown in the drawings and will be described in detail herein with the understanding that these representative examples are provided as an exemplification of the disclosed principles, not limitations of the broad aspects of the disclosure. To that extent, elements and limitations that are described in the Abstract, Technical Field, Background, Summary, and Detailed Description sections, but not explicitly set forth in the claims, should not be incorporated into the claims, singly or collectively, by implication, inference or otherwise. For purposes of the present detailed description, unless specifically disclaimed: the singular includes the plural and vice versa; the words “and” and “or” shall be both conjunctive and disjunctive; the words “any” and “all” shall both mean “any and all”; and the words “including,” “comprising,” “having,” “containing,” and the like shall each mean “including without limitation.” Moreover, words of approximation, such as “about,” “almost,” “substantially,” “approximately,” and the like, may be used herein in the sense of “at, near, or nearly at,” or “within 0-5% of,” or “within acceptable manufacturing tolerances,” or any logical combination thereof, for example. Lastly, directional adjectives and adverbs, such as fore, aft, medial, lateral, proximal, distal, vertical, horizontal, front, back, left, right, etc., may be ...
The present disclosure is amenable to various modifications and alternative forms, and some representative embodiments are shown by way of example in the drawings and will be described in detail herein. It should be understood, however, that the novel aspects of this disclosure are not limited to the particular forms illustrated in the above-enumerated drawings. Rather, the disclosure is to cover all modifications, equivalents, combinations, subcombinations, permutations, groupings, and alternatives falling within the scope of this disclosure as encompassed by the appended claims.
DETAILED DESCRIPTION
This disclosure is susceptible of embodiment in many different forms. Representative examples of the disclosure are shown in the drawings and will be described in detail herein with the understanding that these representative examples are provided as an exemplification of the disclosed principles, not limitations of the broad aspects of the disclosure. To that extent, elements and limitations that are described in the Abstract, Technical Field, Background, Summary, and Detailed Description sections, but not explicitly set forth in the claims, should not be incorporated into the claims, singly or collectively, by implication, inference or otherwise.
For purposes of the present detailed description, unless specifically disclaimed: the singular includes the plural and vice versa; the words “and” and “or” shall be both conjunctive and disjunctive; the words “any” and “all” shall both mean “any and all”; and the words “including,” “comprising,” “having,” “containing,” and the like shall each mean “including without limitation.” Moreover, words of approximation, such as “about,” “almost,” “substantially,” “approximately,” and the like, may be used herein in the sense of “at, near, or nearly at,” or “within 0-5% of,” or “within acceptable manufacturing tolerances,” or any logical combination thereof, for example. Lastly, directional adjectives and adverbs, such as fore, aft, medial, lateral, proximal, distal, vertical, horizontal, front, back, left, right, etc., may be with respect to an article of footwear when worn on a user's foot and operatively oriented with a ground-engaging portion of the sole structure seated on a flat surface, for example.
Aspects of this disclosure are directed to computer-generated virtual collectibles, such as digital shoes (e.g., “CryptoKicks”), that, in some instances, are linked with real-world, physical products, such as tangible shoes, and are protected by cryptographic tokens. In some embodiments, instead of being linked with real-world, physical products, the digital asset may be linked with a 2D or 3D design file, rendering, or drawing package from which a physical product may be constructed. In this embodiment, a company may create a number of product-ready designs with different traits, silhouettes, colors, and the like, and may distribute them across one or more digital platforms, and may then monitor the popularity, value, demand, and/or virtual use, of different product designs and/or traits. In doing so, the company may gain a valuable understanding of the real-time demand for a product, which may be helpful when prioritizing of designs for future manufacturing.
In some embodiments, a digital asset may be created for brand promotion purposes. In this embodiment, a digital shoe may be created in a preset and/or controlled limited quantity and distributed as part of a promotion, event, moment, or contest. For example, spectators at a professional sporting home opener may give the right to acquire one of a limited quantity of unique digital assets, each being separately secured via its own cryptographic token.
As used herein, “cryptographic digital assets,” or simply “digital assets” may refer to any computer-generated virtual object, including digital footwear, apparel, headgear, avatars, pets, etc., that have a unique, non-fungible tokenized code (“token”) registered on and validated by a blockchain platform or otherwise registered in an immutable database. Furthermore all references to “CryptoKicks” and variations of the term within this disclosure should be understood to be exemplary of a virtual collectible backed by a unique, non-fungable token or registry entry within an immutable database. It should not be limiting to only footwear. All such references should be read to equally apply to apparel (e.g., “CryptoThreads”), headgear (e.g., “CryptoLids”), and sporting equipment (e.g., “CryptoGear”), or other such objects.
In some embodiments, the virtual object may have a plurality of attributes (i.e., phenotypic traits) that are at least partially derived from an encrypted alphanumeric string may be associated with the cryptographic token. In this sense, the alphanumeric string may be akin to the genetic code of the virtual object. While the phenotypic traits may depend on the encoded genotypic information, in some embodiments, they may further depend on any one or more of: a virtual environment (e.g., virtual check-ins, situation-specific criterion, etc.); time-dependent breeding (e.g., a user is restricted from breeding a virtual shoe offspring until it reaches a preset maturity); virtual user interactions, which may speed up or slow down maturity or increase/decrease a likelihood of certain traits developing; real-world user activities (e.g., user's level of physical activity may increase one or more “desirable” qualities; daily use of a related good speeds up maturing of virtual offspring, etc.); cloning restrictions set by manufacturer, point of sale, owner, etc., (e.g., preset maximum number of clones that can be produced from a desirable offspring for actual real-world production).
In a footwear context, each unique token may be directly linked to a single CryptoKick object, which may be embodied as a virtual reproduction or digital-art version of a sneaker. In one embodiment, the token may include a 64-bit alphanumeric code that is sectioned into individual code segments. One or more or all of the code segments of the alphanumeric code may express data indicative of attributes of the collectible digital shoe. For instance, a series of code segments may provide digital shoe attributes, such as Style, Materials, Family, Heat, Colorway, Future Attributes, Make, Model, Pattern Scheme, Image Background, etc. Each subset of a code may generally function as a genotype that produces a visual phenotype expression to the user. In some embodiments, an originally created CryptoKick may include cryptographic token data that is representative of attributes from a companion physical shoe. During the creation of a CryptoKick, a smart contract may be generated to authenticate ownership and to track future transaction of the CryptoKick. Digital shoe attributes may also be linked to a bill of materials.
In a representative example, an authenticated pair of physical shoes are created and assigned a Unique Product Identifier (UPID). Upon purchase by a consumer, the UPID is used to unlock a cryptographic digital asset—a “CryptoKick”—composed of a collectible digital shoe and a unique non-fungible token (NFT) operating on a blockchain-based distributed computing platform.
In general, before a consumer can unlock or acquire a CryptoKick, they may first be required to procure a blockchain locker address (e.g., an Ethereum hardware wallet). This blockchain locker may be used to store the private key belonging to the CryptoKick's NFT and, optionally, may be linked to a personal user account that is registered with the original manufacturer of the physical shoes (e.g., a NIKEPLUS® account profile).
It is envisioned that there are several ways in which a user may be enabled to unlock a CryptoKick. As a first example, upon scanning the shoe's UPC or UPID at a point-of-sale (POS) terminal during first purchase or directly associated with the product, a unique crypto-token and corresponding private key (“KickID”) are automatically generated and assigned to the user's blockchain locker (seeFIG.7). In a second example, a KickID is provided to the user via a printed or digital receipt, a visual or electronic tag (RFID or NFC) hidden in the physical shoe, a pop-up message or email sent to a personal user account, a push notification or text message sent to a smartphone, or some other record; the consumer uses the KickID to link the CryptoKick to their digital blockchain locker. Another example may require the user to assemble the KickID in part via a physical code or UPID associated with the shoe (on the box, on a hang tag, under a label, on an insole, etc.), and in part via a transaction authentication code (i.e., to prevent consumers from collecting a CryptoKick when they merely try on a pair of shoes). Another example may require the user to “hunt” for CryptoKicks in a brick-and-mortar store by using a photographic “snap” or augmented reality (“AR”) function on a handheld personal computing device. For this method, a KickID may be provided via the retail transaction, however, the user must separately find a hidden CryptoKick in AR hidden within the store or local area before the digital asset can be transferred to their locker (i.e., the cryptographic key and the virtual object must both be separately acquired before the transfer occurs). In this example, obtaining the cryptographic key may enable the AR engine associated with a user device to initiate a game where the CryptoKick/virtual object associated with that key is locally hidden and available for the user to locate.
In some instances, the CryptoKick may not be originally linked to a physical product, but instead may be gifted to the user as part of a brand promotion campaign, event, moment, or experience. In one example, such as generally illustrated inFIG.8, a user at a sporting event may be required to hunt for the CryptoKick within the confines of the event using the camera on a smartphone device. In this embodiment, the GPS associated with the smartphone device may further constrain optical recognition capabilities to within a particular geofenced area. Once the CryptoKick is located (e.g., virtually disguised in a billboard advertisement), the user may be prompted to scan a unique code, such as the barcode on their ticket to the event. This two-part action may then transfer a token uniquely provisioned for that ticket to the user's locker. Following the event, the promotion organizer may reclaim any unclaimed KickIDs for subsequent use in other promotional events.
After acquiring a CryptoKick, the owner may buy, sell, intermingle, collect, or trade CryptoKicks, e.g., using physical, fiat, and/or digital currency. In some examples, an entity may maintain a digital online marketplace that includes an inventory of CryptoKicks for sale and/or a marketplace that may broker transactions between individuals.
In one embodiment, it may be possible to breed or mashup (“Collab”) two CryptoKicks to create an offspring CryptoKick (an “RVK” or “CollaboKick”). This CollaboKick will have a unique token and distinct attributes compared to the parent CryptoKicks. A Collab may combine attribute data and/or genetic code from the two tokens of the parents to generate a new NFT or KickID that, in turn, provisions a CollaboKick. In some implementations, there may be a pre-established limitation on the total number of Collab events within a given time limit, e.g., to help prevent overproduction of CollaboKicks between the same two users. The creation of the genetic code for a CollaboKick may be random, systematic, regulated, unconstrained, or any combination thereof. One or more code subsets, for example, may be based on controlled probability using Mendel's Law. For example, if a first attribute code (e.g., molding heat) is expressed as two genes (e.g., HH, Hh or hh), a CollaboKick is considered to have “high heat” if it has two genes that are “hh” (recessive trait). In other words, if genotype data contained in the KickIDs of the CryptoKick parents have Hh as their “heat genes,” the offspring CollaboKick will have a 25% of getting a high heat gene, e.g., using the Punnett square methodology.
The option to execute a Collab event may require one or both owners comply with one or more prerequisite conditions. As one example, the two owners of the parent CryptoKicks may be required to meet at a designated location or be within a predetermined proximity of one another to create a CollaboKick. For example, a user may employ a “CryptoKick Collab” matching feature on a dedicated mobile software application (“app”) to find another user to Collab with. Using this app, the parties may set a time and place to meet, set the conditions of the Collab, submit a formal request to a governing middleware computing node, etc. Another example may include the footwear manufacturer or a third-party sponsor host a Collab event at which CryptoKick owners meet at a designated location to Collab with one another within a specific time frame.
In some embodiments, owners may be provided some indication of the genetic traits of their CryptoKicks to facilitate more deliberate Collab events. In an example, a user may desire a CryptoKick of a particular model in a certain exclusive color. That user may then search out a CryptoKick that has the genetic code for that color and attempt to Collab with them. To further the understanding of a trait's value, in some embodiments, the user may be provided with an indication of the rarity or total circulating supply of each trait that makes up their CryptoKick and/or a rarity score that provides an indication of the overall exclusivity of their CryptoKick. In this manner, if offered for sale on a commercial marketplace, a CryptoKick may carry an intrinsic value that reflects the combined rarity or exclusivity of its various traits.
A predetermined set of intermingling rules may govern if and how a Collab may be executed. For example, certain constraints may be imposed so that broad style guidelines are maintained in the CollaboKick. In one embodiment, these style constrains may be the same constraints or guidelines that a company may use when creating new versions, colorways, or iterations of an existing product line. When a Collab is created, the genetic mixing algorithm may be constrained such that any resultant Collab kick maintains a likeness or silhouette that is indicative of or more existing products. While in one embodiment, these style guidelines or rules may expressly set by the company, in another embodiment, they may be discovered and assembled, for example, using an image-based processing algorithm that may recognize style attributes (e.g., color patterns, material, cut, and/or dimensional patterns) from existing product.
For at least some implementations, a CryptoKick may be programmed to function as a “living” digital pet that the user feeds, cleans, entertains and otherwise cares for to ensure the pet is happy and healthy. Optionally, an owner can either care for the CryptoKick pet by him/herself or have a third-party user care for the CryptoKick pet. As the CryptoKick pet evolves—growing from a baby digital pet to a toddler, then preschooler, and so forth to adulthood—one or more attributes of the CryptoKick automatically change with age or are unlocked over time. Furthermore, as the CryptoKick pet “grows” through various life stages, it may unlock a real-life shoe version of itself that a user can have made. For example, if a CryptoKick pet has evolved into a royal blue athletic shoe for a toddler, the user has unlocked the option to buy a special royal blue athletic shoe in one or more toddler sizes.
In some implementations, a user's CryptoKick may be capable of being imported into one or more other digital platforms to serve, for example, as a skin on a video game character that may be developed and/or controlled by the user. For example, if the user was active in a certain basketball video game, the CryptoKick could be imported to that game and worn by the user's player or team.
If the CryptoKick is imported into a separate video game, in some configurations, different attributes of the CryptoKick may impart changes in the ability level of a user's character outfitted with the asset. In one example, the attributes of the user's character may be positively influenced by the rarity or exclusivity of the various attributes or by the overall combined rarity or exclusivity. For example, a rare CryptoKick may impart better jumping ability or lateral quickness, a rare CryptoThread may impart better strength or speed, and a rare CryptoLid may impart better vision.
In some embodiments, CryptoKicks users may decide on a “best CollaboKick” in the marketplace, e.g., on a W/M/Q/Y basis. Such a voting scheme may be used to designate one or more CollaboKicks as suitable for the commercial production of physical product bearing that digital asset's likeness. As a further option, a CollaboKick that may receive a preset threshold number of upvotes may automatically trigger the manufacturer to produce the CollaboKick in real life.
As CryptoKicks and CollaboKicks are transferred between users over time due to selling, trading, buying, and Collab, each transaction history may be tracked within a blockchain ledger of transactions. If a CollaboKick or CryptoKick is fabricated, previous users may be notified of such real-life existence and will may be given an option to purchase their own real-life pair of the CollaboKick/CryptoKick.
As a further extension, in one embodiment, CryptoKicks may be backed by fungible tokens, where the digital collectible represents a monetary value. In one implementation, certain attributes within the code assigned to the token may dictate the worth. For example, a style attribute indicative of a high-top sneaker, may have a first value, a style attribute indicative of yoga pants may have a second value, and a style attribute indicative of a running shirt may have a third value. In one embodiment, these values may either be allowed to float according to market forces, or may be tied to a fiat currency.
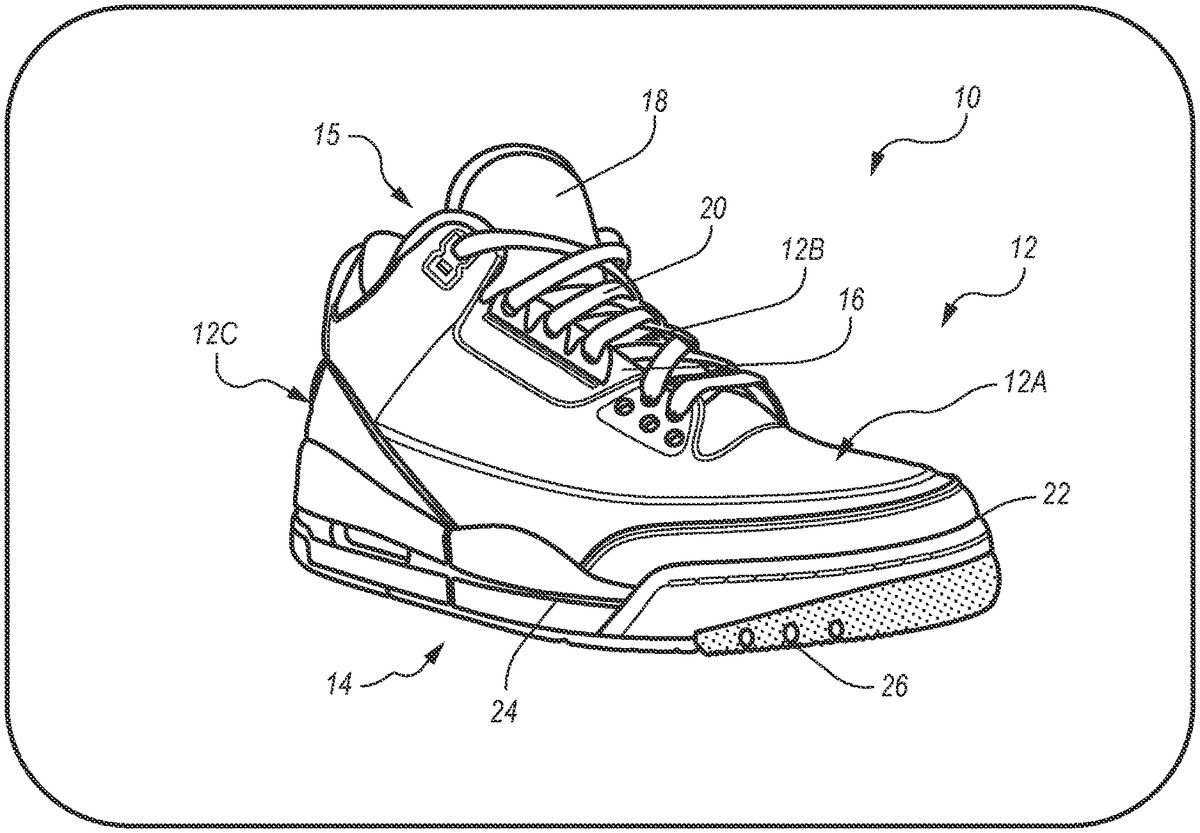
Referring now to the drawings, wherein like reference numbers refer to like features throughout the several views, there is shown inFIG.1a representative article of footwear, which is designated generally at10and portrayed herein for purposes of discussion as an athletic shoe or “sneaker.” The illustrated article of footwear10—also referred to herein as “footwear” or “shoe” for brevity—is merely an exemplary application with which novel aspects and features of this disclosure may be practiced. In one embodiment, the illustrated article of footwear10may be or resemble a CryptoKick. In the same vein, implementation of the present concepts for a digital shoe and cryptographic token for footwear should also be appreciated as a representative implementation of the disclosed concepts. It will therefore be understood that aspects and features of this disclosure may be utilized for other types of footwear, and may be incorporated into any logically relevant consumer product. As used herein, the terms “shoe” and “footwear,” including permutations thereof, may be used interchangeably and synonymously to reference any suitable type of garment worn on a human foot. Lastly, features presented in the drawings are not necessarily to scale and are provided purely for instructional purposes. Thus, the specific and relative dimensions shown in the drawings are not to be construed as limiting.
The representative article of footwear10is generally depicted inFIG.1as a bipartite construction that is primarily composed of a foot-receiving upper12mounted on top of a subjacent sole structure14. While only a single shoe10for a left foot of a user is shown inFIG.1, a mirrored, substantially identical counterpart for a right foot of a user may be provided. Recognizably, the shape, size, material composition, and method of manufacture of the shoe10may be varied, singly or collectively, to accommodate practically any conventional or nonconventional footwear application.
With continued reference toFIG.1, the upper12is depicted as having a shell-like, closed toe and heel configuration for encasing a human foot. Upper12ofFIG.1is generally defined by three adjoining sections, namely a toe box12A, a vamp12B and a rear quarter12C. The toe box12A is shown as a rounded forward tip of the upper12that extends from distal to proximal phalanges to cover and protect the user's toes. By comparison, the vamp12B is an arched midsection of the upper12that is located aft of the toe box12A and extends from the metatarsals to the cuboid. As shown, the vamp12B also provides a series of lace eyelets16and a shoe tongue18. Positioned aft of the vamp12B is a rear quarter12C that extends from the transverse tarsal joint to the calcaneus bone, and includes the rear portions of the upper12. While portrayed in the drawings as comprising three primary segments, the upper12may be fabricated as a single-piece construction or may be composed of any number of segments, including a toe cap, heel cap, ankle cuff, interior liner, etc. For sandal and slipper applications, the upper12may take on an open toe or open heel configuration, or may be replaced with a single strap or multiple interconnected straps.
The upper12portion of the footwear10may be fabricated from any one or combination of a variety of materials, such as textiles, engineered foams, polymers, natural and synthetic leathers, etc. Individual segments of the upper12, once cut to shape and size, may be stitched, adhesively bonded, fastened, welded or otherwise joined together to form an interior void for comfortably receiving a foot. The individual material elements of the upper12may be selected and located with respect to the footwear10in order to impart desired properties of durability, air-permeability, wear-resistance, flexibility, appearance, and comfort, for example. An ankle opening15in the rear quarter12C of the upper12provides access to the interior of the shoe10. A shoelace20, strap, buckle, or other conventional mechanism may be utilized to modify the girth of the upper12to more securely retain the foot within the interior of the shoe10as well as to facilitate entry and removal of the foot from the upper12. Shoelace20may be threaded through a series of eyelets16in or attached to the upper12; the tongue18may extend between the lace20and the interior void of the upper12.
Sole structure14is rigidly secured to the upper12such that the sole structure14extends between the upper12and a support surface upon which a user would stand. The sole structure14may be fabricated as a sandwich structure with a top-most insole22, an intermediate midsole24, and a bottom-most outsole26or outsole surface. Alternative sole configurations may be fabricated with greater or fewer than three layers. Insole22is shown located partially within the interior void of the footwear10, operatively attached at a lower portion of the upper12, such that the insole22abuts a plantar surface of the foot. Underneath the insole22is a midsole24that incorporates one or more materials or embedded elements that enhance the comfort, performance, and/or ground-reaction-force attenuation properties of footwear10. These elements and materials may include, individually or in any combination, a polymer foam material, such as polyurethane or ethylvinylacetate (EVA), filler materials, moderators, air-filled bladders, plates, lasting elements, or motion control members. Outsole26is located underneath the midsole24, defining some or all of the bottom-most, ground-engaging portion of the footwear10. The outsole26may be formed from a natural or synthetic rubber material that provides a durable and wear-resistant surface for contacting the ground. In addition, the outsole26may be contoured and textured to enhance the traction (i.e., friction) properties between footwear10and the underlying support surface.
As a general matter, each element, panel, section, and material of the article of footwear10shown inFIG.1may be separately rendered or defined in a digital CryptoKick. Furthermore, these attributes may similarly be reflected within the genetic code of the NFT, as discussed above.
FIG.2is a diagrammatic illustration of an exemplary decentralized computing system, designated generally as30, with attendant blockchain control logic for mining, intermingling, and exchanging blockchain-enabled digital collectibles. User11communicatively couples to a remote host system34and/or a cloud computing system36via a wireless communications network38. While illustrating a single user11communicating over the decentralized computing system30with a single host system34and a single cloud computing system36, it is envisioned that any number of users may communicate with any number of remote computing nodes that are suitably equipped for wirelessly exchanging information and data. Wireless data exchanges between the user11and remote computing nodes on the decentralized computing system30may be conducted directly, e.g., through direct communications between the host system34/cloud computing system36and a user device39(e.g., the user's smartphone40, smartwatch42, or other suitable personal computing device), or indirectly, e.g., with all communications between the user11and other computing nodes being routed through the host system34. Only select components of the decentralized computing10and decentralized computing system30are shown and will be described in detail herein. Nevertheless, the systems and devices discussed herein can include numerous additional and alternative features, and other available hardware and well-known peripheral components, for example, for carrying out the various methods and functions disclosed herein. While the described system relies on a blockchain ledger and process for recording ownership of the digital asset, it should be understood that the present technology may operate on a public chain or a private chain, and may utilize one or more forms of cryptography, encoding, proof of work challenges, or other concepts and technologies involved in available blockchain standards or suitable alternative immutable databases/ledgers.
With continuing reference toFIG.2, the host system34may be implemented as a high-speed server computing device or a mainframe computer capable of handling bulk data processing, resource planning, and transaction processing. For instance, the host system34may operate as middleware in a client-server interface for conducting any necessary data exchanges and communications with one or more “third party” servers to complete a particular transaction. The cloud computing system36, on the other hand, may operate as middleware for IoT (Internet of Things), WoT (Web of Things), Internet of Adaptive Apparel and Footwear (IoAAF), and/or M2M (machine-to-machine) services, connecting an assortment of heterogeneous electronic devices with a service-oriented architecture (SOA) via a data network. As an example, cloud computing system36may be implemented as a middleware node to provide different functions for dynamically onboarding heterogeneous devices, multiplexing data from each of these devices, and routing the data through reconfigurable processing logic for processing and transmission to one or more destination applications. Network38may be any available type of network, including a combination of public distributed computing networks (e.g., Internet) and secured private networks (e.g., local area network, wide area network, virtual private network). It may also include wireless and wireline transmission systems (e.g., satellite, cellular network, terrestrial networks, etc.). Most if not all data transaction functions carried out by the user11may be conducted, for example, over a wireless network, such as a wireless local area network (WLAN) or cellular data network.
As a decentralized blockchain platform, computing system30operates as an open, yet encrypted peer-to-peer network in which asset transaction records—known as “blocks”—are linked via cryptographic hash functions in a distributed, immutable ledger of interconnected blocks, i.e., a “blockchain.” Each block in the chain includes one or more digital asset transactions accompanied by corroboration information representing a validity of each transaction as assessed by peer-validation devices. Encrypted, decentralized computing architectures allow for identity verification and authentication of transacted assets while preventing duplication of a cryptography-protected (“cryptographic”) digital asset registered to the platform. Decentralized asset management may work by encrypting a proprietary asset file, breaking the encrypted code into tiny “nonsense” shards, and sending these shards to numerous different computing nodes on the decentralized computing network. A validated owner is provided with a private key that indicates where in the network the asset is located and how to reassemble or “decrypt” the file. For use as a distributed ledger, an individual blockchain is typically managed by a host administrator and distributed to multiple peers collectively adhering to a protocol for inter-node communication and block validation.
One should appreciate that the disclosed systems and techniques provide many advantageous technical effects including construction and storage of a digital asset blockchain representing user-to-user transactions of virtual collectibles associated with real-world products. Construction and storage of a digital asset blockchain enables networked computing devices to quickly and efficiently generate, validate and transact digital asset data, thereby improving the performance of the individual computing devices. A decentralized network of interconnected computing nodes may function as a “supercomputer” that has access to many parallel processors, coordinating the assignment and reassembly of various chunks of computation. In so doing, the network is more computationally efficient, rapid, and inexpensive than a centralized computing system or a single processing farm. In the same vein, decentralized storage provides each individual computing node with tremendous storage capacity that is limited only by the number of peer devices and their cumulative available memory space.
FIG.3provides one example of the functional structure of a decentralized computing system30, such as shown inFIG.2. As generally illustrated, a user11may operatively interface with a user device39(i.e., interface device39) that may include one or more of a smart phone40, a tablet computer, a smart watch42, a laptop computer, a desktop computer, a standalone video game console, smart footwear/apparel, or other similar internet enabled devices. The interface device39may be operatively configured to communicate with one or more of an immutable public database (e.g., a blockchain service/network60—referred to as “blockchain60”), a virtual object generator62, an online digital marketplace64, and/or a 3rdparty integration service66.
In general, the blockchain60may include at least one non-fungible token registered thereon that includes genomic information representative of a digital asset. The user11, via the user device39, may be in possession of, or may be lined with a locker/wallet that includes a private cryptographic key that permits the user device to read the encrypted data associated with the token. This key may further enable the user11to freely transfer ownership of the token.
In one embodiment, a virtual object generator62may be provided to create a digital object on the basis of the genomic information associated with the token. More specifically, the virtual object generator62may be responsible for expressing the genomic information into a plurality of phenotypic traits. The virtual object generator62may employ a plurality of style and artistic rules such that the resultant digital objects are unique, yet recognizable according to predefined silhouettes, styles, articles, or characters. In some embodiments, the virtual object generator62may further operate on the basis of other non-genomic factors, such as the age of the asset, user activity (tracked via the user device), or use via third party platforms. In such an embodiment, these non-genomic inputs may alter the phenotypic expression, and/or may unlock new abilities, breeding rights, and/or production rights. For example, in one configuration, a color of a CryptoKick may depend on the genetically assigned color, together with the age of the asset and/or use of the asset in a virtual world or via a linked pair of physical shoes in the real world. The initial color together with the age/experience based alteration may result in a new color that has its own relative rarity score/value.
The virtual object generator62and/or blockchain60may further be in communication with a hosted digital marketplace64, forum, social platform, or the like (such as generally shown inFIG.5—displayed on a smartphone40). The digital marketplace64may represent a plurality of virtual objects80in such a manner that permits the organized trade or sale/purchase of the virtual objects between parties. Upon the closing of a sale, the digital marketplace64may update the blockchain60with the new ownership information and facilitate the transfer of new of existing keys to the new asset holder. In some embodiments, the marketplace64may further enable various social engagement functions, such as voting or commenting on the represented virtual objects. Likewise, in some instances the marketplace64may be configured to assess and score the rarity of a particular virtual object based on the sum total of the object's expressed traits. Such a rarity score may then enable the marketplace (and/or users who participate within the marketplace) to better assess the value of the object.
In one configuration, the computing system30may further include a 3rdparty integration service66that may enable the use of the virtual object in different contexts or manners. The 3rdparty integration service66may operate as an API on an app provided on the user's device, or as a dedicated cloud based service. In some embodiments, the 3rd party integration service66may make the virtual object (for example, as expressed by the virtual object generator62), and/or the genomic information available for external use. Examples of such a use may include skins on 3rdparty video game characters, objects capable of being used by 3rdparty video game characters (seeFIG.9), digital artwork displays, physical print generation, manufacturing production, and the like. In one embodiment, the genomic information and/or rarity score may be made available, and may alter the traits or abilities of a user's video game character in a video game played on the user's device39(seeFIG.10).
As further shown inFIG.3, in one configuration, a corporate host system68may be in communication with the blockchain60for the purpose of provisioning/creating new digital assets. Additionally, the host system68may provide one or more rules to the virtual object generator62to constrain the manner and style in which genomic information from the blockchain60is expressed in a visual/artistic form.
With reference now to the flow chart ofFIG.4, an improved method or control strategy for generating collectible digital assets protected by cryptographic tokens on a blockchain ledger is generally described at100in accordance with aspects of the present disclosure. Some or all of the operations illustrated inFIG.4and described in further detail below may be representative of an algorithm that corresponds to processor-executable instructions that may be stored, for example, in main or auxiliary or remote memory, and executed, for example, by a resident or remote controller, central processing unit (CPU), control logic circuit, or other module or device or network of devices, to perform any or all of the above or below described functions associated with the disclosed concepts. It should be recognized that the order of execution of the illustrated operation blocks may be changed, additional blocks may be added, and some of the blocks described may be modified, combined, or eliminated.
Method100begins at terminal block101with processor-executable instructions for a programmable controller or control module or similarly suitable processor to call up an initialization procedure for a protocol to generate a cryptographic digital asset, such as computer-generated digital shoe44and encrypted token key46ofFIG.2, for a consumer product, such as sneaker10ofFIGS.1and2. This routine may be called-up and executed in real-time, continuously, systematically, sporadically, and/or at regular intervals. As a representative implementation of the methodology set forth inFIG.4, the initialization procedure at block101may automatically commence each time a pair of authentic footwear10is manufactured, each time a user11purchases a real-world pair of the footwear10, or each time the user11unlocks the access key46. Alternatively, the initialization procedure may be manually activated by an employee at a POS terminal or by the manufacturer.
Utilizing a portable electronic device39, such as smartphone40or smartwatch42ofFIG.2, the user11may launch a dedicated mobile software application (“app”) or a web-based applet, such as NIKE+®, that collaborates with a server-class (backend or middleware) computer (e.g., remote host system34) to communicate with the various peer devices on decentralized computing system30. During a communication session with the host system34, for example, the user11may purchase a pair of the footwear10using a corresponding feature provisioned by the app. The user11enters personal information and a method of payment to complete the transaction. Upon completion of a validated payment, the host system34receives, e.g., from an online store transaction module or an approved third-party electronic payment system, a transaction confirmation to indicate a validated transfer of the footwear10to the user11has been completed. As indicated above, validated transfer of the footwear10may be effectuated through any available means, including at a brick-and-mortar store, through an online auction website, an aftermarket consumer-to-consumer trade/sale, etc.
Method100continues to decision block103to determine if the user11has procured a cryptocurrency wallet or other similarly suitable digital blockchain locker that is operable, for example, to upload and maintain location and retrieval information for digital assets that are encrypted and stored in a decentralized manner. A cryptocurrency wallet typically stores public and private key pairs, but does not store the cryptocurrency itself; the cryptocurrency is decentrally stored and maintained in a publicly available blockchain ledger. With the stored keys, the owner may digitally sign a transaction and write it to the blockchain ledger. A platform-dictated smart contract associated with the locker may facilitate transfer of stored assets and create a verifiable audit trail of the same. If the user11has not already acquired a digital blockchain locker (Block103=NO), the method100continues to predefined process block105to set up a blockchain locker. By way of non-limiting example, user11may be prompted to visit or may be automatically routed to any of an assortment of publicly available websites that offer a hardware wallet for cold storage of cryptocurrency and digital assets, such an ERC20-compatible Ethereum wallet provided by MyEtherWallet.
Once the system confirms that the user11has a suitable digital blockchain locker, the method100may automatically link, or prompt the user11to link, the digital blockchain locker to a personal user account (e.g., a NIKEPLUS® account profile), as portrayed at process block107ofFIG.4. This may require the remote host system34retrieve a unique owner ID code (e.g., CryptoKick Owner ID48ofFIG.2) associated with the purchasing party (e.g., user11) from an encrypted relational database (e.g., provisioned through cloud computing system36). At this time, a unique physical shoe ID code (CryptoKick Physical ID50ofFIG.2) associated with the purchased footwear10may be linked to the user's personal account.
Upon determining that the user11has acquired a digital blockchain locker (Block103=YES), or after linking the user's blockchain locker to their personal user account (Block107), the method100continues to input/output block109to enable or “unlock” a cryptographic digital asset associated with the footwear10transacted at process block101. As indicated above, after purchasing the footwear10, the CryptoKick Physical ID or a universally recognized UPID product code may be used to retrieve a collectible CryptoKick, which is generally composed of a collectible digital shoe44and a unique NFT that is identified by an encrypted token key46. A salesperson at a POS terminal or the user11employing their smartphone40may scan the UPID or UPC on the shoe10or a box storing therein the shoe10. Alternatively, the user11may be prompted to carry out a “treasure hunt” using a digital camera on their smartphone to scan various UPIDs throughout a brick-and-mortar store until they scan one that is linked to a KickID. Enabling a cryptographic digital asset may be automatic, random, systematic, prize based, or any logically appropriate manner.
After receiving confirmation that a cryptographic digital asset has been authorized at input/output block109, the method100generates a cryptographic digital asset for the transacted article of footwear. This may comprise generating a unique, encrypted asset code with an address, a token, and a public and private key pair, as denoted at predefined process block111. Host system34may transmit the token, with the public key and the owner ID, to a distributed blockchain ledger to record and peer-validate transfer of the cryptographic digital asset to the user11on a transaction block. The method100continues to process block113to link the cryptographic digital asset with the unique owner ID code. This control logic may comprise executable instructions for assigning the encrypted asset code to the user11and storing the public and private keys in the user's digital blockchain locker.
With continuing reference toFIG.4the method100proceeds to process block115to produce the virtual representation or “digital art” of the cryptographic digital asset. Continuing with the footwear example ofFIG.2, the virtual representation may include a computer-generated avatar of the shoe10or a limited-edition artist rendition of the shoe10. It is also envisioned that one or more attributes of the virtual representation of the cryptographic digital asset may be created, in whole or in part, via the user11. A machine learning function may be executed at predefined process block117in order to generate image features through a neural network. Upon completion of the digital art, the image may be uploaded to cloud computing system36at block119. In addition, optional process block121may issue a digital notification, such as an email or push notification, to the user's smartphone40, smartwatch42, or other personal computing device, with all related information for accessing, transferring and intermingling the cryptographic digital asset. The remote host system34may operate as a web server hosting a web-based graphical user interface (GUI) that is operable to translate the data stored in the encryption keys into a visual image that is displayed to the user11at optional process block123. Digital asset manipulation and use may also be effectuated through the user's digital blockchain locker. This may comprise posting the cryptographic digital asset to an online crypto-collectible marketplace for sale or breeding, as provided in optional process block125.
Prospective and current owners of a cryptographic digital asset, such as the CryptoKick ofFIG.2, may buy and sell digital assets through one or more blockchain ledgers operating on the decentralized computing system30. By way of example, and not limitation, a user may buy a new pair of highly sought after sneakers from a verified vendor who may provide authenticated provenance records for the sneakers. While the sneakers are in transit, the user may receive an email notification with detailed instructions for unlocking a CryptoKick once the shipment arrives. After receiving the shoe box containing the purchased sneakers, the user scans the box UPC with a barcode scan feature in a sneakers app operating on the user's smartphone. In the sneakers app, a new profile page is responsively enabled; the sneakers app opens the new profile page. For at least some applications, the new profile page is linked with, exported to, or initially enabled in the user's personal (NIKEPLUS®) account profile. Private and public blockchain platform keys are generated, genotype and phenotype data are created, this data is embedded in segments of the public key's alphanumeric code, and the virtual representation of the CryptoKick is engendered. The CryptoKick's blockchain data, token, etc., are assigned to the user's new address; the new profile page lists the CryptoKick the user has acquired.
A user may wish to lease, license, or assign his/her new CryptoKick to any of one or more prospective buyers. In one example, a seller (also referred to herein as “transferor” or “first party”) offers to sell, and a buyer (also referred to herein as “transferee” or “second party”) agrees to buy a CryptoKick for an agreed-upon sum (e.g., three (3) ETH). The buyer may be interested to make such as purchase as the available CryptoKick has one or more attributes (e.g., artist, body type, colorway, etc.) the buyer is looking to add to a collection. The seller may initiate the sale process by marking a specific CryptoKick in the sneaker app as “For Sale” via a corresponding soft-key “auction” button. Sally may set a minimum bid and/or a buy now price, and provide an auction time window of a selected number of hours, days, weeks, etc. The sneaker app may present the seller with a share modal in which he/she can either share the auction via usual social media, or present a quick-response (QR) code for a potential buyer to scan. The buyer may then scan the QR code using a smartphone digital camera through operation of a scan feature in the sneaker app, and transmit the requisite funds (e.g., 3 ETH) to the auction site. The seller's sneakers app notifies him/her of the payment; the seller is prompted to agree to a terms of sale and finalize the transaction. The CryptoKick is then transferred from the first party to the address of the second party.
Owners of cryptographic digital assets may wish to intermingle or “breed” their digital assets with other digital assets to create asset “offspring,” such as schematically shown inFIG.6. A first digital asset owner and a second digital asset owner may wish to collaborate and crossbreed their digital assets82,84in order to create a new cryptographic digital asset. The first owner may be set as a “primary artist” if his/her digital asset has attributes desired by the second owner. In this instance, the second owner may initiate a smart contract with the first owner to collaborate. One or both parties may fund the contract with physical or digital currency, e.g., to pay for the transfer, a “collab fee” set by the breeding host site, and an optional siring fee for the second owner's siring services. Once both parties agree to and sign the breeding contract, one or both parties may be prompted to select one or more traits from their “parent” digital asset to transfer to the resultant “progeny” digital asset. Alternatively, the breeding host site may employ a breeding algorithm to build a new digital asset from two or more preexisting digital assets.
A “CollabScience” Algorithm may be employed to determine which contributing cryptographic digital asset will be designated as the sire, determine which contributing cryptographic digital asset will be designated as the dam, and determine which code subsets from each parent asset will be employed to build the cryptographic token key for the resultant digital asset. For example, the token keys for the two parent digital assets, DA1 and DA2, may appear as:
DA1: 4352635657387611432650689898388672080892866850020829309339781214
DA2: 1997670191981520482540801616208235668515393854245661572126051434
The CollabScience algorithm may use a random number generator (RNG) or other applicable means to generate a random number, e.g., between 0 and 65535. In accord with this example, the random number may be 21123. Once generated, the CollabScience algorithm may convert the resultant number 21123 to a binary code: 0101001010000011. Concomitantly, with the first number in the binary code being zero (0), the first parent digital asset DA1 is designated as the sire and corresponds to all zeros in the string; with the first parent digital asset DA1 being designated as the sire, the second parent digital asset DA2 is automatically designated as the dam and corresponds to all ones in the string.
Continuing with the above example, the CollabScience algorithm segments the parent token keys into multi-digit code subsets or “chunks”; in this example, each parent token key is broken into sixteen (16) 4-digit code subsets:Segmented DA1: [‘4352’, ‘6356’, ‘5738’, ‘7611’, ‘4326’, ‘5068’, ‘9898’, ‘3886’, ‘7208’, ‘0892’, ‘8668’, ‘5002’, ‘0829’, ‘3093’, ‘3978’, ‘1214’]Segmented DA2: +[‘1997’, ‘6701’, ‘9198’, ‘1520’, ‘4825’, ‘4080’, ‘1616’, ‘2082’, ‘3566’, ‘8515’, ‘3938’, ‘5424’, ‘5661’, ‘5721’, ‘2605’, ‘1434’]
The Collab Science algorithm then builds a new token ID for the resultant “progeny” digital asset based on the digits in the random number, with the sixteen chunks of the child token key being sequentially assigned a one or a zero based on the binary code of the above-generated random number. From this example, the first number in the binary code version of the random number is zero; the first parent digital asset DA1 is the designated sire, which corresponds to zero; as a result, the first chunk in the child token key will be copied from the first chunk of the sire and is, thus, set to 4352. Next, the second number in the binary code version of the random number is one; the second parent digital asset DA2 is the designated dam, which corresponds to one; as a result, the second chunk in the child token key will be copied from the second chunk of the dam and is, thus, set to 6701, and so on and so forth until all sixteen chunks in the child token key are filled with corresponding chunks from the parent token keys. The resultant new array for the child digital asset DA3 will therefore look like:Segmented DA3: +[‘4352’, ‘6701’, ‘5738’, ‘1520’, ‘4326’, ‘5068’, ‘1616’, ‘3886’, ‘3566’, ‘0892’, ‘8668’, ‘5002’, ‘0829’, ‘3093’, ‘2605’, ‘1434’]
The CollabScience algorithm produces the new token key ID from the array as:4352670157381520432650681616388635660892866850020829309326051434
The CollabScience algorithm then processes the cryptographic digital asset, produces the virtual representation of the new asset, and assigns the asset to the buyer's digital blockchain locker.
It is envisioned that other techniques may be employed to determine the attributes of a progeny digital asset. For instance, a Punnett Square may be implemented to express the dominant and recessive traits (“genes”) from the two parent digital assets, and create probabilities of a trait expression in an offspring digital asset. A Punnett Square is a graphical mechanism used to calculate a mathematical probability of a child asset inheriting a specific trait from two parent assets. The resultant array is provide by arranging the genotypes of one parent across the top of a table and that of the other parent down one side to discover all of the potential combinations of genotypes that can occur in a child given the genotypes of the parents. As seen inFIG.2, the genotype and phenotype information contained in encrypted token key46includes the digital shoe's: breeding attributes (“collab”), materials information, make data (“family”), manufacturing requirements (“heat”), color combination (“colorway”), future attributes, model data, and image background information.
Epigenetic factors may result in heritable phenotype changes that do not involve alterations in an underlying DNA sequence. In some instances, genotypic changes in an encrypted token key may be caused by real world and/or virtual interactions, leading to alterations of a cryptographic digital asset's phenotypic characteristics. A gene representing high heat and rare heat could be changed from Hhrr to HHRR due to epigenetic factors like the following: usage of real-world shoes may increase a likelihood of a genetic mutation or passing of a “good qualities” variation of genes to offspring; real world workouts, like running or sports, may increase a good gene mutation or increase speed of maturity of a progeny asset; checking into stores or other real-world criterion may lead to positive gene mutation, passing of “good traits” to offspring, speed up maturity; time-dependent breeding that prevents two cryptographic digital assets from crossbreeding before both assets reach a minimum age, otherwise breeding may fail or increase probability of passing “bad qualities” genes to progeny; unique breeding times may cause genetic mutations; frequent interactions (e.g., trading, selling, buying, and collaboration) with other assets or other apps may lead to positive gene mutation, passing of “good traits” to offspring, or speed up maturity.
As noted above,FIG.7schematically illustrates a method of acquiring a digital collectable that may be linked or coordinated with the sale of a physical product. Namely, as shown inFIG.7, the user11brings a device (i.e., smart phone device40) in proximity to a physical product200that includes an identifier (UPID), such as a QR Code, barcode, digital image, RFID tag, NFC tag, BLUETOOTH id, registry entry in an embedded processor, or some other machine readable code. This code may then be recognized by the phone40either optically, via radio frequency communication, or via wired data communication. Following the identification/recognition of the UPID, the phone40may initiate the transfer and/or original provisioning of a digital asset202linked with that product200to the user's locker204that is in communication with a blockchain service/network60. In an extension of this concept, the transfer of the digital asset202may be further secured using a PIN, cryptographic key, access code, or the like that may be provided, for example, on a receipt following the user's purchase of the product200.
In one embodiment, should the user11acquire a CryptoKick with the purchase of a pair of sneakers, and then subsequently return the sneakers, a smart contract associated with the CryptoKicks may unravel the acquisition and automatically return the token and full right to the CryptoKick back to the company/retailer. In the event the purchaser sold/traded the CryptoKick to a bona fide purchaser (BFP) prior to returning the shoes, this secondary transaction may similarly be unraveled/reversed. In some embodiments, with the reversal of this secondary transaction, the BFP may be presented with the option to re-acquire the CryptoKick from the company/retailer for a predetermined price (e.g., a prevailing price for the asset, at a discount to a prevailing price, at a fixed price set prior to market release, or for a nominal amount). In another embodiment, the BFP of the CryptoKick may have the first right of refusal to acquire/purchase the retuned physical product. This may be significant in the case of limited release sneakers that are, by definition, scarce.
FIG.8schematically illustrates a method of acquiring a digital collectable such as during a promotional giveaway. As shown, the user11may locate a virtual object210, such as a CryptoKick, in an arena212using an AR capability of a smart phone40. In this example, the CryptoKick may be “hidden” in a scoreboard214, though may be freely recognizable using an app on the phone that interfaces with a camera on the phone. The app may illustrate the virtual object on a display when the camera recognizes a specific environmental optical pattern (i.e., the scoreboard within the arena), and when the phone is geolocated within a particular area (i.e., via GPS sensing, beacons, geofencing techniques, wi-fi connectivity, and the like. Once located, the user11may be prompted to scan a unique code, such as the barcode on a ticket, a unique code provided on a program or physical item (e.g., noise maker, light stick, towel) that may be placed on the user's seat prior to the game. Once this code is scanned or entered, the phone40may initiate the transfer of the digital asset202to the user's locker204that is in communication with a blockchain service/network60.
In some embodiments, the ability to acquire the CryptoKick may be initiated by an aspect of the game/event, rather than by locating an AR object. Examples of such triggering events may include, for example, a shut-out (hockey/baseball), no-hitter (baseball), 50+ point individual performance (basketball), a triple-double (basketball), a hat trick (soccer/hockey), a scoreless quarter/period/half (basketball, hockey, soccer), and overtime/extra innings. In such an embodiment, the occurrence of the event may trigger an alert on the user's device39, which would prompt the user to scan their ticket to facilitate the transfer. In one embodiment, to eliminate a secondary market for ticket stubs, the app on the user's device that facilitates the notification may require that the scan occur within a predetermined geofence or time of the game/event. In a further extension, the marketplace (described above) may further permit the user39to prospectively sell the unvested right to the CryptoKick if the triggering event were to occur. This would resemble the user writing and selling a tradable option to the CryptoKick that either expires worthless, or results in the option purchaser acquiring the CryptoKick Similar future rights/options may be prospectively traded for the progeny of a CryptoKick.
FIGS.9-10schematically illustrates a video game interface220including a display222. The video game interface220and/or display222may be integral with a user device39(e.g., a smart phone40or tablet), or may be a standalone gaming console coupled with a display222. The device39may generally be configured to execute a digital application224that requires user input to control a virtual character226within an environment228. The character226may include or be defined by a plurality of attributes230that may affect how the character226behaves, responds, or performs within the environment230, and/or how the character226interacts with other characters232that may be controlled by the application224or by other users in a networked environment.
In one context, the character226may be an athlete and the environment228may be a sporting environment.FIG.9illustrates such a character226as a footballer, and the environment228as a football pitch within a stadium. The character's attributes230may include, for example, speed, ball control, passing, defense, kicking power, balance, and stamina (among others). In one embodiment, the character226may be outfit/skinned with a digital collectable (e.g., an article of apparel234) that may be uniquely backed by a token on the blockchain60. In an embodiment, the digital collectable may have been acquired in any one of the manners described herein. In one configuration, the application224may access the genetic code of the digital asset on the blockchain60via an API or other software interface236(i.e., an embodiment of the 3rdparty interface66described above) and/or may access the phenotype expression of the object either via an integrated software decoder or by accessing a networked virtual object generator62of the kind described above. In one configuration, one or more of the attributes230may be positively or negatively influenced by the genetic code or phenotype expression of the object234. WhileFIG.9illustrate the object as an article of apparel, it may similarly be an article of footwear, an object the character may use, a piece of sporting equipment, or the like.
Further building upon the notion of the CryptoKick as property, in one embodiment, a user or company may rent out or lease out the use of the digital collectable within a video game for a period of time. In one embodiment, the leasing may be constrained so that only one instance of a particular user's asset exists in any particular context. For example, a user may own full rights to an exclusive CryptoKick. That user may concurrently lease out the CryptoKick for use in Basketball Game A for 1 week, Soccer Game B for 2 weeks, and 1stPerson Shooter Game C for 3 weeks.
Another option may include programming a cryptographic digital asset as a virtual “pet” that a user cares for and helps to grow from a baby to an adult.FIG.10, for example, illustrates a user's avatar226taking his pet CryptoKicks240for a virtual walk and interacting with an avatar of another user232within an environment228representative of a virtual world. As mentioned above, such virtual interactions may affect the evolution, value, rate of maturation, visual appearance, marketability, etc., of the pet CryptoKick. The attributes of the digital asset may change with age or be unlocked over time. A user may care for the virtual pet directly or source to a third party (e.g., through ETH payment or transaction by other means). The virtual pet may go through various life stages, and concomitantly unlock different real-life sneaker versions of itself that a user can then purchase in stores.
Referring again toFIG.9, much like the virtual pet ofFIG.10, in some embodiments, gameplay, use of the digital asset, or improvements in a character's level, experience, or accomplishments may operatively alter/modify one or more genotypic and/or phenotypic attributes of the digital asset/CryptoKick. Similarly, in some embodiments, gameplay, use of the digital asset, or improvements in a character's level, experience, or accomplishments may operatively modify the effect that the digital asset has on the character's ability or gameplay. For example, in one embodiment, achievement of a new level, tournament victory, global ranking above a predefined threshold, or other similar accomplishments may modify an attribute of the CryptoKick to have a distinctive or limited availability appearance, colorway, skin, or the like. Likewise, in some embodiments, such accomplishments may serve as a multiplier on the effects that the digital asset imparts to the character.
Referring toFIG.11, in some embodiments, the digital assets may take the form of, or may be used in a digital collectable card game (DCCG). In such a game, each user may have a collection of digital assets, each with a different set, balance, or weighting of attributes/attribute scores, and/or different features, abilities, or powers. In some embodiments, users may take turns playing individual cards or groups of cards in an effort to win according to the rules set by the game.
While collectable card games, themselves, are generally well known, the use of the presently described digital assets may provide a unique extension of these games. Furthermore these games may serve as an additional use and motivation for collecting the digital assets. By uniquely securing each digital asset to an immutable database such as a blockchain60, each player's collection of cards and their required strategy for using those cards will likely be unique also.
In such an embodiment, a game server300may be in communication with a plurality of different user devices39. As with above, the user devices39may be smartphones40, smart watches42, tablet computers, laptop computers, web enabled devices, or other such devices that are capable of networked communication with the server300. Each user device39may be linked to a separate digital locker204, which may permit the user to access their securely stored digital assets from the blockchain60. Each asset may be represented as a separate digital card on the user's device, and may have its own unique attribute set (i.e., part of the phenotype). In one embodiment, a virtual object generator62may be in communication with the user devices39and/or the game server300to create the expression of the virtual object from the genotypic information associated with the token on the blockchain60. The game server300may manage the rules of the game, including maintaining a plurality of user accounts, instructing a first user, via the user's device39, when it is time to play, and altering an attribute of a second user's account based on the receipt of digital asset data from the first user. The received digital asset data may correspond to a digital asset played by the first user via the first user's device.
In one embodiment, the game server300may not have any stored understanding of a user's collection of digital assets until digital asset data is received. As such, in this embodiment, the asset collection for a user may be maintained solely by the user's device. In an alternate embodiment, a user's collection of assets may be registered with the user's account maintained by the game server300. In this configuration, the digital asset data may simply be an indication of which card in the user's account was played.
WhileFIG.11is intended to illustrate a plurality of users engaged in a DCCG, in an alternate configuration, the illustration may be representative of a meet-up where a plurality of users come to a common location for the purpose of breeding their CryptoKicks. Such an event may be coordinated by a central server that is linked to user accounts in a local area. Alternatively, users may have the ability to sponsor events and/or broadcast their own location for others to connect and/or create a user-initiated meet-up or invitation.
In some embodiments, the attributes of a cryptographic digital asset can be directly related to corresponding attributes of a real-world shoe for purposes of production. Optionally, digital asset attributes may be linked to a bill of materials for cost calculation and as a control mechanism. Resulting offspring may be restricted to having phenotype characteristics that can be created in the real world based on manufacturing capabilities, materials, and other factors. As CryptoKicks and CollaboKicks change owners due to selling, trading, buying, and collaboration, the resultant transaction history is tracked within the blockchain. Once a CollaboKick or CryptoKick that does not currently exist is created in real life, previous owners/users may be notified of such real-life existence and may be given an option to purchase the sneaker.
Aspects of this disclosure may be implemented, in some embodiments, through a computer-executable program of instructions, such as program modules, generally referred to as software applications or application programs executed by any of a controller or the controller variations described herein. Software may include, in non-limiting examples, routines, programs, objects, components, and data structures that perform particular tasks or implement particular data types. The software may form an interface to allow a computer to react according to a source of input. The software may also cooperate with other code segments to initiate a variety of tasks in response to data received in conjunction with the source of the received data. The software may be stored on any of a variety of memory media, such as CD-ROM, magnetic disk, bubble memory, and semiconductor memory (e.g., various types of RAM or ROM).
Moreover, aspects of the present disclosure may be practiced with a variety of computer-system and computer-network configurations, including multiprocessor systems, microprocessor-based or programmable-consumer electronics, minicomputers, mainframe computers, and the like. In addition, aspects of the present disclosure may be practiced in distributed-computing environments where tasks are performed by resident and remote-processing devices that are linked through a communications network. In a distributed-computing environment, program modules may be located in both local and remote computer-storage media including memory storage devices. Aspects of the present disclosure may therefore be implemented in connection with various hardware, software or a combination thereof, in a computer system or other processing system.
Any of the methods described herein may include machine readable instructions for execution by: (a) a processor, (b) a controller, and/or (c) any other suitable processing device. Any algorithm, software, control logic, protocol or method disclosed herein may be embodied as software stored on a tangible medium such as, for example, a flash memory, a CD-ROM, a floppy disk, a hard drive, a digital versatile disk (DVD), or other memory devices. The entire algorithm, control logic, protocol, or method, and/or parts thereof, may alternatively be executed by a device other than a controller and/or embodied in firmware or dedicated hardware in an available manner (e.g., implemented by an application specific integrated circuit (ASIC), a programmable logic device (PLD), a field programmable logic device (FPLD), discrete logic, etc.). Further, although specific algorithms are described with reference to flowcharts depicted herein, many other methods for implementing the example machine-readable instructions may alternatively be used.
Aspects of the present disclosure have been described in detail with reference to the illustrated embodiments; those skilled in the art will recognize, however, that many modifications may be made thereto without departing from the scope of the present disclosure. The present disclosure is not limited to the precise construction and compositions disclosed herein; any and all modifications, changes, and variations apparent from the foregoing descriptions are within the scope of the disclosure as defined by the appended claims. Moreover, the present concepts expressly include any and all combinations and subcombinations of the preceding elements and features. Additional features may be reflected in the following clauses:
Clause 1: A method of brand promotion using cryptographic digital assets, the method comprising: provisioning a plurality of non-fungable tokens, each registered with an immutable database or blockchain, and each corresponding to a unique digital asset; associating each token with a unique, machine readable identification code; providing each machine readable identification code to a different respective individual from a plurality of individuals; providing software code to a user device associated with at least one of the plurality of individuals; wherein the user device includes a camera, a display, and a location recognition circuit, the software code configured to: cause the user device to discover a virtual image within a real-world environment, display a prompt, via the display, for the user to scan the machine readable identification code upon discovery of the virtual image; recognize a machine readable identification code, and cause the token associated with the machine readable identification code to be transferred to a digital locker associated with the individual or user device.
Clause 2: The method of clause 1, wherein the token includes genotypic information corresponding to one or more phenotypic expressions of a virtual object.
Clause 3: The method of any of clauses 1-2, wherein the software code causes the user device to discover the virtual image within the real-world environment via augmented reality.
Clause 4: The method of any of clauses 1-3, wherein the software code causes the user device to recognize an environment according to an optical image perceived by the camera and a location determined by the location recognition circuit; display the optical image on the display, overlay the displayed optical image with the virtual image at a predetermined location within the displayed environment.
Clause 5: The method of any of clauses 1-4, wherein the unique digital asset includes a virtual object comprising a plurality of attributes, and where each attribute is determinable, at least in part, according to a portion of code associated with the token of that unique digital asset.
Clause 6: The method of clause 5, wherein at least one of the plurality of attributes is influenced in its expression by use of the virtual object.
Clause 7: The method of any of clauses 1-6, wherein the location recognition circuit is a GPS receiver.
Clause 8: A method of brand promotion using cryptographic digital assets, the method comprising: provisioning a plurality of non-fungable tokens, each registered with an immutable database or blockchain, and each corresponding to a different respective physical retail product selected from a plurality of physical retail products; associating each token with a unique, machine readable identification code; providing the machine readable identification code associated with a first physical retail product to a retail purchaser of the first physical retail product; receiving a request from a user device associated with the retail purchaser to transfer the non-fungable token associated with the first physical retail product to a digital locker associated with the retail purchaser or user device, wherein the request includes a code included in or derived from the machine readable identification code associated with the first physical retail product.
Clause 9: The method of clause 8, further comprising initiating a request to the immutable database or blockchain to transfer the non-fungable token associated with the first physical retail product to the digital locker associated with the retail purchaser.
Clause 10: The method of any of clauses 8-9, further comprising: providing software code to the user device; wherein the user device includes a camera, a display, and a location recognition circuit, the software code configured to: cause the user device to discover a virtual image within a real-world environment, display a prompt, via the display, for the user to scan the machine readable identification code upon discovery of the virtual image; and recognize a machine readable identification code.
Clause 11: The method of clause 10, wherein the software code causes the user device to recognize the machine readable identification code through at least one of optical recognition via the camera, RFID, NFC, or BLUETOOTH communications.
Clause 12: The method of any of clauses 8-11 wherein providing the machine readable identification code associated with a first physical retail product to a retail purchaser of the first physical retail product includes at least one of: including the machine readable identification code on a tag, label, or sticker attached to the first retail product; printing the machine readable identification code on a box, container, or packaging material enclosing the first physical retail product; printing the machine readable identification code on a receipt provided to the retail purchaser; printing a first portion of the machine readable identification code on the box, container, or packaging material enclosing the first physical retail product, and printing a second portion of the machine readable identification code on a receipt provided to the retail purchaser.
Clause 13: The method of clause 12, wherein the software code causes the user device to discover the virtual image within the real-world environment via augmented reality.
Clause 14: The method of any of clauses 12-13, wherein the software code causes the user device to recognize an environment according to an optical image perceived by the camera and a location determined by the location recognition circuit; display the optical image on the display, overlay the displayed optical image with the virtual image at a predetermined location within the displayed environment.
Clause 15: The method of any of clauses 8-14, wherein the token includes genotypic information corresponding to one or more phenotypic expressions of a virtual object.
Clause 16: The method of any of clauses 8-15, wherein the unique digital asset includes a virtual object comprising a plurality of attributes, and where each attribute is determinable, at least in part, according to a portion of code associated with the token of that unique digital asset.
Clause 17: The method of clause 16, wherein at least one of the plurality of attributes is influenced in its expression by use of the virtual object.
Clause 18: A method comprising: providing a virtual object to a user, wherein the virtual object includes a plurality of attributes, and wherein each attribute of the plurality of attributes is at least partially derived from a code associated with a non-fungible token registered to an immutable database or blockchain.
Clause 19: The method of clause 18, wherein providing the virtual object to the user includes causing the non-fungible token to be transferred to an account associated with the user.
Clause 20: The method of clause 19, further comprising receiving value from the user in consideration for causing the non-fungible token to be transferred to the account associated with the user.
Clause 21: The method of any of clauses 18-20, wherein providing the virtual object to the user includes making the virtual object available to the user within a video game.
Clause 22: The method of clause 21, wherein the video game includes an avatar, character, or athlete within a virtual environment, and wherein the avatar, character, or athlete is controlled by user input received via a user device.
Clause 23: The method of clause 22, wherein the virtual object is an article of footwear or an article of apparel.
Clause 24: The method any of clauses 22-23, wherein the avatar, character, or athlete includes a plurality of character attributes, each having a respective attribute score that affects a behavior, performance, or ability of the avatar, character, or athlete within the environment; and wherein integration of the virtual object with the avatar, character, or athlete operatively modifies at least one attribute score.
Clause 25: The method of clause 21, wherein the video game is a digital collectable card game, and wherein the virtual object is represented as a digital collectable card.
Clause 26: The method of any of clauses 21-25, further comprising providing an indication of the use of the virtual object within the video game to a remote server, and wherein the indication of use of the virtual object is operative to alter at least one of the plurality of attributes of the virtual object.
Clause 27: A computerized system for implementing any of the methods of clauses 1-16.
Clause 28: A method for automating generation of cryptographic digital assets associated with articles of footwear, each of the articles of footwear including an upper for attaching to a foot of a user and a sole structure attached to the upper for supporting thereon the foot of the user, the method comprising: receiving, via a middleware server computer over a distributed computing network from a remote computing node, a transaction confirmation indicative of a validated transfer of an article of footwear from a first party to a second party; determining, via the middleware server computer from an encrypted relational database, a unique owner identification (ID) code associated with the second party; generating a cryptographic digital asset associated with the article of footwear, the cryptographic digital asset including a digital shoe and a unique digital shoe ID code; linking, via the middleware server computer, the cryptographic digital asset with the unique owner ID code; and transmitting, via the middleware server computer to a distributed blockchain ledger, the unique digital shoe ID code and the unique owner ID code to record transfer of the cryptographic digital asset to the second party on a transaction block.
Clause 29: The method of clause 28, wherein the unique digital shoe ID code includes a cryptographic token key with a code string segmented into a series of code subsets, wherein a first plurality of the code subsets includes data indicative of attributes of the digital shoe.
Clause 30: The method of clause 29, wherein the first plurality of the code subsets includes genotype and phenotype data for the digital shoe.
Clause 31: The method of any of clauses 29-30, wherein a second plurality of the code subsets includes data indicative of attributes of the article of footwear.
Clause 32: The method of clause 31, wherein the second plurality of the code subsets includes colorway, materials, manufacturing, make, and/or model data for the article of footwear.
Clause 33: The method of any of clauses 28-32, further comprising: responsive to receiving the transaction confirmation, transmitting a notification to the second party with information for accessing the cryptographic digital asset; and receiving, via the middleware server computer from a handheld personal computing device of the second party, a scanning confirmation verifying a universal product code (UPC) and/or a unique product identifier number (UPIN) corresponding to a make and a model of the article of footwear has been scanned, wherein linking the cryptographic digital asset with the unique owner ID code is responsive to receipt of the scanning confirmation.
Clause 34: The method of any of clauses 28-33, further comprising, responsive to receiving the transaction confirmation, transmitting a notification to the second party with a unique key with a hashed address to a cryptographic token.
Clause 35: The method of any of clauses 28-34, further comprising: receiving a digital breeding solicitation with a request to intermingle the cryptographic digital asset with a third-party cryptographic digital asset; and generating a progeny cryptographic digital asset with a combination of one or more features from the cryptographic digital asset and one or more features from the third-party cryptographic digital asset.
Clause 36: The method of clause 35, wherein: the unique digital shoe ID code includes a first cryptographic token key with a first code string segmented into a series of first code subsets, a first of the first code subsets including data indicative of attributes of the digital shoe; the third-party cryptographic digital asset includes a second cryptographic token key with a second code string segmented into a series of second code subsets, a first of the second code subsets including data indicative of attributes of a third-party digital shoe; and the progeny cryptographic digital asset includes a third cryptographic token key with a third code string segmented into a series of third code subsets, a first of the third code subsets including the data from the first of the first code subsets, and a second of the third code subsets including the data from the first of the second code subsets.
Clause 37: The method of clause 36, wherein the first of the first and third code subsets both share a first distinct alphanumeric sequence, and wherein the first of the second code subsets and the second of the third code subsets share a second distinct alphanumeric sequence.
Clause 38: The method of any of clauses 36-37, wherein generating the progeny cryptographic digital asset includes applying a random number generator to: designate one of the cryptographic digital asset or the third-party cryptographic digital asset as a sire; designate another of the cryptographic digital asset or the third-party cryptographic digital asset as a dam; and determine which of the third code subsets corresponds to which of the first code subsets and which of the of third code subsets correspond to which of the second code subsets.
Clause 39: The method of any of clauses 28-38, further comprising: receiving a digital transfer proposal with a request to transfer the cryptographic digital asset to a third party; determining a new unique owner ID code associated with the third party; linking the cryptographic digital asset with the new unique owner ID code; and transmitting the unique digital shoe ID code and the new unique owner ID code to the distributed blockchain ledger for recordation on a new transaction block.
Clause 40: The method of clause 39, further comprising receiving a new transaction confirmation indicative of a new validated transfer of the article of footwear from the second party to the third party.
Clause 41: The method of any of clauses 28-40, further comprising generating, via the middleware server computer, a smart contract operable to authenticate ownership and to track future transaction of the cryptographic digital asset.
Clause 42: The method of any of clauses 28-41, wherein the unique owner ID code is linked with a cryptocurrency wallet registered with the distributed blockchain ledger.
Clause 43: The method of any of clauses 28-42, wherein the transaction confirmation includes a universal product code (UPC) and/or a unique product identifier number (UPIN) corresponding to a make and a model of the article of footwear.
Clause 44: A decentralized computing system for automating generation of cryptographic digital assets associated with articles of footwear, each of the articles of footwear including an upper for attaching to a foot of a user and a sole structure attached to the upper for supporting thereon the foot of the user, the decentralized computing system comprising: a wireless communications device configured to connect with a remote computing node over a distributed computing network; a cryptographic digital asset registry storing digital shoes and unique digital shoe ID codes associated with multiple cryptographic digital assets; and a middleware server computer operatively connected to the wireless communications device and the cryptographic digital asset registry, the middleware server computer being programmed to: receive, over the distributed computing network from the remote computing node, an electronic transaction confirmation indicative of a validated transfer of an article of footwear from a first party to a second party; retrieve, from an encrypted relational database, a unique owner identification (ID) code associated with the second party; generate a cryptographic digital asset associated with the article of footwear, the cryptographic digital asset including a digital shoe and a unique digital shoe ID code; link the cryptographic digital asset with the unique owner ID code in the cryptographic digital asset registry; and transmit the unique digital shoe ID code and the unique owner ID code to a distributed blockchain ledger to record transfer of the cryptographic digital asset to the second party on a transaction block.
Clause 45: The decentralized computing system of clause 44, wherein the unique digital shoe ID code includes a cryptographic token key with a code string segmented into a series of code subsets, wherein a first plurality of the code subsets includes data indicative of attributes of the digital shoe.
Clause 46: The decentralized computing system of clause 45, wherein a second plurality of the code subsets includes data indicative of attributes of the article of footwear.
Clause 47: The decentralized computing system of any of clauses 44-45, wherein the middleware server computer is further programmed to: responsive to receiving the transaction confirmation, transmit a digital notification to the second party with information for accessing the cryptographic digital asset; and receive, from a handheld personal computing device of the second party, a scanning confirmation verifying a universal product code (UPC) and/or a unique product identifier number (UPIN) corresponding to a make and a model of the article of footwear has been scanned, wherein linking the cryptographic digital asset with the unique owner ID code is responsive to receipt of the scanning confirmation.
Clause 48: The decentralized computing system of any of clauses 44-47, wherein the middleware server computer is further programmed to, responsive to receiving the transaction confirmation, transmit a digital notification to the second party with a unique key with a hashed address to the cryptographic token.
Clause 49: The decentralized computing system of any of clauses 44-48, wherein the middleware server computer is further programmed to: receive a digital breeding bid from the second party with a request to intermingle the cryptographic digital asset with a third-party cryptographic digital asset; and generate a progeny cryptographic digital asset with a combination of one or more features from the cryptographic digital asset and one or more features from the third-party cryptographic digital asset.
Clause 50: The decentralized computing system of clause 49, wherein: the unique digital shoe ID code includes a first cryptographic token key with a first code string segmented into a series of first code subsets, a first of the first code subsets including data indicative of attributes of the digital shoe; the third-party cryptographic digital asset includes a second cryptographic token key with a second code string segmented into a series of second code subsets, a first of the second code subsets including data indicative of attributes of a third-party digital shoe; and the progeny cryptographic digital asset includes a third cryptographic token key with a third code string segmented into a series of third code subsets, a first of the third code subsets including the data from the first of the first code subsets, and a second of the third code subsets including the data from the first of the second code subsets.
Clause 51: The decentralized computing system of clause 50, wherein generating the progeny cryptographic digital asset includes applying a random number generator to: designate one of the cryptographic digital asset or the third-party cryptographic digital asset as a sire; designate another of the cryptographic digital asset or the third-party cryptographic digital asset as a dam; and determine which of the of third code subsets correspond to the first code subsets and which of the of third code subsets correspond to the second code subsets.
Clause 52: The decentralized computing system of any of clauses 44-51, wherein the middleware server computer is further programmed to: receive a digital transfer proposal with a request to transfer the cryptographic digital asset to a third party; determine a new unique owner ID code associated with the third party; link the cryptographic digital asset with the new unique owner ID code; and record the unique digital shoe ID code and the new unique owner ID code on a new transaction block with the distributed blockchain ledger.
Claims
- A method of integrating a cryptographic digital asset into a digital software application, the digital software application including code that, when executed, displays a character avatar on a display associated with a user device, the character avatar being operably controlled by a user via the user device, the method comprising: receiving a digital asset identification (ID) code, the digital asset ID code existing together with a unique owner ID code on a distributed blockchain ledger, wherein the digital asset ID code represents the cryptographic digital asset, and wherein the cryptographic digital asset comprises a plurality of attributes;representing a virtual object on the display via the digital software application, wherein the virtual object has an appearance that is based on the plurality of attributes of the cryptographic digital asset, and wherein the virtual object includes a plurality of object attributes;modifying at least one of the object attributes according to an aspect of the digital software application or interaction between the character avatar and the virtual object;representing a modified virtual object on the display via the digital software application, wherein the modified virtual object has an appearance that is based, in part, on the modified object attributes;and modifying at least one of the plurality of attributes of the cryptographic digital asset according to the modified object attributes or an accomplishment of the user or character avatar within the digital software application;and transmitting a cryptographic block comprising the digital asset ID code with the modified attributes of the cryptographic digital asset to a distributed blockchain ledger to record the modification.
- The method of claim 1, wherein the virtual object is a virtual shoe, article of apparel, headgear, avatar, or pet.
- The method of claim 1, wherein the user is a first user, and wherein the unique owner ID code is a code of a second user.
- The method of claim 1, further comprising modifying at least one of the plurality of object attributes according to an aspect of the digital software application or accomplishment of the user or character avatar within the digital software application.
- The method of claim 1, further comprising offering a real-world physical embodiment of the virtual object for sale to an owner of the cryptographic digital asset.
- The method of claim 5, wherein the real-world physical embodiment of the virtual object includes at least one of the modified object attributes.
- The method of claim 5, wherein the virtual object is a virtual shoe or virtual article of apparel, and wherein the real-world physical embodiment of the virtual object is a corresponding physical shoe or physical article of apparel.
- A method for integrating a cryptographic digital asset into a digital software application executing on a user device, the digital software application including code that, when executed, displays a character avatar on a display associated with a user device, the character avatar being operably controlled by a user via the user device, the method comprising: displaying, by the digital software application, a virtual environment on a display of the user device;receiving, by the digital software application, a user selection of a cryptographic digital asset from a digital asset registry storing a plurality of cryptographic digital assets linked to blockchain data;displaying, by the digital software application, a virtual representation of the selected cryptographic digital asset within the virtual environment, the virtual representation of the cryptographic digital asset comprising a plurality of object attributes;modifying, by the digital software application, one or more object attributes according to an aspect of the digital software application or interaction between the character avatar and the virtual object;and displaying, by the digital software application, a modified virtual representation having an appearance that is based, in part, on the modified object attributes;and modifying at least one of the plurality of attributes of the cryptographic digital asset according to the modified object attributes or an accomplishment of the user or character avatar within the digital software application;and transmitting a cryptographic block comprising the digital asset ID code with the modified attributes of the cryptographic digital asset to a distributed blockchain ledger to record the modification.
- The method of claim 8, further comprising: tracking, by the digital software application, accomplishments of the user controlled character within the video game;modifying, by the digital software application, one or more attributes of the selected cryptographic digital asset based on the tracked accomplishments.
- The method of claim 8, wherein the selected cryptographic digital asset is a virtual shoe, article of apparel, accessory, or equipment.
- The method of claim 8, further comprising: enabling, by the digital software application, breeding between the selected cryptographic digital asset and a second cryptographic digital asset to generate a new cryptographic digital asset with blended attributes.
- The method of claim 11, wherein enabling breeding is performed responsive to the user controlled character achieving a predetermined accomplishment within the digital software application.
Disclaimer: Data collected from the USPTO and may be malformed, incomplete, and/or otherwise inaccurate.