U.S. Pat. No. 11,110,355
VIDEOGAME PERIPHERAL SECURITY SYSTEM AND METHOD
AssigneeActivision Publishing, Inc.
Issue DateSeptember 23, 2015
Illustrative Figure
Abstract
A system and method relating to a videogame system comprising videogame software and a videogame peripheral is presented. The presented system and method prevents against the use of certain videogame peripherals with unauthorized videogame software through the use of “protected” and “unprotected” inputs.
Description
DETAILED DESCRIPTION The invention relates generally to videogames, and more particularly to a system and method that prevents against the use of certain videogame peripherals with unauthorized videogame software through the use of “protected” and “unprotected” inputs. Exemplary System Architecture FIG. 1is an example of a videogame system in accordance with aspects of the invention. In some embodiments, the videogame system includes a videogame console101, a display unit103, videogame software executing on the videogame console (not shown), and one or more videogame peripherals105. The videogame console is connected to the display unit via an audio-video cable107and with the videogame peripherals. In the embodiment ofFIG. 1, the connection between the videogame peripheral and the videogame console is a wireless connection109. In other embodiments, the connection may be wired. The videogame console inFIG. 1also includes one or more removable memory interfaces, for example, optical media reader111. Though the embodiment ofFIG. 1relates to a videogame console, any device suitable for playing videogames may be used, including personal computers (e.g., desktops, laptops, etc.), handheld devices (e.g., mobile phones, tablets, etc.), smart televisions, and other computing devices. Although not explicitly shown, the videogame console inFIG. 1includes internal circuitry for processing instructions contained in the videogame software. The videogame console generally includes at least one processor, memory, and other circuitry, for example, graphics circuitry and interface circuitry. The videogame console also includes network circuitry for connecting to, for example, the internet, one or more servers, and/or other networked devices. Although not illustrated inFIG. 1, the videogame system may further comprise a server that may include one or more processors programmed by computer program instructions. For example, a server may include all or a portion of the videogame software and therefore provide all or a portion of the videogame instructions. The videogame peripheral105ofFIG. 1is guitar-shaped, with a ...
DETAILED DESCRIPTION
The invention relates generally to videogames, and more particularly to a system and method that prevents against the use of certain videogame peripherals with unauthorized videogame software through the use of “protected” and “unprotected” inputs.
Exemplary System Architecture
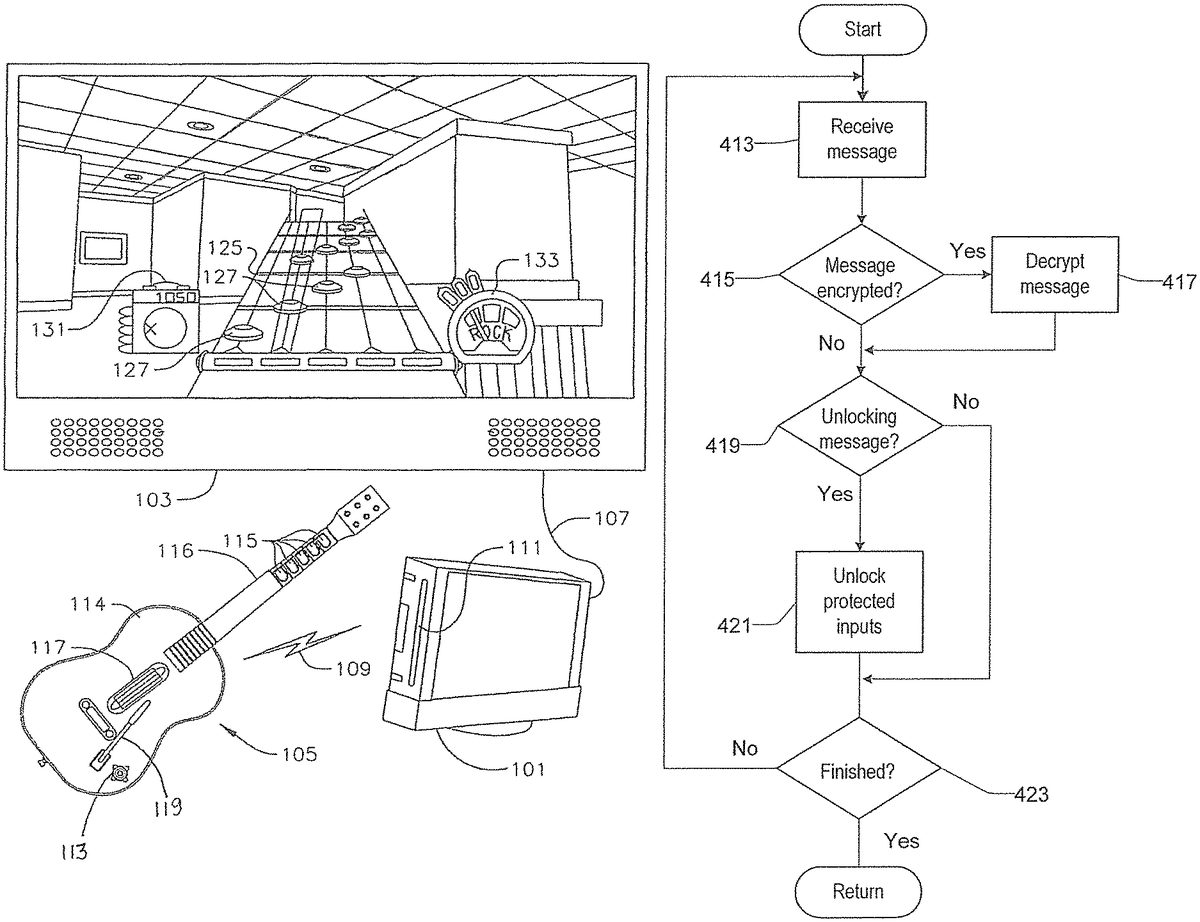
FIG. 1is an example of a videogame system in accordance with aspects of the invention. In some embodiments, the videogame system includes a videogame console101, a display unit103, videogame software executing on the videogame console (not shown), and one or more videogame peripherals105. The videogame console is connected to the display unit via an audio-video cable107and with the videogame peripherals. In the embodiment ofFIG. 1, the connection between the videogame peripheral and the videogame console is a wireless connection109. In other embodiments, the connection may be wired. The videogame console inFIG. 1also includes one or more removable memory interfaces, for example, optical media reader111. Though the embodiment ofFIG. 1relates to a videogame console, any device suitable for playing videogames may be used, including personal computers (e.g., desktops, laptops, etc.), handheld devices (e.g., mobile phones, tablets, etc.), smart televisions, and other computing devices.
Although not explicitly shown, the videogame console inFIG. 1includes internal circuitry for processing instructions contained in the videogame software. The videogame console generally includes at least one processor, memory, and other circuitry, for example, graphics circuitry and interface circuitry. The videogame console also includes network circuitry for connecting to, for example, the internet, one or more servers, and/or other networked devices. Although not illustrated inFIG. 1, the videogame system may further comprise a server that may include one or more processors programmed by computer program instructions. For example, a server may include all or a portion of the videogame software and therefore provide all or a portion of the videogame instructions.
The videogame peripheral105ofFIG. 1is guitar-shaped, with a body114and a neck116extending from the body. The peripheral includes various inputs meant to simulate aspects of a real guitar, including for example, a strum bar117, whammy bar119, and a plurality of fret buttons115. Other inputs include one or more control buttons113. The control buttons may correspond to “start” and “select” for controlling the operation of a videogame, for example.
The inputs of the videogame peripheral are manipulated by a user of the videogame peripheral and generate input signals based on the user manipulations. The videogame console and videogame software receive the input signals generated by the videogame peripheral and processes the videogame based on the received input signals. In various combinations, the videogame console may simultaneously receive and process input signals from more than one connected videogame peripheral.
The display unit inFIG. 1shows a screenshot of gameplay in a music videogame. The screenshot shows an interactive music track125with a plurality of gems, for example, gems127, providing user instructions as to instructed user manipulation of inputs of the guitar controller during gameplay. Other features of the screenshot include, for example, a user score indicator131and a power meter133.
In the music videogame ofFIG. 1, the videogame console's processor(s) receive input signals from the videogame peripheral. In some embodiments, user instructions are retrieved from the removable memory source holding videogame instructions, and a visual representation of the user instructions are displayed on the display unit. A user of the videogame attempts to manipulate the videogame peripheral in compliance with the user instructions. For example, the gems may represent instructions to depress a corresponding fret button and strum the strum bar at an appropriate time (e.g., when the gem a particular part of the screen). Input signals corresponding to the user manipulations on the videogame peripheral are generated and transmitted to the videogame console. The videogame console compares the input signals for compliance with the user instructions, and determines whether the user has complied or the extent to which the user has complied with the user instructions. A score is assigned to the user based on extent of user compliance with the user instructions.
FIG. 2is an example of a block diagram of a processing unit of a videogame console in accordance with aspects of the invention. In the embodiment ofFIG. 2, the processing unit includes a bus201interconnecting a processor203, memory205, a removable memory interface207, an audio driver209and a video driver211, a display input/output port213, a user input/output port215, a wireless communication interface217, and other circuitry219that may include, for example, networking circuitry. In various embodiments of the invention, the processing unit may include various different combinations of components to suit the particular application of each individual embodiment.
In operation, the processor executes videogame instructions to facilitate gameplay for a particular videogame. The processor may communicate with each individual component in the processing unit as needed to facilitate gameplay. In some embodiments, the processor retrieves specific instructions for a videogame from a removable memory source holding videogame software. The processor may process the videogame instructions based on general program instructions the processor retrieves from the memory.
Videogame execution is also based, in part, on input signals received from connected videogame peripheral(s), which communicate with the processor through either the user input/output port or through a wireless connection interface, as illustrated inFIG. 1. The processor processes the various instructions and input signals it receives to generate data associated with the proper execution of the videogame, for example, audio and video data related to videogame action.
In some embodiments, communication between a videogame peripheral and the videogame console's processor may be bidirectional such that the videogame peripheral may both transmit and receive communications to or from the processor. As discussed in more detail herein, communications received by the videogame peripheral from the processor may be used to implement the security protocol of the present invention.
Exemplary Peripheral Security System
Referring again to the videogame system ofFIG. 1, one aspect of the invention relates to preventing the use of the videogame peripheral with unauthorized videogame software through the use of one or more protected inputs, which are disabled until unlocked. Protected inputs may be selected such that as long as the protected inputs remain disabled, a user will find it difficult, if not impossible, to successfully engage, or completely successfully engage, in the videogame's gameplay. Note that although the example ofFIG. 1depicts a music videogame using a guitar-shaped peripheral, it should be appreciated that the inventive aspects discussed herein can be applied to peripherals as used in any videogame genre or software application.
According to aspects of the invention, the videogame peripheral ofFIG. 1comprises one or more protected inputs that are disabled by default and remain disabled until unlocked, for example, when an unlocking message is received. As used herein, “input” may refer to a single input (e.g., a control button or fret button) or a plurality of inputs actuated in combination or sequence (e.g., actuating the strum bar input after or while depressing one or more fret buttons may be considered a specific “input”). In some embodiments, a protected input may include a single (or plural) input(s) that are disabled based on status of another input (e.g. the strum bar input is disabled when one or more fret buttons are in a depressed state). In one embodiment, the peripheral includes circuitry, which in some embodiments is a processor, for example programmed by program instructions, to disable the protected inputs by not generating signals to the videogame console in response to the user actuating the protected inputs. In another embodiment, the signals may be generated but masked by circuitry in the videogame console, a wireless transceiver coupled to the console, and/or the peripheral itself to achieve the same effect. It should be appreciated that there are other ways to disable a protected input, any of which may be implemented within the scope of this invention.
In some embodiments, the protected inputs are a subset of the peripheral's inputs (i.e., the protected inputs do not include all of the peripheral's inputs). In other embodiments, the protected inputs are specific sequences and/or combinations of inputs. In such cases, the peripheral may further comprise one or more unprotected inputs that are enabled by default and do not need to be unlocked for use.
According to aspects of the invention, inputs can be classified as being useful only within gameplay, being useful only outside of gameplay (e.g., to navigate videogame menus or console menus), or useful both within and outside of gameplay. In some embodiments, the protected inputs may comprise one or more inputs useful only within gameplay, while the unprotected inputs comprise one or more inputs only useful outside of gameplay or useful within and outside of gameplay. In the example ofFIG. 1, protected inputs may include certain button combinations only used during gameplay, for example, the button combination of actuating the strum bar input while pressing one or more fret buttons (here referred to as a “chord” input) or certain individual inputs such as the whammy bar. Unprotected inputs may include, for example, inputs useful in navigating menus outside of gameplay (e.g., the strum bar, certain fret buttons, the start/select buttons, and other inputs may be used to navigate in-game menus, the console's system menus, virtual stores, or other applications). In such embodiments, the videogame system disclosed herein allows the user to use the videogame peripheral outside of gameplay, while preventing meaningful use of the videogame peripheral within gameplay by disabling certain inputs needed for gameplay. The scheme of selecting of protected and unprotected inputs on whether the inputs are useful within or outside of gameplay is one example of how to group protected and unprotected inputs, and other schemes may be used. For example, the protected and unprotected inputs may correspond to their usefulness during certain game modes or in particular sections of the game.
According to aspects of the invention, the protected inputs are disabled until unlocked. In some embodiments, the protected inputs are unlocked when the peripheral receives from the videogame software or console an unlocking message. In some embodiments, all protected inputs may be unlocked by a single unlocking message, though in other embodiments, different unlocking messages may be required to unlock different protected inputs.
FIG. 3illustrates an unlocking message300in accordance with aspects of the invention. Unlocking message300may be transmitted by software being executed on the videogame console including, for example, the console's system software or videogame software executing on the console. Unlocking message300may comprise, for example, a header/control portion310and a payload/data portion320. The header portion may, in some embodiments, comprise information identifying the message as an unlocking message. The payload portion, in some embodiments, may comprise information identifying one or more protected inputs to be unlocked.
In some embodiments, the videogame peripheral includes one or more countdown timers. After unlocking one or more protected inputs, for example, in response to receiving an unlocking message, the videogame peripheral initiates the countdown timer. The videogame peripheral disables (or “re-locks”) the unlocked protected inputs upon expiration of the countdown timer. If, however, the videogame peripheral receives another unlocking message before the countdown timer's expiration, the videogame peripheral resets the countdown timer and the protected inputs remain unlocked. In some embodiments, aspects of the control circuitry relating to the protected and unprotected inputs may be found in the console, the wireless transceiver coupled to the console, and/or the peripheral itself. In some embodiments, the protected inputs may be unlocked by default, but locked after no unlocking message is received before the countdown timer's expiration.
In some embodiments, the unlocking message may contain data representing the countdown timer's starting value (or “countdown value”). For example, the unlocking message's payload may include the starting value to be programmed into the countdown timer (e.g., millisecond, 1 second, 10 seconds, etc.). The countdown timer's starting value may thus be set or changed by the software sending the unlocking messages (e.g., videogame software or console software). In some embodiments, the unlocking messages are sent periodically at specific intervals, and the countdown value may be a function of the interval for sending unlocking messages. For example, the countdown value may be ten (or any other factor) times the interval for sending unlocking messages. In that example, if unlocking messages are sent every one second, the countdown value would be ten seconds. As another example, the interval for sending unlocking messages may be a certain number of seconds greater than the countdown value (e.g., countdown value+X seconds). Utilizing a countdown value greater than the interval for sending unlocking messages, helps mitigate against unsuccessfully delivered unlocking messages (e.g., those that were dropped due to an unreliable connection between the console and peripheral).
In one implementation of the invention, the unlocking message may be cryptographically secured to prevent unauthorized access. For example, the unlocking message may be encrypted or scrambled amongst other messages. In some embodiments, a 2-way handshake may be required between the console and peripheral before unlocking messages are sent.
Exemplary Flowcharts
The various processing operations and/or data flows depicted in the exemplary flowcharts ofFIGS. 4 and 5are described in greater detail herein. The described operations may be accomplished using some or all of the system components described in detail above and, in some implementations, various operations may be performed in different sequences and various operations may be omitted. In some embodiments operations of the processes ofFIG. 4and/orFIG. 5are performed by circuitry of a videogame peripheral, for example the videogame peripheral ofFIG. 1. In some embodiments the circuitry comprises a processor, which in some embodiments is programmed by program instructions. In some embodiments operations of processes ofFIG. 4and/orFIG. 5are performed by circuitry of a videogame console, for example the videogame console ofFIG. 1and/or the processing unit ofFIG. 2. In some embodiments the operations ofFIG. 4and/orFIG. 5are performed by a videogame peripheral and a videogame console acting in concert. In some embodiments, additional operations may be performed along with some or all of the operations shown in the depicted flow diagrams. One or more operations may be performed simultaneously. Accordingly, the operations as illustrated (and described in greater detail below) are exemplary by nature and, as such, should not be viewed as limiting.
Exemplary Process for Unlocking Protected Inputs
FIG. 4depicts an exemplary process for unlocking protected inputs according to aspects of the invention.
In an operation413, the process receives a message. The message could, for example, be sent by software running on a videogame console (e.g., videogame software or console system software) and received by a videogame peripheral coupled to the videogame console.
In an operation415, the process determines whether the received message is encrypted. If so, the process decrypts the message in an operation417and proceeds to an operation419. If not the process proceeds directly to an operation419. In some embodiments in which no encryption is utilized, the process skips operation415altogether and proceeds directly to an operation419.
In an operation419the process determines if the message is an unlocking message. In some embodiments, the message type may be encoded in the message header, as described in connection withFIG. 3. If the message is an unlocking message, the process proceeds to an operation421and unlocks one or more protected inputs. In some instances, the process unlocks all protected inputs in response to receiving an unlocking message. In other embodiments, the message's payload may contain information relating to which of a plurality of protected inputs should be unlocked. Once the designated protected inputs have been unlocked, the process proceeds to an operation423, where the process either returns to an operation413or finishes.
Exemplary Process for Unlocking and Locking Protected Inputs
FIG. 5depicts an exemplary process for unlocking and locking protected inputs according to an implementation of the invention.
In operations513and515, the process receives an unlocking message and unlocks one or more protected inputs. The receiving of an unlocking message and unlocking operations may be similar to those described in connection withFIG. 4, above.
In an operation517, the process retrieves from the unlocking message's payload a countdown value.
In an operation519, the videogame peripheral's countdown timer is set to the countdown value obtained from the unlocking message.
In an operation521, the countdown timer begins.
In an operation523, the process determines if an additional unlocking message has been received before the expiration of the countdown timer. If the countdown timer expired before an additional unlocking message is received, the process proceeds to an operation525, in which the one or more protected inputs previously unlocked in operation515are again locked by the process. On the other hand, if an additional unlocking message is received before the countdown timer's expiration, the process proceeds to an operation513and repeats the process of receiving an unlocking message, unlocking one or more protected inputs, and programming the videogame peripheral's countdown timer with the unlocking message's countdown value.
As discussed above, the countdown value can be representative of any time value (e.g., 100 millisecond, 1 second, 1 minute, etc.), and in some embodiments, is a function of the interval for sending unlocking messages. For example, the countdown value may be the interval for sending unlocking messages multiplied by some factor (e.g., 10, 50, 100). In this manner, the console will send multiple unlocking messages before the countdown timer expires. Additionally or alternatively, the countdown timer may be dynamically adjusted. If, for example, it is determined that unlocking messages sent from the console to the peripheral are being dropped due to an unreliable coupling between the console and peripheral, the software sending the unlocking messages may increase the value of the countdown timer to allow more unlocking messages to be sent before the countdown timer expires.
Other implementations, uses and advantages of the invention will be apparent to those skilled in the art from consideration of the specification and practice of the invention disclosed herein. The specification should be considered exemplary only, and the scope of the invention is accordingly intended to be limited only by the following claims.
Claims
- A system for providing a music videogame, the system comprising: a peripheral coupled to a videogame console, the peripheral comprising one or more protected inputs, one or more unprotected inputs, and a countdown timer;videogame software executing on the videogame console, the videogame console comprising one or more physical processors programmed with one or more computer program instructions which, when executed, programs the console to transmit an unlocking message to the peripheral;wherein the peripheral's one or more protected inputs are disabled until the peripheral receives the unlocking message sent by the console and are enabled in response to receiving the unlocking message;wherein the protected inputs are combinations of inputs of the peripheral;wherein the one or more unprotected inputs are not disabled;and wherein the unlocking message comprises a countdown value to be programmed into the countdown timer of the peripheral.
- A method of processing videogame peripheral inputs, comprising: locking at least one protected input of the videogame peripheral, the videogame peripheral including the at least one protected input and unprotected inputs which are not locked, the protected input being a combination of inputs of the videogame peripheral;receiving, in the videogame peripheral, an unlocking message for the at least one protected input, the unlocking message including a value indicative of a countdown time;unlocking the at least one protected input based upon receipt of the unlocking message;starting a timer of the videogame peripheral;and locking the at least one protected input upon the timer reaching a time reflective of the countdown time.
- The method of claim 2 , further comprising resetting the timer upon receiving a further unlocking message in the videogame peripheral.
- The method of claim 2 , wherein the videogame peripheral is a guitar-shaped videogame peripheral for music-based video game.
- The method of claim 4 , wherein the videogame peripheral includes a strum bar input and fret button inputs.
- The method of claim 5 , wherein the at least one protected input comprises a plurality of protected inputs, each of the plurality of protected inputs including a strum bar input and one or more fret button inputs actuated in combination.
- The method of claim 2 wherein locking the at least one protected input is performed by circuitry of the videogame peripheral.
- The method of claim 7 , wherein the circuitry of the videogame peripheral comprises a processor.
Disclaimer: Data collected from the USPTO and may be malformed, incomplete, and/or otherwise inaccurate.