U.S. Pat. No. 10,960,315
MAPPING IDENTIFIER VALUES OF A GAMEPLAY SESSION FOR APPLICATION PROFILING
AssigneeElectronic Arts Inc
Issue DateDecember 3, 2018
Illustrative Figure
Abstract
A computing system may determine values associated with a plurality of identifiers that are associated with a gameplay session of a video gaming application. The computing system may determine a mapping of the values associated with the plurality of identifiers, including associating, for each identifier, each value associated with the respective identifier during a time period of the gameplay session with values that are associated with a respective one or more other identifiers from the plurality of identifiers during at least a portion of the time period of the gameplay session. The computing system may, in response to receiving a query that indicates a value associated with an identifier from the plurality of identifiers, providing values associated with one or more identifiers that are associated with the value associated with the identifier based at least in part on the mapping of the values associated with the plurality of identifiers.
Description
In one or more implementations, not all of the depicted components in each figure may be required, and one or more implementations may include additional components not shown in a figure. Variations in the arrangement and type of the components may be made without departing from the scope of the subject disclosure. Additional components, different components, or fewer components may be utilized within the scope of the subject disclosure. DETAILED DESCRIPTION The detailed description set forth below is intended as a description of various implementations and is not intended to represent the only implementations in which the subject technology may be practiced. As those skilled in the art would realize, the described implementations may be modified in various different ways, all without departing from the scope of the present disclosure. Accordingly, the drawings and description are to be regarded as illustrative in nature and not restrictive. General Overview The disclosed system provides for a keychain service that creates a mapping of the values of identifiers associated with a gameplay session of a video gaming application that may be used to profile the performance of the video gaming application. The disclosed system utilizes values of identifiers associated with the gameplay session of the video gaming application to identify data and information associated with the gameplay session. The disclosed system associates identifier values such that the disclosed system may, in response to receiving a query for a value that is associated with an identifier during a specific time period of the gameplay session, return all values that are associated with identifiers during at least a portion of the specified time period. Because each value associated with an identifier identifies data and information associated with the gameplay session for the time period in which the value is associated with the identifier, the disclosed ...
In one or more implementations, not all of the depicted components in each figure may be required, and one or more implementations may include additional components not shown in a figure. Variations in the arrangement and type of the components may be made without departing from the scope of the subject disclosure. Additional components, different components, or fewer components may be utilized within the scope of the subject disclosure.
DETAILED DESCRIPTION
The detailed description set forth below is intended as a description of various implementations and is not intended to represent the only implementations in which the subject technology may be practiced. As those skilled in the art would realize, the described implementations may be modified in various different ways, all without departing from the scope of the present disclosure. Accordingly, the drawings and description are to be regarded as illustrative in nature and not restrictive.
General Overview
The disclosed system provides for a keychain service that creates a mapping of the values of identifiers associated with a gameplay session of a video gaming application that may be used to profile the performance of the video gaming application.
The disclosed system utilizes values of identifiers associated with the gameplay session of the video gaming application to identify data and information associated with the gameplay session. The disclosed system associates identifier values such that the disclosed system may, in response to receiving a query for a value that is associated with an identifier during a specific time period of the gameplay session, return all values that are associated with identifiers during at least a portion of the specified time period.
Because each value associated with an identifier identifies data and information associated with the gameplay session for the time period in which the value is associated with the identifier, the disclosed system enables the use of a single query to identify a wide variety of information relevant to the time period of the gameplay session, which may be used to perform profiling and debugging of the video gaming application. This is in contrast to techniques that include making multiple queries to a wide variety of servers and devices in order to identify and retrieve information that is relevant to a specific time period of the gameplay session.
As such, the disclosed system addresses a technical problem tied to computer technology and arising in the realm of computer networks, namely the technical problem of making numerous queries and transactions in order to identify and retrieve information that is relevant to a specific time period of the gameplay session of a video gaming application for the purposes of performing profiling and debugging of the video gaming application. The disclosed system solves this technical problem by associating identifier values so that for a given time period in which a value is associated with an identifier, the value is associated with all other values tracked by the disclosed system that are also associated with identifiers during at least a portion of the given time period. This reduces the amount of computations, queries, network transactions, and the like that are needed to identify and retrieve information that is relevant to a specific time period of the gameplay session of a video gaming application for the purposes of performing profiling and debugging of the video gaming application, thereby increasing the speed of the system.
The disclosed system may also address a technical problem tied to identifying data and information stored at a variety of different servers and systems for use in profiling and debugging video gaming applications and debugging video gaming applications, which are concepts inextricably tied to computing technology. While many examples are provided herein in the context of a gameplay session of a video gaming application, the principles of the present disclosure contemplate other types of software applications as well.
Example System Architecture
FIG. 1illustrates an example architecture100for illustrates an example architecture for profiling runtime performance of a gaming application, according to certain aspects of the disclosure. As shown inFIG. 1, the architecture100includes gaming device110, one or more remote gaming devices115, gaming servers120, keychain server130, one or more computing devices135, and one or more artifacts servers140that are connected over network150.
Examples of gaming device110, one or more remote gaming devices115, and one or more computing devices125may include any combinations of a desktop computer, a mobile computer, a laptop computer, a tablet device, a mobile phone, a mobile device, a server, a mainframe, a set-top box, a television, a wearable device (e.g., a computerized watch, computerized eyewear, computerized gloves, etc.), a personal digital assistant (PDA), a video game console, a media player, or any other devices having appropriate processor, memory, and communications capabilities.
One or more gaming servers120, keychain server130, and one or more artifacts servers140may include any device having an appropriate processor, memory, and communications capability for hosting data encoder service. Examples of one or more gaming servers120, keychain server130, and one or more artifacts servers140may include any combinations of desktop computers, laptop computers, mainframes, servers, cloud computing systems, or any other suitable computing systems. In some examples, one or more of servers120,130, and140can be a cloud computing server of an infrastructure-as-a-service (IaaS) and be able to support a platform-as-a-service (PaaS) and software-as-a-service (SaaS) services.
Network150may represent any public or private communications network, such as cellular, Wi-Fi, and/or other types of networks, the Internet, and/or an intranet for transmitting data between computing systems, servers, and computing devices. Network150may include one or more network hubs, network switches, network routers, or any other network equipment that are operably inter-coupled to provide for the exchange of information between gaming device110, one or more remote gaming devices115, gaming servers120, keychain server130, one or more computing devices135, and one or more artifacts servers140.
Gaming device110may be configured to execute video gaming application112. During a gameplay session of video gaming application112, video gaming application112may interact and exchange data with one or more gaming servers120and one or more remote gaming devices115via network150. For example, video gaming application112may communicate with one or more gaming servers120to log onto a gaming network and to find one or more online players at one or more remote gaming devices115in order to start a game between the player at video gaming application112and the one or more online players. In other examples, video gaming application112may communicate with one or more gaming servers120via network150to download gaming levels, update the online scoreboard, and the like.
A gameplay session of video gaming application112may be a time period where video gaming application112executes at gaming device110that starts when a player (i.e., user of video gaming application112) starts up video gaming application112at gaming device110, and ends when the user exits video gaming application112. During a gameplay session, the user may start and play one or more games. For example, the user may start and end one or more games during the gameplay session. Such games may include offline games where video gaming application112does not communicate with one or more remote gaming devices115or one or more gaming servers120, and/or online games where the player at video gaming application112may play with or against online players at one or more remote gaming devices115that communicate with one or more gaming servers120via network150.
During the gameplay session, video gaming application112may encounter a variety of data and information that are sent from, received by, and/or created by video gaming application112. For example, video gaming application112may create and send a player identifier to log into a gaming system at one or more gaming servers120. In another example, video gaming application112may create or receive a level identifier that indicates the level of the game being played during the gameplay session of video gaming application112. The value of the level identifier may change each time a new level is reached during the gameplay session, so that each value of the level identifier is associated with each level reached during the gameplay session. In another example, in order to start an online gaming session, video gaming application112may send a request for, and receive, a matchmaking identifier from one or more gaming servers120that identifies the details of an online gaming session in which the player at video gaming application112is matched with a remote player at one of one or more remote gaming devices115.
Video gaming application112may encounter two kinds of identifiers: system identifiers and contextual identifiers. System identifiers may be identifiers associated with data at one or more external systems (e.g., one or more gaming servers120), while context identifiers may be identifiers associated with context of video gaming application112. Examples of system identifiers include player identifiers, matchmaking identifiers, and the like. These identifiers may be communicated by video gaming application112to external systems such as one or more gaming servers120. For example, video gaming application112may send a player identifier to one or more gaming servers120to log on to a gaming network. In another example, video gaming application112may receive a matchmaking identifier as part of establishing an online gaming session.
The system identifiers may be associated with values that may be used to access data and information that exist at external systems such as one or more gaming servers120. For example, one or more gaming servers120may store information associated with online gaming sessions, where the information about a particular online gaming session includes an indication of the matchmaking identifier value associated with the online gaming session along with additional information regarding the online gaming session. Thus, the value associated with a matchmaking identifier may be used to retrieve additional information regarding the associated online gaming session. In this way the value associated with a matchmaking identifier is associated with data stored at an external system regarding an online gaming session.
In another example, one or more gaming servers120may store information associated with players that are part of a gaming network, which may be indexed based on the player identifier value associated with the player. Thus, the value associated with a player identifier may be used to retrieve additional information associated with the player from external systems, such as one or more gaming servers120.
Examples of contextual identifiers associated with the context of video gaming application112may include build version identifiers associated with values that identify the build version of video gaming application112, user name identifiers associated with values that identify the user names that were logged into video gaming application112during gameplay session206, platform identifiers associated with values that identify the computing platform of gaming device110, level identifiers associated with values that identify levels of video gaming application112that were played during a gameplay session, start position identifiers associated with values that identifies the start positions of the video gaming application112during the gameplay session, video card identifiers associated with values that identify the type of video card installed in gaming device110, and the like.
Artifacts server140may be configured to execute artifacts engine142to generate artifacts associated with the gaming session of video gaming application112. Artifacts associated with the gaming session of video gaming application112may include files and documents that are generated by artifacts engine142outside of the gaming session of video gaming application112. Artifacts server140may execute artifacts engine142during a gaming session or after a gaming session in order to generate artifacts associated with the gaming session. Examples of artifacts generated by artifacts engine142may include telemetry data associated with the gaming session, gameplay logs associated with the gameplay session, screenshots associated with the gaming session, bug reports associated with the gaming session, and the like. Artifacts server140may execute artifacts engine142to generate artifact identifiers having values that indicate the artifacts generated by artifacts engine142. Artifact identifiers may include bug identifiers telemetry identifiers, screenshot identifiers, and the like.
Keychain server130may be configured to execute keychain service132to receive indications of values associated with identifiers that are associated with a gameplay session of a video gaming application112. Keychain service132may receive indications of values associated with one or more system identifiers and one or more contextual identifiers from video gaming application112. Keychain service132may also receive indications of values associated with one or more artifact identifiers from artifacts engine142.
Keychain service132may execute to determine a mapping of the values associated with the identifiers. Keychain service132may associate, for each identifier from the identifiers, each value associated with the respective identifier during a time period of the gameplay session with values that are associated with one or more other identifiers during at least a portion of the time period of the game play session. Thus, for each value that is associated with an identifier for a specified period of time during the gameplay session, keychain service132may associate the values that is associated with the identifier with other values that are also associated for at least a portion of the specified period of time, with other identifiers.
Keychain service132may use the mapping of the values associated with the identifiers to determine, for a value associated for a period of time with an identifier, all other associated values that are associated for at least a portion of the period of time with other identifiers. For example, if a value “M1234” is associated for a period of time during the gaming session with a matchmaking identifier, and if a value “P1234” is associated with a player identifier for at least a portion of the same period of time during the gaming session, then keychain service132may be queried using the value “M1234” associated with the matchmaking identifier to return the value “P1234” associated with the player identifier.
In this way, keychain service132enables the use of a single value associated with an identifier to identify associated values associated with other identifiers. This enables a profiling application or a debugging application, which may execute at one or more computing devices135, to communicate with and utilize keychain service132to quickly discover all of the values associated at identifiers at a particular time during the gaming session by just knowing one value associated with an identifier at the particular time during the gaming session.
Example Profiling System
FIG. 2is a block diagram illustrating an example gaming device110, example keychain server130, and example artifacts server140communicating via example network150in the example architecture100ofFIG. 1according to certain aspects of the disclosure. As shown inFIG. 2, gaming device110, keychain server130, and artifacts server140may be connected over the network150via respective communications modules210,224, and244. The communications modules210,224, and244are configured to interface with the network150to send and receive information, such as data, requests, responses, and commands to other devices on the network. The communications modules210,224, and244can be any suitable wired or wireless network interfaces, such as modems or Ethernet cards.
Gaming device110includes a processor212, the communications module210, and the memory202that includes video gaming application112. Gaming device110also includes input device216, such as a keyboard, mouse, touchscreen, joystick, steering wheel and the like, and output device214such as a display device. Processor212of gaming device110is configured to execute instructions, such as instructions physically coded into processor212, instructions received from software in memory202, or a combination of both. For example, processor212of gaming device110may receive and execute instructions of video gaming application112to perform the functionality of video gaming application112. Processor212may execute instructions of video gaming application112to receive input data from input device216and to output data such as graphical content, audio content, and the like at output device214.
Video gaming application112may be any suitable video gaming application that may be played by a user via input device216, including but not limited to roleplaying video games, first person shooter video games, sports video games, and the like. In some examples, video gaming application112may be single player video games or multiplayer video games. Video gaming application112may be played entirely offline or may be played online by interacting with one or more gaming servers120via network150. Video gaming application112may interact with one or more gaming servers120to log into a gaming network hosted on one or more gaming servers120and/or to match the user of video gaming application112with other users so that the user of video gaming application112may play video gaming application112against other users or cooperatively play video gaming application112with other users.
During gameplay session206, video gaming application112may encounter two kinds of identifiers associated with gameplay session206: system identifiers and contextual identifiers. System identifiers may be identifiers associated with data at one or more external systems (e.g., one or more gaming servers120), while context identifiers may be identifiers associated with context of video gaming application112. Examples of system identifiers include player identifiers, matchmaking identifiers, and the like. These identifiers may be communicated by video gaming application112to external systems such as one or more gaming servers120. For example, video gaming application112may send a player identifier to one or more gaming servers120to log on to a gaming network. In another example, video gaming application112may receive a matchmaking identifier as part of establishing an online gaming session.
Examples of contextual identifiers associated with the context of video gaming application112may include build version identifiers associated with values that identify the build version of video gaming application112, user name identifiers associated with values that identify the user names that were logged into video gaming application112during gameplay session206, platform identifiers associated with values that identify the computing platform of gaming device110, level identifiers associated with values that identify levels of video gaming application112that were played during gameplay session206, start position identifiers associated with values that identifies the start positions of the video gaming application112during gameplay session206, video card identifiers associated with values that identify the type of video card installed in gaming device110, and the like.
Video gaming application112may include keychain extension208. Keychain extension208may be instructions that processor212may receive and execute to determine values associated with identifiers that are utilized by video gaming application112during gameplay session206and to send, via communications module210and network150, indications of the identifiers and the associated values that are utilized by video gaming application112during gameplay session206to keychain server130. As gameplay session206progresses, video gaming application112may encounter identifiers and values associated with identifiers. For example, video gaming application112may encounter new identifiers associated with values as well as previously-encountered identifiers associated with an updated value. As video gaming application112encounters identifiers associated with values, keychain extension208may send indications of the identifiers and the associated values to keychain server130.
Artifacts server140includes processor242, communications module244, and memory246that includes artifacts engine142and artifacts storage250. Processor242of artifacts server140is configured to execute instructions, such as instructions physically coded into processor242, instructions received from software in memory246, or a combination of both. For example, processor242of artifacts server140may receive and execute instructions of artifacts engine142to perform the functionality of artifacts engine142.
Artifacts engine142may execute at processor242to generate artifacts associated with gameplay session206of video gaming application112that executes at gaming device110. Artifacts engine142may generate artifacts associated with gameplay session206of video gaming application112outside of gameplay session206. In other words, artifacts engine142may include applications, modules, services, processes, and the like that execute separately from video gaming application112. Such applications, modules, services, processes, and the like may execute to generate artifacts associated with gameplay session206during gameplay session206and even after gameplay session206has ended.
In the example ofFIG. 2, artifacts engine142includes telemetry module252, bug tracking module254, and screenshot module256. Modules252,254, and256are just some examples of applications, modules, services, processes, and the like that may execute to generate artifacts associated with gameplay session206, and architecture100may include any other applications, modules, services, processes, and the like that may execute to generate artifacts associated with gameplay session206. Further, while modules252,254, and256are named “modules” in the present disclosure, modules252,254, and256may be implemented as applications, modules, services, processes, and the like that may execute to generate artifacts associated with gameplay session206.
Telemetry module252may execute at processor242to monitor gameplay session206, to generate telemetry data associated with gameplay session206based on the monitoring of gameplay session206, and to store the generated telemetry data in artifacts storage250. Telemetry module252may execute to monitor an entire gameplay session206or may execute to monitor only certain portions (e.g., certain time periods) of gameplay session206. As such telemetry data generated by telemetry module252may be associated with specific time periods during gameplay session206where telemetry module252monitored gameplay session206to generate the telemetry data. Telemetry data generated by telemetry module252may include performance data associated with gameplay session206, user interaction data associated with user interactions with video gaming application112during gameplay session206, gameplay logs associated with gameplay session206, and the like. Telemetry module252may generate telemetry identifier values (e.g., values associated with the telemetry identifier) to identify telemetry data generated by telemetry module252. Telemetry module252may execute to send telemetry identifiers and associated values to keychain service132so that keychain service132may associate the telemetry identifiers and associated values with the keychain for gameplay session206. Because telemetry data may be associated with specific time periods within gameplay session206, telemetry module252may send, along with the telemetry identifiers and associated values, indications of the time periods within gameplay session206that are associated with the telemetry identifiers and associated values to keychain service132.
Bug tracking module254may execute at processor242to track bugs that occur at gameplay session206, to generate bug reports associated with gameplay session206, and to store the generated bug reports in artifacts storage250. In some examples, bug tracking module254may be triggered by execute at processor242when video gaming application112crashes during gameplay session206. In other examples, bug tracking module254may execute during gameplay session206to generate bug reports. Bug tracking module254may also be used after gameplay session206has ended so that a user may use bug tracking module254to create bug reports.
Bug reports may be associated with specific times in gameplay session206, such as specific times in gameplay session206when bugs occur. For example, when bug tracking module254executes to generate a bug report in response to video gaming application112crashing during gameplay session206, bug tracking module254may execute to associate the bug report with the specific time within gameplay session206when the crash occurred. In another example, after gameplay session206has ended, a developer or tester of video gaming application112may use development or testing tools to replay gameplay session206and may use bug tracking module254to create bug reports and associate them with specific times within gameplay session206.
Bug tracking module254may generate bug identifier values (e.g., values associated with the bug identifier) to identify bug reports generated by bug tracking module254. Bug tracking module254may execute to send bug identifiers and associated values to keychain service132so that keychain service132may associate the bug identifiers and associated values with the keychain for gameplay session206. Because bug reports generated by bug tracking module254may be associated with specific times within gameplay session206, bug tracking module254may send, along with the bug identifiers and associated values, indications of the times within gameplay session206that are associated with the bug identifiers and associated values to keychain service132.
Screenshot module256may execute at processor242to capture screenshots of video frames that video gaming application112outputs for display at output device214during gameplay session206. Video frames may be any frame of graphics data that video gaming application112outputs for display at output device214during gameplay session206. In some examples, screenshot module256may execute during gameplay session206to take screenshots of video frames that video gaming application112outputs for display at output device214at specific times during gameplay session206. In other examples, after gameplay session206has ended, a developer or tester of video gaming application112may use development or testing tools to replay gameplay session206and may use screenshot module256to take screenshots of video frames that video gaming application112outputs for display at output device214at specific times during the replay of gameplay session206.
Each screenshot captured by screenshot module256is associated with a screenshot identifier value that is embedded within the screenshot itself. The screenshot identifier value may be visually embedded within a screenshot, such that the value of the screenshot identifier may be readily apparent via visually inspecting the screenshot. In other examples, the value of the screenshot identifier may be embedded within metadata of the screenshot.
In some examples, video gaming application112may embed screenshot identifier values within the video frames it outputs for display during gameplay session206. Video gaming application112may generate graphical frames that visually includes an indication of the screenshot identifier value within the video frame, or may modify a video frame to include an indication of the screenshot identifier before it outputs the modified video frame for display during gameplay session206. In these examples, screenshot module256may capture screenshots of video frames that are output by video gaming application112for display during gameplay session206and may save the captured screenshots in artifacts storage250. In other examples, screenshot module256may capture screenshots of video frames that are output by video gaming application112for display during gameplay session206, modify the captured screenshots to embed an indication of the screenshot identifier value within each of the captured screenshots, and save the modified screenshots in artifacts storage250.
Each screenshot is associated with a specific time within gameplay session206corresponding to when the screenshot was taken during gameplay session206. Because screenshots saved to artifacts storage250already includes an indication of the screenshot identifier value within each of the screenshots, screenshot module256may execute to send screenshots that it has captured to keychain service132along with the specific times within gameplay session206that corresponds to when each of the screenshots was taken.
As such, artifacts engine142executes at processor242to generate artifacts associated with gameplay session206of video gaming application112, and to store the generated artifacts in artifacts storage250. Artifacts generated by artifacts engine142include telemetry data generated by telemetry module252, bug reports generated by bug tracking module254, and screenshots captured by screenshot module256.
Artifacts engine142executes at processor242to associate artifact identifiers and values associated with artifact identifiers with the generated artifacts stored in artifacts storage250, so that each value associated with an artifact identifier identifies an artifact stored in artifacts storage250. The artifact identifiers include telemetry identifiers that identify telemetry reports stored in artifacts storage250, the bug identifiers identify bug reports stored in artifacts storage250, and the screenshot identifiers identify screenshots stored in artifacts storage250. As discussed above, indications of screenshot identifiers are directly embedded within screenshots.
Each artifact stored in artifacts storage250may be associated with a specific time within gameplay session206or a specific time period within gameplay session206. Artifacts engine142may execute at processor242to send to keychain service132indications of values associated with artifact identifiers as well as indications of specific times or time periods within gameplay session206associated with the artifacts indicated by the values associated with the artifact identifiers.
Artifacts engine142executes at processor242to send indications of values associated with telemetry identifiers that are associated with telemetry data stored in artifacts storage250along with specific times within gameplay session206or a specific time period within gameplay session206associated with the telemetry data. Artifacts engine142executes at processor242to send indications of values associated with bug identifiers that are associated with bug reports stored in artifacts storage250along with specific times within gameplay session206or a specific time period within gameplay session206associated with the bug reports. Artifacts engine142executes at processor242to send indications of screenshots stored in artifacts storage250along with specific times within gameplay session206or a specific time period within gameplay session206associated with the screenshots. In this way, artifacts engine142executes to send indications of values associated with artifact identifiers that are associated with artifacts stored in artifacts storage250along with specific times within gameplay session206or a specific time period within gameplay session206associated with the artifacts to keychain service132.
Keychain server130includes processor222, communications module224, and memory226that includes keychain storage228and keychain service132. Processor222of keychain server130is configured to execute instructions, such as instructions physically coded into processor222, instructions received from software in memory226, or a combination of both. For example, processor222of keychain server130may receive and execute instructions of keychain service132to perform the functionality of keychain service132.
Keychain service132may execute at processor222to receive indications of values associated with a plurality of identifiers that are associated with gameplay session206of video gaming application112from video gaming application112at gaming device110and artifacts engine142at artifacts server140. The plurality of identifiers associated with gameplay session206may include one or more system identifiers associated with data at one or more external systems, such as one or more gaming servers120and/or one or more remote gaming devices115, one or more contextual identifiers associated with context of video gaming application112, and one or more artifact identifiers that are generated outside of gameplay session206.
Receiving an indication of a value associated with an identifier may include receiving a “, ” pair, where “” is the name of an identifier and “” is the value associated with the named identifier. One example of a “, ” pair received by keychain service132may be “Matchmaking ID, 3987”, which indicates a matchmaking identifier having an associated value of 3987.
Keychain service132may execute at processor222to receive indications of values associated with the one or more system identifiers associated with gameplay session206and indications of values associated with one or more contextual identifiers associated with gameplay session206from video gaming application112. Examples of system identifiers associated with gameplay session206may include matchmaking identifiers associated with online gaming sessions during gameplay session206, player identifier associated with a gaming network that video gaming application112is logged into during gameplay session206, and the like. The values associated with matchmaking identifiers may identify data regarding specific online gaming sessions that took place during gameplay session206that are stored at devices and servers external to gaming device110, such as one or more gaming servers120and/or one or more remote gaming devices115. Such data may include information such as the players involved in the online gaming session, the location (e.g., network address) and characteristics of the server device that hosted the online gaming session, and other details of the online gaming session. The values associated with the player identifier may identify the gaming network that video gaming application112is logged into during gameplay session206, and may identify data and information associated with the gaming network, such as information regarding the server of the gaming network to which the video gaming application112was connected during gameplay session206.
Examples of contextual identifiers associated with gameplay session206may include build version identifiers associated with values that identify the build version of video gaming application112, user name identifiers associated with values that identify the user names that were logged into video gaming application112during gameplay session206, platform identifiers associated with values that identify the computing platform of gaming device110, level identifiers associated with values that identify levels of video gaming application112that were played during gameplay session206, start position identifiers associated with values that identifies the start positions of the video gaming application112during gameplay session206, video card identifiers associated with values that identify the type of video card installed in gaming device110, and the like.
Keychain service132may execute at processor222to receive indications of values associated with the one or more artifact identifiers associated with gameplay session206from artifacts engine142. Artifact identifiers may be associated with values that identify artifacts stored in artifacts storage250. Examples of artifact identifiers associated with gameplay session206may include bug identifiers associated with values that identify bug reports associated with gameplay session206, telemetry identifiers associated with values that identify telemetry data associated with gameplay session206, and screenshot identifiers associated with values associated with screenshots.
Each of the values associated with the plurality of identifiers may be associated with a specific time or time period within gameplay session206. A specific time associated with a value associated with an identifier may be the specific time within gameplay session206when the identifier is associated with the value. Similarly, a specific time period associated with a value associated with an identifier may be the specific time period within gameplay session206during which the identifier is associated with the value. As such, receiving indications of values associated with a plurality of identifiers associated with gameplay session206may include receiving indications of one of: a specific time or a specific time period within gameplay session206that is associated with each of the values associated with the plurality of identifiers. In some examples, if keychain service132does not receive an indication of at least one of: a specific time or a specific time period associated with a value associated with an identifier, keychain service132may default to the value being associated with the identifier for the entirety of gameplay session206.
Mapping module234of keychain service132may execute at processor222to associate a keychain identifier value with a gaming session of video gaming application112, such as gameplay session206of video gaming application112. A keychain identifier value may be a value associated with a keychain identifier that uniquely identifies a keychain of identifiers and associated values associated with gameplay session206. Mapping module234may further execute at processor222to generate a keychain associated with gameplay session206that is a mapping of the values associated with the plurality of identifiers associated with the gameplay session206. Examples of the keychain may include any suitable structured data, such as database records, graphs, linked lists, trees, and the like that relates the values associated with the plurality of identifiers associated with gameplay session206.
Mapping module234may execute at processor222to determine a mapping of the values associated with the plurality of identifiers by associating, for each identifier from the plurality of identifiers associated with gameplay session206during a time period, each value associated with the respective identifier during a time period of gameplay session206with at least one of: values that are associated with one or more other identifiers from the plurality of identifiers during at least a portion of the time period of gameplay session206. The mapping of the values associated with the plurality of identifiers may be referred to as a keychain of the values associated with the plurality of identifiers.
Mapping module234may determine the mapping of the values associated with the plurality of identifiers based at least in part on indications of one of: a specific time or a specific time period within gameplay session206that is associated with each of the values associated with the plurality of identifiers. Mapping module234may, for each value associated with an identifier during a specified time period within gameplay session206, associate the value for each of one or more values that are associated with one or more identifiers during at least a portion of the specified time period within gameplay session206.
Thus, the result of mapping module234determining the mapping of the values associated with the plurality of identifiers may include each of the plurality of values associated with the plurality of identifiers being associated with a specific time or specific time period within gameplay session206during which the value is associated with a specific identifier, and each of the values may be associated with one or more other values that are associated with one or more other identifiers during at least a portion of the specific time or specific time period. For example, for each value that is associated with an identifier during time period txto tywithin gameplay session206, mapping module234may determine all values that are associated with identifiers for at least a portion of the time period txto tywithin gameplay session206, and may associate the set of values associated with identifiers determined by mapping module234with each other.
In this way, mapping module234may determining the mapping of the values associated with the plurality of identifiers. Such a mapping of the values associated with the plurality of identifiers may enable a single value associated with an identifier to be used to index into all other values associated with identifiers during at least a portion of the time period in which the single value is associated with the identifier. For example, if a user knows only the value of associated with a bug identifier, the user may query the mapping of values using the known value associated with the bug identifier to find all other values that are associated with identifiers at the time during which the known value is associated with the bug identifier. The mapping of values may, for example, return a value associated with a matchmaking identifier, which the user may use to query one or more gaming server120to receive information related to the online gaming session identified by the value associated with the matchmaking identifier, thereby enabling quick and easy retrieval of information that may be used to debug or profile video gaming application112.
Keychain service132may store the mapping of the values associated with the plurality of identifiers in keychain storage228in any structured fashion. For example, the mapping of the values associated with the plurality of identifiers may be stored as database records of a relational database, such as a Structured Query Language (SQL) database.
Keychain service132may provide interfaces236for querying and accessing the keychain of the values associated with the plurality of identifiers stored in keychain storage228. In some examples, interfaces236may receive a query that indicates a value associated with an identifier from the plurality of identifiers. Interfaces236may, in response to receiving the query that indicates the value associated with the identifier from the plurality of identifiers, provide values associated with one or more identifiers that are associated with the value associated with the identifier as indicated by the query based at least in part on the mapping of the values associated with the plurality of identifiers.
Because the value associated with the identifier as indicated by the query is associated with the indicated identifier for a specified time period within gameplay session206, the values associated with one or more identifiers provided by interfaces236in response to the query may be values that are associated with the one or more identifiers during at least a portion of the specified time period.
In some examples, interfaces236may provide a publish and subscribe interface that may receive, from downstream services, subscription requests for identifiers from the plurality of identifiers of a gameplay session, such as gameplay session206. In response to receiving an indication of a request to subscribe to an identifier from the plurality of identifiers for a gameplay session from a requesting computing device, such as one or more computing devices135, interfaces236may send updated values associated with the indicated identifier as keychain service132receives updated values associated with the indicated identifier from gaming device110and/or artifacts server140until the end of the gameplay session. For example, if interfaces236receives a request to subscribe to a bug identifier for gameplay session206from a requesting computing device, interfaces236may, from the start of gameplay session206, send updated values associated with the bug identifier to the requesting computing device upon receiving updated values associated with the bug identifier from artifacts engine142until the end of gameplay session206.
In some examples, if the mapping of the values associated with the plurality of identifiers is stored as database records of a structured database, such as a SQL database, interfaces236may be able to receive and respond to structured database queries, such as SQL queries for specific records of the database containing associations of values and identifiers, and may be able to respond to such structured database queries with the requested associations of values and identifiers based on the queries.
FIG. 3Ais a block diagram illustrating an example timeline of example identifiers and example artifacts associated with an example gaming session, according to certain aspects of the disclosure.FIG. 3Ais described with respect to the components of architecture100inFIGS. 1 and 2.FIG. 3Ais just an example of some of the example values of example identifiers and artifacts that may be associated with an example gaming session, and it should be understood that a gaming session may be associated with any number of identifiers and artifacts having any number of suitable values not illustrated byFIG. 3A.
As shown inFIG. 3A, values302,304,306,307,308,310,312,314,316,318, and320associated with identifiers322,324,326,328,330,332, and334are associated with gameplay session206, and are plotted in timeline300from the start of gameplay session206at time to to the end of gameplay session206at t7. Timeline300illustrates that values302,304,306,307,308,310,312,314,316,318, and320are associated with identifiers322,324,326,328,330,332, and334at either a specific time between the start of gameplay session206at time to to the end of gameplay session206at time t7or within a specific time period between the start of gameplay session206at time to to the end of gameplay session206at time t7. Thus, while a value is associated with an identifier during a time period within gameplay session206, another identifier during that same period may change its associated values and may be associated with two or more values during that same time period.
As can be seen, at any point in time in timeline300, one or more identifiers may each be associated with a single value. Meanwhile, during a time period in timeline300, it is possible for one or more identifiers to each be associated with a single value, while another one or more identifiers may each be associated with two or more different values. By determine a mapping of the values associated with the plurality of identifiers and the plurality of artifacts, keychain service132generates a representation of a timeline of values associated with artifacts, such as timeline300, and stores such a representation of a timeline of values associated with artifacts in keychain storage228. Further, keychain service132may also track the start of gameplay session206(i.e., at time t0) and the end of gameplay session206(i.e., at time t7) to maintain a timeline independent of the individual identifiers322-334that are tracked by keychain service132. By tracking the start and the end of gameplay session206, keychain service132may be able to coordinate with downstream services to enable such downstream services to subscribe to and receive updated values of identifiers of gameplay session206during the duration of gameplay session206.
In the example ofFIG. 3A, because value302of keychain identifier322and value304of player identifier324do not change during gameplay session206, keychain service132may execute at processor222of keychain server130to associate value302of keychain identifier322with value304of player identifier324, and may also associate value302of keychain identifier322and value304of player identifier324with values306,307,308,310,312,314,316,318, and320of all other identifiers326,328,330,332, and334associated with gameplay session206.
Level identifier326associated with gameplay session206may indicate the level of the game in gaming application that is currently being played. Because a player may move through different levels of the game during gameplay session206, such as by finishing a first level to move onto a second level, level identifiers326may be associated with different values306,307, and316during gameplay session206that indicate the different levels of the game encountered during gameplay session206. In the example ofFIG. 3A, level identifier326may be associated with value306from time t0to time t3, associated with value307from time t3to time t5, and associated with value316from time t5to time t7.
Matchmaking identifier328associated with gameplay session206may indicate each different online game between the player of video gaming application112and an online opponent. Thus, each time video gaming application112starts a game with an online opponent, matchmaking identifier328may be associated with a different value from the start of the game until the game ends. In the example ofFIG. 3A, matchmaking identifier328may be associated with value308from time t0to time t5and associated with value318from time t5to time t7.
Artifact identifier330associated with gameplay session206may identify an artifact associated with a specific time within gameplay session206, such as a screenshot of gameplay session206. In the example ofFIG. 3A, artifact identifier330may be associated with value312at time t1, which may be the specific time within gameplay session206when the screenshot associated with value312of artifact identifier330was taken.
Bug identifier332associated with gameplay session206may identify bug reports associated with gameplay session206. For example, a player or a tester of video gaming application112may submit bug reports at specific times within gameplay session206. In the example ofFIG. 3A, bug identifier332may be associated with value310at time t1and with value320at time t6that are associated with bug reports submitted at times t1and t6within gameplay session206, respectively.
Telemetry identifier334associated with gameplay session206may identify telemetry data associated with a time period within gameplay session206. For example, a telemetry application or process may execute at, for example, processor212of gaming device110or at processor242of artifacts server140that monitors video gaming application112and obtains telemetry data based on the monitoring of video gaming application112. In the example ofFIG. 3A, telemetry identifier334may be associated with value314from time t2to time t4within gameplay session206that is associated with telemetry data captured from time t2to time t4of gameplay session206.
Keychain service132may execute at processor222to determine associations of values302,304,306,307,308,310,312,314,316,318, and320of identifiers322,324,326,328,330,332, and334to associate each value that is associated with an identifier during a time period of gameplay session206with values associated with one or more other identifiers during at least a portion of the same time period of gameplay session206.
Keychain service132may execute at processor222to associate value302associated with keychain identifier322during the time period t0to t7with values that are associated with identifiers during at least a portion of the same time period t0to t7of gameplay session206. Because values304,306,307,310,312,314,316,318, and320are all associated with identifiers324,326,328,330,332, and334during at least a portion of the time period t0to t7of gameplay session206, keychain service132may execute to associate value302associated with keychain identifier322with value304associated with player identifier324, values306,307, and316associated with level identifier326, values308and318associated with matchmaking identifiers328, value312associated with artifact identifier330, values310and320associated with bug identifier332, and value314associated with telemetry identifier334.
Keychain service132may execute at processor222to associate value304associated with keychain identifier324during the time period to to t7with values that are associated with identifiers during at least a portion of the same time period to to t7of gameplay session206. Because values302,306,307,310,312,314,316,318, and320are all associated with identifiers322,326,328,330,332, and334during at least a portion of the time period t0to t7of gameplay session206, keychain service132may execute to associate value304associated with player identifier324with value302associated with keychain identifier322, values306,307, and316associated with level identifier326, values308and318associated with matchmaking identifiers328, value312associated with artifact identifier330, values310and320associated with bug identifier332, and value314associated with telemetry identifier334.
Keychain service132may execute at processor222to associate value306associated with level identifier326during the time period t0to t3with values that are associated with identifiers during at least a portion of the same time period t0to t3of gameplay session206. Because values302,304,308,310,312, and314are all associated with identifiers322,324,328,332,330, and334, respectively, during at least a portion of the same time period t0to t3of gameplay session206, keychain service132may execute to associate value302associated with keychain identifier322with value306associated with level identifier326, value304associated with player identifier324with value306associated with level identifier326, value308associated with matchmaking identifier328with value306associated with level identifier326, value312associated with artifact identifier330with value306associated with level identifier326, value310associated with bug identifier332with value306associated with level identifier326, and value314associated with telemetry identifier334with value306associated with level identifier326.
Keychain service132may execute at processor222to associate value307associated with level identifier326during the time period t3to t5with values that are associated with identifiers during at least a portion of the same time period t3to t5of gameplay session206. Because values302,304,308, and314are all associated with identifiers322,324,328, and334, respectively, during at least a portion of the same time period t3to t5of gameplay session206, keychain service132may execute to associate value302associated with keychain identifier322with value307associated with level identifier326, value304associated with player identifier324with value307associated with level identifier326, value308associated with matchmaking identifier328with value307associated with level identifier326, and value314associated with telemetry identifier332with value307associated with level identifier326.
Keychain service132may execute at processor222to associate value316associated with level identifier326during the time period t5to t7with values that are associated with identifiers during at least a portion of the same time period t5to t7of gameplay session206. Because values302,304,318, and320are all associated with identifiers322,324,328, and332, respectively, during at least a portion of the same time period t5to t7of gameplay session206, keychain service132may execute to associate value302associated with keychain identifier322with value316associated with level identifier326, value304associated with player identifier324with value316associated with level identifier326, value318associated with matchmaking identifier328with value316associated with level identifier326, and value320associated with bug identifier332with value316associated with level identifier326.
Keychain service132may execute at processor222to associate value308associated with level identifier328during the time period t0to t3with values that are associated with identifiers during at least a portion of the same time period t0to t5of gameplay session206. Because values302,304,306,307,310,312, and314are all associated with identifiers322,324,328,332,330, and334during at least a portion of the same time period t0to t5of gameplay session206, keychain service132may execute to associate value302associated with keychain identifier322with value308associated with level identifier328, value304associated with player identifier324with value308associated with level identifier328, value306associated with level identifier326with value308associated with level identifier328, value307associated with level identifier326with value308associated with level identifier328, value312associated with artifact identifier330with value308associated with level identifier328, value310associated with bug identifier332with value308associated with level identifier328, and value314associated with telemetry identifier334with value308associated with level identifier328.
Keychain service132may execute at processor222to associate value318associated with matchmaking identifier328during the time period t5to t7with values that are associated with identifiers during at least a portion of the same time period t5to t7of gameplay session206. Because values302,304,316, and320are all associated with identifiers322,324,326, and332, respectively, during at least a portion of the same time period t5to t7of gameplay session206, keychain service132may execute to associate value302associated with keychain identifier322with value318associated with matchmaking identifier328, value304associated with player identifier324with value318associated with matchmaking identifier328, value316associated with level identifier326with value318associated with matchmaking identifier328, and value320associated with bug identifier332with value318associated with matchmaking identifier328.
Keychain service132may execute at processor222to associate value312associated with artifact identifier330at time t1with values that are associated with identifiers at time t1of gameplay session206. Because values302,304,306,308, and310are associated with identifiers322,324,326,328, and332during time t1of gameplay session206, keychain service132may execute to associate value302associated with keychain identifier322with value312associated with artifact identifier330, value304associated with player identifier324with value312associated with artifact identifier330, value306associated with level identifier326with value312associated with artifact identifier330, value308associated with level identifier326with value312associated with artifact identifier330, and value310associated with bug identifier332with value312associated with artifact identifier330.
Keychain service132may execute at processor222to associate value310associated with bug identifier332at time t1with values that are associated with identifiers at time t1of gameplay session206. Because values302,304,306,308, and312are associated with identifiers322,324,326,328, and332during time t1of gameplay session206, keychain service132may execute to associate value302associated with keychain identifier322with value310associated with bug identifier332, value304associated with player identifier324with value310associated with bug identifier332, value306associated with level identifier326with value310associated with bug identifier332, value308associated with level identifier326with value310associated with bug identifier332, and value312associated with artifact identifier330with value310associated with bug identifier332.
Keychain service132may execute at processor222to associate value320associated with bug identifier332at time t6with values that are associated with identifiers at time t6of gameplay session206. Because values302,304,316, and318are associated with identifiers322,324,326, and328during time t6of gameplay session206, keychain service132may execute to associate value302associated with keychain identifier322with value320associated with bug identifier332, value304associated with player identifier324with value320associated with bug identifier332, value316associated with level identifier326with value320associated with bug identifier332, and value318associated with level identifier326with value320associated with bug identifier332.
Keychain service132may execute at processor222to associate value314associated with telemetry identifier334during the time period t2to t4with values that are associated with identifiers during the time period t2to t4of gameplay session206. Because values302,304,306,307, and308are associated with identifiers322,324,326, and328during the time period t2to t4of gameplay session206, keychain service132may execute to associate value302associated with keychain identifier322with value314associated with telemetry identifier334, value304associated with player identifier324value314associated with telemetry identifier334, value306associated with level identifier326with value314associated with telemetry identifier334, value307associated with level identifier326with value314associated with telemetry identifier334and value308associated with level identifier326with value314associated with telemetry identifier334.
As can be seen, a value associated with an identifier during a time period during gameplay session206may be associated with values that are associated with other identifiers during at least a portion of the same time period. For example, value306that is associated with level identifier326during the time period t0to t3may be associated with values that are associated with identifiers only during a part (but not all) of the time period t0to t3, such as value310that is associated with bug identifier322only at time t1. Further, a value associated with an identifier during a time period during gameplay session206may include an identifier that is associated with an identifier only at a specific time, such as value310that is associated with bug identifier322only at time t1.
In addition, a value associated with an identifier during a time period during gameplay session206may be associated with different values that are associated with the same identifier during at least a portion of the time period when the value is associated with the identifier. For example, value314that is associated with telemetry identifier314during the time period t2to t4may be associated with both values306and307associated with level identifier326because level identifier326is associated with value306during time period t2to t3and is further associated with value307during time period t3to t4, where both time periods t2to t3and t3to t4are within the time period t2to t4.
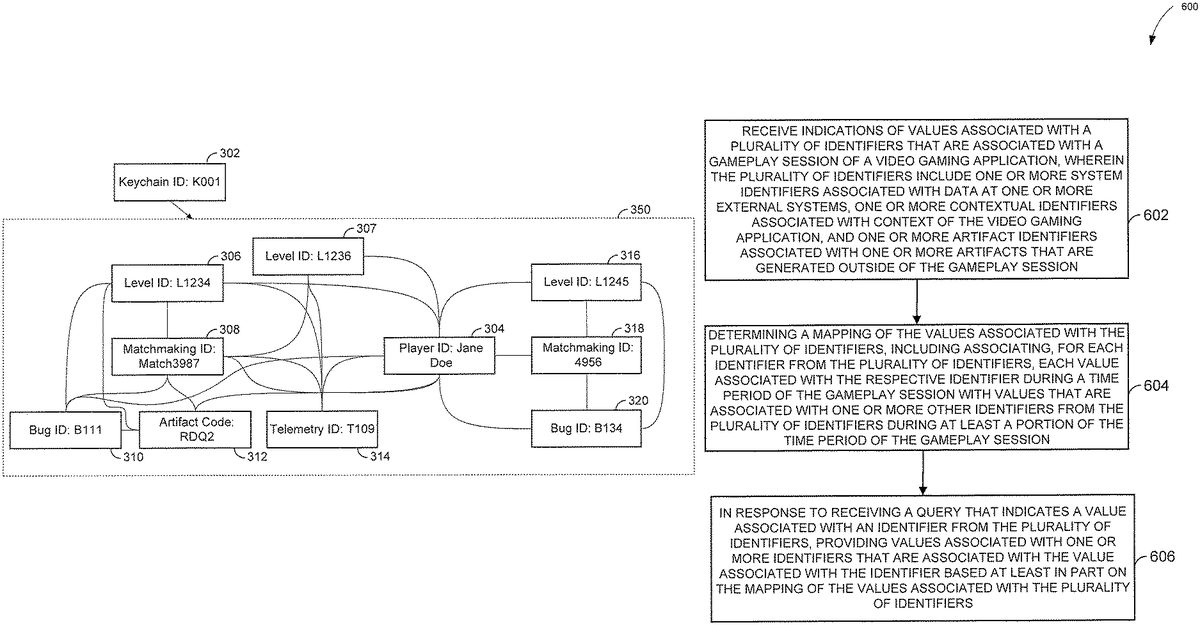
FIG. 3Bis a block diagram illustrating an example graph of associations between values associated with identifiers of an example gaming session, according to certain aspects of the disclosure.FIG. 3Bis an alternative way of illustrating the same associations of associated values of identifiers illustrated in timeline300ofFIG. 3A.
As shown inFIG. 3B, keychain350is a mapping of the values associated with a plurality of identifiers associated with a gaming session, such as gameplay session206, as determined by keychain service132, and keychain350is associated with a keychain identifier value302of “K001”. Keychain identifier value302is connected with each identifier value within keychain350. Within keychain350, an identifier value is illustrated inFIG. 3Bas being connected to another identifier value if and only if they are associated with each other. For example, player identifier value304of “Jane Doe” is only connected to every identifier value within keychain350. Meanwhile, level identifier value306is connected to player identifier value304, matchmaking identifier value308, artifact identifier value312, bug identifier value310, and telemetry identifier value314.
As shown inFIG. 3B, level identifier value307is connected to player identifier value304, matchmaking identifier value308, and telemetry identifier value314. Level identifier value316is connected to player identifier value304, matchmaking identifier value318, and bug identifier value320. Matchmaking identifier value308is connected to player identifier value304, level identifier values306and307, artifact identifier value312, bug identifier310, and telemetry identifier value314. Matchmaking identifier value318is connected to player identifier value304, level identifier value316, and bug identifier value320. Artifact identifier value312is connected to player identifier value304, level identifier value306, matchmaking identifier value308, and bug identifier value310. Bug identifier value310is connected to player identifier value304, level identifier value306, matchmaking identifier value308, and artifact identifier value312. Bug identifier value320is connected to player identifier value304, level identifier value316, and matchmaking identifier value318. Telemetry identifier value314is connected to player identifier value304, level identifier values306and307, and matchmaking identifier value308. As can be seen via visual inspection, a value of an identifier is associated with another value of another identifier if and only if they are connected with each other.
FIG. 4illustrates an example artifact associated with an example gameplay session according to certain aspects of the disclosure. As discussed above, each artifact associated with gameplay session206is associated with an artifact identifier having a value that identifies the associated artifact. As shown inFIG. 4, an example of an artifact associated with gameplay session206may be screenshot400. Screenshot400may be captured via screenshot module256during gameplay session206. A screenshot such as screenshot400may be a frame of video captured at a specific time during gameplay session206that is output by video gaming application112during gameplay session206that is displayed at output device214.
Screenshot400may include visual indication402of a value associated with an artifact identifier (e.g., a screenshot identifier) that is embedded within screenshot400. In some examples, video gaming application112may embed visual indication402of the value associated with the artifact identifier, and may display frames that include the embedded visual indication402of the value associated with the artifact identifier during gameplay session206. In other examples, when screenshot module256captures screenshot400, screenshot module256may modify the captured screenshot to embed visual indication402of the value associated with the artifact identifier in the version of screenshot400that it stores in artifacts storage250.
Because screenshot400captured by screenshot module256and stored in artifacts storage250includes an indication of the value associated with the artifact identifier associated with itself, screenshot400may be used to query keychain service132to determine the values associated with identifiers associated with gameplay session206at the specific time during gameplay session206that screenshot400was captured by screenshot module256.
FIG. 5is a block diagram illustrating an example computing device that may query an example keychain server to receive example identifiers that the example computing device may use to determine additional details of an example gaming server in the example architecture ofFIGS. 1 and 2, according to certain aspects of the disclosure. As shown inFIG. 5, computing device135may send query502that indicates a value associated with an identifier from a plurality of identifiers to keychain service132of keychain server130to query for values associated with one or more identifiers that are associated with the value associated with the identifier indicated by query502.
As discussed above, an identifier is associated with a value at a specific time within gameplay session206or within a period of time within gameplay session206. Thus, the identifier indicated by query502is associated with its associated value as indicated by query502at a specific time within gameplay session206or within a period of time within gameplay session206. In the example ofFIG. 5, query502may include an indication of screenshot400that includes visual indication402of a value associated with an artifact identifier that is embedded within screenshot400.
Screenshot400includes visual indication402of an artifact identifier having an associated value of “RDQ2”. Keychain service132may receive screenshot400and may query keychain storage228for identifiers having associated values that are associated with an artifact identifier having the associated value of “RDQ2”. Keychain service132may determine that a bug identifier having an associated value of “B111”, a matchmaking identifier having an associated value of “3987”, a level identifier having an associated value of “L1234”, a player identifier having an associated value of “Jane Doe”, and a keychain identifier having an associated value of “K0001” may each be associated with the artifact identifier having the associated value of “RDQ2” as indicated by query502. In response, keychain service132may send reply504that includes indications of the associated identifiers and their associated values that are each associated with the artifact identifier having the associated value of “RDQ2” as indicated by query502.
Computing device135may use the identifiers and associated values indicated by query502to query external systems and servers with which video gaming application112communicated during gameplay session206in order to gather additional data about such external systems and servers which may be used to profile or debug video gaming application112. In the example ofFIG. 5, computing device135may send query506that indicates the matchmaking identifier and its associated value of “3987” to gaming server115to request information regarding the online gaming session associated with the matchmaking identifier value of “3987” indicated in query506.
In response to receiving query506, gaming server115may send response508to computing device135that includes additional details of the online gaming session, such as the IP address of the server on which the online gaming session took place, the server load of the server during the online gaming session, the players involved in the online gaming session, and the like. Computing device135may receive response508and may use the details of the online gaming session included in response508to further profile gameplay session206.
The techniques described herein may be implemented as method(s) that are performed by physical computing device(s); as one or more non-transitory computer-readable storage media storing instructions which, when executed by computing device(s), cause performance of the method(s); or, as physical computing device(s) that are specially configured with a combination of hardware and software that causes performance of the method(s).
FIG. 6illustrates an example process600for profiling runtime performance of a video gaming application using the example architecture100ofFIGS. 1-5. WhileFIG. 6is described with reference toFIGS. 1-5, it should be noted that the process steps ofFIG. 6may be performed by other systems.
Process600includes keychain service132receiving indications of values associated with a plurality of identifiers that are associated with a gameplay session206of a video gaming application112, wherein the plurality of identifiers include one or more system identifiers associated with data at one or more external systems, one or more contextual identifiers associated with context of the video gaming application112, and one or more artifact identifiers associated with one or more artifacts that are generated outside of the gameplay session (602).
Process600further includes keychain service132determining a mapping of the values associated with the plurality of identifiers, including associating, for each identifier from the plurality of identifiers, each value associated with the respective identifier during a time period of the gameplay session206with values associated with a respective one or more other identifiers from the plurality of identifiers during at least a portion of the time period of the gameplay session206(604).
Process600further includes in response to keychain service132receiving a query that indicates a value associated with an identifier from the plurality of identifiers, keychain service132providing values associated with one or more identifiers that are associated with the value associated with the identifier based at least in part on the mapping of the values associated with the plurality of identifiers (606).
In some examples, keychain service132associating, for each identifier from the plurality of identifiers, each value associated with the respective identifier during the time period of the gameplay session206with the values associated with a respective one or more other identifiers from the plurality of identifiers during at least the portion of the time period of the gameplay session206may further include keychain service132associating the respective value associated with the respective identifier during the time period of the gameplay session206with two or more different values associated with a same identifier from the plurality of identifiers during at least the portion of the time period of the gameplay session206.
In some examples, process600further includes keychain service132receiving, from a requesting computing device135, an indication of a request to subscribe a second identifier from the plurality of identifiers. Process600may further include in response to keychain service132receiving the indication of the request to subscribe to the second identifier, keychain service132sending updated values of the second identifier to the requesting computing device135as the updated values of the second identifier are received from the video gaming application112.
In some examples, the one or more artifacts that are generated outside of the gameplay session206include a screenshot400of the video gaming application112captured at a specific time during the gameplay session206, and the screenshot400includes a value associated with an artifact identifier embedded within the screenshot400. In some examples, keychain service132receiving the query that indicates the value associated with an identifier from the plurality of identifiers includes keychain service132receiving the screenshot400that includes the value associated with the artifact identifier embedded within the screenshot400.
In some examples, the one or more artifacts that are generated outside of the gameplay session206includes telemetry data of the video gaming application112during the gameplay session206that is generated by a telemetry program, such as telemetry module252, and the telemetry data is associated with a telemetry identifier from the one or more artifact identifiers.
In some examples, the one or more artifacts that are generated outside of the gameplay session206includes a bug report that is generated by a bug tracking application, such as bug tracking module254, and the bug report is associated with a bug identifier from the one or more artifact identifiers.
In some examples, the one or more system identifiers include a matchmaking identifier that is associated with an online gaming session.
In some examples, process600includes keychain service132storing the mapping of the values associated with the plurality of identifiers and the plurality of artifacts in a relational database.
Hardware Overview
FIG. 7is a block diagram illustrating an example computer system700with which gaming device110, keychain server130, and artifacts server140ofFIGS. 1 and 2can be implemented. In certain aspects, the computer system700may be implemented using hardware or a combination of software and hardware, either in a dedicated server, or integrated into another entity, or distributed across multiple entities.
Computer system700(e.g., gaming device110, keychain server130, and/or artifacts server130) includes a bus708or other communication mechanism for communicating information, and a processor702(e.g., processor212,222and/or242) coupled with bus708for processing information. According to one aspect, the computer system700can be a cloud computing server of an IaaS that is able to support PaaS and SaaS services. In one aspect, the computer system700is implemented as one or more special-purpose computing devices. The special-purpose computing device may be hard-wired to perform the disclosed techniques, or may include digital electronic devices such as one or more application-specific integrated circuits (ASICs) or field programmable gate arrays (FPGAs) that are persistently programmed to perform the techniques, or may include one or more general purpose hardware processors programmed to perform the techniques pursuant to program instructions in firmware, memory, other storage, or a combination. Such special-purpose computing devices may also combine custom hard-wired logic, ASICs, or FPGAs with custom programming to accomplish the techniques. The special-purpose computing devices may be desktop computer systems, portable computer systems, handheld devices, networking devices or any other device that incorporates hard-wired and/or program logic to implement the techniques. By way of example, the computer system700may be implemented with one or more processors702. Processor702may be a general-purpose microprocessor, a microcontroller, a Digital Signal Processor (DSP), an ASIC, a FPGA, a Programmable Logic Device (PLD), a controller, a state machine, gated logic, discrete hardware components, or any other suitable entity that can perform calculations or other manipulations of information.
Computer system700can include, in addition to hardware, code that creates an execution environment for the computer program in question, e.g., code that constitutes processor firmware, a protocol stack, a database management system, an operating system, or a combination of one or more of them stored in an included memory704(e.g., memory202, memory226, and/or memory246), such as a Random Access Memory (RAM), a flash memory, a Read Only Memory (ROM), a Programmable Read-Only Memory (PROM), an Erasable PROM (EPROM), registers, a hard disk, a removable disk, a CD-ROM, a DVD, or any other suitable storage device, coupled to bus708for storing information and instructions to be executed by processor702. The processor702and the memory704can be supplemented by, or incorporated in, special purpose logic circuitry. Expansion memory may also be provided and connected to computer system700through input/output module710, which may include, for example, a SIMM (Single In Line Memory Module) card interface. Such expansion memory may provide extra storage space for computer system700, or may also store applications or other information for computer system700. Specifically, expansion memory may include instructions to carry out or supplement the processes described above, and may include secure information also. Thus, for example, expansion memory may be provided as a security module for computer system700, and may be programmed with instructions that permit secure use of computer system700. In addition, secure applications may be provided via the SIMM cards, along with additional information, such as placing identifying information on the SIMM card in a non-hackable manner.
The instructions may be stored in the memory704and implemented in one or more computer program products, e.g., one or more modules of computer program instructions encoded on a computer readable medium for execution by, or to control the operation of, the computer system700, and according to any method well known to those of skill in the art, including, but not limited to, computer languages such as data-oriented languages (e.g., SQL, dBase), system languages (e.g., C, Objective-C, C++, Assembly), architectural languages (e.g., Java, .NET), and application languages (e.g., PHP, Ruby, Perl, Python). Instructions may also be implemented in computer languages such as array languages, aspect-oriented languages, assembly languages, authoring languages, command line interface languages, compiled languages, concurrent languages, curly-bracket languages, dataflow languages, data-structured languages, declarative languages, esoteric languages, extension languages, fourth-generation languages, functional languages, interactive mode languages, interpreted languages, iterative languages, list-based languages, little languages, logic-based languages, machine languages, macro languages, metaprogramming languages, multiparadigm languages, numerical analysis, non-English-based languages, object-oriented class-based languages, object-oriented prototype-based languages, off-side rule languages, procedural languages, reflective languages, rule-based languages, scripting languages, stack-based languages, synchronous languages, syntax handling languages, visual languages, wirth languages, embeddable languages, and xml-based languages. Memory704may also be used for storing temporary variable or other intermediate information during execution of instructions to be executed by processor702.
A computer program as discussed herein does not necessarily correspond to a file in a file system. A program can be stored in a portion of a file that holds other programs or data (e.g., one or more scripts stored in a markup language document), in a single file dedicated to the program in question, or in multiple coordinated files (e.g., files that store one or more modules, subprograms, or portions of code). A computer program can be deployed to be executed on one computer or on multiple computers that are located at one site or distributed across multiple sites and interconnected by a communication network, such as in a cloud-computing environment. The processes and logic flows described in this specification can be performed by one or more programmable processors executing one or more computer programs to perform functions by operating on input data and generating output.
Computer system700further includes a data storage device706such as a magnetic disk or optical disk, coupled to bus708for storing information and instructions. Computer system700may be coupled via input/output module710to various devices. The input/output module710can be any input/output module. Example input/output modules710include data ports such as USB ports. In addition, input/output module710may be provided in communication with processor702, so as to enable near area communication of computer system700with other devices. The input/output module710may provide, for example, for wired communication in some implementations, or for wireless communication in other implementations, and multiple interfaces may also be used. The input/output module710is configured to connect to a communications module712. Example communications modules712(e.g., communication module210,224, and244) include networking interface cards, such as Ethernet cards and modems.
The components of the system can be interconnected by any form or medium of digital data communication, e.g., a communication network. The communication network (e.g., network150) can include, for example, any one or more of a personal area network (PAN), a local area network (LAN), a campus area network (CAN), a metropolitan area network (MAN), a wide area network (WAN), a broadband network (BBN), the Internet, and the like. Further, the communication network can include, but is not limited to, for example, any one or more of the following network topologies, including a bus network, a star network, a ring network, a mesh network, a star-bus network, tree or hierarchical network, or the like. The communications modules can be, for example, modems or Ethernet cards.
For example, in certain aspects, communications module712can provide a two-way data communication coupling to a network link that is connected to a local network. Wireless links and wireless communication may also be implemented. Wireless communication may be provided under various modes or protocols, such as GSM (Global System for Mobile Communications), Short Message Service (SMS), Enhanced Messaging Service (EMS), or Multimedia Messaging Service (MIMS) messaging, CDMA (Code Division Multiple Access), Time division multiple access (TDMA), Personal Digital Cellular (PDC), Wideband CDMA, General Packet Radio Service (GPRS), or LTE (Long-Term Evolution), among others. Such communication may occur, for example, through a radio-frequency transceiver. In addition, short-range communication may occur, such as using a BLUETOOTH, WI-FI, or other such transceiver.
In any such implementation, communications module712sends and receives electrical, electromagnetic or optical signals that carry digital data streams representing various types of information. The network link typically provides data communication through one or more networks to other data devices. For example, the network link of the communications module712may provide a connection through local network to a host computer or to data equipment operated by an Internet Service Provider (ISP). The ISP in turn provides data communication services through the world wide packet data communication network now commonly referred to as the “Internet”. The local network and Internet both use electrical, electromagnetic or optical signals that carry digital data streams. The signals through the various networks and the signals on the network link and through communications module712, which carry the digital data to and from computer system700, are example forms of transmission media.
Computer system700can send messages and receive data, including program code, through the network(s), the network link and communications module712. In the Internet example, a server might transmit a requested code for an application program through Internet, the ISP, the local network and communications module712. The received code may be executed by processor702as it is received, and/or stored in data storage706for later execution.
In certain aspects, the input/output module710is configured to connect to a plurality of devices, such as an input device714(e.g., input device216) and/or an output device716(e.g., output device214). Example input devices714include a keyboard and a pointing device, e.g., a mouse or a trackball, by which a user can provide input to the computer system700. Other kinds of input devices714can be used to provide for interaction with a user as well, such as a tactile input device, visual input device, audio input device, or brain-computer interface device. For example, feedback provided to the user can be any form of sensory feedback, e.g., visual feedback, auditory feedback, or tactile feedback; and input from the user can be received in any form, including acoustic, speech, tactile, or brain wave input. Example output devices716include display devices, such as a LED (light emitting diode), CRT (cathode ray tube), LCD (liquid crystal display) screen, a TFT LCD (Thin-Film-Transistor Liquid Crystal Display) or an OLED (Organic Light Emitting Diode) display, for displaying information to the user. The output device716may comprise appropriate circuitry for driving the output device716to present graphical and other information to a user.
According to one aspect of the present disclosure, gaming device110, keychain server130, and artifacts server140can be implemented using a computer system700in response to processor702executing one or more sequences of one or more instructions contained in memory704. Such instructions may be read into memory704from another machine-readable medium, such as data storage device706. Execution of the sequences of instructions contained in main memory704causes processor702to perform the process steps described herein. One or more processors in a multi-processing arrangement may also be employed to execute the sequences of instructions contained in memory704. Processor702may process the executable instructions and/or data structures by remotely accessing the computer program product, for example by downloading the executable instructions and/or data structures from a remote server through communications module712(e.g., as in a cloud-computing environment). In alternative aspects, hard-wired circuitry may be used in place of or in combination with software instructions to implement various aspects of the present disclosure. Thus, aspects of the present disclosure are not limited to any specific combination of hardware circuitry and software.
Various aspects of the subject matter described in this specification can be implemented in a computing system that includes a back end component, e.g., as a data server, or that includes a middleware component, e.g., an application server, or that includes a front end component, e.g., a client computer having a graphical user interface or a Web browser through which a user can interact with an implementation of the subject matter described in this specification, or any combination of one or more such back end, middleware, or front end components. For example, some aspects of the subject matter described in this specification may be performed on a cloud-computing environment. Accordingly, in certain aspects a user of systems and methods as disclosed herein may perform at least some of the steps by accessing a cloud server through a network connection. Further, data files, circuit diagrams, performance specifications and the like resulting from the disclosure may be stored in a database server in the cloud-computing environment, or may be downloaded to a private storage device from the cloud-computing environment.
Computing system700can include clients and servers. A client and server are generally remote from each other and typically interact through a communication network. The relationship of client and server arises by virtue of computer programs running on the respective computers and having a client-server relationship to each other. Computer system700can be, for example, and without limitation, a desktop computer, laptop computer, or tablet computer. Computer system700can also be embedded in another device, for example, and without limitation, a mobile telephone, a personal digital assistant (PDA), a mobile audio player, a Global Positioning System (GPS) receiver, a video game console, and/or a television set top box.
The term “machine-readable storage medium” or “computer-readable medium” as used herein refers to any medium or media that participates in providing instructions or data to processor702for execution. The term “storage medium” as used herein refers to any non-transitory media that store data and/or instructions that cause a machine to operate in a specific fashion. Such a medium may take many forms, including, but not limited to, non-volatile media, volatile media, and transmission media. Non-volatile media include, for example, optical disks, magnetic disks, or flash memory, such as data storage device706. Volatile media include dynamic memory, such as memory704. Transmission media include coaxial cables, copper wire, and fiber optics, including the wires that comprise bus708. Common forms of machine-readable media include, for example, floppy disk, a flexible disk, hard disk, magnetic tape, any other magnetic medium, a CD-ROM, DVD, any other optical medium, punch cards, paper tape, any other physical medium with patterns of holes, a RAM, a PROM, an EPROM, a FLASH EPROM, any other memory chip or cartridge, or any other medium from which a computer can read. The machine-readable storage medium can be a machine-readable storage device, a machine-readable storage substrate, a memory device, a composition of matter effecting a machine-readable propagated signal, or a combination of one or more of them.
As used in this specification of this application, the terms “computer-readable storage medium” and “computer-readable media” are entirely restricted to tangible, physical objects that store information in a form that is readable by a computer. These terms exclude any wireless signals, wired download signals, and any other ephemeral signals. Storage media is distinct from but may be used in conjunction with transmission media. Transmission media participates in transferring information between storage media. For example, transmission media includes coaxial cables, copper wire and fiber optics, including the wires that comprise bus708. Transmission media can also take the form of acoustic or light waves, such as those generated during radio-wave and infra-red data communications. Furthermore, as used in this specification of this application, the terms “computer”, “server”, “processor”, and “memory” all refer to electronic or other technological devices. These terms exclude people or groups of people. For the purposes of the specification, the terms display or displaying means displaying on an electronic device.
In one aspect, a method may be an operation, an instruction, or a function and vice versa. In one aspect, a clause or a claim may be amended to include some or all of the words (e.g., instructions, operations, functions, or components) recited in other one or more clauses, one or more words, one or more sentences, one or more phrases, one or more paragraphs, and/or one or more claims.
To illustrate the interchangeability of hardware and software, items such as the various illustrative blocks, modules, components, methods, operations, instructions, and algorithms have been described generally in terms of their functionality. Whether such functionality is implemented as hardware, software or a combination of hardware and software depends upon the particular application and design constraints imposed on the overall system. Skilled artisans may implement the described functionality in varying ways for each particular application.
As used herein, the phrase “at least one of” preceding a series of items, with the terms “and” or “or” to separate any of the items, modifies the list as a whole, rather than each member of the list (e.g., each item). The phrase “at least one of” does not require selection of at least one item; rather, the phrase allows a meaning that includes at least one of any one of the items, and/or at least one of any combination of the items, and/or at least one of each of the items. By way of example, the phrases “at least one of A, B, and C” or “at least one of A, B, or C” each refer to only A, only B, or only C; any combination of A, B, and C; and/or at least one of each of A, B, and C.
The word “exemplary” is used herein to mean “serving as an example, instance, or illustration.” Any embodiment described herein as “exemplary” is not necessarily to be construed as preferred or advantageous over other embodiments. Phrases such as an aspect, the aspect, another aspect, some aspects, one or more aspects, an implementation, the implementation, another implementation, some implementations, one or more implementations, an embodiment, the embodiment, another embodiment, some embodiments, one or more embodiments, a configuration, the configuration, another configuration, some configurations, one or more configurations, the subject technology, the disclosure, the present disclosure, other variations thereof and alike are for convenience and do not imply that a disclosure relating to such phrase(s) is essential to the subject technology or that such disclosure applies to all configurations of the subject technology. A disclosure relating to such phrase(s) may apply to all configurations, or one or more configurations. A disclosure relating to such phrase(s) may provide one or more examples. A phrase such as an aspect or some aspects may refer to one or more aspects and vice versa, and this applies similarly to other foregoing phrases.
A reference to an element in the singular is not intended to mean “one and only one” unless specifically stated, but rather “one or more.” Pronouns in the masculine (e.g., his) include the feminine and neuter gender (e.g., her and its) and vice versa. The term “some” refers to one or more. Underlined and/or italicized headings and subheadings are used for convenience only, do not limit the subject technology, and are not referred to in connection with the interpretation of the description of the subject technology. Relational terms such as first and second and the like may be used to distinguish one entity or action from another without necessarily requiring or implying any actual such relationship or order between such entities or actions. All structural and functional equivalents to the elements of the various configurations described throughout this disclosure that are known or later come to be known to those of ordinary skill in the art are expressly incorporated herein by reference and intended to be encompassed by the subject technology. Moreover, nothing disclosed herein is intended to be dedicated to the public regardless of whether such disclosure is explicitly recited in the above description. No claim element is to be construed under the provisions of 35 U.S.C. § 112, sixth paragraph, unless the element is expressly recited using the phrase “means for” or, in the case of a method claim, the element is recited using the phrase “step for”.
While this specification contains many specifics, these should not be construed as limitations on the scope of what may be claimed, but rather as descriptions of particular implementations of the subject matter. Certain features that are described in this specification in the context of separate embodiments can also be implemented in combination in a single embodiment. Conversely, various features that are described in the context of a single embodiment can also be implemented in multiple embodiments separately or in any suitable subcombination. Moreover, although features may be described above as acting in certain combinations and even initially claimed as such, one or more features from a claimed combination can in some cases be excised from the combination, and the claimed combination may be directed to a subcombination or variation of a subcombination.
The subject matter of this specification has been described in terms of particular aspects, but other aspects can be implemented and are within the scope of the following claims. For example, while operations are depicted in the drawings in a particular order, this should not be understood as requiring that such operations be performed in the particular order shown or in sequential order, or that all illustrated operations be performed, to achieve desirable results. The actions recited in the claims can be performed in a different order and still achieve desirable results. As one example, the processes depicted in the accompanying figures do not necessarily require the particular order shown, or sequential order, to achieve desirable results. In certain circumstances, multitasking and parallel processing may be advantageous. Moreover, the separation of various system components in the aspects described above should not be understood as requiring such separation in all aspects, and it should be understood that the described program components and systems can generally be integrated together in a single software product or packaged into multiple software products.
The title, background, brief description of the drawings, abstract, and drawings are hereby incorporated into the disclosure and are provided as illustrative examples of the disclosure, not as restrictive descriptions. It is submitted with the understanding that they will not be used to limit the scope or meaning of the claims. In addition, in the detailed description, it can be seen that the description provides illustrative examples and the various features are grouped together in various implementations for the purpose of streamlining the disclosure. The method of disclosure is not to be interpreted as reflecting an intention that the claimed subject matter requires more features than are expressly recited in each claim. Rather, as the claims reflect, inventive subject matter lies in less than all features of a single disclosed configuration or operation. The claims are hereby incorporated into the detailed description, with each claim standing on its own as a separately claimed subject matter.
The claims are not intended to be limited to the aspects described herein, but are to be accorded the full scope consistent with the language claims and to encompass all legal equivalents. Notwithstanding, none of the claims are intended to embrace subject matter that fails to satisfy the requirements of the applicable patent law, nor should they be interpreted in such a way.
Claims
- A computer-implemented method for profiling runtime performance of a video gaming application, the method comprising: receiving indications of values associated with a plurality of identifiers that are associated with a gameplay session of a video gaming application, wherein the plurality of identifiers include one or more system identifiers associated with data at one or more external systems, one or more contextual identifiers associated with context of the video gaming application, and one or more artifact identifiers associated with one or more artifacts that are generated outside of the gameplay session, the one or more system identifiers comprising at least matchmaking identifiers that identify details of the gameplay session, the matchmaking identifiers received by the video gaming application for establishing the gameplay session, the one or more artifacts that are generated outside of the gameplay session comprising one or more screenshots;in response to capturing screenshots of the video gaming application at a specific time during the gameplay session, associating at least one of the screenshots with a value of an artifact identifier, and embedding the value of the artifact identifier within metadata of the screenshot or visually within the screenshot itself;determining a mapping of the values associated with the plurality of identifiers, including associating, for each identifier from the plurality of identifiers, each value associated with the respective identifier during a time period of the gameplay session with values associated with a respective one or more other identifiers from the plurality of identifiers during at least a portion of the time period of the gameplay session;and in response to receiving a query that indicates a value associated with an identifier from the plurality of identifiers, providing values associated with one or more identifiers that are associated with the value associated with the identifier based at least in part on the mapping of the values associated with the plurality of identifiers.
- The method of claim 1 , wherein associating, for each identifier from the plurality of identifiers, each value associated with the respective identifier during the time period of the gameplay session with the values associated with a respective one or more other identifiers from the plurality of identifiers during at least the portion of the time period of the gameplay session further comprises: associating the respective value associated with the respective identifier during the time period of the gameplay session with two or more different values associated with the same identifier from the plurality of identifiers during at least the portion of the time period of the gameplay session.
- The method of claim 1 , further comprising: receiving, from a requesting computing device, an indication of a request to subscribe a second identifier from the plurality of identifiers;and in response to receiving the indication of the request to subscribe to the second identifier, sending updated values associated with the second identifier to the requesting computing device as the updated values associated with the second identifier are received from the video gaming application.
- The method of claim 1 , wherein receiving the query that indicates the value associated with an identifier from the plurality of identifiers comprises receiving the screenshot that includes the value associated with the artifact identifier embedded within the screenshot.
- The computer-implemented method of claim 1 , wherein: the one or more artifacts that are generated outside of the gameplay session includes telemetry data of the video gaming application during the gameplay session that is generated by a telemetry program;and the telemetry data is associated with a telemetry identifier from the one or more artifact identifiers.
- The computer-implemented method of claim 1 , wherein: the one or more artifacts that are generated outside of the gameplay session includes a bug report that is generated by a bug tracking application;and the bug report is associated with a bug identifier from the one or more artifact identifiers.
- The computer-implemented method of claim 1 , wherein the one or more system identifiers include a matchmaking identifier that is associated with an online gaming session.
- The computer-implemented method of claim 1 , further comprising: storing the mapping of the values associated with the plurality of identifiers in a relational database.
- A system for profiling runtime performance of a video gaming application, the system comprising: a memory storing instructions;and a processor configured to execute the instructions which, when executed, cause the processor to: receive indications of values associated with a plurality of identifiers that are associated with a gameplay session of a video gaming application, wherein the plurality of identifiers include one or more system identifiers associated with data at one or more external systems, one or more contextual identifiers associated with context of the video gaming application, and one or more artifact identifiers associated with one or more artifacts that are generated outside of the gameplay session, the one or more system identifiers comprising at least matchmaking identifiers that identify details of the gameplay session, the matchmaking identifiers received by the video gaming application for establishing the gameplay session, the one or more artifacts that are generated outside of the gameplay session comprising one or more screenshots;in response to capturing screenshots of the video gaming application at a specific time during the gameplay session, associate at least one of the screenshots with a value of an artifact identifier, and embed the value of the artifact identifier within metadata of the screenshot or visually within the screenshot itself;determine a mapping of the values associated with the plurality of identifiers, including associating, for each identifier from the plurality of identifiers, each value associated with the respective identifier during a time period of the gameplay session with values that are associated with a respective one or more other identifiers from the plurality of identifiers during at least a portion of the time period of the gameplay session;store the mapping of the values associated with the plurality of identifiers in the memory;and in response to receiving a query that indicates a value associated with an identifier from the plurality of identifiers, provide values associated with one or more identifiers that are associated with the value associated with the identifier based at least in part on the mapping of the values associated with the plurality of identifiers.
- The system of claim 9 , wherein the instructions which, when executed, cause the processor to associate, for each identifier from the plurality of identifiers, each value associated with the respective identifier during the time period of the gameplay session with the values associated with a respective one or more other identifiers from the plurality of identifiers during at least the portion of the time period of the gameplay session further cause the processor to: associate the respective value associated with the respective identifier during the time period of the gameplay session with two or more different values associated with the same identifier from the plurality of identifiers during at least the portion of the time period of the gameplay session.
- The system of claim 9 , wherein the instructions which, when executed, further cause the processor to: receive, from a requesting computing device, an indication of a request to subscribe a second identifier from the plurality of identifiers;and in response to receiving the indication of the request to subscribe to the second identifier, send updated values associated with the second identifier to the requesting computing device as the updated values associated with the second identifier are received from the video gaming application.
- The system of claim 9 , wherein the instructions which, when executed, cause the processor to receive the query that indicates the value associated with an identifier from the plurality of identifiers further cause the processor to receive the screenshot that includes the value associated with the artifact identifier embedded within the screenshot.
- The system of claim 9 , wherein: the one or more artifacts that are generated outside of the gameplay session includes telemetry data of the video gaming application during the gameplay session that is generated by a telemetry program;and the telemetry data is associated with a telemetry identifier from the one or more artifact identifiers.
- The system of claim 9 , wherein: the one or more artifacts that are generated outside of the gameplay session includes a bug report that is generated by a bug tracking application;and the bug report is associated with a bug identifier from the one or more artifact identifiers.
- The system of claim 9 , wherein the one or more system identifiers include a matchmaking identifier that is associated with an online gaming session.
- The system of claim 9 , wherein the instructions which, when executed, cause the processor to store the mapping of the values associated with the plurality of identifiers in the memory further cause the processor to: store the mapping of the values associated with the plurality of identifiers in a relational database in the memory.
- A non-transitory machine-readable storage medium comprising machine-readable instructions for causing a processor to execute a method for profiling runtime performance of a video gaming application, comprising: receiving indications of values associated with a plurality of identifiers that are associated with a gameplay session of a video gaming application, wherein the plurality of identifiers include one or more system identifiers associated with data at one or more external systems, one or more contextual identifiers associated with context of the video gaming application, and one or more artifact identifiers associated with one or more artifacts that are generated outside of the gameplay session, the one or more system identifiers comprising at least matchmaking identifiers that identify details of the gameplay session, the matchmaking identifiers received by the video gaming application for establishing the gameplay session, the one or more artifacts that are generated outside of the gameplay session comprising one or more screenshots;in response to capturing screenshots of the video gaming application at a specific time during the gameplay session, associating at least one of the screenshots with a value of an artifact identifier, and embedding the value of the artifact identifier within metadata of the screenshot or visually within the screenshot itself;determining a mapping of the values associated with the plurality of identifiers, including associating, for each identifier from the plurality of identifiers, each value associated with the respective identifier during a time period of the gameplay session with values associated with a respective one or more other identifiers from the plurality of identifiers during at least a portion of the time period of the gameplay session;and in response to receiving a query that indicates a value associated with an identifier from the plurality of identifiers, providing values associated with one or more identifiers that are associated with the value associated with the identifier based at least in part on the mapping of the values associated with the plurality of identifiers.
- The non-transitory machine-readable storage medium of claim 17 , wherein associating, for each identifier from the plurality of identifiers, each value associated with the respective identifier during the time period of the gameplay session with the values associated with a respective one or more other identifiers from the plurality of identifiers during at least the portion of the time period of the gameplay session further comprises: associating the respective value associated with the respective identifier during the time period of the gameplay session with two or more different values associated with the same identifier from the plurality of identifiers during at least the portion of the time period of the gameplay session.
Disclaimer: Data collected from the USPTO and may be malformed, incomplete, and/or otherwise inaccurate.