U.S. Pat. No. 10,427,048
SECURE ANTI-CHEAT SYSTEM
AssigneeElectronic Arts Inc
Issue DateJune 26, 2015
Illustrative Figure
Abstract
An anti-cheat system may be accessed over a network and stored directly into volatile memory of a user computing system. In some embodiments, this anti-cheat system may scan, or access portions of, the volatile memory of the user computing system to detect whether cheat software or other unauthorized software that may interact with a game application is detected on the user computing system. The accessed portions of the volatile memory may be compared with one or more signatures that are associated with the execution of cheat software on a computing system. The anti-cheat system may be prevented from being stored within non-volatile memory, thereby preventing malicious users from modifying the anti-cheat system.
Description
DETAILED DESCRIPTION OF EMBODIMENTS Introduction Some video games are single user or single player games. Thus, if a user decides to cheat or use some software that's extraneous to the game to modify the operation of the game as intended by the game's developer, the effect of the cheating will only impact the user and typically, not other users. However, with games that are multiplayer, cheating by one user may impact the enjoyment of playing the games for other users. For example, some players (sometimes referred to as users) utilize software, sometimes termed robots or bots, that can interact with the game on the player's behalf to help, for example, improve the abilities or statistics of the player's in-game character or avatar, or to obtain some in-game resource. Using a robot enables a user to, for example, obtain an increased amount of an in-game resource while the user is sleeping, eating, or working. Further, some users will then sell these “farmed” resources to other users, which can result in an unbalancing of the game. The cheating by some users can cause a loss of sales from disillusioned users. Thus, it is beneficial for a game developer or publisher to prevent or reduce the amount of cheating or other unauthorized interaction with the game. One solution to the above problems is to use a system to monitor the player's computing system to detect the use of unauthorized software that interacts with the game. However, in some cases, a malicious user may access the system that monitors the players computing system and modify it to prevent the monitoring system from performing its intended function. Various embodiments disclosed herein describe an anti-cheat system that is accessed over a network and stored directly into volatile memory of a user computing system. This anti-cheat system ...
DETAILED DESCRIPTION OF EMBODIMENTS
Introduction
Some video games are single user or single player games. Thus, if a user decides to cheat or use some software that's extraneous to the game to modify the operation of the game as intended by the game's developer, the effect of the cheating will only impact the user and typically, not other users. However, with games that are multiplayer, cheating by one user may impact the enjoyment of playing the games for other users. For example, some players (sometimes referred to as users) utilize software, sometimes termed robots or bots, that can interact with the game on the player's behalf to help, for example, improve the abilities or statistics of the player's in-game character or avatar, or to obtain some in-game resource. Using a robot enables a user to, for example, obtain an increased amount of an in-game resource while the user is sleeping, eating, or working. Further, some users will then sell these “farmed” resources to other users, which can result in an unbalancing of the game. The cheating by some users can cause a loss of sales from disillusioned users. Thus, it is beneficial for a game developer or publisher to prevent or reduce the amount of cheating or other unauthorized interaction with the game.
One solution to the above problems is to use a system to monitor the player's computing system to detect the use of unauthorized software that interacts with the game. However, in some cases, a malicious user may access the system that monitors the players computing system and modify it to prevent the monitoring system from performing its intended function.
Various embodiments disclosed herein describe an anti-cheat system that is accessed over a network and stored directly into volatile memory of a user computing system. This anti-cheat system may then scan, or access portions of, the volatile memory of the user computing system to detect whether cheat software or other unauthorized software that may interact with the game is detected on the user computing system. The accessed portions of the volatile memory may be compared with one or more signatures that are associated with the execution of cheat software on a computing system.
Advantageously, in certain embodiments, by storing the anti-cheat system, or a portion thereof, directly into volatile memory, malicious users are prevented from accessing and/or modifying the anti-cheat system. Further, by obtaining the anti-cheat system over a network and storing it into volatile memory when the game is executed, the anti-cheat system can be automatically deleted from the volatile memory when the game is exited or ceases executing. Thus, in certain embodiments, the amount of non-volatile memory used by the game may be reduced, which can in some cases result in a particular non-volatile storage device having room to store more applications. Although the present disclosure is primarily described with respect to game applications, it should be understood that embodiments herein may be implemented with respect to other software applications and is not limited to game applications.
As one illustrative, non-limiting example, of certain embodiments described herein, a gamer Will has been playing a multi-player shooter game on his smartphone, but is not advancing as quickly as he had hoped. Thus, Will decided to load some game cheating software onto his smartphone to assist him with the game. The game cheating software may act as an automated bot and may automatically make selections that will advance or level-up Will's character in the game enabling Will to more easily advance in the game to the next level. However, Will does not know that the shooter game includes an anti-cheat system. Thus, when Will loads the game the next time and attempts to use the game cheating software, the anti-cheat software automatically detects that Will is using game cheating software and sends a signal to a game server that disables or reduces Will's access to the game.
As used herein, the term “developer” may include its plain meaning. Further, the term “developer” may not only refer to a user, group of users, or entity that developed and/or created an application, but may also include other users or entities involved in the maintenance or provisioning of an application. For example, the term “developer” as used herein may include a video game publisher or a video game host entity that provides access to a video game or other application on behalf of, for example, a developer or publisher.
Example Networked Computing Environment
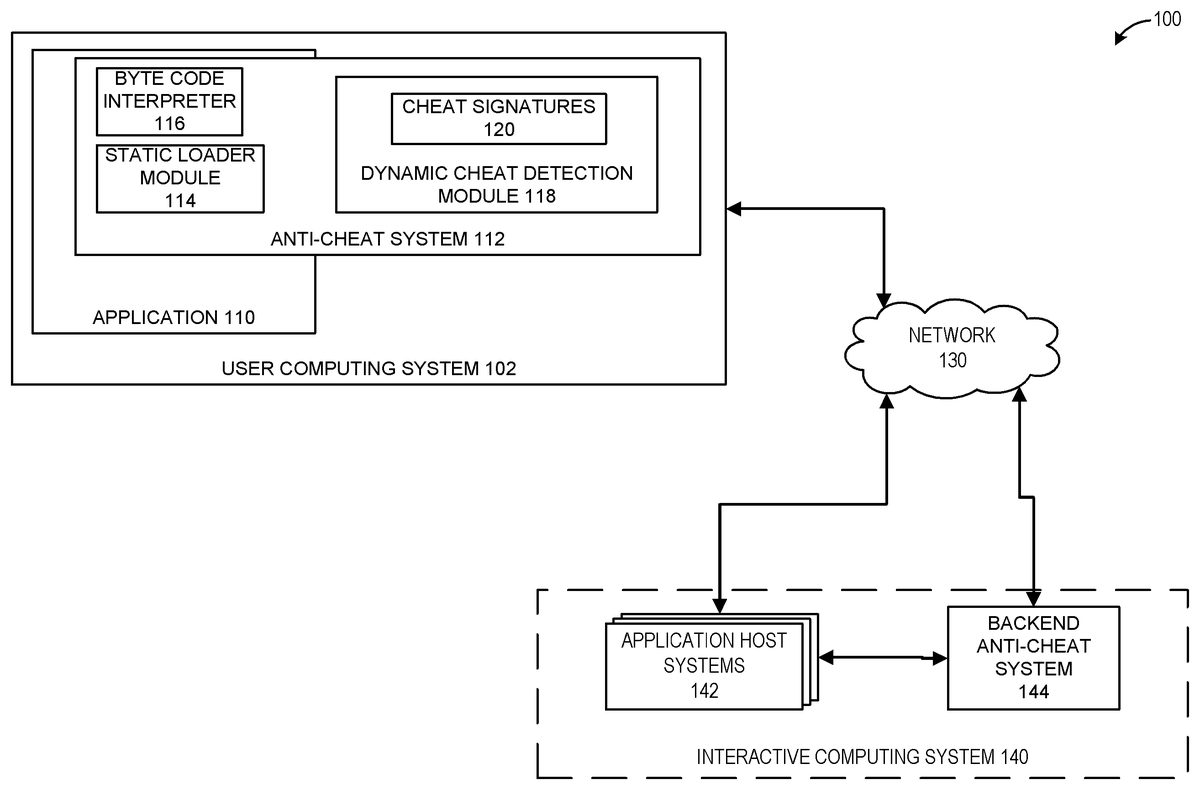
FIG. 1illustrates an embodiment of a networked computing environment100that can implement one or more embodiments of an anti-cheat system112. The networked computing environment100can include one or more user computing systems102and one or more interactive computing systems140. To simplify discussion and not to limit the present disclosure,FIG. 1illustrates only one user computing system102and one interactive computing system140. The user computing system102may communicate via a network130with the interactive computing system140. Although only one network130is illustrated, multiple distinct and/or distributed networks130may exist.
The user computing system102may include hardware and software components for establishing communications over a communication network130. For example, the user systems102may be equipped with networking equipment and network software applications (for example, a web browser) that facilitate communications via a network (for example, the Internet) or an intranet. The user computing system102may have varied local computing resources such as central processing units and architectures, memory, mass storage, graphics processing units, communication network availability and bandwidth, and so forth. Further, the user computing system102may include any type of computing system. For example, the user computing system102may include any type of computing device(s), such as desktops, laptops, video game platforms, television set-top boxes, televisions (for example, Internet TVs), network-enabled kiosks, car-console devices computerized appliances, wearable devices (for example, smart watches and glasses with computing functionality), and wireless mobile devices (for example, smart phones, PDAs, tablets, or the like), to name a few. In some embodiments, the user computing system102may include one or more of the embodiments described below with respect toFIG. 4andFIG. 5.
Typically, the user computing system102is capable of executing an application110, such as a video game, that may be stored and/or executed in a distributed environment. For example, the user computing system102may execute a portion of a game and the interactive computing system140, or an application host system142of the interactive computing system140, may execute another portion of the game. For instance, the game may be a massively multiplayer online role-playing game (MMORPG) that includes a client portion executed by the user computing system102and a server portion executed by one or more application host systems142. For the present discussion, the application110can include a distributed application or an application that includes a portion that executes on the user computing system102and a portion that executes on at least one of the application host systems142.
As stated above, the user computing system102may execute one or more applications, such as the application110. Typically, the application110is a videogame. However, the application110is not limited as such and can include any application where a user's actions with respect to the application may impact another user, such as, for example, an email application, a web browser, a testing application, and so forth. These impermissible actions may generally include cheating or other unauthorized actions. One example of cheating may include performing an action with respect to the application110that is not intended by a developer of the application. Another example of cheating may include using another application or script to perform permissible actions or actions intended by the developer more frequently than intended by the developer, without the use of user interaction to perform the action, or with the use of alternative user actions that differ from the developer intended user actions.
To prevent or reduce cheating, or to prevent or reduce a user from performing actions with respect to the application110that an entity owning or managing the interactive computing system140desires to prevent, the application110may include or utilize the anti-cheat system112. In certain embodiments, the anti-cheat system112may be made up of one or more components. Some of the components of the anti-cheat system112may be included as part of the source code or compiled code of application110that a user may obtain when obtaining access to (for example, purchasing renting, licensing, and so forth) a copy of the application110. Other components of the anti-cheat system112may be separate from the application110or may be obtained separately. For example, some components may be installed with the application110from a game media device or over a network, while other components may be obtained in response to executing the application110. To illustrate the idea that the anti-cheat system112may include portions that may be part of the application110and portions that may be separate from the application110, the box representing the anti-cheat system112is illustrated inFIG. 1as being partially within the application110and partially external to the application110.
The illustrated embodiment of the anti-cheat system112includes a static loader module114, a byte code interpreter116, and a dynamic cheat detection module118. The static loader module114may include code that can be executed as part of the application110that is capable of initiating a communication channel with an application host system142and/or a backend anti-cheat system144. Further, static loader module114is capable of obtaining executable code from one or more of the application host system142, the backend anti-cheat system144, or another system. In certain embodiments, the executable code obtained by the static loader module114is the dynamic cheat detection module118. Further, in certain embodiments, the application host system142can implement one or more features of the backend anti-cheat system144. Thus, in certain embodiments, the backend anti-cheat system144may be omitted or optional. Moreover, in some such cases, communication channels established between the static loader module114, the dynamic cheat detection module118, or the anti-cheat system112may be established with the application host system142instead of or in addition to the backend anti-cheat system144.
The static loader module114, in some implementations, may load the dynamic cheat detection module118into volatile memory, such as a Random Access Memory (RAM) (not shown) of the user computing system102. In some embodiments, the static loader module114loads the dynamic cheat detection module118directly into the volatile memory without storing the dynamic cheat detection module118in nonvolatile memory. Advantageously, in certain embodiments, loading the dynamic cheat detection module118directly into volatile memory prevents malicious users from accessing the code of the dynamic cheat detection module118, thereby preventing the malicious users from reverse engineering the dynamic cheat detection module118or otherwise tampering with the dynamic cheat detection module118.
In some implementations, the static loader module114may be or may include a version of a dynamic library loader. In some cases, the dynamic library loader included with the static loader module114may serve as a replacement for a dynamic library loader included in an operating system executed by the user computing system102, such as the dynamic-link library (DLL) loader included in some Microsoft® operating systems.
In some embodiments, the dynamic cheat detection module118may be received from the interactive computing system140as byte code. In such cases, the byte code interpreter116may be used to execute the dynamic cheat detection module118. In some cases, such as when the dynamic cheat detection module118is executable code, the byte code interpreter116may be optional or omitted.
The dynamic cheat detection module118may include executable code that is capable of scanning volatile memory to detect the presence of code or software used to cheat or otherwise perform restricted actions with respect to the application110. Further, the dynamic cheat detection module118is capable of creating a hash or other representation of a portion of the volatile memory and comparing the hash or other representation to a cheat signature, which may be included in the cheat signatures120to determine whether the user is using software to cheat. The cheat signatures120or a representation of the cheat signatures120may be downloaded or otherwise obtained by the dynamic cheat detection module118from the backend anti-cheat system144, or another system. In some cases, the dynamic cheat detection module118may obtain the cheat signatures120(sometimes referred to as the cheat signatures payload) using a communication channel established by the static loader module114. The communication channel may be a secure or encrypted communication channel thereby preventing a malicious user from accessing the cheat signatures payload during or after transmission between the interactive computing system140and the user computing system102.
The interactive computing system140may include one or more computing systems configured to execute a portion of the application110. Further, the interactive computing system140may enable multiple users or computing systems to access the portion of the application110executed or hosted by the interactive computing system140. In some embodiments, the portion of the application110executed by a computing system of the interactive computing system140may create a persistent virtual world. This persistent virtual world may enable one or more users to interact with the virtual world and with each other in a synchronous and/or asynchronous manner. In some cases, multiple instances of the persistent virtual world may be created or hosted by the interactive computing system140. A set of users may be assigned to or may access one instance of the persistent virtual world while another set of users may be assigned to or may access another instance of the persistent virtual world.
As illustrated inFIG. 1, the interactive computing system140may include one or more application host systems142and a backend anti-cheat system144. The one or more application host systems142can include one or more computing devices, such as servers and databases that may host and/or execute a portion of one or more instances of the application110. In certain embodiments, instead of or in addition to executing a portion of the application110, the application host systems142execute another application, which may complement and/or interact with the application110during execution of an instance of the application110.
Further, the backend anti-cheat system144can include systems that can provide to the anti-cheat system112an instance of the dynamic cheat detection module118and/or the cheat signatures payload120. Further, the backend anti-cheat system144may be capable of reviewing and/or regulating a user's access to the application110based, at least in part, on the result of a cheat detection process performed by the dynamic cheat detection module118. In some cases, the backend anti-cheat system144regulates the user's access to the application110by preventing an instance of the application110on the user computing system102from interacting with the application host systems142and/or an application executing or hosted by the application host systems142. As previously described, the application executing or hosted by the application host system142may be a portion of the application110and/or a complementary application configured to interact with the application110.
The network130can include any type of communication network. For example, the network130can include one or more of a wide area network (WAN), a local area network (LAN), a cellular network, an ad hoc network, a satellite network, a wired network, a wireless network, and so forth. Further, in some cases, the network130can include the Internet.
Example Anti-Cheat Initiation Process
FIG. 2presents a flowchart of an embodiment of an anti-cheat initiation process200. The process200can be implemented by any system that can load and/or initiate a system for detecting cheating with respect to interaction, user or otherwise, with an application on a computing system. For example, the process200, in whole or in part, can be implemented by an anti-cheat system112, a static loader module114, or a dynamic cheat detection module118, among others. Although any number of systems, in whole or in part, can implement the process200, to simplify discussion, the process200will be described with respect to particular systems.
The process200begins at block202where, for example, the user computing system102initiates execution of the application110. The application110may be executed in response to an action by the user with respect to the user computing system102. For example, the user may select an icon associated with the application110to instruct the user computing system102to execute or initiate execution of the application110. In some cases, the application110may automatically execute. For example, the user computing system102may be configured to execute the application110after startup of the user computing system102or after insertion of a non-transitory computer readable media (for example, a CD, DVD, or USB memory device) into the user computing system102.
At block204, the user computing system102executes the static loader module114included in the application110. The static loader module114may be executed as part of the execution of an anti-cheat system112, or a part thereof. Executing the static loader module114may include executing program code or software included with the application110that corresponds to the static loader module114. In some implementations, the block204may be performed as part of the initial application execution process performed at the block202.
At block206, the static loader module114establishes a network connection to an application host system142. Alternatively, or in addition, the static loader module114may establish a network connection with the backend anti-cheat system144. In some implementations, a separate network connection may be established between the application110and one of the application host systems142. In some implementations, it can be advantageous for the backend anti-cheat system144to communicate indirectly with the anti-cheat system112via the application host systems142. In such an implementation, the backend anti-cheat system144would not be exposed to the user computing system102, and would help prevent potential cheaters and cheat-makers from analyzing and/or manipulating communication between the user computing system102and the backend anti-cheat system144. Alternatively, the static loader module114and other components of the application110may share one or more network connections with the application host system142. In some implementations, the connection between the static loader module114and the backend anti-cheat system144is a secure connection. This secure connection may use one or more types of encryption processes including, for example, symmetric encryption, asymmetric encryption, pretty good privacy (PGP) encryption, RSA encryption, Data Encryption Standard (DES) based encryption, and so forth.
The static loader module114, at block208, loads the dynamic cheat detection module118obtained from the application host system142into volatile memory, such as RAM, cache memory, or any other type of memory that does not maintain the storage of data when the user computing system102is turned off or otherwise loses power. Typically, the dynamic cheat detection module118is loaded into a portion of the volatile memory that cannot be accessed or otherwise addressed by a user or application other than the application110or the anti-cheat system112of the application110. Advantageously, in certain embodiments, by loading the dynamic cheat detection module118directly into volatile memory, a copy of the dynamic cheat detection module118is not stored or accessible from a non-volatile memory on the user computing system102, such as a hard disk drive or a solid state drive of the user computing system102. Thus, a user is prevented from accessing a copy of the dynamic cheat detection module118and reverse engineering or otherwise interacting with the dynamic cheat detection module118in a manner the developer of the dynamic cheat detection module118does not desire.
Loading the dynamic cheat detection module118into volatile memory may include downloading an instance, or otherwise obtaining the instance from the application host system142via the network130, of the dynamic cheat detection module118from the application host system142. Thus, althoughFIG. 1illustrates the dynamic cheat detection module118as part of the anti-cheat system112on the user computing system102, in some cases, the dynamic cheat detection module118is not initially included as part of the anti-cheat system112that may initially be installed with the application110. Instead, the dynamic cheat detection module118may be loaded from the interactive computing system140. After it is downloaded, the dynamic cheat detection module118may be linked with or may become part of the anti-cheat detection system112. Alternatively, or in addition, the dynamic cheat detection module118may complement or function in cooperation with the anti-cheat detection system112.
At block210, the static loader module114executes the dynamic cheat detection module118within the volatile memory. Although the dynamic cheat detection module118is typically only stored and executed within volatile memory, in certain embodiments, at least a portion of the dynamic cheat detection module118may be stored in a protected portion of non-volatile memory, such as virtual memory. This may occur, for example, when RAM for the user computing system102exceeds a utilization rate and the user computing system102uses a portion of the non-volatile memory as virtual memory to supplement the available RAM. In certain embodiments, the dynamic cheat detection module118is prevented from being stored in non-volatile memory regardless of whether the user computing system102utilizes virtual memory. Thus, in some cases, pages of data within the RAM that include a portion of the dynamic cheat detection module118are prevented from being copied to portions of the non-volatile memory being utilized as virtual memory. In certain embodiments, executing the dynamic cheat detection module118may include using the byte code interpreter116to interpret or execute code associated with the dynamic cheat detection module118.
At block212, the dynamic cheat detection module118communicates with the backend anti-cheat system144via the network connection to the application host systems142. In some embodiments, the dynamic cheat detection module118establishes a separate network connection to the backend anti-cheat system144. Alternatively, the dynamic cheat detection module118may utilize a connection established by the static loader module114with the backend anti-cheat system144. In other words, in some cases, the dynamic cheat detection module118may communicate with the backend anti-cheat system144using a network connection established by the static loader module114. In either case, the connection may be a secure connection and may use encryption to help secure the connection.
At block214, the dynamic cheat detection module118loads the cheat signatures payload (for example, the cheat signatures120) from the backend anti-cheat system144into volatile memory. In some embodiments, the cheat signature payload can be loaded as part of the dynamic cheat detection module118. In some such embodiments, the cheat signature payload could be downloaded into volatile memory as part of the dynamic cheat detection module118. In some embodiments, the cheat signatures payload is provided by the backend anti-cheat system144to the application host systems142. In some such embodiments, the dynamic cheat detection module118may load the cheat signatures payload from the application host system142. As previously described with respect to the dynamic cheat detection module118, in some embodiments, the cheat signatures120may in some cases be stored at least temporarily in a portion of non-volatile memory, such as a portion of non-volatile memory that is allocated as virtual memory to complement the RAM. However, in other embodiments, the cheat signatures120are prevented from being stored, even temporarily, in the non-volatile memory. Thus, in some cases, pages of data within the RAM that include a portion of the cheat signatures120are prevented from being copied to portions of the non-volatile memory being utilized as virtual memory. Further, in some cases, the portion of the volatile memory that includes the cheat signatures120is protected from access by applications or processes not associated with the dynamic cheat detection module118. Advantageously, in certain embodiments, by limiting access to the cheat signatures120and/or preventing processes or applications not associated with the dynamic cheat detection module118from accessing the cheat signatures120, malicious users are prevented from modifying the cheat signatures120.
In certain embodiments, one or more of the dynamic cheat detection module118and the cheat signatures payload120may be selected based on one or more selection rules. The selection rules may include determining a geographic location of the user computing system102, demographics associated with a user using the user computing system102, a selected service level, or any other information that can be used to determine a version of a dynamic cheat detection module118and/or a version of the cheat signatures payload120to provide to the user computing system102. Advantageously, in certain embodiments, an entity can test different versions of the dynamic cheat detection module118and/or different versions of the cheat signatures payload120by providing different versions of the dynamic cheat detection module118and/or the cheat signatures payload120to different users. For example, users in one country may receive a particular cheat signatures payload120, but users in another country may receive another cheat signatures payload120. In some cases, the different dynamic cheat detection module118and/or cheat signatures120may be selected based on differences in the language packs utilized by the application110and/or an operating system on the user computing system102. Further, in some cases, the different dynamic cheat detection module118and/or cheat signatures120may be selected based on information about the user, such as the user's age, location, past history of cheating, and so forth.
After the dynamic cheat detection module118and the cheat signatures payload120has been obtained, an anti-cheat detection process may be implemented by the dynamic cheat detection module118. A number of processes for detecting cheats are possible within the context of the present disclosure. One such non-limiting example process is described below with respect toFIG. 3.
Example Cheat Detection Process
FIG. 3presents a flowchart of an embodiment of a cheat detection process300. The process300can be implemented by any system that can detect whether a user is attempting to cheat with respect to using an application (for example, playing a videogame) by, for example, using software that is not included as part of the application by the developer of the application. For example, the process300, in whole or in part, can be implemented by an anti-cheat system112, a static loader module114, or a dynamic cheat detection module118, among others. Although any number of systems, in whole or in part, can implement the process300, to simplify discussion, the process300will be described with respect to particular systems.
Although the process300is primarily described with respect to a user attempting to cheat at a videogame, the process is not limited as such. In some embodiments, the process300may be used to detect user actions and/or automated actions (such as from or by a bot) that are beyond or outside the scope of interactions intended by the developer of the application110. For instance, the process300may be used to detect an attempt to circumvent or cheat with respect to a test or exam application designed to test students.
As another example, the process300may be used to detect an attempt to cheat at a contest or to circumvent marketing. For instance, one contest or marketing scheme may involve voting for particular contestants or contest entries via a website or other computer-based voting mechanism. The contest organizers may desire to limit how frequently a particular user can vote. The process300may be used to reduce or prevent cheating by using an anti-cheat system112to identify cheat software that enables a user to circumvent voting limits. In some embodiments, the process300, or a modified form thereof, may be used to detect cheating with respect to one or more types of processes or interactions that involve communication between computing systems, such as with respect to client/server interaction, without limit to the type of interaction or process. In other words, in certain embodiments, the process300may be used to detect unauthorized interactions by automated software between computing systems.
The process300begins at block302where, for example, the dynamic cheat detection module118intermittently sends a heartbeat signal to the backend anti-cheat system144via the application host system142. For example, the heartbeat signal can be provided to the backend anti-cheat system144by the application host system142. In some implementations, the dynamic cheat detection module118may send the signal directly to the backend anti-cheat system144. Although intermittent, in some cases, the heartbeat signal is sent on a particular schedule. For example, the heartbeat signal may be sent every second, every minute, every five minutes, at a random time within an interval, and so forth. Alternatively, the heartbeat signal may be sent on a continuous basis or with each packet of data communicated between the application110and a portion of the application hosted by the application host system142. This heartbeat signal may include any type of signal or message that informs the backend anti-cheat system144that the dynamic cheat detection module118is operating. Advantageously, in certain embodiments, the backend anti-cheat system144can use the heartbeat signal to confirm that a malicious user has not performed an action to cause the dynamic cheat detection module118to stop operating. In certain embodiments, the block302may be optional or omitted.
At block304, the dynamic cheat detection module118accesses a portion of the volatile memory, such as RAM. As previously described, the dynamic cheat detection module118is typically stored in the volatile memory. Further, when the dynamic cheat detection module118is executing, it may be associated with a particular portion of the volatile memory that is allocated for use by the dynamic cheat detection module118. In such cases, the dynamic cheat detection module118is not limited to accessing a portion of the volatile memory allocated for its use, but may access other portions of the volatile memory in an attempt to determine whether code associated with cheating is being utilized or executed by the user computing system102.
At block306, the dynamic cheat detection module118generates a hash value of the contents of the portion of the volatile memory accessed at the block304. Alternatively, or in addition, the block306may include generating an alternative abstraction or other piece of data that corresponds to the portion of the volatile memory accessed at the block304.
The dynamic cheat detection module118, at block308, compares the hash value to one or more signatures included in the cheat signatures payload120. In some embodiments, the hash may serve as an index value for accessing a particular location within a data structure or database that includes the cheat signatures120. Using the hash to access the data structure may result in obtaining a value or other data associated with the hash value, which may then be used to help determine whether a user is cheating. In some such cases, the lack of a value in the data structure associated with the hash may be used to help determine whether a user is cheating.
At decision block310, the dynamic cheat detection module118determines whether the hash matches a signature included in the cheat signatures payload120based at least in part on the comparison performed at the block308. In some cases, the decision block310may include determining whether the hash is a valid index to the cheat signatures payload120. In other words, the decision block310may include determining whether the hash can be used as a key to access a value from a data structure corresponding to the cheat signatures payload120. In some such cases, if the hash cannot be used to access a value, the decision block310determines that there is no match to a signature included in the cheat signatures payload120. In contrast, if the hash can be used to access a value in the cheat signatures payload120, then the decision block310determines that there is a match to a signature in the cheat signatures payload120. In some cases, the hash may be referred to as a hash key. In certain embodiments, the cheat signatures payload120does not store signatures, but instead may have in identifier, such as an identification code, associated with different cheat signatures. This identification code may serve as the value in the cheat signatures payload120that may be accessed using the hash as the key.
If it is determined at the decision block310that the hash value does not match a signature included in the cheat signatures payload120, the dynamic cheat detection module118accesses a another portion of the volatile memory at block312. This additional portion of the volatile memory may be a subsequent portion of the volatile memory to the portion accessed at the block304. However, the block312is not limited as such and the additional portion of volatile memory may be accessed from any portion of the volatile memory and/or based on a selection algorithm. Subsequent to block312, the process300may return to block306where a hash of the volatile memory accessed at block312is created. In certain embodiments the process300may repeat until a cheat is detected or the application110ceases executing either in response to a user action or otherwise.
If it is determined at decision block310that the hash does match a signature included in the cheat signatures payload120, the dynamic cheat detection module118provides a cheat identification code associated with the signature to the backend anti-cheat system144at block314. As described above, the cheat identification code may be obtained by accessing a value from a cheat signatures payload120using the hash as an index or key to a data structure of the cheat signatures payload120. In some cases, the value may be associated with the cheat identification code or may itself be the cheat identification code. Further, in some cases, the cheat identification code is a distinct code associated with a type of cheat. Alternatively, or in addition, the cheat identification code may include the hash value and/or signature associated with the identified cheat.
In certain embodiments, the backend anti-cheat system144may take one or more actions or perform one or more operations based on the cheat identification code received in response to performance of block314. For example, the backend anti-cheat system144may request that the application host system142prevent the user computing system102and/or a user associated with the user computing system102from continuing to access the application host system142. In some cases, this may effectively prevent the user from using or playing the application110. As another example, the backend anti-cheat system144may identify or include the user in a list of potential cheaters and may provide a warning to the user. In some cases, the backend anti-cheat system144may take no action in response to receiving the identification of a cheat identification code. For example, in some cases, an entity associated with the interactive computing system140may be testing a new signature to determine if it is narrow enough to distinguish a particular cheat software from a signature associated with legitimate software or software that is not used for cheating, such as a word processor. In some such cases, the backend anti-cheat system144may monitor the number of users identified as potentially cheating based on the new signature. An administrator may then use the collected information to determine whether the new signature is likely narrow enough to identify cheaters without identifying non-cheaters or while only identifying less than a threshold number of non-cheaters.
In some cases, after block314completes executing, the process300may end. In other cases, at least a portion of the process300may continue executing. For example, in cases where the cheat identification code is not associated with an action that triggers preventing the user from continuing to play the application110, the process300may proceed to the block312. For instance, the cheat identification may be associated with a warning or may be collected for tracking purposes. Further, in some embodiments, a multi-strike policy may be enacted by a developer of the application110. Thus, in some such cases, a particular cheat identification code may trigger a warning the first time the cheat is detected, but may prevent a user from continuing to execute or play the application110a second time the cheat is detected. The multi-strike policy may be based on a particular cheat or on a set of cheats. Thus, the first strike may occur when a first cheat identification code is identified and the second strike may occur when a second cheat identification code that differs from the first cheat identification code is detected. In some embodiments, the cheat identification code may undergo further processing using heuristic detection algorithms to determine whether the user is cheating. For example, the cheat identification code may indicate that there is a possibility that a user may be cheating. The heuristic detection algorithms can be used to further analyze the cheat identification code in conjunction with other cheat identification codes, other information associated with the user computing device102, and/or other computing devices to determine whether the user is cheating.
Generally, upon completion of the process300, such as when a user exits the application110, anything stored within the volatile memory related to the application110may be deleted, flushed from the volatile memory and/or non-volatile virtual memory, and/or overwritten by other applications. In some user computing systems, the volatile memory related to the application110may not be flushed or emptied when the application110exists. For example, a user computing system may be configured to allocate the volatile memory used by the application110for use by other applications enabling the contents of the volatile memory associated with the application110to eventually be overwritten, but may not immediately empty the memory upon the application110ceasing to execute. In some such cases, the anti-cheat system112may cause the volatile memory to be flushed or emptied as part of the shutdown process of the application110, thereby preventing a user from accessing memory associated with the anti-cheat system112or individual components thereof, upon the application110ceasing to execute. In some such cases, at least the portion of the volatile memory that stores the cheat signatures120, the dynamic cheat detection module118, and/or the anti-cheat system112is emptied, overwritten, or flushed before the portion of the volatile memory is returned to an available memory pool. The available memory pool may include available memory from which the operating system, or other memory arbitrator, of the user computing system102allocates or assigns memory, such as RAM, for use by one or more applications. In some implementations, volatile memory assigned for use by a particular application cannot be accessed by other applications until the volatile memory is relinquished or returned to the available memory pool.
In some embodiments, a copy of a portion of the volatile memory is saved or provided to the interactive computing system140. This saved portion of the volatile memory may be stored as proof or evidence of cheating by a user. Alternatively, or in addition, the saved portion of the volatile memory may be saved for further analysis by, for example, the backend anti-cheat system144to confirm whether cheating occurred and/or to detect the type of software used to cheat and/or the type of cheating that occurred.
Advantageously, in certain embodiments, as the dynamic cheat detection module118may only exist in volatile memory, the dynamic cheat detection module118is removed from the user computing system102upon exit of the application110. Thus, a malicious user may be prevented from accessing or modifying the dynamic cheat detection module118as it is not stored, or permanently stored, within the non-volatile memory of the user computing system102. Further, in some embodiments, the cheat signatures payload120is removed from the volatile memory of user computing system102when the application110ceases to execute. Moreover, as the cheat signatures payload120is only loaded into the volatile memory, in some embodiments, the cheat signatures payload120is deleted from the user computing system102upon the application110ceasing to execute.
Overview of Game System
FIG. 4illustrates an embodiment of a computing device100, also referred to as a gaming system. The computing device400can be an embodiment of the user computing system102described above. In the example ofFIG. 4, the computing device400is a touch-capable computing device capable of receiving input from a user via a touchscreen display402. However, the computing device400is not limited as such and may include non-touch capable embodiments, which do not include a touchscreen display402.
The computing device400includes a touchscreen display402and a touchscreen interface404, and is configured to execute a game application410. In certain embodiments, the game application410may be the application110and may include some or all of the embodiments described with respect to the application110including, for example, the anti-cheat system112. Although described as a game application410, in some embodiments the application410may be another type of application, such as exam software, a gambling application, or a financial application.
The computing device400can include one or more processors, such as central processing units (CPUs), graphics processing units (GPUs), and accelerated processing units (APUs). Further, the computing device400may include one or more data storage elements. In some embodiments, the computing device400can be a specialized computing device created for the purpose of executing game applications410. For example, the computing device400may be a video game console. The game applications410executed by the computing device400may be created using a particular application programming interface (API) or compiled into a particular instruction set that may be specific to the computing device400. In some embodiments, the computing device400may be a general purpose computing device capable of executing game applications410and non-game applications. For example, the computing device400may be a laptop with an integrated touchscreen display or desktop computer with an external touchscreen display. Components of an example embodiment of a computing device400are described in more detail with respect toFIG. 5.
The touchscreen display402can be capacitive touchscreen, a resistive touchscreen, surface acoustic wave touchscreen, or other type of touchscreen technology that is configured to receive tactile inputs, also referred to as touch inputs, from a user. For example, the touch inputs can be received via a finger touching the screen, multiple fingers touching the screen, a stylus, or other stimuli that can be used to register a touch input on the touchscreen display402. The touchscreen interface404can be configured to translate the touch input into data and output the data such that it can be interpreted by components of the computing device400, such as an operating system and the application410. The touchscreen interface404can translate characteristics of the tactile touch input touch into touch input data. Some example characteristics of a touch input can include, shape, size, pressure, location, direction, momentum, duration, and/or other characteristics. The touchscreen interface404can be configured to determine the type of touch input, such as, for example a tap (for example, touch and release at a single location) or a swipe (for example, movement through a plurality of locations on touchscreen in a single touch input). The touchscreen interface404can be configured to detect and output touch input data associated with multiple touch inputs simultaneously, or substantially in parallel. In some cases, the simultaneous touch inputs may include instances where a user maintains a first touch on the touchscreen display402while subsequently performing a second touch on the touchscreen display402. The touchscreen interface404can be configured to detect movement of the touch inputs. The touch input data can be transmitted to components of the computing device400for processing. For example, the touch input data can be transmitted directly to the application410for processing.
In some embodiments, the touch input data can undergo processing and/or filtering by the touchscreen interface404, an operating system, or other components prior to being output to the game application410. As one example, raw touch input data can be captured from a touch input. The raw data can be filtered to remove background noise, pressure values associated with the input can be measured, and location coordinates associated with the touch input can be calculated. The type of touch input data provided to the game application410can be dependent upon the specific implementation of the touchscreen interface404and the particular API associated with the touchscreen interface404. In some embodiments, the touch input data can include location coordinates of the touch input. The touch signal data can be output at a defined frequency. Processing the touch inputs can be computed many times per second and the touch input data can be output to the game application for further processing.
A game application410can be configured to be executed on the computing device400. The game application410may also be referred to as a videogame, a game, game code and/or a game program. A game application should be understood to include software code that a computing device400can use to provide a game for a user to play. A game application410might comprise software code that informs a computing device400of processor instructions to execute, but might also include data used in the playing of the game, such as data relating to constants, images and other data structures. For example, in the illustrated embodiment, the game application includes a game engine412, game data414, and game state information416.
Further, the game application410can include an embodiments of the anti-cheat system112described above. As described with respect toFIG. 1, the anti-cheat system112may include components that are part of the game application410, or are included with the game application410, as well as additional components that are obtained during execution of the game application410from another computing system. Thus, to illustrate the point that, in some embodiments, the anti-cheat system112may include components integrated with the game application410as well as additional separate components the game application410is illustrated as extending outside of the box representing the game application410.
The touchscreen interface404or another component of the computing device100, such as the operating system, can provide user input, such as touch inputs, to the game application. In some embodiments, the computing device400may include alternative or additional user input devices, such as a mouse, a keyboard, a camera, a game controller, and the like. A user can interact with the game application410via the touchscreen interface404and/or one or more of the alternative or additional user input devices. The game engine412can be configured to execute aspects of the operation of the game application410within the computing device400. Execution of aspects of gameplay within a game application can be based, at least in part, on the user input received, the game data414, and a game state information416. The game data414can include game rules, prerecorded motion capture poses/paths, environmental settings, constraints, skeleton models, and/or other game application information. The game engine412can execute gameplay within the game according to the game rules. Some examples of game rules can include rules for scoring, possible inputs, actions/events, movement in response to inputs, and the like. Other components can control what inputs are accepted and how the game progresses, and other aspects of gameplay. During execution of the game application410, the game application410can store game state information416, which can include character states, environment states, scene object storage, and/or other information associated with a state of execution of the game application410. For example, the game state information116can identify the state of the game application at a specific point in time, such as a character position, character action, game level attributes, and other information contributing to a state of the game application.
The game engine412can receive the user inputs and determine in-game events, such as actions, collisions, runs, throws, attacks and other events appropriate for the game application410. During operation, the game engine412can read in game data414and a game state information416in order to determine the appropriate in-game events. In one example, after the game engine412determines the character events, the character events can be conveyed to a movement engine that can determine the appropriate motions the characters should make in response to the events and passes those motions on to a physics engine. The physics engine can determine new poses for the characters and provide the new poses to a skinning and rendering engine. The skinning and rendering engine, in turn, can provide character images to an object combiner in order to combine animate, inanimate, and background objects into a full scene. The full scene can conveyed to a renderer, which can generate a new frame for display to the user. The process can be repeated for rendering each frame during execution of the game application. Though the process has been described in the context of a character, the process can be applied to any process for processing events and rendering the output for display to a user.
Overview of Computing Device
FIG. 5illustrates additional details of an embodiment of the computing device400ofFIG. 4according to the present disclosure. Other variations of the computing device400may be substituted for the examples explicitly presented herein, such as removing or adding components to the computing device400. The computing device400may include a game device, a smart phone, a tablet, a personal computer, a laptop, a smart television, a car console display, and the like. Further, (although not explicitly illustrated inFIG. 5) as described with respect toFIG. 4, the computing device400may optionally include a touchscreen display402and a touchscreen interface404.
As shown, the computing device400includes a processing unit20that interacts with other components of the computing device400and also external components to the computing device100. A game media reader22may be included that can communicate with game media12. Game media reader22may be an optical disc reader capable of reading optical discs, such as CD-ROM or DVDs, or any other type of reader that can receive and read data from game media12. In some embodiments, the game media reader22may be optional or omitted. For example, game content or applications may be accessed over a network via the network I/O38rendering the game media reader22and/or the game media12optional.
The computing device400may include a separate graphics processor24. In some cases, the graphics processor24may be built into the processing unit20, such as with an APU. In some such cases, the graphics processor24may share Random Access Memory (RAM) with the processing unit20. Alternatively, or in addition, the computing device400may include a discrete graphics processor24that is separate from the processing unit20. In some such cases, the graphics processor24may have separate RAM from the processing unit20. Further, in some cases, the graphics processor24may work in conjunction with one or more additional graphics processors and/or with an embedded or non-discrete graphics processing unit, which may be embedded into a motherboard and which is sometimes referred to as an on-board graphics chip or device. Computing device400might be a handheld video game device, a dedicated game console computing system, a general-purpose laptop or desktop computer, a smart phone, a tablet, a car console, or other system capable of executing one or more game applications or other types of applications.
The computing device400also includes various components for enabling input/output, such as an I/O32, a user I/O34, a display I/O36, and a network I/O38. As previously described, the input/output components may, in some cases, including touch-enabled devices. The I/O32interacts with storage element40and, through a device42, removable storage media44in order to provide storage for computing device100. Processing unit20can communicate through I/O32to store data, such as game state data and any shared data files. In addition to storage40and removable storage media44, computing device100is also shown including ROM (Read-Only Memory)46and RAM48. RAM48may be used for data that is accessed frequently, such as when a game is being played. Further, the RAM48may be used to store at least some of the anti-cheat system112. As previously described, access restrictions may be placed on the portions of the RAM48that store the at least some of the anti-cheat system112.
User I/O34is used to send and receive commands between processing unit20and user devices, such as game controllers. In some embodiments, the user I/O34can include touchscreen inputs. As previously described, the touchscreen can be a capacitive touchscreen, a resistive touchscreen, or other type of touchscreen technology that is configured to receive user input through tactile inputs from the user. Display I/O36provides input/output functions that are used to display images from the game being played. Network I/O38is used for input/output functions for a network. Network I/O38may be used during execution of a game, such as when a game is being played online or being accessed online. Further, the network I/O38may be used to access at least a portion of the anti-cheat system112from another computing system, such as a backend anti-cheat system144and/or an application host system142. In some embodiments, at least some content or data packets received by the network I/O38are prevented from being stored in the storage40, or in non-volatile memory. By preventing certain data packets associated with the anti-cheat system112from being provided to non-volatile memory, a user is prevented from accessing, modifying, or interfering with the operation of the anti-cheat system112.
Display output signals may be produced by the display I/O36and can include signals for displaying visual content produced by the computing device400on a display device, such as graphics, user interfaces, video, and/or other visual content. Computing device400may comprise one or more integrated displays configured to receive display output signals produced by the display I/O36, which may be output for display to a user. According to some embodiments, display output signals produced by the display I/O36may also be output to one or more display devices external to the computing device400.
The computing device400can also include other features that may be used with a game, such as a clock50, flash memory52, and other components. An audio/video player56might also be used to play a video sequence, such as a movie. It should be understood that other components may be provided in computing device400and that a person skilled in the art will appreciate other variations of computing device400.
Program code can be stored in ROM46, RAM48, or storage40(which might comprise hard disk, other magnetic storage, optical storage, solid state drives, and/or other non-volatile storage, or a combination or variation of these). At least part of the program code can be stored in ROM that is programmable (ROM, PROM, EPROM, EEPROM, and so forth), in storage40, and/or on removable media such as game media12(which can be a CD-ROM, cartridge, memory chip or the like, or obtained over a network or other electronic channel as needed). In general, program code can be found embodied in a tangible non-transitory signal-bearing medium.
Random access memory (RAM)48(and possibly other storage) is usable to store variables and other game and processor data as needed. RAM is used and holds data that is generated during the play of the game and portions thereof might also be reserved for frame buffers, game state and/or other data needed or usable for interpreting user input and generating game displays. Generally, RAM48is volatile storage and data stored within RAM48may be lost when the computing device100is turned off or loses power.
As computing device400reads game media12and provides a game, information may be read from game media12and stored in a memory device, such as RAM48. Additionally, data from storage40, ROM46, servers accessed via a network (not shown), or removable storage media46may be read and loaded into RAM48. Although data is described as being found in RAM48, it will be understood that data does not have to be stored in RAM48and may be stored in other memory accessible to processing unit20or distributed among several media, such as game media12and storage40.
It is to be understood that not necessarily all objects or advantages may be achieved in accordance with any particular embodiment described herein. Thus, for example, those skilled in the art will recognize that certain embodiments may be configured to operate in a manner that achieves or optimizes one advantage or group of advantages as taught herein without necessarily achieving other objects or advantages as may be taught or suggested herein.
All of the processes described herein may be embodied in, and fully automated via, software code modules executed by a computing system that includes one or more computers or processors. The code modules may be stored in any type of non-transitory computer-readable medium or other computer storage device. Some or all the methods may be embodied in specialized computer hardware.
Many other variations than those described herein will be apparent from this disclosure. For example, depending on the embodiment, certain acts, events, or functions of any of the algorithms described herein can be performed in a different sequence, can be added, merged, or left out altogether (for example, not all described acts or events are necessary for the practice of the algorithms). Moreover, in certain embodiments, acts or events can be performed concurrently, for example, through multi-threaded processing, interrupt processing, or multiple processors or processor cores or on other parallel architectures, rather than sequentially. In addition, different tasks or processes can be performed by different machines and/or computing systems that can function together.
The various illustrative logical blocks and modules described in connection with the embodiments disclosed herein can be implemented or performed by a machine, such as a processing unit or processor, a digital signal processor (DSP), an application specific integrated circuit (ASIC), a field programmable gate array (FPGA) or other programmable logic device, discrete gate or transistor logic, discrete hardware components, or any combination thereof designed to perform the functions described herein. A processor can be a microprocessor, but in the alternative, the processor can be a controller, microcontroller, or state machine, combinations of the same, or the like. A processor can include electrical circuitry configured to process computer-executable instructions. In another embodiment, a processor includes an FPGA or other programmable device that performs logic operations without processing computer-executable instructions. A processor can also be implemented as a combination of computing devices, for example, a combination of a DSP and a microprocessor, a plurality of microprocessors, one or more microprocessors in conjunction with a DSP core, or any other such configuration. Although described herein primarily with respect to digital technology, a processor may also include primarily analog components. For example, some or all of the signal processing algorithms described herein may be implemented in analog circuitry or mixed analog and digital circuitry. A computing environment can include any type of computer system, including, but not limited to, a computer system based on a microprocessor, a mainframe computer, a digital signal processor, a portable computing device, a device controller, or a computational engine within an appliance, to name a few.
Conditional language such as, among others, “can,” “could,” “might” or “may,” unless specifically stated otherwise, are otherwise understood within the context as used in general to convey that certain embodiments include, while other embodiments do not include, certain features, elements and/or steps. Thus, such conditional language is not generally intended to imply that features, elements and/or steps are in any way required for one or more embodiments or that one or more embodiments necessarily include logic for deciding, with or without user input or prompting, whether these features, elements and/or steps are included or are to be performed in any particular embodiment.
Disjunctive language such as the phrase “at least one of X, Y, or Z,” unless specifically stated otherwise, is otherwise understood with the context as used in general to present that an item, term, etc., may be either X, Y, or Z, or any combination thereof (for example, X, Y, and/or Z). Thus, such disjunctive language is not generally intended to, and should not, imply that certain embodiments require at least one of X, at least one of Y, or at least one of Z to each be present.
Any process descriptions, elements or blocks in the flow diagrams described herein and/or depicted in the attached figures should be understood as potentially representing modules, segments, or portions of code which include one or more executable instructions for implementing specific logical functions or elements in the process. Alternate implementations are included within the scope of the embodiments described herein in which elements or functions may be deleted, executed out of order from that shown, or discussed, including substantially concurrently or in reverse order, depending on the functionality involved as would be understood by those skilled in the art.
Unless otherwise explicitly stated, articles such as “a” or “an” should generally be interpreted to include one or more described items. Accordingly, phrases such as “a device configured to” are intended to include one or more recited devices. Such one or more recited devices can also be collectively configured to carry out the stated recitations. For example, “a processor configured to carry out recitations A, B and C” can include a first processor configured to carry out recitation A working in conjunction with a second processor configured to carry out recitations B and C.
It should be emphasized that many variations and modifications may be made to the above-described embodiments, the elements of which are to be understood as being among other acceptable examples. All such modifications and variations are intended to be included herein within the scope of this disclosure.
Claims
- A computer-implemented method comprising: as implemented by a user computing device configured with specific computer-executable instructions, initiating execution of an application by a hardware processor of the user computing device, wherein at least a portion of the application is executed within a volatile memory of the user computing device;executing a static loader included as part of the application;establishing, using the static loader, a communication channel over a network with a backend anti-cheat system that executes on a separate computing system from the user computing device;receiving a dynamic cheat detection module from the backend anti-cheat system over the communication channel;loading the dynamic cheat detection module, obtained over the communication channel from the backend anti-cheat system, directly into the volatile memory of the user computing device;executing the dynamic cheat detection module stored within the volatile memory of the user computing device;using the dynamic cheat detection module, obtaining a cheat signatures payload over the communication channel from the backend anti-cheat system, wherein the cheat signatures payload comprises representations of portions of volatile memory indicative of execution of one or more cheat applications;loading the cheat signatures payload into the volatile memory of the user computing device without storing the cheat signatures payload into a non-volatile memory of the user computing device;and detecting whether the one or more cheat applications are executing on the user computing device by performing an anti-cheat detection process with respect to the application using at least the dynamic cheat detection module and the cheat signatures payload, wherein the one or more cheat applications are separate applications that at least in part execute concurrently with the application.
- The computer-implemented method of claim 1 , wherein the static loader loads the dynamic cheat detection module into the volatile memory of the user computing device without storing the dynamic cheat detection module into the non-volatile memory of the user computing device.
- The computer-implemented method of claim 1 , further comprising: receiving a command to cease execution of the application;and in response to receiving the command, ceasing execution of the application;removing the dynamic cheat detection module from the user computing device;and removing the cheat signatures payload from the user computing device.
- The computer-implemented method of claim 3 , wherein removing the cheat signatures payload includes emptying a portion of the volatile memory allocated for storing the cheat signatures payload before returning the portion of the volatile memory to an available memory pool.
- The computer-implemented method of claim 3 , wherein the command is received in response to a detection of a match to a cheat signature during performance of the anti-cheat detection process.
- The computer-implemented method of claim 1 , wherein the application is a game.
- The computer-implemented method of claim 1 , wherein the application comprises two portions, and wherein initiating execution of the application comprises: initiating execution of a first portion of the application on the user computing device;and establishing a communication connection with a second portion of the application executing on an application host system.
- The computer-implemented method of claim 1 , wherein performing the anti-cheat detection process comprises: accessing a portion of the volatile memory using the dynamic detection module;creating a hash of a contents of the portion of the volatile memory;determining whether the hash matches a signature included in the cheat signatures payload;and in response to determining that the hash matches the signature included in the cheat signatures payload, sending an indication of a cheat code associated with the signature to the backend anti-cheat system.
- The computer-implemented method of claim 1 , wherein the cheat signatures payload comprises one or more signatures, each signature associated with a particular cheat software.
- A system comprising: an electronic data store configured to store an application, the electronic data store comprising non-volatile memory;a volatile memory configured to temporarily store data, the volatile memory separate from the electronic data store;and a hardware processor in communication with the electronic data store and the volatile memory, the hardware processor configured to execute specific computer-executable instructions to at least: initiate execution of the application wherein at least a portion of the application is executed within the volatile memory;execute a static loader included as part of the application;establish, using the static loader, a communication channel over a network with a backend anti-cheat system that executes on a separate computing system from the hardware processor;receive a cheat detection module from the backend anti-cheat system over the communication channel;load the cheat detection module, obtained over the communication channel from the backend anti-cheat system, directly into the volatile memory;execute the cheat detection module stored within the volatile memory;using the cheat detection module, obtain a cheat signatures payload from the backend anti-cheat system, wherein the cheat signatures payload comprises representations of portions of volatile memory indicative of execution of one or more cheat applications, and the backend anti-cheat system is implemented by a separate computing system;load the cheat signatures payload into the volatile memory without storing the cheat signatures payload into the electronic data store;and detect whether the one or more cheat applications are executing on the user computing device by performing an anti-cheat detection process with respect to the application using at least the cheat detection module and the cheat signatures payload, wherein the one or more cheat applications at least partially concurrently execute with the application.
- The system of claim 10 , wherein the cheat detection module establishes a second communication channel with the backend anti-cheat system to obtain the cheat signatures payload.
- The system of claim 10 , wherein the static loader loads the cheat detection module into the volatile memory without storing the cheat detection module into the electronic data store.
- The system of claim 10 , wherein the hardware processor is further configured to execute the specific computer-executable instructions to at least: cease execution of the application;remove the cheat detection module from the volatile memory;and remove the cheat signatures payload from the volatile memory.
- The system of claim 10 , wherein the application comprises at least two portions, and wherein the hardware processor is further configured to initiate execution of the application by: initiating execution of a first portion of the application;and establishing a communication connection with a second portion of the application executing on an application host system.
- The system of claim 10 , wherein the hardware processor is further configured to perform an anti-cheat detection process by: accessing data from a portion of the volatile memory using the detection module;creating a hash of the data from the portion of the volatile memory;determining whether the hash matches a signature included in the cheat signatures payload;and in response to determining that the hash matches the signature included in the cheat signatures payload, identifying the signature to the backend anti-cheat system.
- The system of claim 15 , wherein the cheat signatures payload comprises a data structure of cheat signatures and wherein determining whether the hash matches the signature included in the cheat signatures payload comprises using the hash as a key to access the data structure.
- The system of claim 15 , wherein the portion of the volatile memory is separate from volatile memory allocated to the application.
- A non-transitory computer-readable storage medium storing computer executable instructions that, when executed by one or more computing devices, configure the one or more computing devices to perform operations comprising: executing a first application, wherein at least a portion of the first application is executed within a volatile memory of a first computing device of the one or more computing devices;executing a static loader included as part of the first application;establishing, using the static loader, a communication channel over a network with a second computing device;receiving a cheat detection module from the second computing device over the communication channel;loading the cheat detection module, obtained over the communication channel from the second computing device, directly into the volatile memory of the first computing device;executing the cheat detection module within the volatile memory of the first computing device of the one or more computing devices;using the cheat detection module, accessing a cheat signatures payload over the communication channel from the second computing device, wherein the cheat signatures payload comprises representations of portions of volatile memory indicative of execution of one or more cheat applications;loading the cheat signatures payload into the volatile memory of the first computing device without storing the cheat signatures payload into a non-volatile memory of the first computing device;and using at least the cheat detection module and the cheat signatures payload to determine whether a second application executing on the first computing device is an instance of one of the one or more cheat applications, the second application enabling a user to cheat with respect to the first application.
- The computer-readable, non-transitory storage medium of claim 18 , wherein detecting whether the second application is executing comprises: accessing data from a portion of the volatile memory using the detection module;hashing the data to create a hash key;determining whether an entry exists in the cheat signatures payload corresponding to the hash key;and in response to determining the entry exists in the cheat signatures payload corresponding to the hash key, providing an alert to the second computing device corresponding to the entry in the cheat signatures payload.
- The computer-readable, non-transitory storage medium of claim 18 , wherein accessing the cheat signatures payload from the second computing device comprises, providing geographical location information to the second computing device, wherein the cheat signatures payload is associated with a geographical location of the first computing device.
Disclaimer: Data collected from the USPTO and may be malformed, incomplete, and/or otherwise inaccurate.